Kubernetes实战总结 - Ingress选型与应用
一、概述
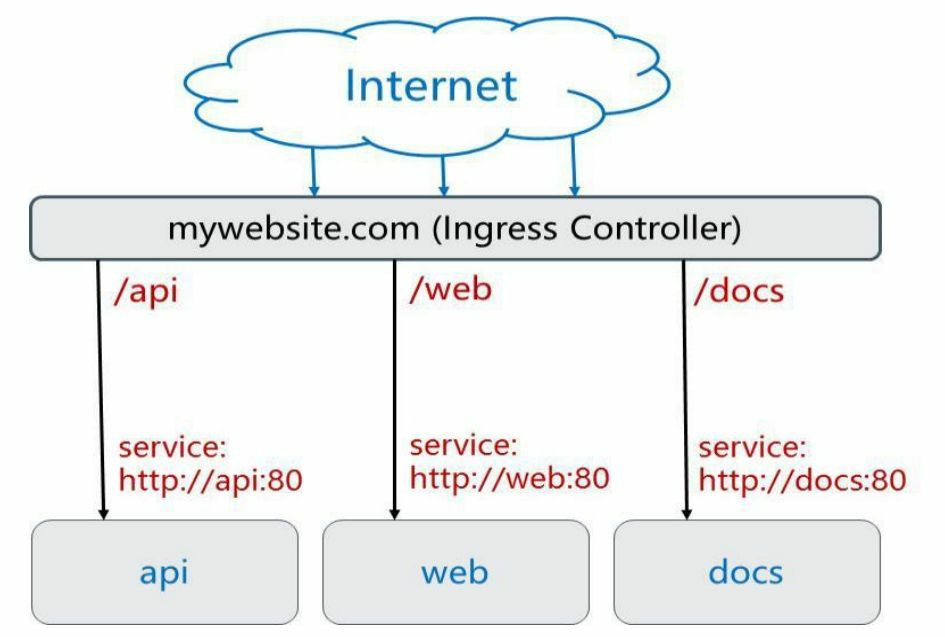
Ingress 是对集群中服务的外部访问进行管理的 API 对象,可以提供负载均衡、SSL 终结和基于名称的虚拟托管。
典型的访问方式是 HTTP,用于将不同URL的访问请求转发到后端不同的 Service,以实现HTTP层的业务路由机制。
Kubernetes使用了一个Ingress策略定义和一个具体的 Ingress Controller,两者结合并实现了一个完整的Ingress负载均衡器。
使用Ingress进行负载分发时,Ingress Controller基于Ingress规则将客户端请求直接转发到Service对应的后端Endpoint(Pod)上,这样会跳过kube-proxy的转发功能,kube-proxy不再起作用。
Ingress 不会公开任意端口或协议。 将 HTTP 和 HTTPS 以外的服务公开到 Internet 时,通常使用 Service.Type=NodePort 或者 Service.Type=LoadBalancer 类型的服务。
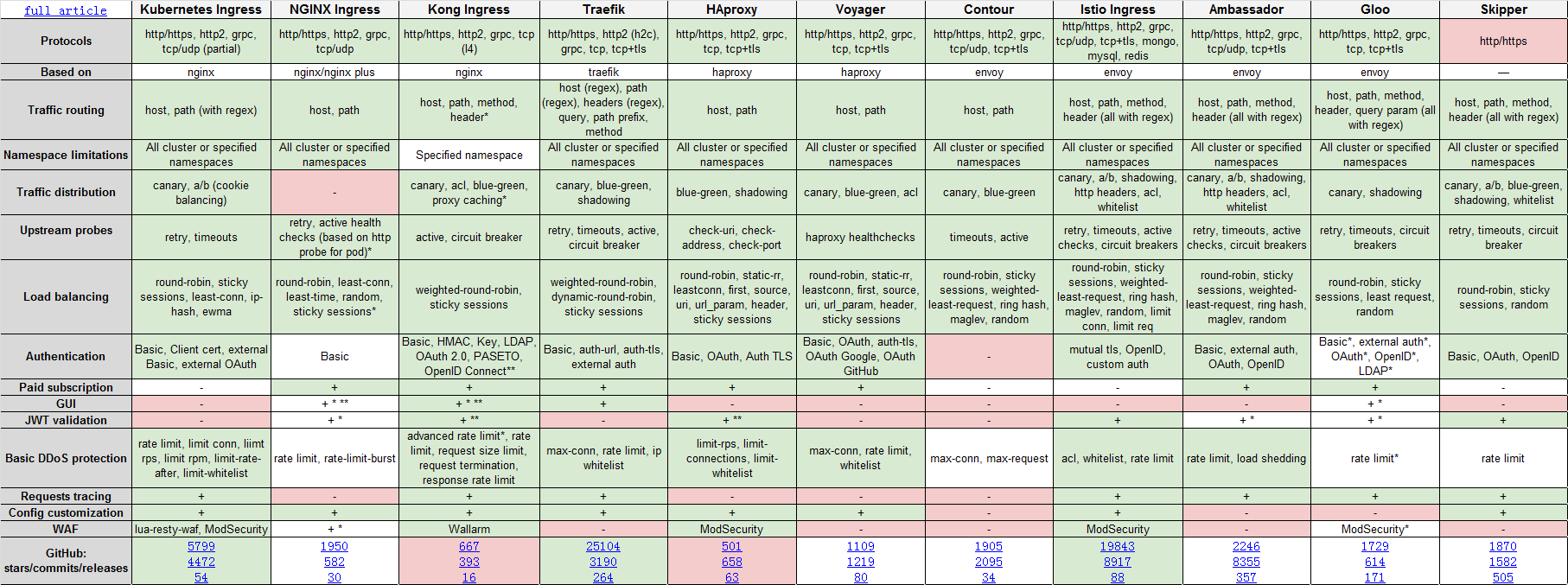
二、常见控制器
Kubernetes Ingress 作为"官方"控制器,它是由社区基于NGINX Web服务器开发的,并补充了一组用于实现额外功能的Lua插件。
NGINX Ingress 这是NGINX开发人员的官方产品,NGINX控制器具有很高的稳定性,持续的向后兼容性,没有任何第三方模块,并且由于消除了Lua代码而保证了较高的速度(与官方控制器相比)。
Kong Ingress由Kong Inc开发,并且有两个版本:商业版本和免费版本。Kong Ingress建立在NGINX之上,并增加了扩展其功能的Lua模块。
HAProxy Ingress 由HAProxy开发,它提供了“软”配置更新(无流量丢失),基于DNS的服务发现,通过API的动态配置。
Traefik 是一个全功能的 ingress 控制器 (Let's Encrypt,secrets,http2,websocket),并且它也有来自 Containous 的商业支持。
Istio 是IBM,Google和Lyft(Envoy的原始作者)的联合项目,它是一个全面的服务网格解决方案。它不仅可以管理所有传入的外部流量(作为Ingress控制器),还可以控制集群内部的所有流量。
在幕后,Istio将Envoy用作每种服务的辅助代理。从本质上讲,它是一个可以执行几乎所有操作的大型处理器。其中心思想是最大程度的控制,可扩展性,安全性和透明性。
更多参考 >>> Kubernetes的Ingress控制器比较
三、推荐控制器
1) 如果刚开始接触Ingress,项目并发和性能要求也不高,那我推荐使用官方的Ingress控制器。毕竟官方产品对k8s本身支持无可厚非,并且配置和部署都比较简单。
① 安装部署指导:https://kubernetes.github.io/ingress-nginx/deploy/
kubectl apply -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/master/deploy/static/provider/baremetal/deploy.yaml
② 当然你也可以直接复制以下修改好的文件:


apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
---
# Source: ingress-nginx/templates/controller-serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx
namespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx-controller
namespace: ingress-nginx
data:
---
# Source: ingress-nginx/templates/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
name: ingress-nginx
namespace: ingress-nginx
rules:
- apiGroups:
- ''
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ''
resources:
- nodes
verbs:
- get
- apiGroups:
- ''
resources:
- services
verbs:
- get
- list
- update
- watch
- apiGroups:
- extensions
- networking.k8s.io # k8s 1.14+
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ''
resources:
- events
verbs:
- create
- patch
- apiGroups:
- extensions
- networking.k8s.io # k8s 1.14+
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io # k8s 1.14+
resources:
- ingressclasses
verbs:
- get
- list
- watch
---
# Source: ingress-nginx/templates/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
name: ingress-nginx
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress-nginx
subjects:
- kind: ServiceAccount
name: ingress-nginx
namespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx
namespace: ingress-nginx
rules:
- apiGroups:
- ''
resources:
- namespaces
verbs:
- get
- apiGroups:
- ''
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ''
resources:
- services
verbs:
- get
- list
- update
- watch
- apiGroups:
- extensions
- networking.k8s.io # k8s 1.14+
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- extensions
- networking.k8s.io # k8s 1.14+
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io # k8s 1.14+
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- ''
resources:
- configmaps
resourceNames:
- ingress-controller-leader-nginx
verbs:
- get
- update
- apiGroups:
- ''
resources:
- configmaps
verbs:
- create
- apiGroups:
- ''
resources:
- endpoints
verbs:
- create
- get
- update
- apiGroups:
- ''
resources:
- events
verbs:
- create
- patch
---
# Source: ingress-nginx/templates/controller-rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress-nginx
subjects:
- kind: ServiceAccount
name: ingress-nginx
namespace: ingress-nginx
---
# Source: ingress-nginx/templates/controller-service-webhook.yaml
apiVersion: v1
kind: Service
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx-controller-admission
namespace: ingress-nginx
spec:
type: ClusterIP
ports:
- name: https-webhook
port: 443
targetPort: webhook
selector:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/component: controller
---
# Source: ingress-nginx/templates/controller-service.yaml
apiVersion: v1
kind: Service
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx-controller
namespace: ingress-nginx
spec:
type: NodePort
ports:
- name: http
port: 80
protocol: TCP
targetPort: http
- name: https
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/component: controller
---
# Source: ingress-nginx/templates/controller-deployment.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: controller
name: ingress-nginx-controller
namespace: ingress-nginx
spec:
selector:
matchLabels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/component: controller
revisionHistoryLimit: 10
minReadySeconds: 0
template:
metadata:
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/component: controller
spec:
dnsPolicy: ClusterFirst
containers:
- name: controller
image: registry.cn-shanghai.aliyuncs.com/leozhanggg/ingress/nginx-ingress-controller:0.32.0
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
args:
- /nginx-ingress-controller
- --election-id=ingress-controller-leader
- --ingress-class=nginx
- --configmap=ingress-nginx/ingress-nginx-controller
- --validating-webhook=:8443
- --validating-webhook-certificate=/usr/local/certificates/cert
- --validating-webhook-key=/usr/local/certificates/key
securityContext:
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
runAsUser: 101
allowPrivilegeEscalation: true
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
livenessProbe:
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
timeoutSeconds: 1
successThreshold: 1
failureThreshold: 3
readinessProbe:
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
timeoutSeconds: 1
successThreshold: 1
failureThreshold: 3
ports:
- name: http
containerPort: 80
protocol: TCP
- name: https
containerPort: 443
protocol: TCP
- name: webhook
containerPort: 8443
protocol: TCP
volumeMounts:
- name: webhook-cert
mountPath: /usr/local/certificates/
readOnly: true
resources:
requests:
cpu: 100m
memory: 90Mi
serviceAccountName: ingress-nginx
terminationGracePeriodSeconds: 300
volumes:
- name: webhook-cert
secret:
secretName: ingress-nginx-admission
---
# Source: ingress-nginx/templates/admission-webhooks/validating-webhook.yaml
apiVersion: admissionregistration.k8s.io/v1beta1
kind: ValidatingWebhookConfiguration
metadata:
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
name: ingress-nginx-admission
namespace: ingress-nginx
webhooks:
- name: validate.nginx.ingress.kubernetes.io
rules:
- apiGroups:
- extensions
- networking.k8s.io
apiVersions:
- v1beta1
operations:
- CREATE
- UPDATE
resources:
- ingresses
failurePolicy: Fail
clientConfig:
service:
namespace: ingress-nginx
name: ingress-nginx-controller-admission
path: /extensions/v1beta1/ingresses
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: ingress-nginx-admission
annotations:
helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
rules:
- apiGroups:
- admissionregistration.k8s.io
resources:
- validatingwebhookconfigurations
verbs:
- get
- update
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: ingress-nginx-admission
annotations:
helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress-nginx-admission
subjects:
- kind: ServiceAccount
name: ingress-nginx-admission
namespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-createSecret.yaml
apiVersion: batch/v1
kind: Job
metadata:
name: ingress-nginx-admission-create
annotations:
helm.sh/hook: pre-install,pre-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
spec:
template:
metadata:
name: ingress-nginx-admission-create
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
spec:
containers:
- name: create
image: registry.cn-shanghai.aliyuncs.com/leozhanggg/ingress/kube-webhook-certgen:v1.2.0
imagePullPolicy: IfNotPresent
args:
- create
- --host=ingress-nginx-controller-admission,ingress-nginx-controller-admission.ingress-nginx.svc
- --namespace=ingress-nginx
- --secret-name=ingress-nginx-admission
restartPolicy: OnFailure
serviceAccountName: ingress-nginx-admission
securityContext:
runAsNonRoot: true
runAsUser: 2000
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-patchWebhook.yaml
apiVersion: batch/v1
kind: Job
metadata:
name: ingress-nginx-admission-patch
annotations:
helm.sh/hook: post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
spec:
template:
metadata:
name: ingress-nginx-admission-patch
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
spec:
containers:
- name: patch
image: registry.cn-shanghai.aliyuncs.com/leozhanggg/ingress/kube-webhook-certgen:v1.2.0
imagePullPolicy:
args:
- patch
- --webhook-name=ingress-nginx-admission
- --namespace=ingress-nginx
- --patch-mutating=false
- --secret-name=ingress-nginx-admission
- --patch-failure-policy=Fail
restartPolicy: OnFailure
serviceAccountName: ingress-nginx-admission
securityContext:
runAsNonRoot: true
runAsUser: 2000
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: ingress-nginx-admission
annotations:
helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
rules:
- apiGroups:
- ''
resources:
- secrets
verbs:
- get
- create
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/rolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: ingress-nginx-admission
annotations:
helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress-nginx-admission
subjects:
- kind: ServiceAccount
name: ingress-nginx-admission
namespace: ingress-nginx
---
# Source: ingress-nginx/templates/admission-webhooks/job-patch/serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: ingress-nginx-admission
annotations:
helm.sh/hook: pre-install,pre-upgrade,post-install,post-upgrade
helm.sh/hook-delete-policy: before-hook-creation,hook-succeeded
labels:
helm.sh/chart: ingress-nginx-2.0.3
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/version: 0.32.0
app.kubernetes.io/managed-by: Helm
app.kubernetes.io/component: admission-webhook
namespace: ingress-nginx
kube-ingress.yaml
③ 执行以上部署文件,等待部署完成,修改Service暴露类型:
[root@k8s-32 ~]# kubectl get pod -n ingress-nginx
NAME READY STATUS RESTARTS AGE
ingress-nginx-admission-create-mw7mv 0/1 Completed 0 23h
ingress-nginx-admission-patch-k2zwl 0/1 Completed 1 23h
ingress-nginx-controller-df8b8bcbd-klmlc 1/1 Running 0 23h
[root@k8s-32 ~]# kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.111.132.119 <none> 80:30467/TCP,443:30002/TCP 23h
ingress-nginx-controller-admission ClusterIP 10.100.33.182 <none> 443/TCP 23h
2) 如果你对性能比较高,功能要求不多,那我推荐使用Nginx-ingress。由于Nginx-ingress消除了Lua代码而保证了较高的速度(与官方控制器相比),而在高并发下Nginx-ingress性能也是优于Haproxy-ingress的。
① 安装部署参考:https://docs.nginx.com/nginx-ingress-controller/installation/installation-with-manifests/
② 当然你也可以直接复制以下修改好的文件:


# Source: kubernetes-ingress/deployments/common/ns-and-sa.yaml
apiVersion: v1
kind: Namespace
metadata:
name: nginx-ingress
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress
namespace: nginx-ingress
---
# Source: kubernetes-ingress/deployments/rbac/rbac.yaml
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: nginx-ingress
rules:
- apiGroups:
- ""
resources:
- services
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- secrets
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- configmaps
verbs:
- get
- list
- watch
- update
- create
- apiGroups:
- ""
resources:
- pods
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- extensions
resources:
- ingresses
verbs:
- list
- watch
- get
- apiGroups:
- "extensions"
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- k8s.nginx.org
resources:
- virtualservers
- virtualserverroutes
- globalconfigurations
- transportservers
verbs:
- list
- watch
- get
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: nginx-ingress
subjects:
- kind: ServiceAccount
name: nginx-ingress
namespace: nginx-ingress
roleRef:
kind: ClusterRole
name: nginx-ingress
apiGroup: rbac.authorization.k8s.io
---
# Source: kubernetes-ingress/deployments/common/default-server-secret.yaml
apiVersion: v1
kind: Secret
metadata:
name: default-server-secret
namespace: nginx-ingress
type: Opaque
data:
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUN2akNDQWFZQ0NRREFPRjl0THNhWFhEQU5CZ2txaGtpRzl3MEJBUXNGQURBaE1SOHdIUVlEVlFRRERCWk8KUjBsT1dFbHVaM0psYzNORGIyNTBjbTlzYkdWeU1CNFhEVEU0TURreE1qRTRNRE16TlZvWERUSXpNRGt4TVRFNApNRE16TlZvd0lURWZNQjBHQTFVRUF3d1dUa2RKVGxoSmJtZHlaWE56UTI5dWRISnZiR3hsY2pDQ0FTSXdEUVlKCktvWklodmNOQVFFQkJRQURnZ0VQQURDQ0FRb0NnZ0VCQUwvN2hIUEtFWGRMdjNyaUM3QlBrMTNpWkt5eTlyQ08KR2xZUXYyK2EzUDF0azIrS3YwVGF5aGRCbDRrcnNUcTZzZm8vWUk1Y2Vhbkw4WGM3U1pyQkVRYm9EN2REbWs1Qgo4eDZLS2xHWU5IWlg0Rm5UZ0VPaStlM2ptTFFxRlBSY1kzVnNPazFFeUZBL0JnWlJVbkNHZUtGeERSN0tQdGhyCmtqSXVuektURXUyaDU4Tlp0S21ScUJHdDEwcTNRYzhZT3ExM2FnbmovUWRjc0ZYYTJnMjB1K1lYZDdoZ3krZksKWk4vVUkxQUQ0YzZyM1lma1ZWUmVHd1lxQVp1WXN2V0RKbW1GNWRwdEMzN011cDBPRUxVTExSakZJOTZXNXIwSAo1TmdPc25NWFJNV1hYVlpiNWRxT3R0SmRtS3FhZ25TZ1JQQVpQN2MwQjFQU2FqYzZjNGZRVXpNQ0F3RUFBVEFOCkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQWpLb2tRdGRPcEsrTzhibWVPc3lySmdJSXJycVFVY2ZOUitjb0hZVUoKdGhrYnhITFMzR3VBTWI5dm15VExPY2xxeC9aYzJPblEwMEJCLzlTb0swcitFZ1U2UlVrRWtWcitTTFA3NTdUWgozZWI4dmdPdEduMS9ienM3bzNBaS9kclkrcUI5Q2k1S3lPc3FHTG1US2xFaUtOYkcyR1ZyTWxjS0ZYQU80YTY3Cklnc1hzYktNbTQwV1U3cG9mcGltU1ZmaXFSdkV5YmN3N0NYODF6cFErUyt1eHRYK2VBZ3V0NHh3VlI5d2IyVXYKelhuZk9HbWhWNThDd1dIQnNKa0kxNXhaa2VUWXdSN0diaEFMSkZUUkk3dkhvQXprTWIzbjAxQjQyWjNrN3RXNQpJUDFmTlpIOFUvOWxiUHNoT21FRFZkdjF5ZytVRVJxbStGSis2R0oxeFJGcGZnPT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
tls.key: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBdi91RWM4b1JkMHUvZXVJTHNFK1RYZUprckxMMnNJNGFWaEMvYjVyYy9XMlRiNHEvClJOcktGMEdYaVN1eE9ycXgrajlnamx4NXFjdnhkenRKbXNFUkJ1Z1B0ME9hVGtIekhvb3FVWmcwZGxmZ1dkT0EKUTZMNTdlT1l0Q29VOUZ4amRXdzZUVVRJVUQ4R0JsRlNjSVo0b1hFTkhzbysyR3VTTWk2Zk1wTVM3YUhudzFtMApxWkdvRWEzWFNyZEJ6eGc2clhkcUNlUDlCMXl3VmRyYURiUzc1aGQzdUdETDU4cGszOVFqVUFQaHpxdmRoK1JWClZGNGJCaW9CbTVpeTlZTW1hWVhsMm0wTGZzeTZuUTRRdFFzdEdNVWozcGJtdlFmazJBNnljeGRFeFpkZFZsdmwKMm82MjBsMllxcHFDZEtCRThCay90elFIVTlKcU56cHpoOUJUTXdJREFRQUJBb0lCQVFDZklHbXowOHhRVmorNwpLZnZJUXQwQ0YzR2MxNld6eDhVNml4MHg4Mm15d1kxUUNlL3BzWE9LZlRxT1h1SENyUlp5TnUvZ2IvUUQ4bUFOCmxOMjRZTWl0TWRJODg5TEZoTkp3QU5OODJDeTczckM5bzVvUDlkazAvYzRIbjAzSkVYNzZ5QjgzQm9rR1FvYksKMjhMNk0rdHUzUmFqNjd6Vmc2d2szaEhrU0pXSzBwV1YrSjdrUkRWYmhDYUZhNk5nMUZNRWxhTlozVDhhUUtyQgpDUDNDeEFTdjYxWTk5TEI4KzNXWVFIK3NYaTVGM01pYVNBZ1BkQUk3WEh1dXFET1lvMU5PL0JoSGt1aVg2QnRtCnorNTZud2pZMy8yUytSRmNBc3JMTnIwMDJZZi9oY0IraVlDNzVWYmcydVd6WTY3TWdOTGQ5VW9RU3BDRkYrVm4KM0cyUnhybnhBb0dCQU40U3M0ZVlPU2huMVpQQjdhTUZsY0k2RHR2S2ErTGZTTXFyY2pOZjJlSEpZNnhubmxKdgpGenpGL2RiVWVTbWxSekR0WkdlcXZXaHFISy9iTjIyeWJhOU1WMDlRQ0JFTk5jNmtWajJTVHpUWkJVbEx4QzYrCk93Z0wyZHhKendWelU0VC84ajdHalRUN05BZVpFS2FvRHFyRG5BYWkyaW5oZU1JVWZHRXFGKzJyQW9HQkFOMVAKK0tZL0lsS3RWRzRKSklQNzBjUis3RmpyeXJpY05iWCtQVzUvOXFHaWxnY2grZ3l4b25BWlBpd2NpeDN3QVpGdwpaZC96ZFB2aTBkWEppc1BSZjRMazg5b2pCUmpiRmRmc2l5UmJYbyt3TFU4NUhRU2NGMnN5aUFPaTVBRHdVU0FkCm45YWFweUNweEFkREtERHdObit3ZFhtaTZ0OHRpSFRkK3RoVDhkaVpBb0dCQUt6Wis1bG9OOTBtYlF4VVh5YUwKMjFSUm9tMGJjcndsTmVCaWNFSmlzaEhYa2xpSVVxZ3hSZklNM2hhUVRUcklKZENFaHFsV01aV0xPb2I2NTNyZgo3aFlMSXM1ZUtka3o0aFRVdnpldm9TMHVXcm9CV2xOVHlGanIrSWhKZnZUc0hpOGdsU3FkbXgySkJhZUFVWUNXCndNdlQ4NmNLclNyNkQrZG8wS05FZzFsL0FvR0FlMkFVdHVFbFNqLzBmRzgrV3hHc1RFV1JqclRNUzRSUjhRWXQKeXdjdFA4aDZxTGxKUTRCWGxQU05rMXZLTmtOUkxIb2pZT2pCQTViYjhibXNVU1BlV09NNENoaFJ4QnlHbmR2eAphYkJDRkFwY0IvbEg4d1R0alVZYlN5T294ZGt5OEp0ek90ajJhS0FiZHd6NlArWDZDODhjZmxYVFo5MWpYL3RMCjF3TmRKS2tDZ1lCbyt0UzB5TzJ2SWFmK2UwSkN5TGhzVDQ5cTN3Zis2QWVqWGx2WDJ1VnRYejN5QTZnbXo5aCsKcDNlK2JMRUxwb3B0WFhNdUFRR0xhUkcrYlNNcjR5dERYbE5ZSndUeThXczNKY3dlSTdqZVp2b0ZpbmNvVlVIMwphdmxoTUVCRGYxSjltSDB5cDBwWUNaS2ROdHNvZEZtQktzVEtQMjJhTmtsVVhCS3gyZzR6cFE9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=
---
# Source: kubernetes-ingress/deployments/common/nginx-config.yaml
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-config
namespace: nginx-ingress
data:
external-status-address: "127.0.0.1"
---
# Source: kubernetes-ingress/deployments/common/vs-definition.yaml
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: virtualservers.k8s.nginx.org
spec:
group: k8s.nginx.org
versions:
- name: v1
served: true
storage: true
scope: Namespaced
names:
kind: VirtualServer
plural: virtualservers
singular: virtualserver
shortNames:
- vs
preserveUnknownFields: false
validation:
openAPIV3Schema:
description: VirtualServer defines the VirtualServer resource.
type: object
properties:
apiVersion:
description: 'APIVersion defines the versioned schema of this representation
of an object. Servers should convert recognized schemas to the latest
internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources'
type: string
kind:
description: 'Kind is a string value representing the REST resource this
object represents. Servers may infer this from the endpoint the client
submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds'
type: string
metadata:
type: object
spec:
description: VirtualServerSpec is the spec of the VirtualServer resource.
type: object
properties:
host:
type: string
routes:
type: array
items:
description: Route defines a route.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
errorPages:
type: array
items:
description: ErrorPage defines an ErrorPage in a Route.
type: object
properties:
codes:
type: array
items:
type: integer
redirect:
description: ErrorPageRedirect defines a redirect for an
ErrorPage.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ErrorPageReturn defines a return for an ErrorPage.
type: object
properties:
body:
type: string
code:
type: integer
headers:
type: array
items:
description: Header defines an HTTP Header.
type: object
properties:
name:
type: string
value:
type: string
type:
type: string
matches:
type: array
items:
description: Match defines a match.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an
Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
conditions:
type: array
items:
description: Condition defines a condition in a MatchRule.
type: object
properties:
argument:
type: string
cookie:
type: string
header:
type: string
value:
type: string
variable:
type: string
splits:
type: array
items:
description: Split defines a split.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect
in an Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in
an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
weight:
type: integer
path:
type: string
route:
type: string
splits:
type: array
items:
description: Split defines a split.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an
Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
weight:
type: integer
tls:
description: TLS defines TLS configuration for a VirtualServer.
type: object
properties:
redirect:
description: TLSRedirect defines a redirect for a TLS.
type: object
properties:
basedOn:
type: string
code:
type: integer
enable:
type: boolean
secret:
type: string
upstreams:
type: array
items:
description: Upstream defines an upstream.
type: object
properties:
buffer-size:
type: string
buffering:
type: boolean
buffers:
description: UpstreamBuffers defines Buffer Configuration for
an Upstream.
type: object
properties:
number:
type: integer
size:
type: string
client-max-body-size:
type: string
connect-timeout:
type: string
fail-timeout:
type: string
healthCheck:
description: HealthCheck defines the parameters for active Upstream
HealthChecks.
type: object
properties:
connect-timeout:
type: string
enable:
type: boolean
fails:
type: integer
headers:
type: array
items:
description: Header defines an HTTP Header.
type: object
properties:
name:
type: string
value:
type: string
interval:
type: string
jitter:
type: string
passes:
type: integer
path:
type: string
port:
type: integer
read-timeout:
type: string
send-timeout:
type: string
statusMatch:
type: string
tls:
description: UpstreamTLS defines a TLS configuration for an
Upstream.
type: object
properties:
enable:
type: boolean
keepalive:
type: integer
lb-method:
type: string
max-conns:
type: integer
max-fails:
type: integer
name:
type: string
next-upstream:
type: string
next-upstream-timeout:
type: string
next-upstream-tries:
type: integer
port:
type: integer
queue:
description: UpstreamQueue defines Queue Configuration for an
Upstream.
type: object
properties:
size:
type: integer
timeout:
type: string
read-timeout:
type: string
send-timeout:
type: string
service:
type: string
sessionCookie:
description: SessionCookie defines the parameters for session
persistence.
type: object
properties:
domain:
type: string
enable:
type: boolean
expires:
type: string
httpOnly:
type: boolean
name:
type: string
path:
type: string
secure:
type: boolean
slow-start:
type: string
subselector:
type: object
additionalProperties:
type: string
tls:
description: UpstreamTLS defines a TLS configuration for an Upstream.
type: object
properties:
enable:
type: boolean
---
# Source: kubernetes-ingress/deployments/common/vsr-definition.yaml
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: virtualserverroutes.k8s.nginx.org
spec:
group: k8s.nginx.org
versions:
- name: v1
served: true
storage: true
scope: Namespaced
names:
kind: VirtualServerRoute
plural: virtualserverroutes
singular: virtualserverroute
shortNames:
- vsr
preserveUnknownFields: false
validation:
openAPIV3Schema:
type: object
properties:
apiVersion:
description: 'APIVersion defines the versioned schema of this representation
of an object. Servers should convert recognized schemas to the latest
internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources'
type: string
kind:
description: 'Kind is a string value representing the REST resource this
object represents. Servers may infer this from the endpoint the client
submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds'
type: string
metadata:
type: object
spec:
type: object
properties:
host:
type: string
subroutes:
type: array
items:
description: Route defines a route.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
errorPages:
type: array
items:
description: ErrorPage defines an ErrorPage in a Route.
type: object
properties:
codes:
type: array
items:
type: integer
redirect:
description: ErrorPageRedirect defines a redirect for an
ErrorPage.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ErrorPageReturn defines a return for an ErrorPage.
type: object
properties:
body:
type: string
code:
type: integer
headers:
type: array
items:
description: Header defines an HTTP Header.
type: object
properties:
name:
type: string
value:
type: string
type:
type: string
matches:
type: array
items:
description: Match defines a match.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an
Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
conditions:
type: array
items:
description: Condition defines a condition in a MatchRule.
type: object
properties:
argument:
type: string
cookie:
type: string
header:
type: string
value:
type: string
variable:
type: string
splits:
type: array
items:
description: Split defines a split.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect
in an Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in
an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
weight:
type: integer
path:
type: string
route:
type: string
splits:
type: array
items:
description: Split defines a split.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
redirect:
description: ActionRedirect defines a redirect in an
Action.
type: object
properties:
code:
type: integer
url:
type: string
return:
description: ActionReturn defines a return in an Action.
type: object
properties:
body:
type: string
code:
type: integer
type:
type: string
weight:
type: integer
upstreams:
type: array
items:
description: Upstream defines an upstream.
type: object
properties:
buffer-size:
type: string
buffering:
type: boolean
buffers:
description: UpstreamBuffers defines Buffer Configuration for
an Upstream.
type: object
properties:
number:
type: integer
size:
type: string
client-max-body-size:
type: string
connect-timeout:
type: string
fail-timeout:
type: string
healthCheck:
description: HealthCheck defines the parameters for active Upstream
HealthChecks.
type: object
properties:
connect-timeout:
type: string
enable:
type: boolean
fails:
type: integer
headers:
type: array
items:
description: Header defines an HTTP Header.
type: object
properties:
name:
type: string
value:
type: string
interval:
type: string
jitter:
type: string
passes:
type: integer
path:
type: string
port:
type: integer
read-timeout:
type: string
send-timeout:
type: string
statusMatch:
type: string
tls:
description: UpstreamTLS defines a TLS configuration for an
Upstream.
type: object
properties:
enable:
type: boolean
keepalive:
type: integer
lb-method:
type: string
max-conns:
type: integer
max-fails:
type: integer
name:
type: string
next-upstream:
type: string
next-upstream-timeout:
type: string
next-upstream-tries:
type: integer
port:
type: integer
queue:
description: UpstreamQueue defines Queue Configuration for an
Upstream.
type: object
properties:
size:
type: integer
timeout:
type: string
read-timeout:
type: string
send-timeout:
type: string
service:
type: string
sessionCookie:
description: SessionCookie defines the parameters for session
persistence.
type: object
properties:
domain:
type: string
enable:
type: boolean
expires:
type: string
httpOnly:
type: boolean
name:
type: string
path:
type: string
secure:
type: boolean
slow-start:
type: string
subselector:
type: object
additionalProperties:
type: string
tls:
description: UpstreamTLS defines a TLS configuration for an Upstream.
type: object
properties:
enable:
type: boolean
---
# Source: kubernetes-ingress/deployments/common/ts-definition.yaml
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: transportservers.k8s.nginx.org
spec:
group: k8s.nginx.org
versions:
- name: v1alpha1
served: true
storage: true
scope: Namespaced
names:
plural: transportservers
singular: transportserver
kind: TransportServer
shortNames:
- ts
preserveUnknownFields: false
validation:
openAPIV3Schema:
description: TransportServer defines the TransportServer resource.
type: object
properties:
apiVersion:
description: 'APIVersion defines the versioned schema of this representation
of an object. Servers should convert recognized schemas to the latest
internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources'
type: string
kind:
description: 'Kind is a string value representing the REST resource this
object represents. Servers may infer this from the endpoint the client
submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds'
type: string
metadata:
type: object
spec:
description: TransportServerSpec is the spec of the TransportServer resource.
type: object
properties:
action:
description: Action defines an action.
type: object
properties:
pass:
type: string
host:
type: string
listener:
description: TransportServerListener defines a listener for a TransportServer.
type: object
properties:
name:
type: string
protocol:
type: string
upstreamParameters:
description: UpstreamParameters defines parameters for an upstream.
type: object
properties:
udpRequests:
type: integer
udpResponses:
type: integer
upstreams:
type: array
items:
description: Upstream defines an upstream.
type: object
properties:
name:
type: string
port:
type: integer
service:
type: string
---
# Source: kubernetes-ingress/deployments/common/gc-definition.yaml
apiVersion: apiextensions.k8s.io/v1beta1
kind: CustomResourceDefinition
metadata:
name: globalconfigurations.k8s.nginx.org
spec:
group: k8s.nginx.org
versions:
- name: v1alpha1
served: true
storage: true
scope: Namespaced
names:
plural: globalconfigurations
singular: globalconfiguration
kind: GlobalConfiguration
shortNames:
- gc
preserveUnknownFields: false
validation:
openAPIV3Schema:
description: GlobalConfiguration defines the GlobalConfiguration resource.
type: object
properties:
apiVersion:
description: 'APIVersion defines the versioned schema of this representation
of an object. Servers should convert recognized schemas to the latest
internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources'
type: string
kind:
description: 'Kind is a string value representing the REST resource this
object represents. Servers may infer this from the endpoint the client
submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds'
type: string
metadata:
type: object
spec:
description: GlobalConfigurationSpec is the spec of the GlobalConfiguration
resource.
type: object
properties:
listeners:
type: array
items:
description: Listener defines a listener.
type: object
properties:
name:
type: string
port:
type: integer
protocol:
type: string
---
# Source: kubernetes-ingress/deployments/common/global-configuration.yaml
apiVersion: k8s.nginx.org/v1alpha1
kind: GlobalConfiguration
metadata:
name: nginx-configuration
namespace: nginx-ingress
---
# Source: kubernetes-ingress/deployments/daemon-set/nginx-ingress.yaml
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: nginx-ingress
namespace: nginx-ingress
spec:
selector:
matchLabels:
app: nginx-ingress
template:
metadata:
labels:
app: nginx-ingress
#annotations:
#prometheus.io/scrape: "true"
#prometheus.io/port: "9113"
spec:
serviceAccountName: nginx-ingress
containers:
- image: nginx/nginx-ingress:1.7.1
name: nginx-ingress
ports:
- name: http
containerPort: 80
hostPort: 80
- name: https
containerPort: 443
hostPort: 443
#- name: prometheus
#containerPort: 9113
securityContext:
allowPrivilegeEscalation: true
runAsUser: 101 #nginx
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
env:
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
args:
- -nginx-configmaps=$(POD_NAMESPACE)/nginx-config
- -default-server-tls-secret=$(POD_NAMESPACE)/default-server-secret
#- -v=3 # Enables extensive logging. Useful for troubleshooting.
- -report-ingress-status
- -external-service=nginx-ingress
- -enable-leader-election
#- -enable-prometheus-metrics
- -global-configuration=$(POD_NAMESPACE)/nginx-configuration
---
# Source: kubernetes-ingress/deployments/service/nodeport.yaml
apiVersion: v1
kind: Service
metadata:
name: nginx-ingress
namespace: nginx-ingress
spec:
#externalTrafficPolicy: Local
#type: LoadBalancer
type: NodePort
ports:
- port: 80
targetPort: 80
protocol: TCP
name: http
- port: 443
targetPort: 443
protocol: TCP
name: https
selector:
app: nginx-ingress
---
# kubectl delete namespace nginx-ingress
# kubectl delete clusterrole nginx-ingress
# kubectl delete clusterrolebinding nginx-ingress
nginx-ingress.yaml
③ 执行以上部署文件,等待部署完成,修改nginx-config,配置负载地址:
[root@k8s147 ~]# kubectl get pod -n nginx-ingress
NAME READY STATUS RESTARTS AGE
nginx-ingress-6m4nm 1/1 Running 1 9d
nginx-ingress-d9b5r 1/1 Running 1 9d
[root@k8s147 ~]# kubectl get svc -n nginx-ingress
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
nginx-ingress NodePort 10.104.157.46 <none> 80:30080/TCP,443:30443/TCP 9d
[root@k8s147 ~]# kubectl get cm nginx-config -oyaml -n nginx-ingress
apiVersion: v1
data:
external-status-address: 10.88.88.147
kind: ConfigMap
metadata:
creationTimestamp: "2020-06-23T01:03:30Z"
name: nginx-config
namespace: nginx-ingress
resourceVersion: ""
selfLink: /api/v1/namespaces/nginx-ingress/configmaps/nginx-config
uid: b7cfa1c3-204a-4310-8859-096dcd3980ba
[root@k8s147 ~]# kubectl edit cm nginx-config -n nginx-ingress
Edit cancelled, no changes made.
更多参考 >>> ingress-nginx性能测试 HAProxy和NGINX性能进行基准测试
3) 如果你追求功能的全面,服务网络的管理,那我推荐使用Istio。Istio开始就是与k8s结合设计的,可以说是一个非常牛逼的落地微服务架构,优点太多,缺点就是一句话 “老子学不动了!!!”。
四、不同场景配置
1、单服务 Ingress
现有的 Kubernetes 概念允许您暴露单个 Servic,你也可以通过指定无规则的 默认后端 来对 Ingress 进行此操作。
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: test-ingress
spec:
backend:
serviceName: test-svc
servicePort: 80
2、简单分列
一个分列配置根据请求的 HTTP URI 将流量从单个 IP 地址路由到多个服务。
foo.bar.com -> 178.91.123.132 -> / foo service1:4200
/ bar service2:8080apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: simple-fanout-example
annotations:
nginx.ingress.kubernetes.io/rewrite-target: /
spec:
rules:
- host: foo.bar.com
http:
paths:
- path: /foo
backend:
serviceName: service1
servicePort: 4200
- path: /bar
backend:
serviceName: service2
servicePort: 8080
3、基于名称的虚拟托管
基于名称的虚拟主机支持将 HTTP 流量路由到同一 IP 地址上的多个主机名。
foo.bar.com --| |-> foo.bar.com service1:80
| 178.91.123.132 |
bar.foo.com --| |-> bar.foo.com service2:80apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: name-virtual-host-ingress
spec:
rules:
- host: foo.bar.com
http:
paths:
- backend:
serviceName: service1
servicePort: 80
- host: bar.foo.com
http:
paths:
- backend:
serviceName: service2
servicePort: 80
注意:如果您创建的 Ingress 资源没有规则中定义的任何主机(host),则可以匹配到你 Ingress 控制器 IP 地址的任何网络流量,而无需基于名称的虚拟主机。
4、TLS安全设置
你可以通过指定包含 TLS 私钥和证书的 secret 来加密 Ingress, TLS Secret 必须包含名为 tls.crt 和 tls.key 的密钥,这些密钥包含用于 TLS 的证书和私钥,例如:
apiVersion: v1
kind: Secret
metadata:
name: secret-tls
namespace: default
data:
tls.crt: base64 encoded cert
tls.key: base64 encoded key
type: kubernetes.io/tls
或者,通过openssl工具生产证书,然后通过kubectl命令创建一个secret tls资源。
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=sslexample.foo.com"
kubectl create secret tls secret-tls --key tls.key --cert tls.crt
另外,你需要确保创建的 TLS secret 来自包含 sslexample.foo.com 的公用名称(CN)的证书,也被称为全限定域名(FQDN)。
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: tls-example-ingress
spec:
tls:
- hosts:
- sslexample.foo.com
secretName: secret-tls
rules:
- host: sslexample.foo.com
http:
paths:
- path: /
backend:
serviceName: service1
servicePort: 80
5、查看访问
我们可以通过 kubectl get 查看 ingress 资源列表
$ kubectl get ingress
NAME HOSTS ADDRESS PORTS AGE
simple-fanout-example foo.bar.com 203.0.113.123 80 59s
我们也可以通过 kubectl describe 查看 ingress 资源详情
$ kubectl describe ingress simple-fanout-example
Name: simple-fanout-example
Namespace: default
Address: 178.91.123.132
Default backend: default-http-backend:80 (10.8.2.3:8080)
Rules:
Host Path Backends
---- ---- --------
foo.bar.com
/foo service1:4200 (10.8.0.90:4200)
/bar service2:8080 (10.8.0.91:8080)
Annotations:
nginx.ingress.kubernetes.io/rewrite-target: /
Events:
Type Reason Age From Message
---- ------ ---- ---- -------
Normal ADD 22s loadbalancer-controller default/test
最后我们可以通过 http协议 + 负载地址 + 控制器端口 + uri 访问到服务。
curl -H 'foo.bar.com' http://203.0.113.123/foo/
五、我对Ingress性能测试

测试工具:wrk性能测试(详解)
由于测试环境比较混乱,配置一般,所以测试结果不一定完全准确,仅供参数。
根据以上测试结果可以看出,kube-ingress性能存在较大的问题,虽然可以通过调节参数来实现性能优化,但是从各方面资料得知,依然与nginx存在较大差异。
而nginx-ingress效果就比较显著,性能与原生nginx无太大差异。另外在部署方面,建议启用daemon-set模式来平滑扩大控制器的副本到各个节点,以提高ingress的性能。
作者:Leozhanggg
出处:https://www.cnblogs.com/leozhanggg/p/13189173.html
本文版权归作者和博客园共有,欢迎转载,但未经作者同意必须保留此段声明,且在文章页面明显位置给出原文连接,否则保留追究法律责任的权利。
Kubernetes实战总结 - Ingress选型与应用的更多相关文章
- 新书推荐《再也不踩坑的Kubernetes实战指南》
<再也不踩坑的Kubernetes实战指南>终于出版啦.目前可以在京东.天猫购买,京东自营和当当网预计一个星期左右上架. 本书贴合生产环境经验,解决在初次使用或者是构建集群中的痛点,帮 ...
- kubernetes实战(二十八):Kubernetes一键式资源管理平台Ratel安装及使用
1. Ratel是什么? Ratel是一个Kubernetes资源平台,基于管理Kubernetes的资源开发,可以管理Kubernetes的Deployment.DaemonSet.Stateful ...
- 2020 最新 Kubernetes实战指南
1.Kubernetes带来的变革 对于开发人员 由于公司业务多,开发环境.测试环境.预生产环境和生产环境都是隔离的,而且除了生产环境,为了节省成本,其他环境可能是没有日志收集的,在没有用k8s的 ...
- Kubernetes实战总结 - 阿里云ECS自建K8S集群
一.概述 详情参考阿里云说明:https://help.aliyun.com/document_detail/98886.html?spm=a2c4g.11186623.6.1078.323b1c9b ...
- kubernetes 实战6_命令_Share Process Namespace between Containers in a Pod&Translate a Docker Compose File to Kubernetes Resources
Share Process Namespace between Containers in a Pod how to configure process namespace sharing for a ...
- kubernetes对象之Ingress
系列目录 概述 向外网暴露集群内服务,以使客户端能够访问,有以下几种方法,本文重点描述Ingress. LoadBalancer LoadBalancer一般由云服务供应商提供或者用户自定义,运行在集 ...
- kubernetes实战(二十六):kubeadm 安装 高可用 k8s v1.16.x dashboard 2.x
1.基本配置 基本配置.内核升级.基本服务安装参考https://www.cnblogs.com/dukuan/p/10278637.html,或者参考<再也不踩坑的Kubernetes实战指南 ...
- Kubernetes 系列(三):Kubernetes使用Traefik Ingress暴露服务
一.Kubernetes 服务暴露介绍 从 kubernetes 1.2 版本开始,kubernetes提供了 Ingress 对象来实现对外暴露服务:到目前为止 kubernetes 总共有三种暴露 ...
- kubernetes实战(二十七):CentOS 8 二进制 高可用 安装 k8s 1.16.x
1. 基本说明 本文章将演示CentOS 8二进制方式安装高可用k8s 1.16.x,相对于其他版本,二进制安装方式并无太大区别.CentOS 8相对于CentOS 7操作更加方便,比如一些服务的关闭 ...
随机推荐
- java实现第九届蓝桥杯最大乘积
最大乘积 把 1~9 这9个数字分成两组,中间插入乘号, 有的时候,它们的乘积也只包含1~9这9个数字,而且每个数字只出现1次. 比如: 984672 * 351 = 345619872 98751 ...
- Babel 7 安装与配置
Babel:帮我们把高级的语法(ES6)转为低级的语法 /* Babel 7.x版本 安装如下 (cnpm i @babel/cli -D) //Bab ...
- Android下的缓存策略
Android下的缓存策略 内存缓存 常用的内存缓存是软引用和弱引用,大部分的使用方式是Android提供的LRUCache缓存策略,本质是个LinkedHashMap(会根据使用次数进行排序) 磁盘 ...
- 括号匹配-算法详细题解LeetCode
题目:有效的括号 给定一个只包括 '(',')','{','}','[',']' 的字符串,判断字符串是否有效. 有效字符串需满足: 左括号必须用相同类型的右括号闭合. 左括号必须以正确的顺序闭合. ...
- 秒懂系列,超详细Java枚举教程!!!
所有知识体系文章,GitHub已收录,欢迎Star!再次感谢,愿你早日进入大厂! GitHub地址: https://github.com/Ziphtracks/JavaLearningmanual ...
- [蓝桥杯]算法提高 GPA
问题描述 输入A,B两人的学分获取情况,输出两人GPA之差. 输入格式 输入的第一行包含一个整数n表示A的课程数,以下n行每行Si,Ci分别表示第i个课程的学分与A的表现. GPA=Σ(Si*Ci) ...
- 2020最新IDEA插件大集合,一款能帮助你写代码的工具是多么重要
摘要 12款为用户精心打造的Idea插件,含盖前后端,另把使用小技巧分享给大家,提高大家的码率,希望对你们有帮助! Lombok Lombok为Java项目提供了非常有趣的附加功能,使用它的注解可以有 ...
- [原创][开源] SunnyUI.Net 安装
SunnyUI.Net, 基于 C# .Net WinForm 开源控件库.工具类库.扩展类库.多页面开发框架 Blog: https://www.cnblogs.com/yhuse Gitee: h ...
- LVS 负载均衡器理论基础及抓包分析
LVS 是 Linux Virtual Server 的简写,即 Linux 虚拟服务器,是一个虚拟的服务器集群系统.本项目在1998年5月由章文嵩博士成立,是中国国内最早出现的自由软件项目之一.(百 ...
- sorted排序
sorted(['bob', 'about', 'Zoo', 'Credit']) # ['Credit', 'Zoo', 'about', 'bob'] ''' 默认情况下,对字符串排序,是按照AS ...
