Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment:
Download and Install Pan-OS from the following website https://docs.gns3.com/appliances/pan-vm-fw.html or https://me.csdn.net/download/hotbrandon

URL https://IP
Default Username/Password: admin/admin
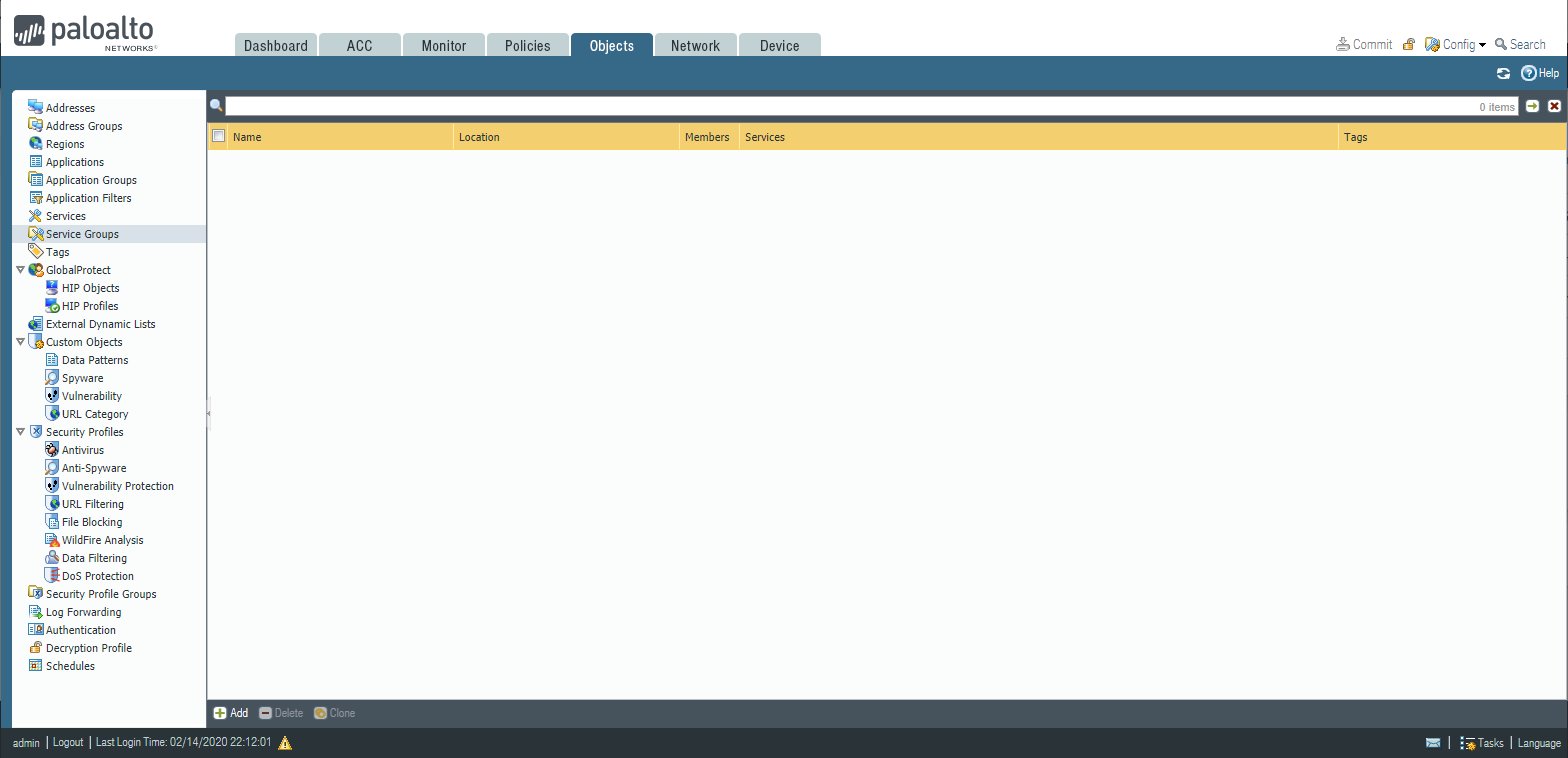
PAN-OS 8 Configuration Tabs:
- Object tab: Configure Firewall objects(address - services - object groups)
- Policy tab: Configure Firewall policies(security -NAT -QoS - PBR)
- Network tab: Configure Firewall interfaces and routing settings
- Device tab: Perform maintenance tasks and administrative tasks.
- Configuration backup and restore.
- High availability.
- Users and administrators.
- Directory synchronization(Active Directory)
PAN-OS 8 Monitoring Tabs:
- ACC Tab: Application command center overview
- Monitor tab: User traffic monitoring based on applied policies
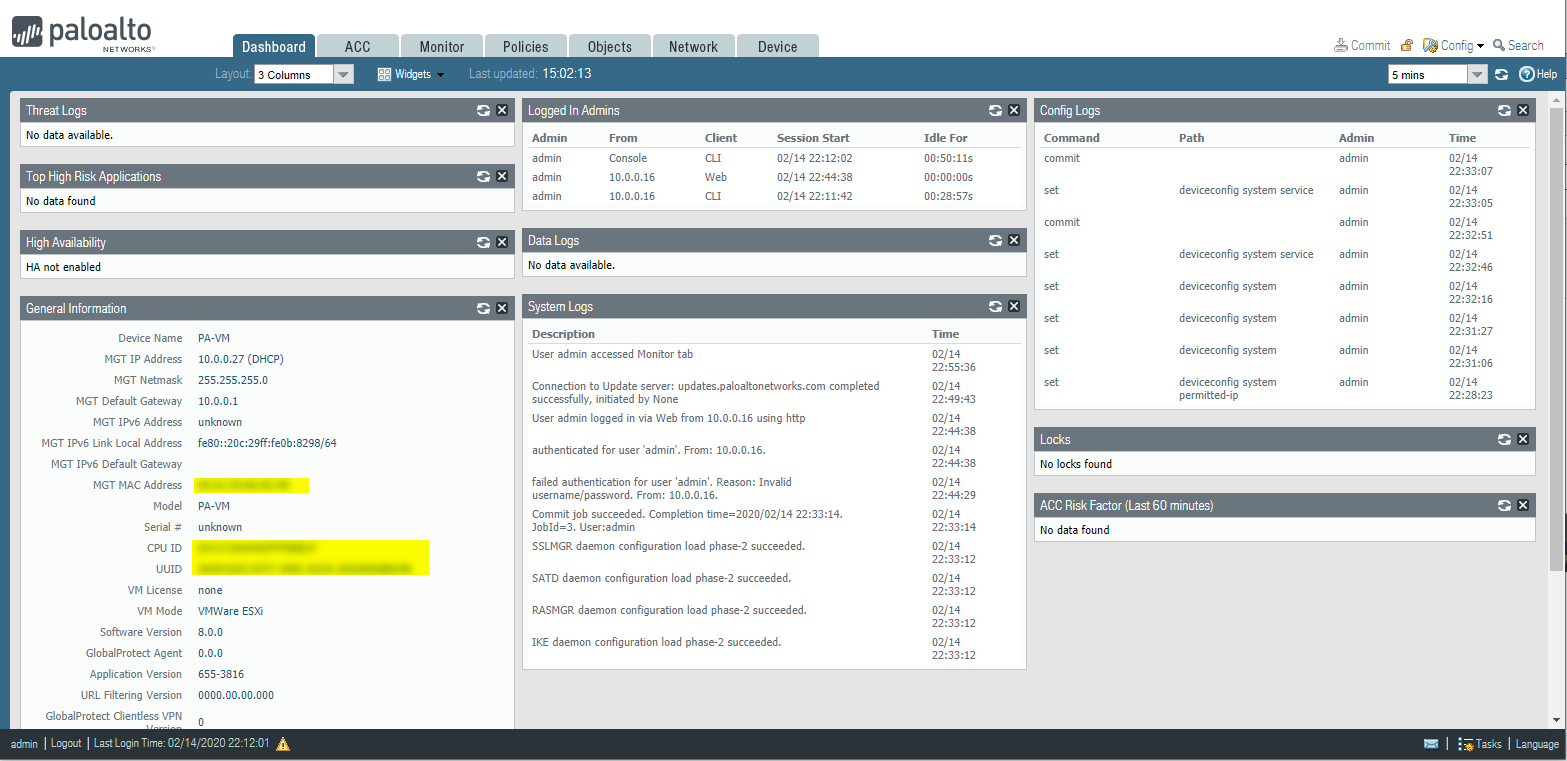
Dashboard:
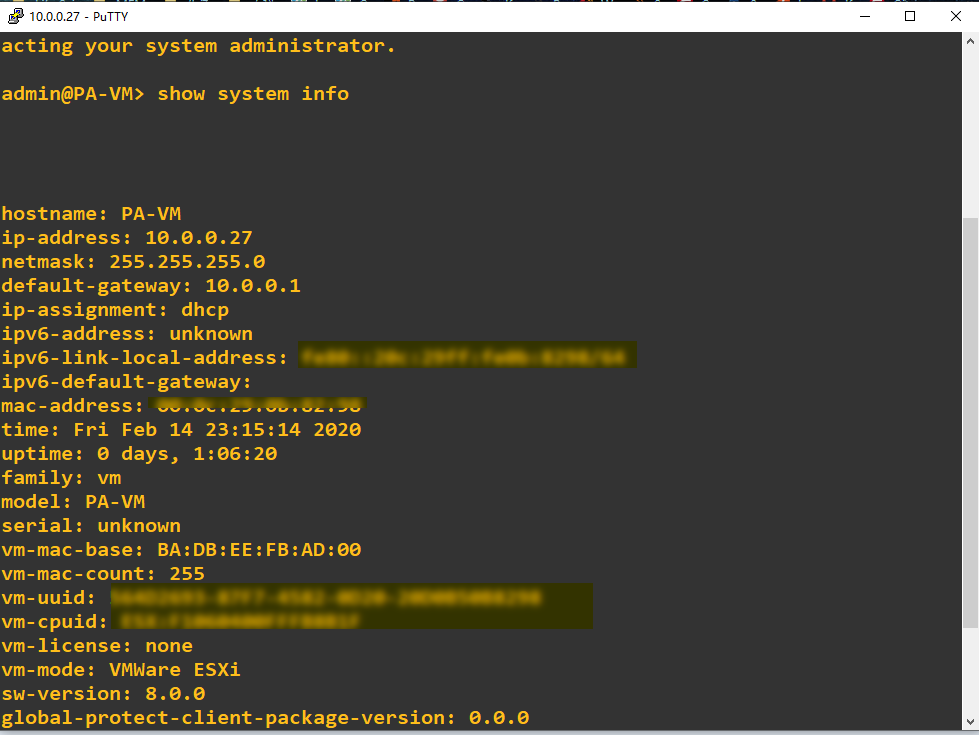
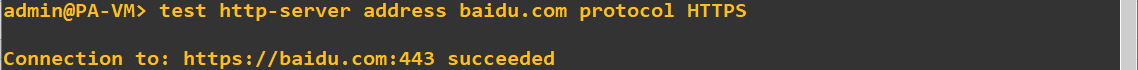
Console - Based Administration
Action commands - show, request, test, configure
CLI structure:{action}{section}{element}
show:
show system info
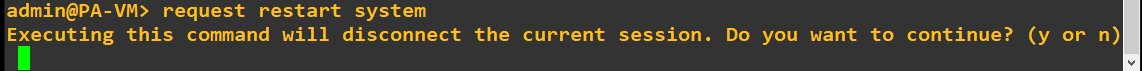
request:
request system restart
Test:
test vpn ike-sa gateway {name}
test vpn ipsec-sa gateway {name}
Device Management Overview
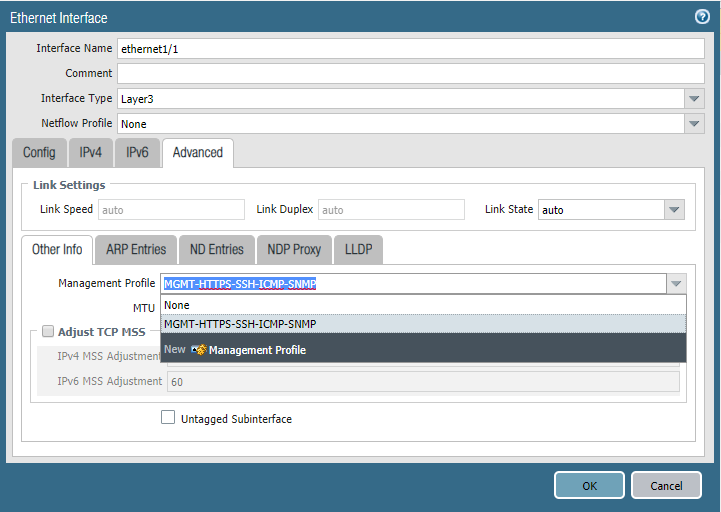
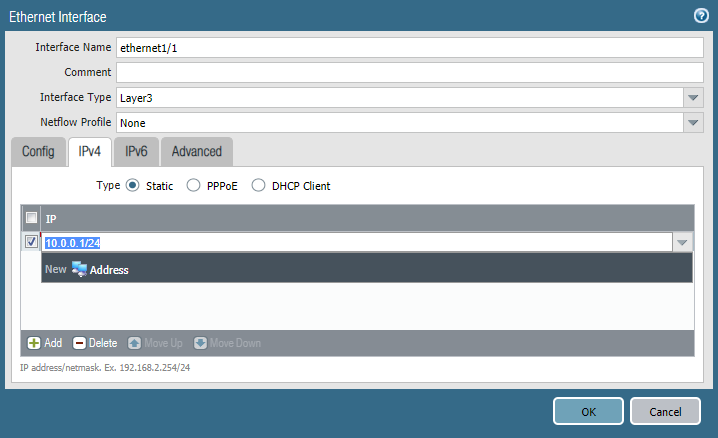
Interface Management Profile
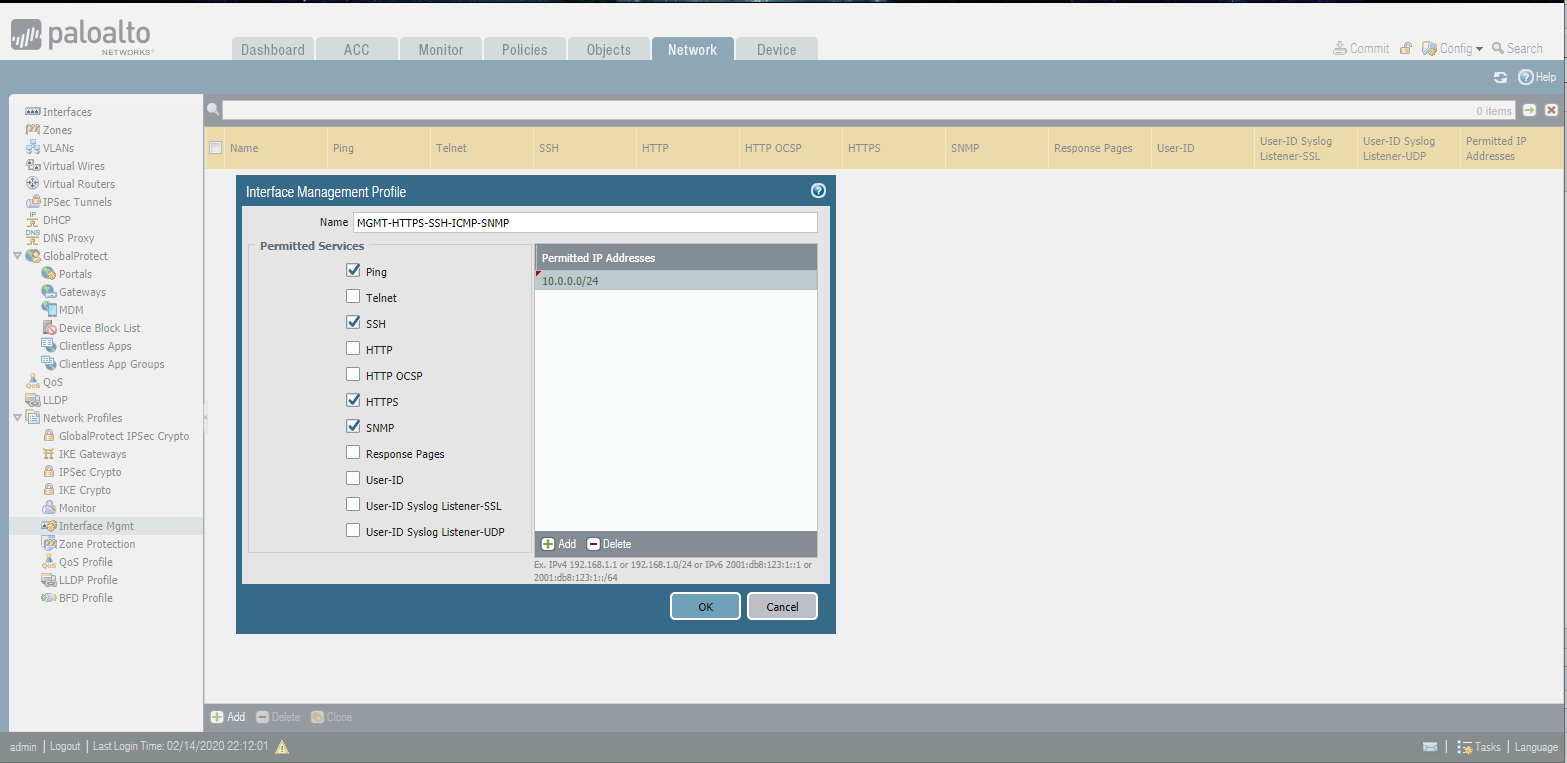
Ethernet Interface
Local admin
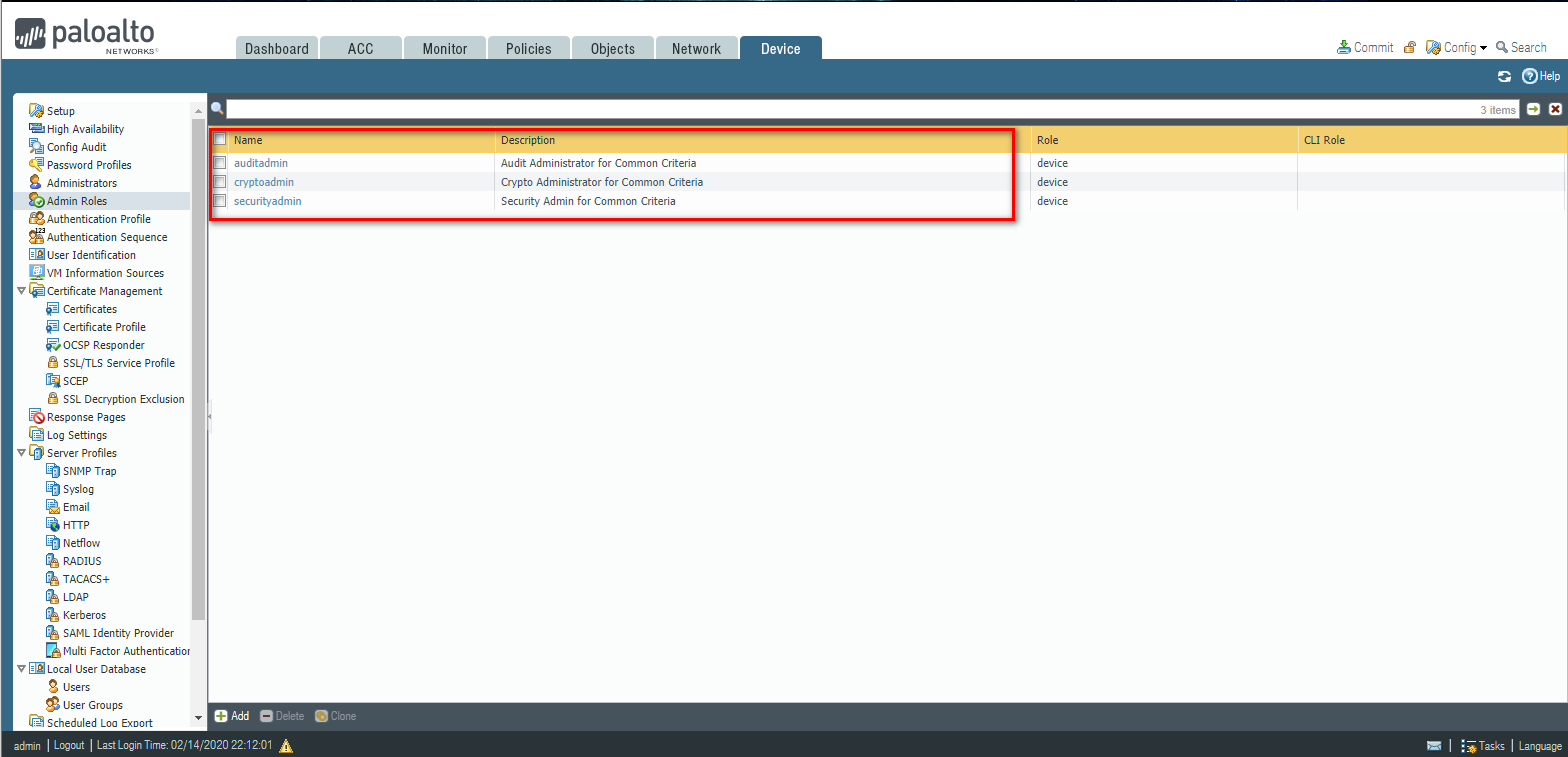
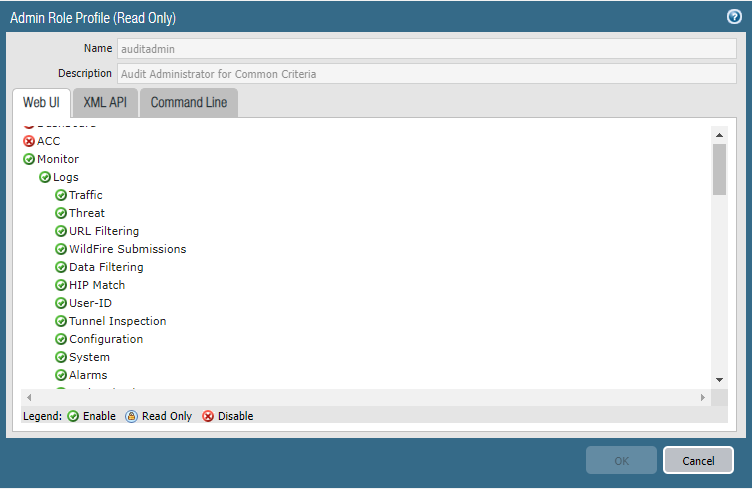
Create a new Role Profile(All function except Policies, Objects, Device, and Privacy.)
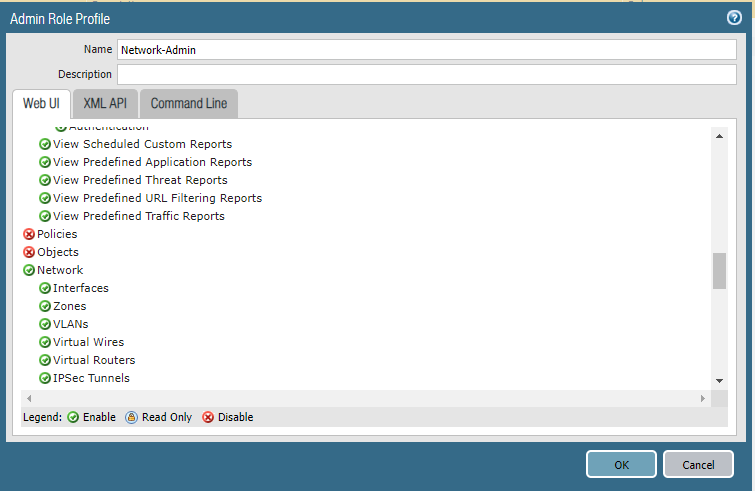
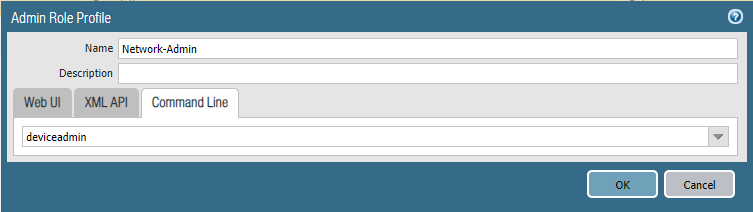
Add a new network administrator.

Cyber Security - Palo Alto Basic Introduction的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- 这篇文章,我们来谈一谈Spring中的属性注入
本系列文章: 读源码,我们可以从第一行读起 你知道Spring是怎么解析配置类的吗? 配置类为什么要添加@Configuration注解? 谈谈Spring中的对象跟Bean,你知道Spring怎么创 ...
- Linux 初始化系统 SystemV Upstart
System V 特点 缺点: 启动时间长,init是串行启动,只有前一个进程启动完,才会启动下一个进程 启动脚本复杂,init只是执行启动脚本,不管其他事情,脚本需要自己处理各种情况,这往往使得脚本 ...
- intellij配置github
一.在IDEA中设置Git,在File-->Setting->Version Control-->Git-->Path to Git executable选择你的git安装后的 ...
- Java WebService学习笔记 - Axis进阶(二)
上一篇 Java WebService学习笔记 - Axis(一) 前一篇博文中简单介绍了Axis的使用方法,这篇将介绍一些Axis的一些高级特性 Axis中Handler的使用 Handler ...
- Java WebService学习笔记 - Axis(一)
WebService 简介 实际开发中,很多系统都是基于历史遗留系统进行开发,有时,这些系统基于不同的语言,如C,C++,C#,java,PHP等等.为了实现历史系统的再利用,或向外部程序暴露调用接口 ...
- springboot_自动配置原理
目录 1.1 @SpringBootApplication 2.1 @EnableAutoConfiguration 2.1.1 @AutoConfigurationPackage 2.1.2 @Im ...
- 入门大数据---Flume 简介及基本使用
一.Flume简介 Apache Flume 是一个分布式,高可用的数据收集系统.它可以从不同的数据源收集数据,经过聚合后发送到存储系统中,通常用于日志数据的收集.Flume 分为 NG 和 OG ( ...
- css设置边框阴影;box-shadow的使用
html代码: <!DOCTYPE html> <html> <head> <meta charset="UTF-8"> <t ...
- JQuery UI - draggable参数中文详细说明
概述 在任何DOM元素启用拖动功能.通过单击鼠标并拖动对象在窗口内的任何地方移动. 官方示例地址:http://jqueryui.com/demos/draggable/ 所有的事件回调函数都有两个参 ...
- vim中设置tab的长度
