Model Inversion Attack Paper Indexpage
Paper [1]:
White-box neural network attack, adversaries have full access to the model. Using Gradient Descent going back to update the input so that reconstructing the original training data.
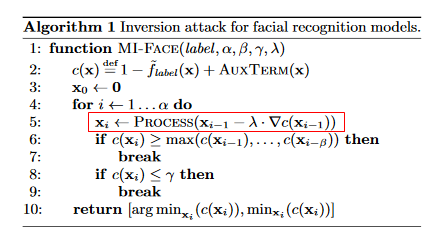
About black-box attack, they mentioned using numeric gradient approximation.
Question: If the model does not overfit the dataset, cannot recover the training data.
Paper [2]:
Proposed black-box attack via online ML-as-a-S platform, targeting to extract parameters from simple structures by solving equations. Condifence values is the key to solve these equations.
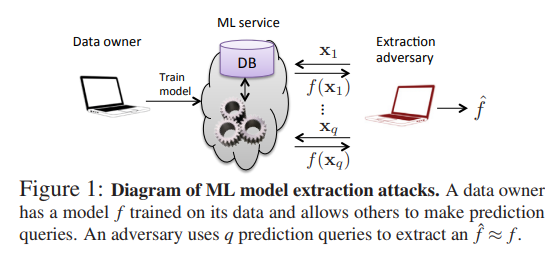
Question: However, this method seems like brute force, and it would be tough when the type and structure of model are unknown or really complex. Ex. they query 10,000 times to steal a neural network, which will be identified as hacking activity in real environment. (or too expensive to query online service)
[1] M. Fredrikson, S. Jha and T. Ristenpart, "Model inversion attacks that exploit confidence information and basic countermeasures," in 2015, . DOI: 10.1145/2810103.2813677.
[2] Florian Tramer, Fan Zhang, Ari Juels, Michael K. Reiter, and Thomas Ristenpart. Stealing machine learning models via prediction apis. In 25th USENIX Security Symposium, USENIX Security 16, Austin, TX, USA, August 10-12, 2016., pages 601-618, 2016. Presentation: https://www.youtube.com/watch?time_continue=26&v=qGjzmEzPkiI
Model Inversion Attack Paper Indexpage的更多相关文章
- Summary on Visual Tracking: Paper List, Benchmarks and Top Groups
Summary on Visual Tracking: Paper List, Benchmarks and Top Groups 2018-07-26 10:32:15 This blog is c ...
- 【Paper】智能家居
From: http://liudongdong1.github.io keyword: Human-centered computing , LoRa Paper: WIDESEE WIDESEE: ...
- Attention and Augmented Recurrent Neural Networks
Attention and Augmented Recurrent Neural Networks CHRIS OLAHGoogle Brain SHAN CARTERGoogle Brain Sep ...
- linux 并发 RCU
What is RCU, Fundamentally? https://lwn.net/Articles/262464/ If you can fill the unforgiving secondw ...
- [笔记]Practical Lessons from Predicting Clicks on Ads at Facebook
ABSTRACT 这篇paper中作者结合GBDT和LR,取得了很好的效果,比单个模型的效果高出3%.随后作者研究了对整体预测系统产生影响的几个因素,发现Feature+Model的贡献程度最大,而其 ...
- 用Caffe生成对抗样本
同步自我的知乎专栏:https://zhuanlan.zhihu.com/p/26122612 上篇文章 瞎谈CNN:通过优化求解输入图像 - 知乎专栏 中提到过对抗样本,这篇算是针对对抗样本的一个小 ...
- Unity文档阅读 第二章 依赖注入
Introduction 介绍Chapter 1 outlines how you can address some of the most common requirements in enterp ...
- Unity Rain Ai 插件基本使用(二)
前言 在前面的教程中我们已经基本实现了路径导航和障碍物规避. 但是这样我们并没有让我们的角色学会思考,他只是机械的去完成一些步骤,这并不能体现Rain插件的智能. 一个角色他应该有多个不同的状态,待机 ...
- 机器学习算法GBDT
http://www-personal.umich.edu/~jizhu/jizhu/wuke/Friedman-AoS01.pdf https://www.cnblogs.com/bentuwuyi ...
随机推荐
- Redis怎么做持久化
1.redis持久化的两种方式 2.两种持久化方式区别 3.两种持久化方式的使用场景 1.Redis 是内存型数据库,一般来用作缓存.保存在内存的数据有一个特点, 就是断电消失,因此一旦 Redis ...
- 分岔 Bifurcations
1. saddle-node bifurcation 2. transcritical bifurcation 3.pitchfork bifurcation 4. Hopf bifurcation ...
- 【leetcode】560. Subarray Sum Equals K
题目如下:解题思路:本题的关键在于题目限定了是连续的数组,我们用一个dp数组保存第i位到数组末位的和.例如nums = [1,1,1],那么dp = [3,2,1], dp[i]表示nums[i]+n ...
- 安装vue-cli脚手架项目
1,下载安装node.官网下载后,重新打开cmd再打开. 命令:node -v检测版本. 2,安装vue-cli: 命令:npm install --global vue-cli .根据安装情况,会 ...
- delphi 10.3 控件遮挡 webbrowser
听闻10.3的新特性之一,webbrowser可以被其他控件遮挡, 在等待10.3.1出来后才开始来尝鲜, 但在webbrowser上添加控件后, 发现控件还是被挡住了, 研究发现需要将控件的cont ...
- plt.imshow()为什么不能显示同时显两张照片
在编程的过程中发现plt.imshow()不能同时显示两张照片,如果有两条plt.imshow()语句处于一前一后的位置,那么程序运行后只会显示后面的图片.如果想让每一张图片都显示出来,需要在每一个p ...
- Online Game Development in C++ 第五部分总结
I. 教程案例框架描述 该套教程做了一个简单的汽车控制系统,没有用到物理模拟.用油门和方向控制汽车的加速度和转向,同时还有一些空气阻力和滚动摩擦力的设置增加了真实感.汽车的位置是通过加速度和时间等计算 ...
- 使用@Test报java.lang.NullPointerException at org.eclipse.jdt.internal.junit4.runner.SubForestFilter.shouldRun(SubForestFilter.java:81)异常
对公司的项目进行二次开发时,在调试过程中用到@Test注解,运行使发现控制台报空指针异常,如图: 参考网上相应资料后,删除项目中自带的Junit4.jar,然后使用eclipse开发工具自带的Juni ...
- java.lang.OutOfMemoryError:GC overhead limit exceeded解决方
Tomcat异常信息: Exception in thread "main" java.lang.OutOfMemoryError: GC overhead limit excee ...
- paper about spring
一.解析用户原始信息的json文件 #!/usr/bin/python # -*- coding=utf-8 -*- import os import sys import json def main ...
