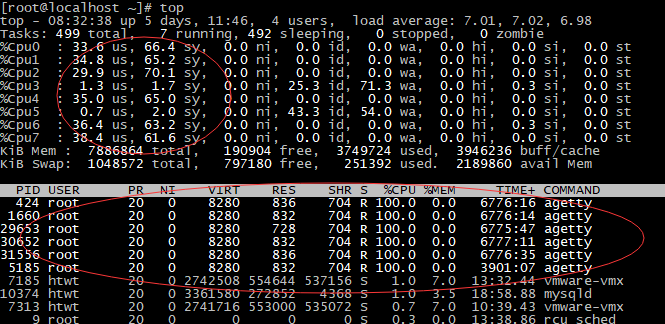
docker运行容器后agetty进程cpu占用率100%
1、最近在使用docker容器的时候,发现宿主机的agetty进程cpu占用率达到100%
在Google上搜了下,引起这个问题的原因是在使用"docker run"运行容器时使用了"/sbin/init"和"--privileged"参数。
使用/sbin/init启动容器并加上--privileged参数,相当于docker容器获得了宿主机的全权委托权限。这时docker容器内部的init与宿主机的init产生了混淆。
# 引用google到的一段话:
I've done all my testing on them without using --privileged, especially since that's so dangerous (effectively, you're telling this second init process on your system that it's cool to go ahead and manage your system resources, and then giving it access to them as well). I always think of --privileged as a hammer to be used very sparingly.
出于对安全的考虑,在启动容器时,docker容器里的系统只具有一些普通的linux权限,并不具有真正root用户的所有权限。而--privileged=true参数可以让docker容器具有linux root用户的所有权限。
为了解决这个问题,docker后来的版本中docker run增加了两个选项参数"--cap-add"和"--cap-drop"。
--cap-add : 获取default之外的linux的权限
--cap-drop: 放弃default linux权限
从docker官网的文档中可以查到,docker容器具有的default权限及--cap-add可以获取到的扩展权限如下:
Default 权限:
|
Capability Key |
Capability Description |
|
SETPCAP |
Modify process capabilities. |
|
MKNOD |
Create special files using mknod(2). |
|
AUDIT_WRITE |
Write records to kernel auditing log. |
|
CHOWN |
Make arbitrary changes to file UIDs and GIDs (see chown(2)). |
|
NET_RAW |
Use RAW and PACKET sockets. |
|
DAC_OVERRIDE |
Bypass file read, write, and execute permission checks. |
|
FOWNER |
Bypass permission checks on operations that normally require the file system UID of the process to match the UID of the file. |
|
FSETID |
Don’t clear set-user-ID and set-group-ID permission bits when a file is modified. |
|
KILL |
Bypass permission checks for sending signals. |
|
SETGID |
Make arbitrary manipulations of process GIDs and supplementary GID list. |
|
SETUID |
Make arbitrary manipulations of process UIDs. |
|
NET_BIND_SERVICE |
Bind a socket to internet domain privileged ports (port numbers less than 1024). |
|
SYS_CHROOT |
Use chroot(2), change root directory. |
|
SETFCAP |
Set file capabilities. |
通过--cap-add获取到的权限:
|
Capability Key |
Capability Description |
|
SYS_MODULE |
Load and unload kernel modules. |
|
SYS_RAWIO |
Perform I/O port operations (iopl(2) and ioperm(2)). |
|
SYS_PACCT |
Use acct(2), switch process accounting on or off. |
|
SYS_ADMIN |
Perform a range of system administration operations. |
|
SYS_NICE |
Raise process nice value (nice(2), setpriority(2)) and change the nice value for arbitrary processes. |
|
SYS_RESOURCE |
Override resource Limits. |
|
SYS_TIME |
Set system clock (settimeofday(2), stime(2), adjtimex(2)); set real-time (hardware) clock. |
|
SYS_TTY_CONFIG |
Use vhangup(2); employ various privileged ioctl(2) operations on virtual terminals. |
|
AUDIT_CONTROL |
Enable and disable kernel auditing; change auditing filter rules; retrieve auditing status and filtering rules. |
|
MAC_OVERRIDE |
Allow MAC configuration or state changes. Implemented for the Smack LSM. |
|
MAC_ADMIN |
Override Mandatory Access Control (MAC). Implemented for the Smack Linux Security Module (LSM). |
|
NET_ADMIN |
Perform various network-related operations. |
|
SYSLOG |
Perform privileged syslog(2) operations. |
|
DAC_READ_SEARCH |
Bypass file read permission checks and directory read and execute permission checks. |
|
LINUX_IMMUTABLE |
Set the FS_APPEND_FL and FS_IMMUTABLE_FL i-node flags. |
|
NET_BROADCAST |
Make socket broadcasts, and listen to multicasts. |
|
IPC_LOCK |
Lock memory (mlock(2), mlockall(2), mmap(2), shmctl(2)). |
|
IPC_OWNER |
Bypass permission checks for operations on System V IPC objects. |
|
SYS_PTRACE |
Trace arbitrary processes using ptrace(2). |
|
SYS_BOOT |
Use reboot(2) and kexec_load(2), reboot and load a new kernel for later execution. |
|
LEASE |
Establish leases on arbitrary files (see fcntl(2)). |
|
WAKE_ALARM |
Trigger something that will wake up the system. |
|
BLOCK_SUSPEND |
Employ features that can block system suspend. |
所以,在运行容器时,可以不用--privileged参数的尽量不用,用--cap-add参数替代。如果必须使用--privileged=true参数的,可以通过在宿主机和容器中执行以下命令将agetty关闭。
shell> systemctl stop getty@tty1.service shell> systemctl mask getty@tty1.service
参考资料:
https://github.com/docker/docker/issues/4040
https://docs.docker.com/engine/reference/run/
docker运行容器后agetty进程cpu占用率100%的更多相关文章
- 获取进程CPU占用率
获取进程CPU占用率 // 时间转换 static __int64 file_time_2_utc(const FILETIME* ftime) { LARGE_INTEGER li; li.LowP ...
- Linux下java进程CPU占用率高分析方法
Linux下java进程CPU占用率高分析方法 在工作当中,肯定会遇到由代码所导致的高CPU耗用以及内存溢出的情况.这种情况发生时,我们怎么去找出原因并解决. 一般解决方法是通过top命令找出消耗资源 ...
- Linux下分析某个进程CPU占用率高的原因
Linux下分析某个进程CPU占用率高的原因 通过top命令找出消耗资源高的线程id,利用strace命令查看该线程所有系统调用 1.top 查到占用cpu高的进程pid 2.查看该pid的线程 ...
- (转)Linux下java进程CPU占用率高-分析方法
Linux下java进程CPU占用率高-分析方法 原文:http://itindex.net/detail/47420-linux-java-%E8%BF%9B%E7%A8%8B?utm_source ...
- Linux下java进程CPU占用率高分析方法(一)
Linux下java进程CPU占用率高分析方法 在工作当中,肯定会遇到由代码所导致的高CPU耗用以及内存溢出的情况.这种情况发生时,我们怎么去找出原因并解决. 一般解决方法是通过top命令找出消耗资源 ...
- Linux下java进程CPU占用率高分析方法(二)
1. 通过 top 命令查看当前系统CPU使用情况,定位CPU使用率超过100%的进程ID:2. 通过 ps aux | grep PID 命令进一步确定具体的线程信息:3. 通过 ps -mp pi ...
- Linux下java进程CPU占用率高-分析方法
今天登陆同事的一台gateway 开始以为hive环境登陆不了了,仔细一看看了下是因为机器很卡,我每次等几秒没登陆就ctrl+c了,看了下是有个java进程cpu:340.4% mem:14.6% ...
- cidaemon.exe进程cpu占用率高及关闭cidaemon.exe进程方法
问题描写叙述: 这段时间机器总是出现一个奇怪的问题:cidaemon.exe进程占用CUP率98%以上,大大影响了电脑的正常使用.资源管理器中出现多个cidaemon.exe进程,强制结束占用cp ...
- WMI获取进程CPU占用率
Monitor % Process CPU Usage (specific process) http://www.tek-tips.com/viewthread.cfm?qid=395765 for ...
随机推荐
- selenium实现网页截全屏
from selenium import webdriver options = webdriver.ChromeOptions() options.add_argument('--headless' ...
- python 替换字符串的方法replace()、正则re.sub()
一.replace()函数1用字符串本身的replace方法: a = 'hello word' b = a.replace('word','python') print b 1 2 3 二.re ...
- SDWebImage源码解析之SDWebImageManager的注解
http://www.cocoachina.com/ios/20150612/12118.html 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 ...
- 自动编码(AE)器的简单实现
一.目录 自动编码(AE)器的简单实现 一.目录 二.自动编码器的发展简述 2.1 自动编码器(Auto-Encoders,AE) 2.2 降噪自编码(Denoising Auto-Encoders, ...
- @atcoder - AGC035D@ Add and Remove
目录 @description@ @solution@ @accepted code@ @details@ @description@ 给定 N 张排成一行的卡片,第 i 张卡片上面写着 Ai. 重复 ...
- @loj - 2092@ 「ZJOI2016」大森林
目录 @description@ @solution@ @accepted code@ @details@ @description@ 小 Y 家里有一个大森林,里面有 n 棵树,编号从 1 到 n. ...
- CH1401 兔子与兔子
#include<bits/stdc++.h> using namespace std; ,p=; typedef unsigned long long ULL;//自然溢出 ULL f[ ...
- @loj - 2289@「THUWC 2017」在美妙的数学王国中畅游
目录 @description@ @solution@ @accepted code@ @details@ @description@ n 个点编号 0 到 n-1,每个点有一个从 [0,1] 映射到 ...
- APICloud原生APP中ajax需要用api.ajax
报错截屏: APICloud原生APP中ajax请求需要用api.ajax(api对象的ajax方法来替代),否则会将引起请求失败. APICloud api.ajax
- AtCoder Beginner Contest 077 D Small Multiple(最短路)
水过前三道题之后,一直在写这个题,做不对.总有那么几组数据过不去... 看了看题解是最短路,这思路感觉很神奇.看了下唯一做出来这题的那人的代码,是搜索做的. 标程: 对每个数字x,向x+1建一条花费为 ...
