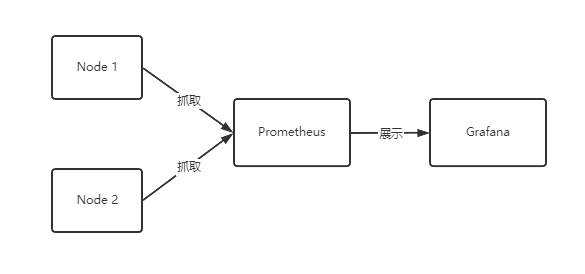
Kubernetes(K8S) 监控 Prometheus + Grafana
监控指标
集群监控
- 节点资源利用率
- 节点数
- 运行Pods
Pod 监控
- 容器指标
- 应用程序
Prometheus
开源的
监控、报警、数据库
以HTTP协议周期性抓取被监控组件状态
不需要复杂的集成过程,使用http接口接入就可以了
Grafana
开源的数据分析和可视化工具
支持多种数据源
Yaml 文件
将 Yaml 传到 linux 服务器
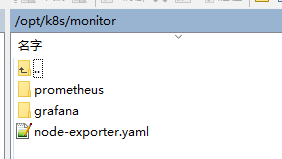
node-exporter.yaml
prometheus
--configmap.yaml
--prometheus.deploy.yml
--prometheus.svc.yml
--rbac-setup.yaml
grafana
--grafana-deploy.yaml
--grafana-ing.yaml
--grafana-svc.yaml
Prometheus Yaml 文件
- node-exporter.yaml
守护进程
---
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: node-exporter
namespace: kube-system
labels:
k8s-app: node-exporter
spec:
selector:
matchLabels:
k8s-app: node-exporter
template:
metadata:
labels:
k8s-app: node-exporter
spec:
containers:
- image: prom/node-exporter
name: node-exporter
ports:
- containerPort: 9100
protocol: TCP
name: http
---
apiVersion: v1
kind: Service
metadata:
labels:
k8s-app: node-exporter
name: node-exporter
namespace: kube-system
spec:
ports:
- name: http
port: 9100
nodePort: 31672
protocol: TCP
type: NodePort
selector:
k8s-app: node-exporter
- configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:
name: prometheus-config
namespace: kube-system
data:
prometheus.yml: |
global:
scrape_interval: 15s
evaluation_interval: 15s
scrape_configs:
- job_name: 'kubernetes-apiservers'
kubernetes_sd_configs:
- role: endpoints
scheme: https
tls_config:
ca_file: /var/run/secrets/kubernetes.io/serviceaccount/ca.crt
bearer_token_file: /var/run/secrets/kubernetes.io/serviceaccount/token
relabel_configs:
- source_labels: [__meta_kubernetes_namespace, __meta_kubernetes_service_name, __meta_kubernetes_endpoint_port_name]
action: keep
regex: default;kubernetes;https
- job_name: 'kubernetes-nodes'
kubernetes_sd_configs:
- role: node
scheme: https
tls_config:
ca_file: /var/run/secrets/kubernetes.io/serviceaccount/ca.crt
bearer_token_file: /var/run/secrets/kubernetes.io/serviceaccount/token
relabel_configs:
- action: labelmap
regex: __meta_kubernetes_node_label_(.+)
- target_label: __address__
replacement: kubernetes.default.svc:443
- source_labels: [__meta_kubernetes_node_name]
regex: (.+)
target_label: __metrics_path__
replacement: /api/v1/nodes/${1}/proxy/metrics
- job_name: 'kubernetes-cadvisor'
kubernetes_sd_configs:
- role: node
scheme: https
tls_config:
ca_file: /var/run/secrets/kubernetes.io/serviceaccount/ca.crt
bearer_token_file: /var/run/secrets/kubernetes.io/serviceaccount/token
relabel_configs:
- action: labelmap
regex: __meta_kubernetes_node_label_(.+)
- target_label: __address__
replacement: kubernetes.default.svc:443
- source_labels: [__meta_kubernetes_node_name]
regex: (.+)
target_label: __metrics_path__
replacement: /api/v1/nodes/${1}/proxy/metrics/cadvisor
- job_name: 'kubernetes-service-endpoints'
kubernetes_sd_configs:
- role: endpoints
relabel_configs:
- source_labels: [__meta_kubernetes_service_annotation_prometheus_io_scrape]
action: keep
regex: true
- source_labels: [__meta_kubernetes_service_annotation_prometheus_io_scheme]
action: replace
target_label: __scheme__
regex: (https?)
- source_labels: [__meta_kubernetes_service_annotation_prometheus_io_path]
action: replace
target_label: __metrics_path__
regex: (.+)
- source_labels: [__address__, __meta_kubernetes_service_annotation_prometheus_io_port]
action: replace
target_label: __address__
regex: ([^:]+)(?::\d+)?;(\d+)
replacement: $1:$2
- action: labelmap
regex: __meta_kubernetes_service_label_(.+)
- source_labels: [__meta_kubernetes_namespace]
action: replace
target_label: kubernetes_namespace
- source_labels: [__meta_kubernetes_service_name]
action: replace
target_label: kubernetes_name
- job_name: 'kubernetes-services'
kubernetes_sd_configs:
- role: service
metrics_path: /probe
params:
module: [http_2xx]
relabel_configs:
- source_labels: [__meta_kubernetes_service_annotation_prometheus_io_probe]
action: keep
regex: true
- source_labels: [__address__]
target_label: __param_target
- target_label: __address__
replacement: blackbox-exporter.example.com:9115
- source_labels: [__param_target]
target_label: instance
- action: labelmap
regex: __meta_kubernetes_service_label_(.+)
- source_labels: [__meta_kubernetes_namespace]
target_label: kubernetes_namespace
- source_labels: [__meta_kubernetes_service_name]
target_label: kubernetes_name
- job_name: 'kubernetes-ingresses'
kubernetes_sd_configs:
- role: ingress
relabel_configs:
- source_labels: [__meta_kubernetes_ingress_annotation_prometheus_io_probe]
action: keep
regex: true
- source_labels: [__meta_kubernetes_ingress_scheme,__address__,__meta_kubernetes_ingress_path]
regex: (.+);(.+);(.+)
replacement: ${1}://${2}${3}
target_label: __param_target
- target_label: __address__
replacement: blackbox-exporter.example.com:9115
- source_labels: [__param_target]
target_label: instance
- action: labelmap
regex: __meta_kubernetes_ingress_label_(.+)
- source_labels: [__meta_kubernetes_namespace]
target_label: kubernetes_namespace
- source_labels: [__meta_kubernetes_ingress_name]
target_label: kubernetes_name
- job_name: 'kubernetes-pods'
kubernetes_sd_configs:
- role: pod
relabel_configs:
- source_labels: [__meta_kubernetes_pod_annotation_prometheus_io_scrape]
action: keep
regex: true
- source_labels: [__meta_kubernetes_pod_annotation_prometheus_io_path]
action: replace
target_label: __metrics_path__
regex: (.+)
- source_labels: [__address__, __meta_kubernetes_pod_annotation_prometheus_io_port]
action: replace
regex: ([^:]+)(?::\d+)?;(\d+)
replacement: $1:$2
target_label: __address__
- action: labelmap
regex: __meta_kubernetes_pod_label_(.+)
- source_labels: [__meta_kubernetes_namespace]
action: replace
target_label: kubernetes_namespace
- source_labels: [__meta_kubernetes_pod_name]
action: replace
target_label: kubernetes_pod_name
- prometheus.deploy.yml
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
name: prometheus-deployment
name: prometheus
namespace: kube-system
spec:
replicas: 1
selector:
matchLabels:
app: prometheus
template:
metadata:
labels:
app: prometheus
spec:
containers:
- image: prom/prometheus:v2.0.0
name: prometheus
command:
- "/bin/prometheus"
args:
- "--config.file=/etc/prometheus/prometheus.yml"
- "--storage.tsdb.path=/prometheus"
- "--storage.tsdb.retention=24h"
ports:
- containerPort: 9090
protocol: TCP
volumeMounts:
- mountPath: "/prometheus"
name: data
- mountPath: "/etc/prometheus"
name: config-volume
resources:
requests:
cpu: 100m
memory: 100Mi
limits:
cpu: 500m
memory: 2500Mi
serviceAccountName: prometheus
volumes:
- name: data
emptyDir: {}
- name: config-volume
configMap:
name: prometheus-config
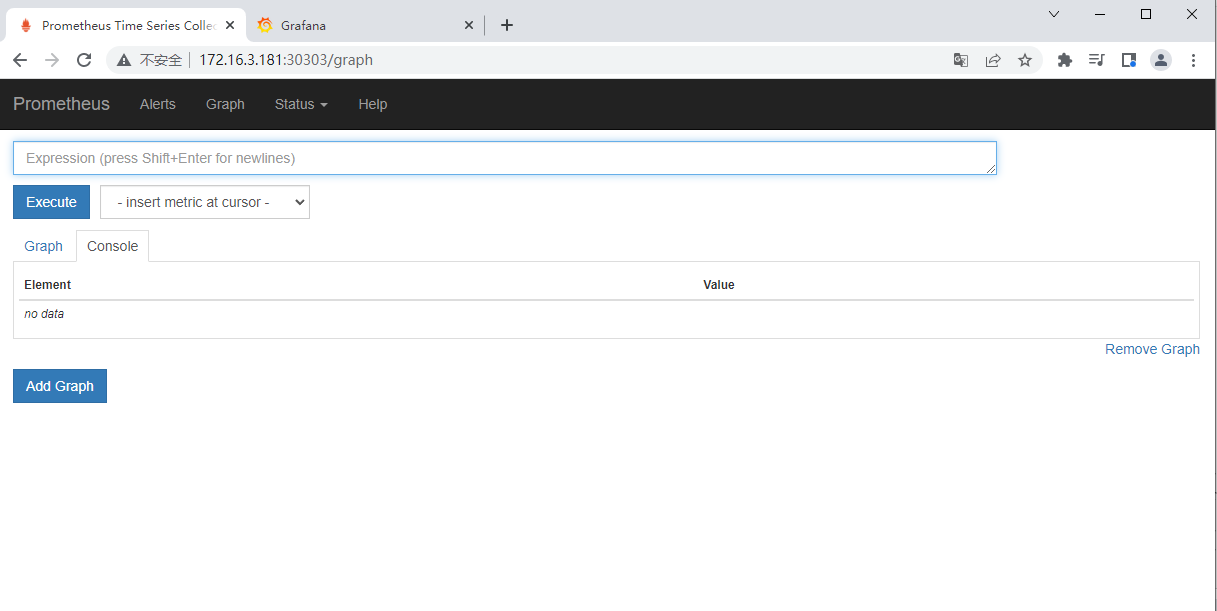
- prometheus.svc.yml
---
kind: Service
apiVersion: v1
metadata:
labels:
app: prometheus
name: prometheus
namespace: kube-system
spec:
type: NodePort
ports:
- port: 9090
targetPort: 9090
nodePort: 30303
selector:
app: prometheus
- rbac-setup.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: prometheus
rules:
- apiGroups: [""]
resources:
- nodes
- nodes/proxy
- services
- endpoints
- pods
verbs: ["get", "list", "watch"]
- apiGroups:
- extensions
resources:
- ingresses
verbs: ["get", "list", "watch"]
- nonResourceURLs: ["/metrics"]
verbs: ["get"]
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: prometheus
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: prometheus
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: prometheus
subjects:
- kind: ServiceAccount
name: prometheus
namespace: kube-system
grafana Yaml 文件
- grafana-deploy.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: grafana-core
namespace: kube-system
labels:
app: grafana
component: core
spec:
replicas: 1
selector:
matchLabels:
app: grafana
component: core
template:
metadata:
labels:
app: grafana
component: core
spec:
containers:
- image: grafana/grafana:4.2.0
name: grafana-core
imagePullPolicy: IfNotPresent
# env:
resources:
# keep request = limit to keep this container in guaranteed class
limits:
cpu: 100m
memory: 100Mi
requests:
cpu: 100m
memory: 100Mi
env:
# The following env variables set up basic auth twith the default admin user and admin password.
- name: GF_AUTH_BASIC_ENABLED
value: "true"
- name: GF_AUTH_ANONYMOUS_ENABLED
value: "false"
# - name: GF_AUTH_ANONYMOUS_ORG_ROLE
# value: Admin
# does not really work, because of template variables in exported dashboards:
# - name: GF_DASHBOARDS_JSON_ENABLED
# value: "true"
readinessProbe:
httpGet:
path: /login
port: 3000
# initialDelaySeconds: 30
# timeoutSeconds: 1
volumeMounts:
- name: grafana-persistent-storage
mountPath: /var
volumes:
- name: grafana-persistent-storage
emptyDir: {}
- grafana-ing.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: grafana
namespace: kube-system
spec:
rules:
- host: k8s.grafana
http:
paths:
- path: /
backend:
serviceName: grafana
servicePort: 3000
- grafana-svc.yaml
apiVersion: v1
kind: Service
metadata:
name: grafana
namespace: kube-system
labels:
app: grafana
component: core
spec:
type: NodePort
ports:
- port: 3000
selector:
app: grafana
component: core
部署
[root@k8smaster monitor]# ls
grafana node-exporter.yaml prometheus
# 安装 Prometheus
[root@k8smaster monitor]# kubectl create -f prometheus/rbac-setup.yaml
clusterrole.rbac.authorization.k8s.io/prometheus created
serviceaccount/prometheus created
clusterrolebinding.rbac.authorization.k8s.io/prometheus created
[root@k8smaster monitor]# kubectl create -f node-exporter.yaml
daemonset.apps/node-exporter created
service/node-exporter created
[root@k8smaster monitor]# kubectl create -f prometheus/configmap.yaml
configmap/prometheus-config created
[root@k8smaster monitor]# kubectl create -f prometheus/prometheus.deploy.yml
deployment.apps/prometheus created
[root@k8smaster monitor]# kubectl create -f prometheus/prometheus.svc.yml
service/prometheus created
# 安装 Grafana
[root@k8smaster monitor]# kubectl create -f grafana/grafana-deploy.yaml
deployment.apps/grafana-core created
[root@k8smaster monitor]# kubectl create -f grafana/grafana-svc.yaml
service/grafana created
[root@k8smaster monitor]# kubectl create -f grafana/grafana-ing.yaml
ingress.extensions/grafana created
# 查看状态
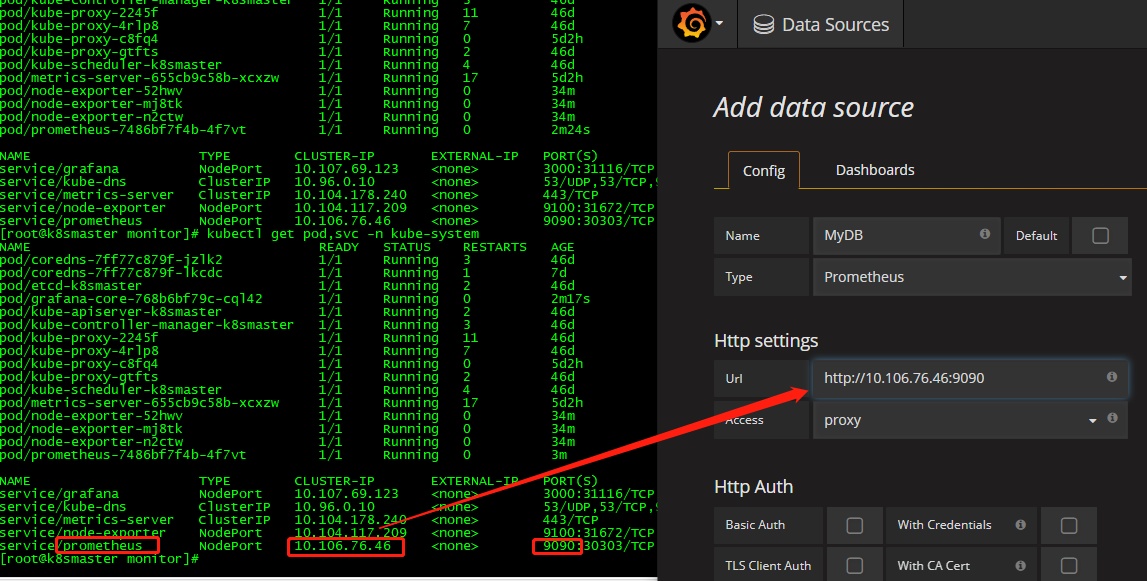
[root@k8smaster monitor]# kubectl get pod,svc -n kube-system
NAME READY STATUS RESTARTS AGE
pod/coredns-7ff77c879f-jzlk2 1/1 Running 3 46d
pod/coredns-7ff77c879f-lkcdc 1/1 Running 1 7d
pod/etcd-k8smaster 1/1 Running 2 46d
pod/grafana-core-768b6bf79c-cql42 1/1 Running 0 2m17s
pod/kube-apiserver-k8smaster 1/1 Running 2 46d
pod/kube-controller-manager-k8smaster 1/1 Running 3 46d
pod/kube-proxy-2245f 1/1 Running 11 46d
pod/kube-proxy-4rlp8 1/1 Running 7 46d
pod/kube-proxy-c8fq4 1/1 Running 0 5d2h
pod/kube-proxy-gtfts 1/1 Running 2 46d
pod/kube-scheduler-k8smaster 1/1 Running 4 46d
pod/metrics-server-655cb9c58b-xcxzw 1/1 Running 17 5d2h
pod/node-exporter-52hwv 1/1 Running 0 34m
pod/node-exporter-mj8tk 1/1 Running 0 34m
pod/node-exporter-n2ctw 1/1 Running 0 34m
pod/prometheus-7486bf7f4b-4f7vt 1/1 Running 0 3m
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/grafana NodePort 10.107.69.123 <none> 3000:31116/TCP 2m8s
service/kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP,9153/TCP 46d
service/metrics-server ClusterIP 10.104.178.240 <none> 443/TCP 11d
service/node-exporter NodePort 10.104.117.209 <none> 9100:31672/TCP 34m
service/prometheus NodePort 10.106.76.46 <none> 9090:30303/TCP 13m
[root@k8smaster monitor]#
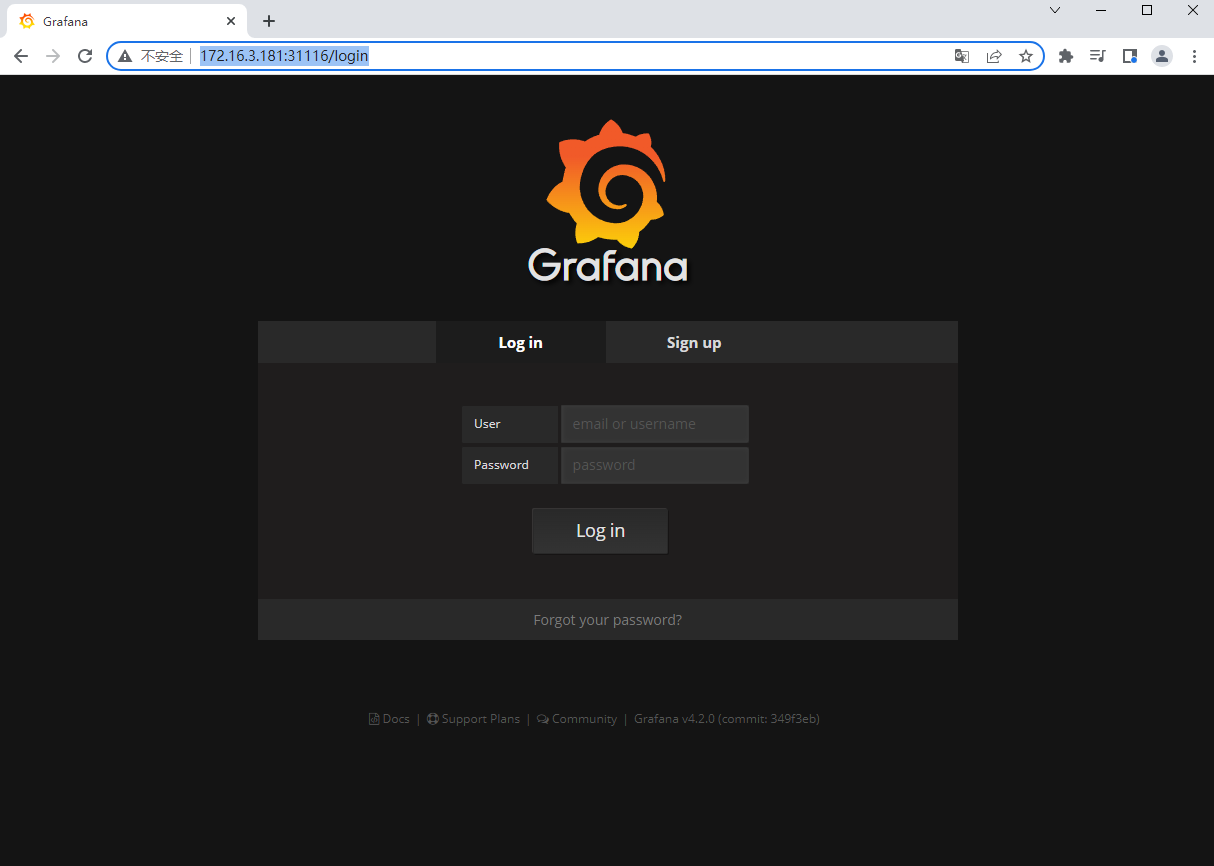
默认用户名:admin 密码:admin
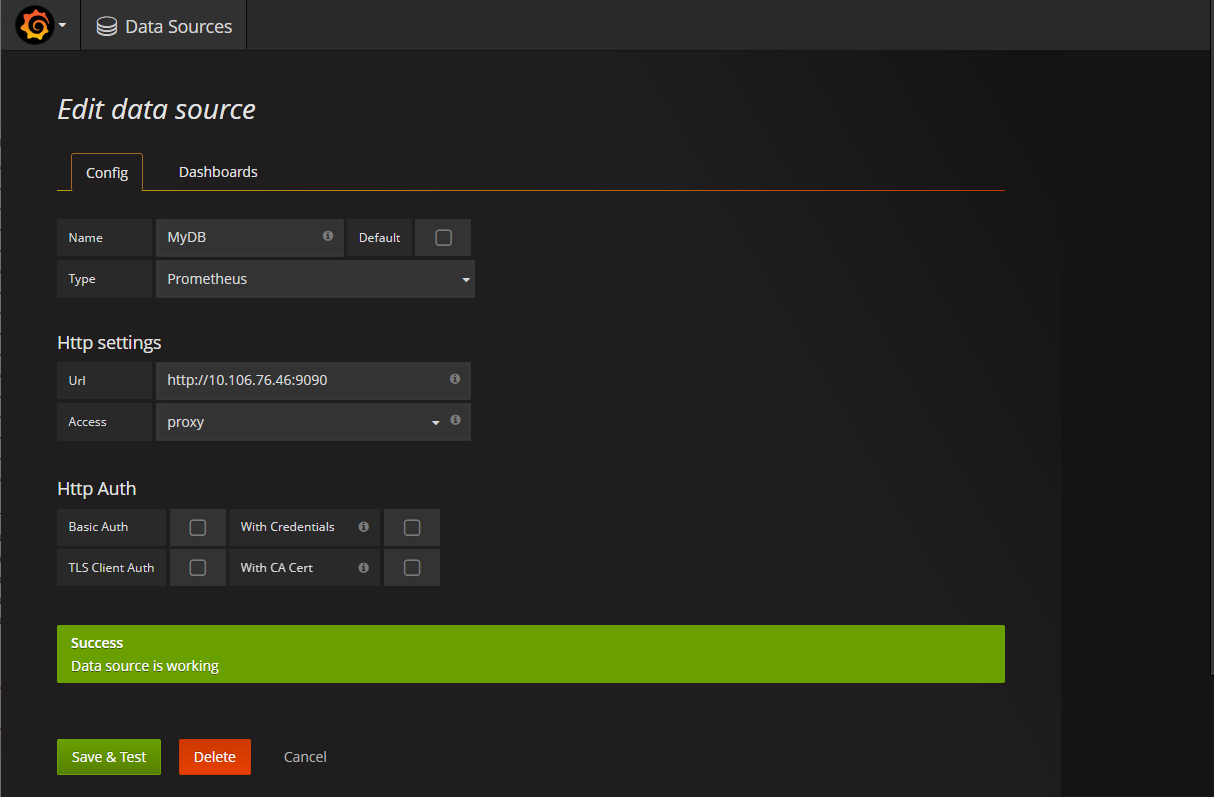
打开 Grafana,配置数据源,
配置数据源,
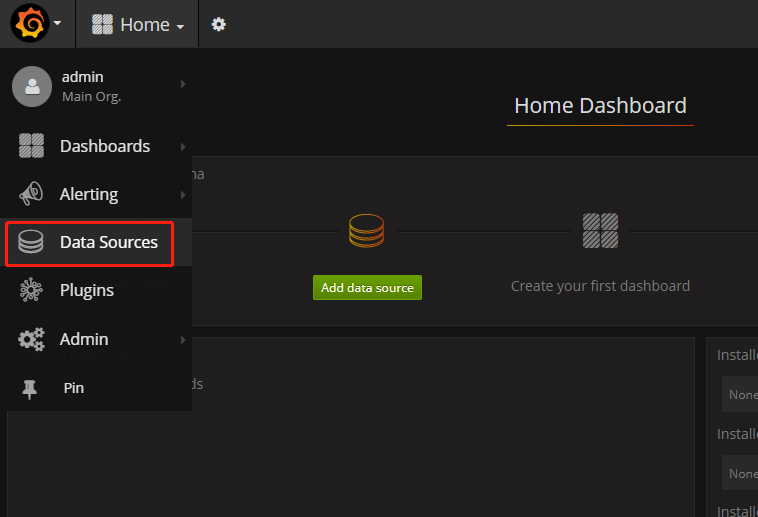
点击 Add
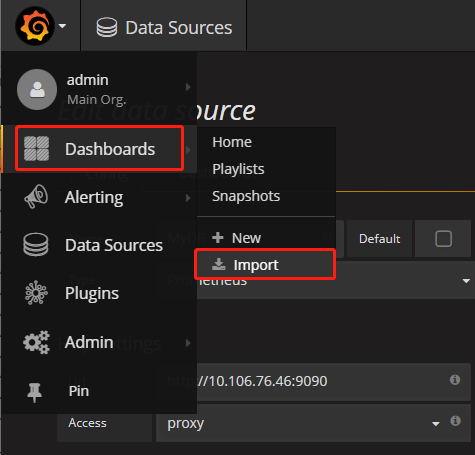
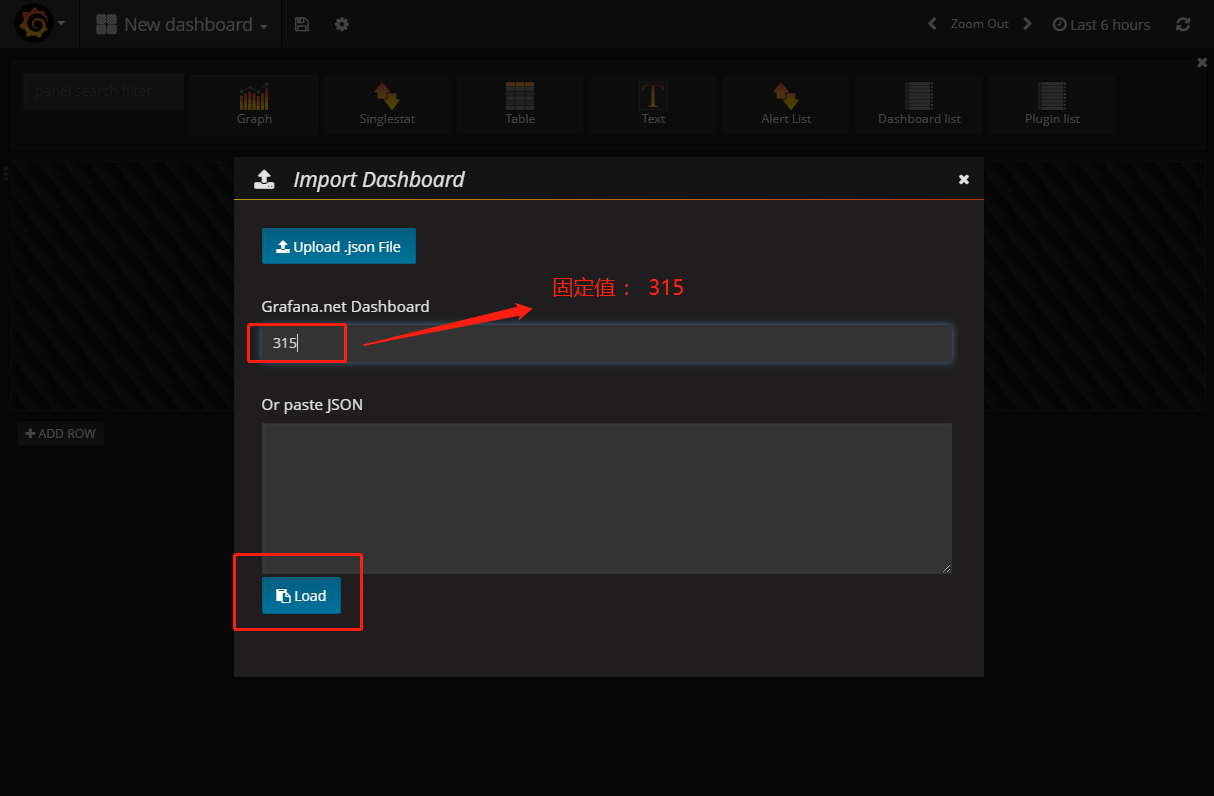
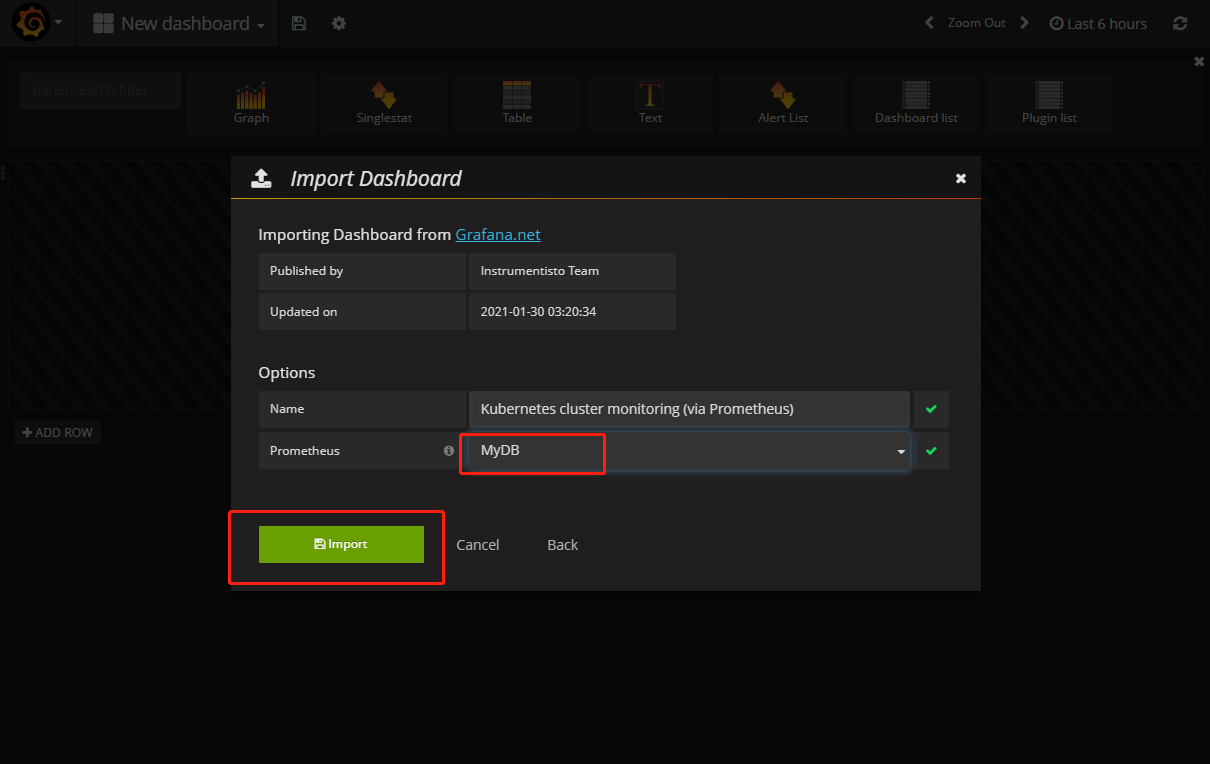
导入显示模板

Kubernetes(K8S) 监控 Prometheus + Grafana的更多相关文章
- K8S的Kafka监控(Prometheus+Grafana)
欢迎访问我的GitHub https://github.com/zq2599/blog_demos 内容:所有原创文章分类汇总及配套源码,涉及Java.Docker.Kubernetes.DevOPS ...
- kubernetes之监控Prometheus实战--prometheus介绍--获取监控(一)
Prometheus介绍 Prometheus是一个最初在SoundCloud上构建的开源监控系统 .它现在是一个独立的开源项目,为了强调这一点,并说明项目的治理结构,Prometheus 于2016 ...
- K8s 部署 Prometheus + Grafana
一.简介 1. Prometheus 一款开源的监控&报警&时间序列数据库的组合,起始是由 SoundCloud 公司开发的 基本原理是通过 HTTP 协议周期性抓取被监控组件的状态, ...
- EggJS 云原生应用硬核实战(Kubernetes+Traefik+Helm+Prometheus+Grafana),提供 Demo
介绍 这是一个关于 Egg.js 应用上云️的示例,笔者所在的大前端团队的已应用于生产. CI/CD & DevOps & GitOps & HPA 等这里暂不做讨论,因为每一 ...
- kubernetes监控-prometheus(十六)
监控方案 cAdvisor+Heapster+InfluxDB+Grafana Y 简单 容器监控 cAdvisor/exporter+Prometheus+Grafana Y 扩展性好 容器,应用, ...
- K8S(14)监控实战-grafana出图_alert告警
k8s监控实战-grafana出图_alert告警 目录 k8s监控实战-grafana出图_alert告警 1 使用炫酷的grafana出图 1.1 部署grafana 1.1.1 准备镜像 1.1 ...
- Prometheus+Grafana企业监控系统
Prometheus+Grafana企业监控系统 作者 刘畅 实验配置: 主机名称 Ip地址 controlnode 172.16.1.70/24 slavenode1 172.16.1.71/24 ...
- kubernetes(k8s) Prometheus+grafana监控告警安装部署
主机数据收集 主机数据的采集是集群监控的基础:外部模块收集各个主机采集到的数据分析就能对整个集群完成监控和告警等功能.一般主机数据采集和对外提供数据使用cAdvisor 和node-exporter等 ...
- [转帖]Prometheus+Grafana监控Kubernetes
原博客的位置: https://blog.csdn.net/shenhonglei1234/article/details/80503353 感谢原作者 这里记录一下自己试验过程中遇到的问题: . 自 ...
- k8s集群监控 cadvisor/exporter+prometheus+grafana
### k8s监控处理 ### 1.cadvisor/exporter+prometheus+grafana 安装#### 1.1 配置nfs安装```shellubuntu: nfs 服务器 apt ...
随机推荐
- js做四则运算时,精度丢失问题及解决方法
一.前言:这个问题可以说是程序员必踩的坑,因此网上针对该问题的分析有很多也很详细,解决方法也比较统一,写法也是大同小异,本以为预期效果真能如他们所说是完美的,然而效果却是差强人意. 二.问题:首先,先 ...
- Android学习day03【跑马灯】
这个学习内容很简单,说一下自己笨蛋的点吧 要实现这种情况,我始终没有办法实现(也就是跑马灯,图片没办法显示) 后来发现 android:layout_width="wrap_content& ...
- Chrome扩展的核心:manifest 文件(中)
大家好,我是 dom 哥.我正在写关于 Chrome 扩展开发的系列文章,感兴趣的可以 点个小星星 . 在上一篇中已经完成了 Chrome 扩展的雏形,本篇接着介绍 manifest 中的可选字段,完 ...
- Mybatis-Flex之增、删、改
方法全解 (1) INSERT BaseMapper 的接口提供了 insert 和 insertBatch 方法,用于新增数据: insert(entity):插入实体类数据,不忽略 null 值. ...
- 【笔记整理】请求携带cookie的两种方法
""" 方法一:在请求头header中携带Cookie请求头信息(因为本身Cookie就是用请求头传递的....) 方法二:使用cookie参数传递cookie字典 &q ...
- Scrapy-CrawlSpider爬虫类使用案例
CrawlSpider类型的爬虫会根据指定的rules规则自动找到url比自动爬取. 优点:适合整站爬取,自动翻页爬取 缺点:比较难以通过meta传参,只适合一个页面就能拿完数据的. import s ...
- GPT Zero 是什么?
from https://openaigptguide.com/gptzero/ 在人工智能技术飞速发展的今天,人们对于文字内容的准确性和可信度要求越来越高.例如在学术研究领域,防止抄袭和造假是非常重 ...
- MES数据追溯常遇问题及解决方法
MES数据追溯常遇问题及解决方法: 在实际数字化工厂MES应用过程,由于设计或使用不当,数据追溯过程中也可能会存在诸多问题,常遇问题包括:1. 数据质量问题 可能存在数据录入错误.数据缺失或不完整等情 ...
- 聊聊流式数据湖Paimon(五)
从Demo入手,了解Paimon/Flink项目搭建的全过程.记录下采坑之旅. 创建Flink项目 在IDEA中创建Flink项目,由于没有Flink的archetype,因此需要手动创建一下. 参考 ...
- 常用API之IP定位地区
常用API之IP定位地区 高德地图API https://lbs.amap.com/api/webservice/guide/api/ipconfig 百度地图API https://lbsyun.b ...
