[转帖]IOC Security: Indicators of Attack vs. Indicators of Compromise
IOC Security: Indicators of Attack vs. Indicators of Compromise
https://www.crowdstrike.com/blog/indicators-attack-vs-indicators-compromise/
- December 9, 2014
- Jessica DeCianno
- Endpoint Protection
What is an Indicator of Compromise (IOC)?
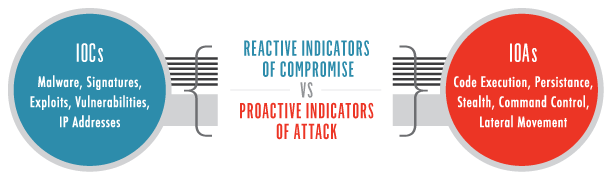
First we should provide a definition of an indicator of compromise (IOC). An IOC is often described in the forensics world as evidence on a computer that indicates that the security of the network has been breached. Investigators usually gather this data after being informed of a suspicious incident, on a scheduled basis, or after the discovery of unusual call-outs from the network. Ideally, this information is gathered to create “smarter” tools that can detect and quarantine suspicious files in the future.
In the Cyber world, an IOC is an MD5 hash, a C2 domain or hardcoded IP address, a registry key, filename, etc. These IOCs are constantly changing making a proactive approach to securing the enterprise impossible. Because IOCs provide a reactive method of tracking the bad guys, when you find an IOC, there is a high probability that you have already been compromised.
What is an Indicator of Attack (IOA)?
Unlike Indicators of Compromise (IOCs) used by legacy endpoint detection solutions, indicators of attack (IOA) focus on detecting the intent of what an attacker is trying to accomplish, regardless of the malware or exploit used in an attack. Just like AV signatures, an IOC-based detection approach cannot detect the increasing threats from malware-free intrusions and zero-day exploits. As a result, next-generation security solutions are moving to an IOA-based approach pioneered by CrowdStrike.
Indicator of Attack – Physical World
One way to focus our discussion around Indicators of Attack (IOA’s) is to provide an example of how a criminal would plan and undertake to rob a bank in the physical world.
A smart thief would begin by “casing” the bank, performing reconnaissance and understanding any defensive vulnerabilities. Once he determines the best time and tactics to strike, he proceeds to enter the bank. The robber disables the security system, moves toward the vault, and attempts to crack the combination. If he succeeds, he pinches the loot, makes an uneventful getaway and completes the mission. IOA’s are a series of behaviors a bank robber must exhibit to succeed at achieving his objective. He has to drive around the bank (identifying the target), park, and enter the building before he can enter the vault. If he doesn’t disable the security system, it will alarm when he enters the vault and takes the money.
Of course, activities like driving around the bank, parking and entering the bank do not, on their own, indicate an attack is imminent. Moreover, opening a bank vault and withdrawing cash is not necessarily an IOA… if the individual is authorized to access the vault. Specific combinations of activity trigger IOA’s.
Indicator of Attack – Cyber World
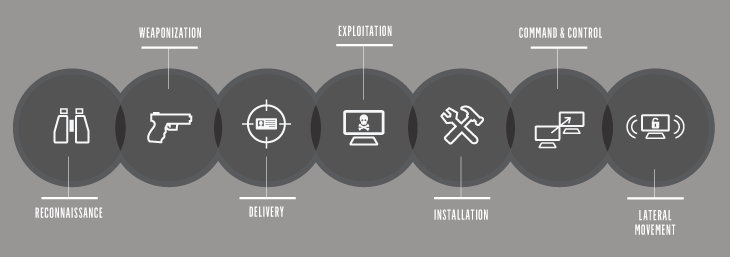
Let’s examine an example from the cyber world. An IOA represents a series of actions that an adversary must conduct to succeed. If we break down the most common and still the most successful tactic of determined adversaries – the spear phish – we can illustrate this point.
A successful phishing email must persuade the target to click on a link or open a document that will infect the machine. Once compromised, the attacker will silently execute another process, hide in memory or on disk and maintain persistence across reboots of the system. The next step is to make contact with a command and control site, informing his handlers that he awaits further instructions.
IOAs are concerned with the execution of these steps, the intent of the adversary and the outcomes he is trying to achieve. IOA’s are not focused on the specific tools he uses to accomplish his objectives.
By monitoring these execution points, gathering the indicators and consuming them via a Stateful Execution Inspection Engine, we can determine how an actor successfully gains access to the network and we can infer intent. No advance knowledge of the tools or malware (aka: Indicators of Compromise) is required.
Comparing an IOA to an IOC
In revisiting the bank robber analogy, imagine if we were only looking for IOC’s. In evidence from a previous robbery CCTV allowed us to identify that the bank robber drives a purple van, wears a Baltimore Ravens cap and uses a drill and liquid nitrogen to break into the vault. Though we try to track and observe these unique characteristics, his modus operandi (MO), what happens when the same individual instead drives a red car and wears a cowboy hat and uses a crowbar to access the vault? The result? The robber is successful again because we, the surveillance team, relied on indicators that reflected an outdated profile (IOCs).
Remember from above, an IOA reflects a series of actions an actor / robber must perform to be successful: enter the bank, disable the alarm systems, enter the vault, etc.
IOA’s are the Real-time Recorder
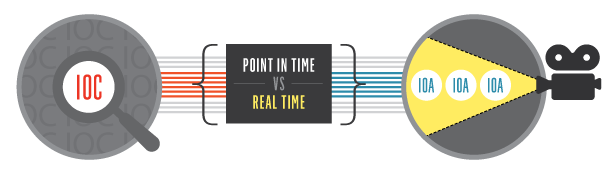
A by-product of the IOA approach is the ability to collect and analyze exactly what is happening on the network in real-time. The very nature of observing the behaviors as they execute is equivalent to observing a video camera and accessing a flight data recorder within your environment.
Returning to the physical world, when a detective arrives on a crime scene and has a gun, a body, and some blood they usually ask to see if anyone has any video of what transpired. The blood, body, and gun are IOCs that need to be manually reconstructed and are point-in-time artifacts. Very simply put, IOAs provide content for the video logs.
In the Cyber realm, showing you how an adversary slipped into your environment, accessed files, dumped passwords, moved laterally and eventually exfiltrated your data is the power of an IOA.
Real-world Adversary Activity – Chinese Actor
CrowdStrike’s Intelligence Team documented the following example activity attributed to a Chinese actor. The following example does highlight how one particular adversary’s activity eluded even endpoint protections.
This adversary uses the following tradecraft:
- In memory malware – never writes to disk
- A known and acceptable IT tool – Windows PowerShell with command line code
- Cleans up logs after themselves leaving no trace
Let’s explore the challenges that other endpoint solutions have with this tradecraft:
Anti-Virus – since the malware is never written to disk, most AV solutions set for an on-demand scan will not be alerted. On-demand scanning is only triggered on a file write or access. In addition, most proactive organizations perform a full scan only once a week because of the performance impact on the end user. If defenders were performing this full scan, and if the AV vendor was able to scan memory with an updated signature, they may provide an alert of this activity.
AV 2.0 Solutions – these are solutions that use machine learning and other techniques to determine if a file is good or bad. PowerShell is a legitimate windows system administration tool that isn’t (and shouldn’t be) identified as malicious. Thus, these solutions will not alert clients to this behavior.
Whitelisting – Powershell.exe is a known IT tool and would be allowed to execute in most environments, evading whitelisting solutions that may be in place.
IOC Scanning Solutions – since this adversary never writes to disk and cleans up after completing their work, what would we search for? IOC’s are known artifacts and in this case, there are no longer artifacts to discover. Moreover, most forensic-driven solutions require periodic “sweeps” of the targeted systems, and if an adversary can conduct his business between sweeps, he will remain undetected.
Final Words
In conclusion, at CrowdStrike, we know that our clients have adversary problems, not malware problems. By focusing on the tactics, techniques and procedures of targeted attackers, we can determine who the adversary is, what they are trying to access, and why. By the time you detect Indicators of Compromise, your organization has probably already been breached and may require an expensive incident response effort to remediate the damage.
By recording and gathering the indicators of attack and consuming them via a Stateful Execution Inspection Engine, you enable your team to view activity in real time and react in the present. Accessing your own network flight recorder avoids many of the time-consuming tasks associated with “putting the pieces together” after the fact. Providing first responders with the tools necessary to reconstruct the crime scene provides a cost-effective and proactive approach to confronting advanced persistent threats.
Interested in learning more about the IOA approach? Read our article on how CrowdStrike leverages Event Stream Processing (ESP) to detect malicious behavior.
[转帖]IOC Security: Indicators of Attack vs. Indicators of Compromise的更多相关文章
- [转帖]/etc/security/limits.conf的含义
https://www.cnblogs.com/pzk7788/p/7250723.html /etc/security/limits.conf 是 Linux 资源使用配置文件,用来限制用户对系统资 ...
- 《Network Security A Decision and Game Theoretic Approach》阅读笔记
网络安全问题的背景 网络安全研究的内容包括很多方面,作者形象比喻为盲人摸象,不同领域的网络安全专家对网络安全的认识是不同的. For researchers in the field of crypt ...
- Security Software Engineer
Security Software Engineer Are you excited to be part of the VR revolution and work on cutting edge ...
- [安全转帖]浅析安全威胁情报共享框架OpenIOC
浅析安全威胁情报共享框架OpenIOC https://www.freebuf.com/sectool/86580.html Indicator of compromise Outline: 1. I ...
- document.domain与js跨域的问题
以前如果要使iframe里面的脚本能访问parent的内容,但iframe和parent的二级域名相同,那一般都会在两者都写上document.domain="xxx.com" 以 ...
- Coablt strike官方教程中文译版本
安装和设置 系统要求 Cobalt Strike的最低系统要求 2 GHz +以上的cpu 2 GB RAM 500MB +可用空间 在Amazon的EC2上,至少使用较高核数的CPU(c1.medi ...
- Parity 钱包启动配置
Parity. Ethereum Client. By Wood/Paronyan/Kotewicz/Drwięga/Volf et al. Copyright 2015, 2016, 2017, 2 ...
- VC/MFC 编程技巧大总结
1 toolbar默认位图左上角那个点的颜色是透明色,不喜欢的话可以自己改. 2 VC++中 WM_QUERYENDSESSION WM_ENDSESSION 为系统关机消息. 3 Java学习书推荐 ...
- 【云计算】使用Libcloud屏蔽OpenStack、AWS、AliYun等虚拟化层差异
libcloud 是一个访问云计算服务的统一接口,该项目已经成为 Apache 组织的顶级项目,采用 Python 开发. Apache基金会于5月25日宣布,Libcloud已完成孵化.成为顶级项目 ...
随机推荐
- WinDbg常用命令系列---!handle
!handle 简介 !handle扩展显示有关目标系统中一个或所有进程拥有的一个或多个句柄的信息. 使用形式 用户模式!handle [Handle [UMFlags [TypeName]]] !h ...
- 【批处理】for命令
for 命令 学习:https://www.cnblogs.com/Braveliu/p/5081087.html FOR这条命令基本上都被用来处理文本,但还有其他一些好用的功能! 看看他的基本格式( ...
- 61、Spark Streaming:部署、升级和监控应用程序
一.部署应用程序 1.流程 1.有一个集群资源管理器,比如standalone模式下的Spark集群,Yarn模式下的Yarn集群等. 2.打包应用程序为一个jar包. 3.为executor配置充足 ...
- 【00NOIP普及组】税收与补贴问题(信息学奥赛一本通 1911)( 洛谷 1023)
[题目描述] 每样商品的价格越低,其销量就会相应增大.现已知某种商品的成本及其在若干价位上的销量(产品不会低于成本销售),并假设相邻价位间销量的变化是线性的且在价格高于给 定的最高价位后,销量以某固定 ...
- 【POJ1321】棋盘问题
本题传动门 本题知识点:深度优先搜索 + 枚举 + 回溯 题意是要求我们把棋子放在棋盘的'#'上,但不能把两枚棋子放在同一列或者同一行上,问摆好这k枚棋子有多少种情况. 我们可以一行一行地找,当在某一 ...
- hadoop jps不显示信息
使用kvm做了一个hadoop组件的镜像,使用该镜像启动,在使用jps的时候,没有任何信息显示. 解决: 删除/tmp下的hsper开头文件,哪个用户没有权限就删除对应的hsper**_usernam ...
- ICEM-带孔小板
原版视频下载地址:https://pan.baidu.com/s/1jHMvXHG 密码: p93q
- Hadoop(四)—— MapReduce
一.Hadoop版本特性 MRv1 第一代计算框架,由编程模型和运行时环境两部分组成. 编程模型是,将数据进行map操作,然后进行reduce操作,最后将计算结果存储到HDFS中. 运行时环境是,由J ...
- 用户账户——《Python编程从入门到实践》
Web应用程序的核心是让任何用户都能够注册账户并能够使用它,不管用户身处何方 1.让用户能够输入数据 建立用于创建用户的身份验证系统之前,我们先来添加几个页面,让用户能够输入数据.当前,只有超级用户能 ...
- 启动服务器 SEVERE: Error configuring application listener of class org.springframework.web.context.ContextLoaderListener
意思是spring.jar这个包在发布的时候没有被放入war.如果是maven管理的项目,可以看看这个项目的部署参数里有没有加入所有maven的包. 右键项目->Properties->D ...
