ssh 认证
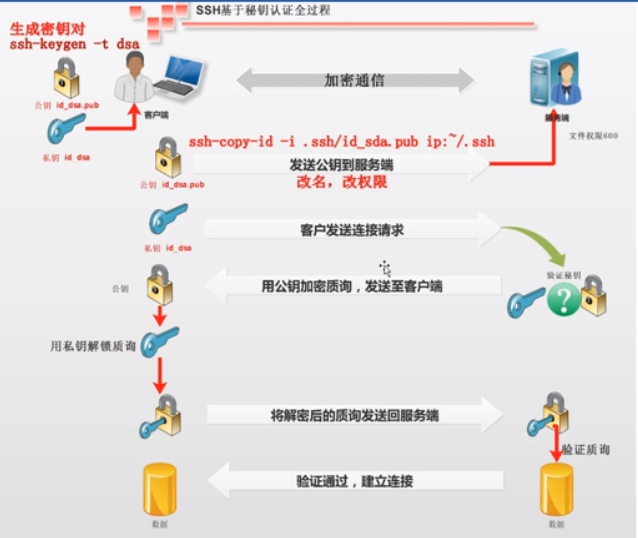
ssh 秘钥认证流程
ssh配置认证
基于口令(密码)的安全验证
[root@m01 ~]# ssh 10.0.0.41 hostname
root@10.0.0.41's password:
backup
[root@m01 ~]# ssh 10.0.0.41 whoami
root@10.0.0.41's password:
root
[root@m01 ~]# ssh lewen@10.0.0.41 whoami
lewen@10.0.0.41's password:
lewen
基于秘钥的认证
1.生成钥匙和锁头
[root@m01 ~]# hostname
m01
[root@m01 ~]# ssh-keygen -t dsa
Generating public/private dsa key pair.
Enter file in which to save the key (/root/.ssh/id_dsa):
Enter passphrase (empty for no passphrase): # 给秘钥加密码
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_dsa.
Your public key has been saved in /root/.ssh/id_dsa.pub.
The key fingerprint is:
::1b:e1:9f:0a:ab::a0:fc:::2d:bc::dd root@m01
The key's randomart image is:
+--[ DSA ]----+
| |
| . + . |
| = + E |
| . + . o |
| o . S |
| ..o = . |
| .o.... o |
| .o..o.. |
| .+o.. |
+-----------------+
2.把锁头发送到目标机器
发送到 backup
[root@m01 ~]# ssh-copy-id -i /root/.ssh/id_dsa.pub root@172.16.1.41
The authenticity of host '172.16.1.41 (172.16.1.41)' can't be established.
RSA key fingerprint is ac:0f:aa:d2:5b:ff:cf:ac:f0:::a6:be::b9:f9.
Are you sure you want to continue connecting (yes/no)? y
Please type 'yes' or 'no': yes
Warning: Permanently added '172.16.1.41' (RSA) to the list of known hosts.
root@172.16.1.41's password:
Now try logging into the machine, with "ssh 'root@172.16.1.41'", and check in:
.ssh/authorized_keys
to make sure we haven't added extra keys that you weren't expecting.
[root@m01 ~]# ssh 10.0.0.41 hostname
backup
#nfs01
[root@m01 ~]# ssh-copy-id -i /root/.ssh/id_dsa.pub root@172.16.1.31
The authenticity of host '172.16.1.31 (172.16.1.31)' can't be established.
RSA key fingerprint is ac:0f:aa:d2:5b:ff:cf:ac:f0:::a6:be::b9:f9.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '172.16.1.31' (RSA) to the list of known hosts.
root@172.16.1.31's password:
Now try logging into the machine, with "ssh 'root@172.16.1.31'", and check in:
.ssh/authorized_keys
to make sure we haven't added extra keys that you weren't expecting.
[root@m01 ~]# ssh 172.16.1.31 hostname
nfs01
3.免密发送
sshpass 软件
yum install sshpass -y #sshpass 给ssh类提供密码
[root@m01 ~]# sshpass -p123456 ssh 172.16.1.41 hostname
backup
sshpass -p123456 ssh -o StrictHostKeyChecking=no 172.16.1.41 hostname
backup
非交互式创建 钥匙锁头
[root@m01 ~]# ssh-keygen -t dsa -P '' -f ~/.ssh/id_dsa
非交互式 分发公钥
不用输入密码将公钥发送到目的机器
[root@m01 ~]# sshpass -p123456 ssh-copy-id -i /root/.ssh/id_dsa.pub "-o StrictHostKeyChecking=no root@172.16.1.41"
Now try logging into the machine, with "ssh '-o StrictHostKeyChecking=no root@172.16.1.41'",
and check in:
.ssh/authorized_keys
to make sure we haven't added extra keys that you weren't expecting.
[root@m01 ~]# sshpass -p123456 ssh-copy-id -i /root/.ssh/id_dsa.pub "-o StrictHostKeyChecking=no root@172.16.1.31"
Now try logging into the machine, with "ssh '-o StrictHostKeyChecking=no root@172.16.1.31'",
and check in:
.ssh/authorized_keys
to make sure we haven't added extra keys that you weren't expecting.
[root@m01 ~]# ssh 172.16.1.41 hostname
backup
[root@m01 ~]# ssh 172.16.1.31 hostname
nfs01
Usage: /usr/bin/ssh-copy-id [-h|-?|-f|-n] [-i [identity_file]] [-p port] [[-o <ssh -o options>] ...] [user@]hostname
-f: force mode -- copy keys without trying to check if they are already installed
-n: dry run -- no keys are actually copied
ssh 认证的更多相关文章
- ssh 认证指定端口
[root@database2 ~]# cat ssh.sh if [ ! $# -eq 2 ] ;then echo "请输入用户密码以空格分开" exit else ssh-k ...
- 批量的单向的ssh 认证
<pre name="code" class="python">if [ ! $# -eq 2 ] ;then echo "请输入用户密码 ...
- debian下使用gitosis+gitweb搭建SSH认证的git服务器
搭建完成Git服务器后,需要使用两台机器进行测试,一台机器作为服务器端server,一台服务器作为客户端client.整个系统,需要三个计算机账户,这里假设server端的账户名为git,client ...
- github添加ssh认证
总概:在使用git的时候,和目标仓库建立关系有两种方式https,ssh.一般用的是https认证(这样简单方便),但有个缺点,pull,push等操作需要频繁输入用户验证.虽然可以把用户验证账号密码 ...
- Linux学习笔记总结--ssh认证登录
原理简介 SSH证书认证登录的基础是一对唯一匹配密钥: 私钥(private key)和公钥(public key).公钥用于对数据进行加密,而且只能用于加密.而私钥只能对使用所匹配的公钥,所加密过的 ...
- git ssh认证
一般新手用git时,使用HTTPS都需要输入用户名和密码,这是一个很低效的开发过程.(虽然有时可以让开发人员减少push的次数).github提供了几种连接方式,其中以https:开头的代表https ...
- 华为SSH认证配置
[设备型号]华为switch-S5700s ————1: [SW1] rsa/dsa local-key-pair create #创建本地密钥对 The key name will be: SW1_ ...
- Jenkins - SSH认证方式拉取Git代码
1.本地生成密钥 [root@root ~] ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which ...
- [Linux] 一次SSH认证失败引发的关于通过日志查错误的思考
一.缘由: 早上在用SSH公钥认证打通所有的机器,有一台机器在完成一些列操作后密钥登陆失败,其他机器一切正常. 错误如下:Public-key authentication with the serv ...
随机推荐
- RTP格式解析
一般为12字节,16字节头(转自https://www.cnblogs.com/qingquan/archive/2011/07/28/2120440.html) 概述: 实时传送协议(Real-ti ...
- textarea 自动到右边就换行
java 到最右边的时候自动换行如实例: textArea.setLineWrap(true);
- Java面试基础知识(2)
1.一个".java"源文件中是否可以包括多个类(不是内部类)?有什么限制? 可以有多个类,但只能有一个public的类,并且public的类名必须与文件名相一致. 2.说说& ...
- Razor 模板引擎的使用
安装Razor的模板引擎,通过vs的“扩展管理器”,查找"RazorEngine"并安装.安装的dll包括”RazorEngine.dll“和”System.Web.Razor.d ...
- org.springframework.web.util.Log4jWebConfigurer
org.springframework.web.util.Log4jWebConfigurer @Deprecated Deprecated. as of Spring 4.2.1, in favor ...
- Git二进制文件冲突解决
Git二进制文件冲突解决 在我们合并分支的时候,如果两个分支都进行了修改那么就会产生合并冲突.对于非二进制文件的冲突解决,git会给出冲突的位置我们可以手动修改然后再commit.但是对于非二进制文件 ...
- execute() 和 sumbit() 的区别
execute()内部实现 1.首次通过workCountof()获知当前线程池中的线程数, 如果小于corePoolSize, 就通过addWorker()创建线程并执行该任务: 否则,将该任务放入 ...
- 改变dos的编码方式
chcp 936 改变成 gbk chcp 65001 改成 utf-8 删除MySqlite文件 generic_x86:/data/data/com.example.lifen.sqlite/da ...
- HISAT2,StringTie,Ballgown处理转录组数据
HISAT2,StringTie,Ballgown处理转录组数据 本文总阅读量次2017-05-26 HISAT2,StringTie,Ballgown处理转录组数据思路如下: 数据质控 将RNA-s ...
- BZOJ1226或洛谷2157 [SDOI2009]学校食堂
BZOJ原题链接 洛谷原题链接 注意到\(B[i]\)很小,考虑状压\(DP\). 设\(f[i][j][k]\)表示前\(i - 1\)个人已经拿到菜,第\(i\)个人及其后面\(7\)个人是否拿到 ...
