Hash Tables and Hash Functions
Reference: Compuer science
Introduction:
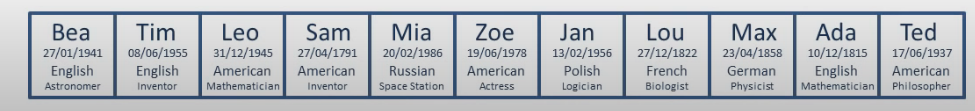
This computer science video describes the fundamental principles of the hash table data structure which allows for very fast insertion and retrieval of data. It covers commonly used hash algorithms for numeric and alphanumeric keys and summarises the objectives of a good hash function. Collision resolution is described, including open addressing techniques such as linear and quadratic probing, and closed addressing techniques such as chaining with a linked list.

Consider a list:
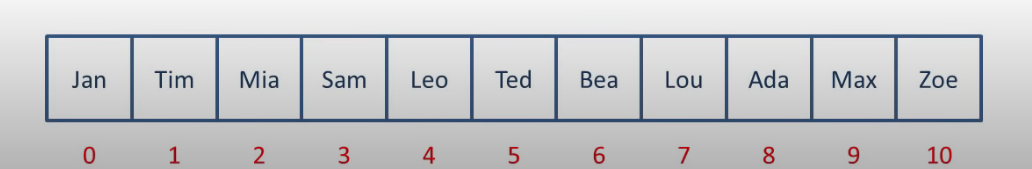
Find Ada
You can use linearly search, which costs the time of O(n)
Or you happend to know the index of ada(8), you can look up the value very quickly.
this costs you the time of O(1)
Can help wondering that what if we encode the name into index would the look-up process become O(1).?
Absolutely!
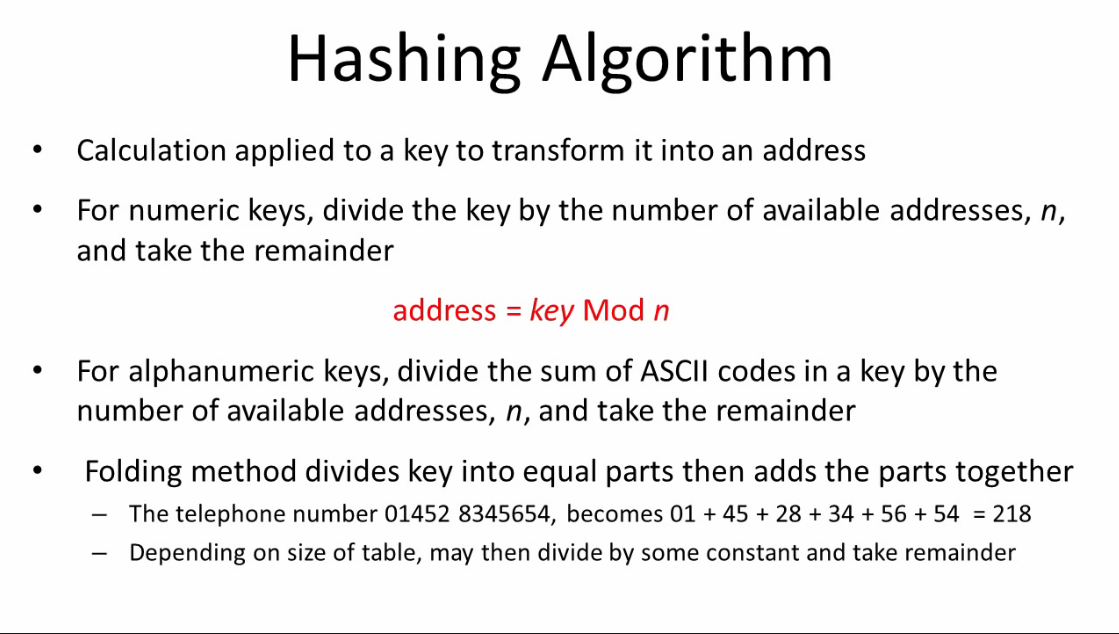
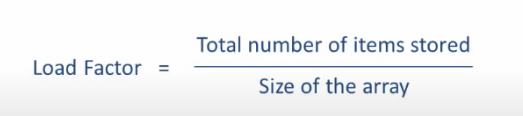
we can turn the key(i.e. the name) into a number(index) with a hash function.
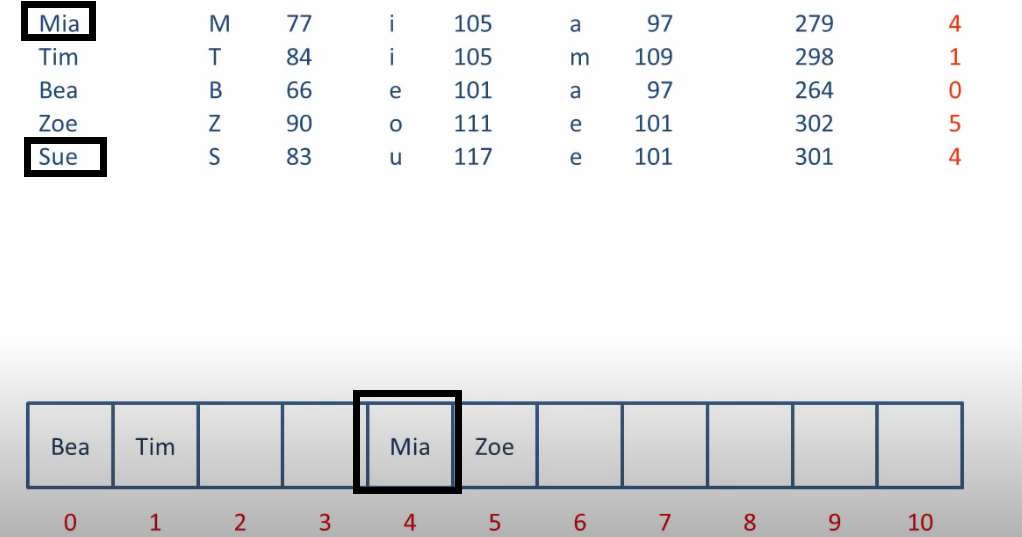
Let's say take each letter of the word get its ascii code,add them up,divided by the length of the array,get the remainder.
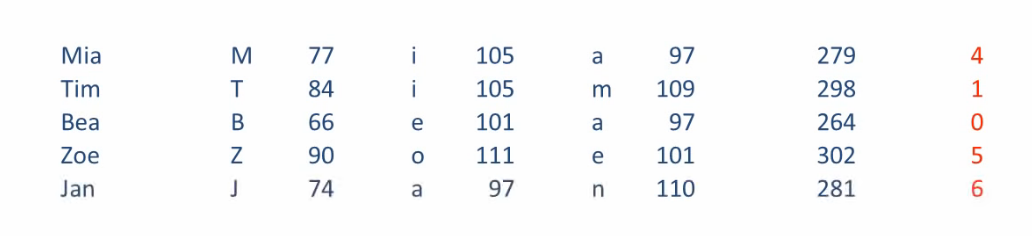
Namely , the hash function here is :
we can serve the properties of a person as the value,the name as key.
So that we can look up the profile of a person by the key(i.e.name)
Notes:
So far you aquire the ability to transform a key into index, you can look up very information by hash table.
Needless to say, that is unrealistic.

Have you ever consider the case that two different key are truned into a same index number?
That is collisions.
Let's look a example.
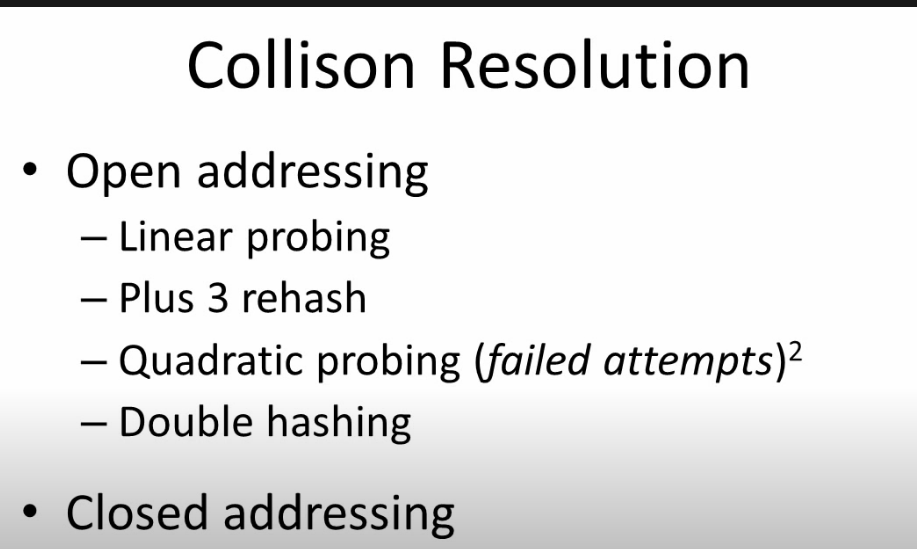
How to solve collisions?
we can put sue into the next place index5 which is empty.
Basically we can put the one that causes collision into the next empty place.
this is linear probing.
put the element somewhere other than the caculated adress is call open adressing.
because every location is open to every elements.
we can use a varity of techniques to decide where to palce.
If we get to the end of the array still can't find a empty place,
it may cycle around to the start of the array.
As you can image , the indexing process is also involved linear probing.(linear search)
In the worse case scenario, it takes O(n) to store and search a key.
Need to mention:
Another way to deal with collisions is called chaining. (close addressing)
we add a linked list in the collision index.
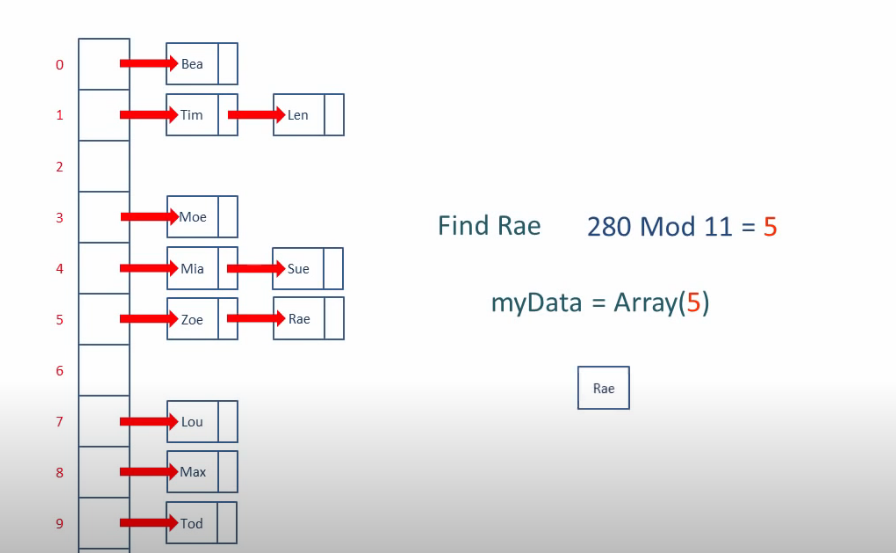
traverse the linked list also takes time.
Summary:

Hash Tables and Hash Functions的更多相关文章
- 11 Hash tables
11 Hash tables Many applications require a dynamic set that supports only the dictionary operatio ...
- 查询计划Hash和查询Hash
查询计划hash和查询hash 在SQL Server 2008中引入的围绕执行计划和缓冲的新功能被称为查询计划hash和查询hash.这是使用针对查询或查询计划的算法来生成二进制hash值的二进制对 ...
- 14.4.3 Adaptive Hash Index 自适应hash index
14.4.3 Adaptive Hash Index 自适应hash index 自适应hash index(AHI) 让InnoDB 执行更像内存数据库在系统使用合适的负载组合和足够的内存用于Buf ...
- 14.2.5.6 Adaptive Hash Indexes 自适应Hash Indexes
14.2.5.6 Adaptive Hash Indexes 自适应Hash Indexes adaptive hash index(AHI) 让InnoDB 执行更加像在一个内存数据库里在, 在不牺 ...
- Hash::make与Hash::check
调用方法之前要先去引用: use Illuminate\Support\Facades\Hash; 可以调用 Hash 门面上的 make 方法对存储密码进行哈希: $pwd = Hash::make ...
- 转载:字符串hash总结(hash是一门优雅的暴力!)
转载自:远航休息栈 字符串Hash总结 Hash是什么意思呢?某度翻译告诉我们: hash 英[hæʃ] 美[hæʃ]n. 剁碎的食物; #号; 蔬菜肉丁;vt. 把…弄乱; 切碎; 反复推敲; 搞糟 ...
- cdoj1092-韩爷的梦 (字符串hash)【hash】
http://acm.uestc.edu.cn/#/problem/show/1092 韩爷的梦 Time Limit: 200/100MS (Java/Others) Memory Limi ...
- Hash表及hash算法的分析
Hash表中的一些原理/概念,及根据这些原理/概念: 一. Hash表概念 二. Hash构造函数的方法,及适用范围 三. Hash处理冲突方法,各自特征 四. ...
- Cuckoo Hash和多级Hash的粗浅认识
通过对Cuckoo Hash.多级Hash和BloomFilter的粗浅了解,感觉它们三者存在类似之处,算是近亲(暂且把普通的Hash称作远亲). Cuckoo Hash的思想非常简单,冲突时,重Ha ...
随机推荐
- CentOS 6.8内核版本升级
1.查看当前版本 [root@www.linuxidc.com docker]# cat /etc/issue CentOS release 6.8 (Final) Kernel \r on an ...
- mysql: SOURCE error 2?
mysql: SOURCE error 2? mysql -uroot -p ****** # 路径输入错误,会抛出这个异常 mysql> source /var/lib/ambari-serv ...
- 线程池的介绍和使用,以及基于jvmti设计非入侵监控
作者:小傅哥 博客:https://bugstack.cn 沉淀.分享.成长,让自己和他人都能有所收获! 一.前言 五常大米好吃! 哈哈哈,是不你总买五常大米,其实五常和榆树是挨着的,榆树大米也好吃, ...
- 面试 07-安全问题:CSRF和XSS
07-安全问题:CSRF和XSS #前言 面试中的安全问题,明确来说,就两个方面: CSRF:基本概念.攻击方式.防御措施 XSS:基本概念.攻击方式.防御措施 这两个问题,一般不会问太难. 有人问: ...
- js上 七、表达式
(1).什么是表达式 任何有值的内容都是表达式 一个表达式会产生一个值,它可以放在任何需要一个值的地方,比如a=3中的3就是一个表达式,a=3整体也可以作为一个表达式. 常见表达式有如下几种: ü 原 ...
- C++模板元编程----快速排序
目录 目录 简介 实现 数据结构定义 在数组前添加一个元素 判断 分堆 合并 快速排序的实现 总结 简介 上一篇使用C++模板模板实现了一个选择排序.这一次,更进一步的,实现了一个快速排序算法.关于快 ...
- Mysql联合索引的最左前缀原则以及b+tree
软件版本mysql5.7 根据官网的文档 https://dev.mysql.com/doc/refman/5.7/en/multiple-column-indexes.html 查询条件要符合最左原 ...
- Python 进阶——如何正确使用 yield?
本文的文字及图片来源于网络,仅供学习.交流使用,不具有任何商业用途,如有问题请及时联系我们以作处理 在 Python 开发中, yield 关键字的使用其实较为频繁,例如大集合的生成,简化代码结构.协 ...
- WEBSERVICE 分析器错误信息: 未能创建类型
问题描述 分析器错误 说明: 在分析向此请求提供服务所需资源时出错.请检查下列特定分析错误详细信息并适当地修改源文件. 分析器错误信息: 未能创建类型"Service1". 源错误 ...
- (十一)、head--查看文件前若干部分,tail--查看文件后若干部分
一.命令描述与格式 head用于查看文件前面部分,tail用于查看文件的末尾部分 格式:head/tail [-选项] 文件 head选项: -c:处理文件若干字节数,加b.k.m -n:前 ...
