Internet History, Technology and Security (Week 9)
Week 9
Security: Web Security
We are now on the second to last week of the class and finishing up our look at Internet Security. You can also see the final exam and its due date. The due date of the final exam signals the end of the class.
This week, we’ll be covering web security. We apply the basic ideas of encryption and signing to who we actually secure the connections that we use on today’s Web and Internet.
Securing Web Connections
Security Public/Private Key - Secure Sockets
本节介绍公开密钥加密。在前几次讲座中一直遵循着机密和完整性两个主题,机密是隐藏的,不能将其泄露给哪些你不想展示的人。
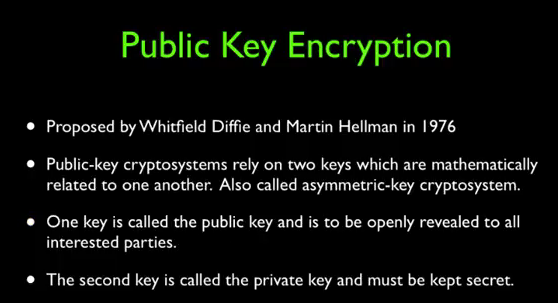
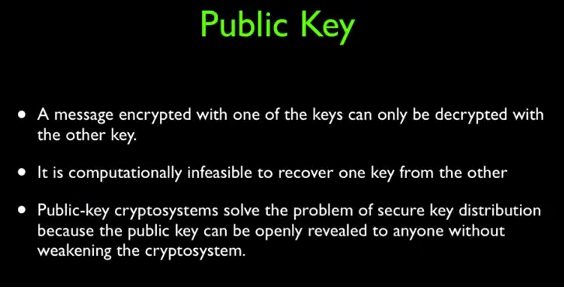
公钥加密被认为是解决这个问题的一种非常优雅的解决方案,它是由Diffie和Hellman在1976年提出的。依赖于两个密钥,且是不对称的,这就意味着我们不能像之前小节那样使用相同的密钥来进行加密。公钥实际上不需要任何保护,公钥用于消息的加密,而私钥则用于消息的解密。他们在数学上是相互关联的。
如果你想使用私密公钥加密,你必须生成一对(公钥和私钥)。
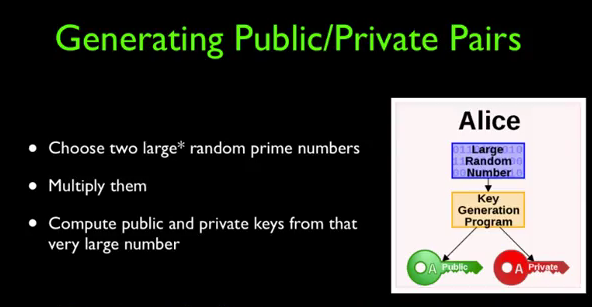
选择两个非常大的随机数,然后将它们相乘。你可以从中计算得到公钥和密钥,公钥和密钥实际上是基于两个质数,所以想要找到他们形如大海捞针。
And so the public and private key is really based on these two prime numbers.
这里老师给我们做了一个演示:
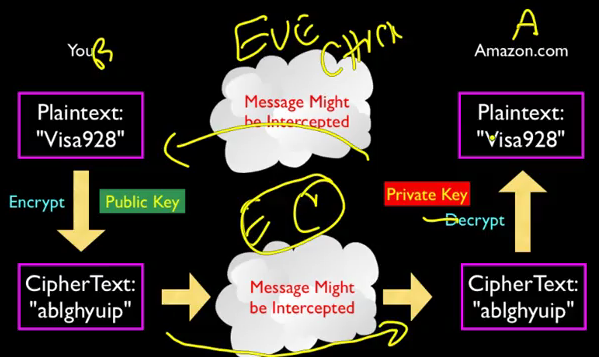
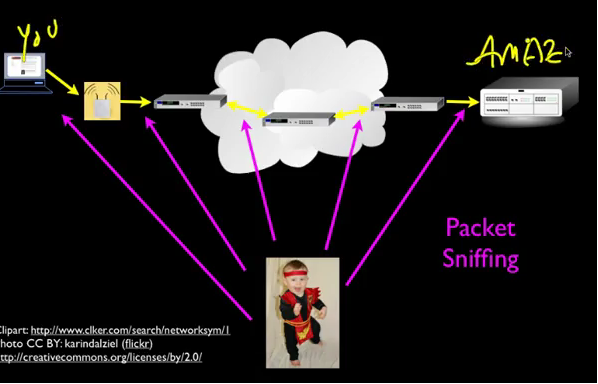
The encrypted text finds its way through all these things. And it come in encrypted. And it actually doesn't get encrypted, until it's sort of right at the point where Amazon's web server that's going to actually charge your credit card. So, this is actually beautifully elegant. In that, the rest of the network is blissfully unaware, that any encryption is happening. It's just moving the data. So, this did not require any change. Again the beauty of the layer of architecture. Did not require any change, sort of below the transport layer. And as a matter of fact, all of the sequencing and re-transmission that happens in the TCP layer. That happens with the encrypted stuff too because it's just encrypted. It's just text. It's gibberish text, it's not the original visa card number that you're sending. You're sending 123 and out comes, you know, wxy, the wxy just goes. It's re-transmitted. All this crap just works, it's like, beautiful. It's a beautiful thing. It's absolutely a beautiful thing. Then it's just like this mini layer kind of between, it's like the top slice of the transport layer. That's how I'm drawing it right here. It's like this little kind of top extra little thing, that says you know what, we're going to transport, actually help me out and give me some encryption while we're at it. And there's all kinds of cool stuff that goes back and forth. The public and private keys get exchanged.
你不得不假定你连接的过程是不安全的。
But, but basically, you know, we want to distrust all of this, okay?
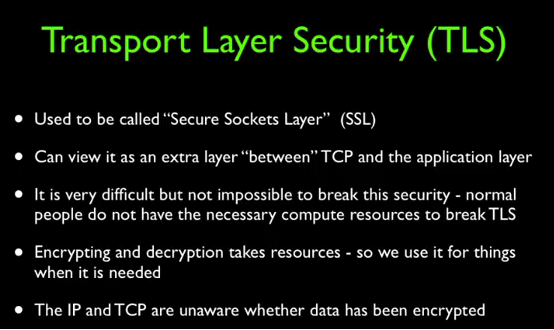
这种思想就是传输层安全(Transport Layer Security),也称作SSL、HTTPS,位于传输层和应用层之间。

Identity on the Web
Security - Integrity and Certificate Authorities
我们如何知道与之对话的是谁呢?是亚马逊还是coursera?可以通过查看浏览器的顶部,通常这里会i有一个指示只想安全连接,可以单机此链接来查看一些信息,这就叫做证书信息。有一个GoDaddy来负责检查Coursera的ID并说,嘿你一定是Coursera的首席执行官,否则我不会给你这个签名的私钥。
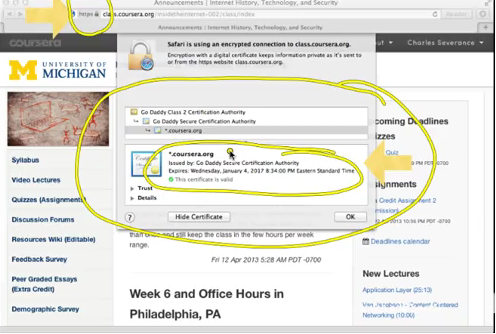
因此这就是一个获得私钥签名的过程,也是一宗确保和其他人交流的方法。所谓的数字证书也被称为签名私钥。
数字证书由第三方权威机构颁布,这些权威机构也是逐渐建立起信任的。
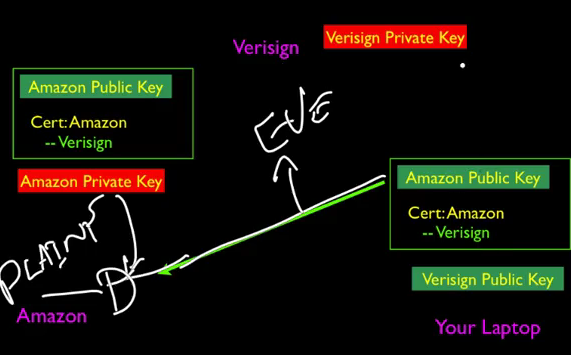
So, if you think this whole thing through, this, Eve was watching the whole time. We sent a public key. We signed and returned a public key. Then we sent the public key to your laptop. We verified the public key. And the whole time Eve is sort of watching all this information and she is powerless to break it.
最后总结一下:
So, that sort of brings us to the conclusion of this, these last couple of lectures have been about message confidentially. And that's protecting the contents from being revealed. We use encrypting and decrypting for that. And then we have message digest. And, sur, to sign things. We've signed messages, we've signed certificates, we've signed many things, and those are important. And we talked about both sort of, shared key, and secret key, where you have to get together. And agree on a key which is a symmetric key that's used for encrypting and decrypting. And then you have the public private key which is the asymmetric. Which is one key is used for encrypting and the other key is used for decrypting. And you can freely show the encrypting key because it gives very little information. Although, it is mathematically possible, but difficult to decrypt public private key message. So, that kinds of suns up, kind of sums up our lecture on public private keys and I hope you find it valuable. See you on the net.

Internet History, Technology and Security (Week 9)的更多相关文章
- Internet History, Technology and Security (Get Started)
Abstract 课程名称:互联网的历史.技术和安全 coursera地址 制作方:密歇根大学(University of Michigan) 教师:Charles Severance, Associ ...
- Internet History,Technology and Security
Internet History,Technology and Security(简单记录) First Week High Stakes Research in Computing,and Comm ...
- Internet History,Technology,and Security - History Through Supercomputing(Week2)
时间飞逝,一周又过去了,这周我们来到了Internet History, Technology and Security (Week 2)的学习,从标题就可以看出,这周主要是介绍“互联网”雏形的诞生. ...
- Internet History, Technology and Security (Week 2)
Week 2 History: The First Internet - NSFNet Welcome to week 2! This week, we'll be covering the hist ...
- Coursera: Internet History, Technology, and Security
课程网址:https://www.coursera.org/learn/internet-history 学习笔记: Week 1: History - Dawn of Early Computing ...
- Internet History, Technology, and Security(week1)——History: Dawn of Electronic Computing
前言: 第一次进行课程学习,在反复观看视频和查找字典翻译理解后选出了视频中个人认为较重要的概念,以下并不按照逐句翻译,中文概括大意余下自由发挥,对老师想要告诉我们的历史有一个初步的了解,顺便锻炼以下英 ...
- Internet History, Technology and Security (Week5.1)
Week5 The Transport layer is built on the Internetwork layer and is what makes our network connectio ...
- Internet History, Technology and Security (Week 4)
Week 4 History: Commercialization and Growth We are now moving into Week 4! This week, we will be co ...
- Internet History,Technology,and Security - Technology: Internets and Packets (Week5)
Week5 Technology: Internets and Packets Welcome to Week 5! This week, we’ll be covering internets an ...
随机推荐
- SSM整合思路
引自网友: https://zhuanlan.zhihu.com/p/23917781
- 【python3】爬取简书评论生成词云
一.起因: 昨天在简书上看到这么一篇文章<中国的父母,大都有毛病>,看完之后个人是比较认同作者的观点. 不过,翻了下评论,发现评论区争议颇大,基本两极化.好奇,想看看整体的评论是个什么样, ...
- python基础学习1-三元表达式和lambda表达式
#!/usr/bin/env python # -*- coding:utf-8 -*- 三元运算 if else 的简写 name ="alex" if 1==1 else &q ...
- 解读Web应用程序安全性问题的本质
转自 http://blog.csdn.net/iwebsecurity/article/details/1688304 相信大家都或多或少的听过关于各种Web应用安全漏洞,诸如:跨site脚本攻击( ...
- 2-5 re模块练习题
1 练习: 1.验证手机号是否合法 2.验证邮箱是否合法 3.开发一个简单的python计算器,实现加减乘除及拓号优先级解析 用户输入 1 - 2 * ( (60-30 +(-40/5) * (9-2 ...
- 亲手搭建一个基于Asp.Net WebApi的项目基础框架4
实现目的:配置website端与服务端对接 1:配置好各项配置文件 2:server端编写接口客户端调用 1.1首先配置文件有log4的配置文件,有config的配置文件,还有服务列表的配置文件 首先 ...
- bootstrap框架中data-toggle="tab"属性会取消a标签默认行为
这几天做公司项目用了bootstrap框架,在用导航组件的过程中,我发现在a标签里面添加data-toggle="tab"属性之后,这个a标签会失去默认行为,点击a标签的时候不会跳 ...
- yolo算法框架使用二
6,voc数据集训练模型 1)下载数据集 官网提供一些voc数据,是基于2007年到2012年的,你可以通过以下地址下载到: wget https://pjreddie.com/media/files ...
- Tomcat学习(一)------部署Web应用方法总结
Tomcat部署Web应用方法总结 在Tomcat中部署Java Web应用程序有两种方式:静态部署和动态部署. 在下文中$CATALINA_HOME指的是Tomcat根目录. 一.静态部署 静态部署 ...
- 学习java常见dos命令
在java基础学习阶段时一般会在dos命令行下操作文件,这里列出一些常用命令. 打开DOS控制台的方式 按win+r 再输入 cmd 然后回车. 常用DOS命令 d: 回车 盘符切换 (盘符加冒号) ...