Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires
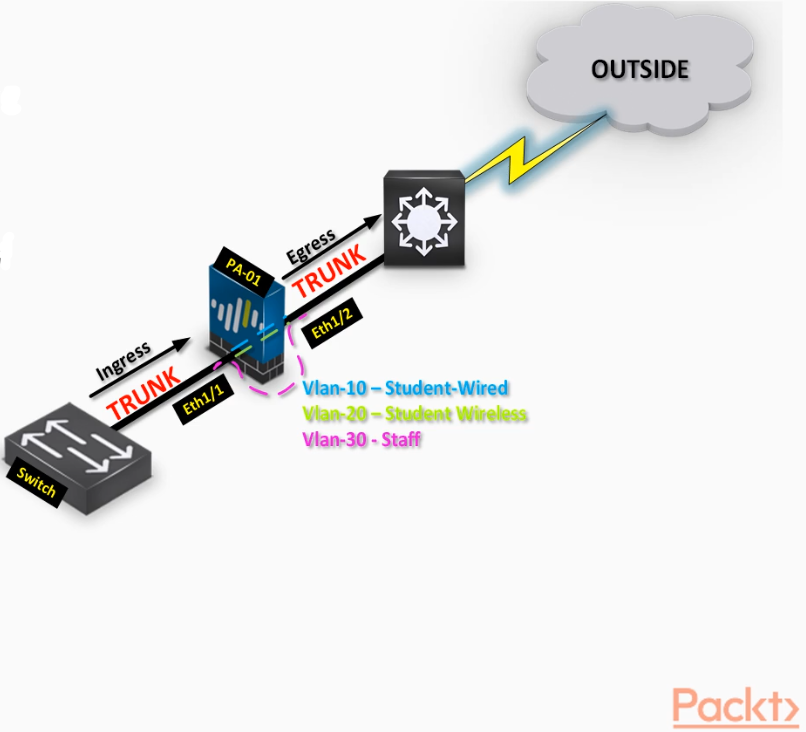
- Bridge two physical connections and apply security
- Policies without influencing any routing decision(transparent Firewall inspection)
- Inspect per VLAN traffic by creating V-Wire sub interfaces.
Interface configuration>>
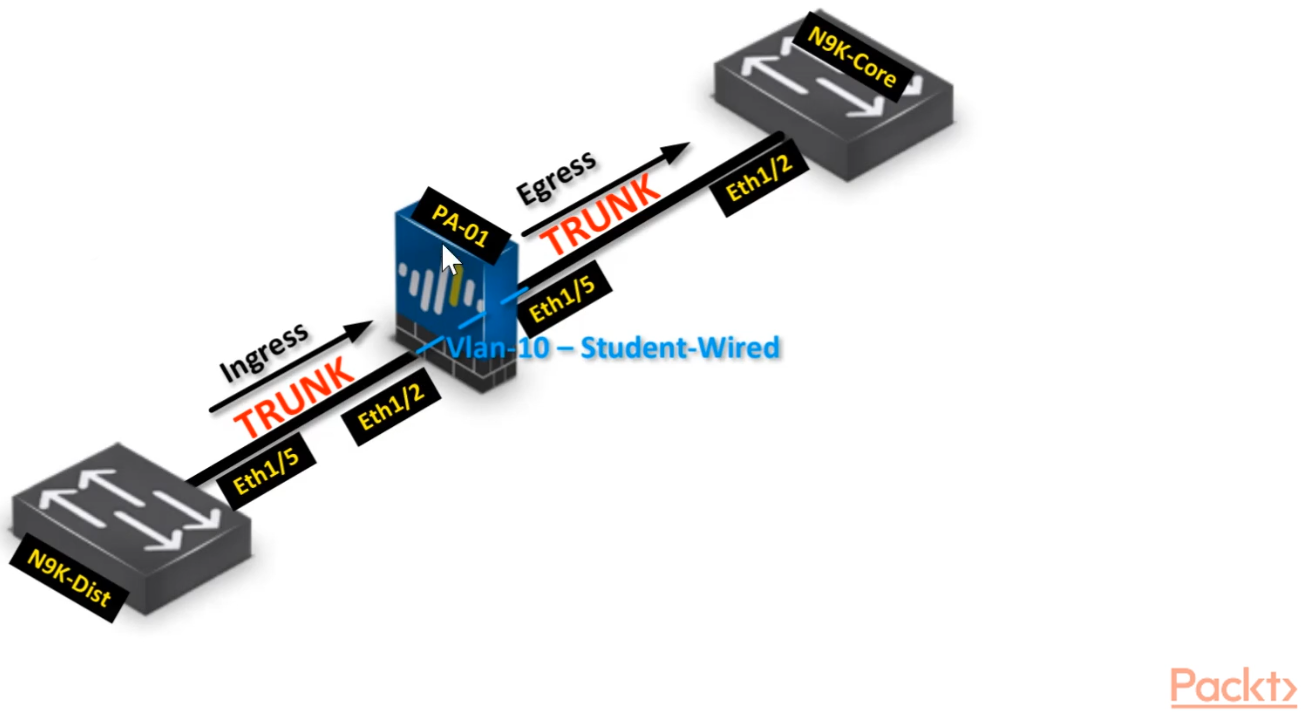
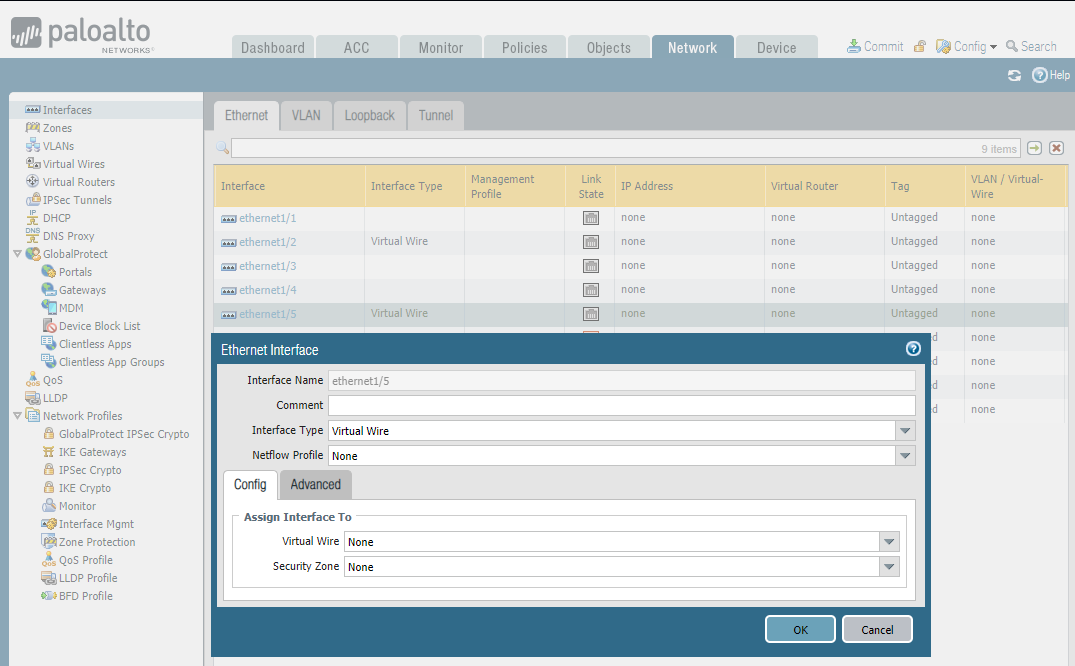
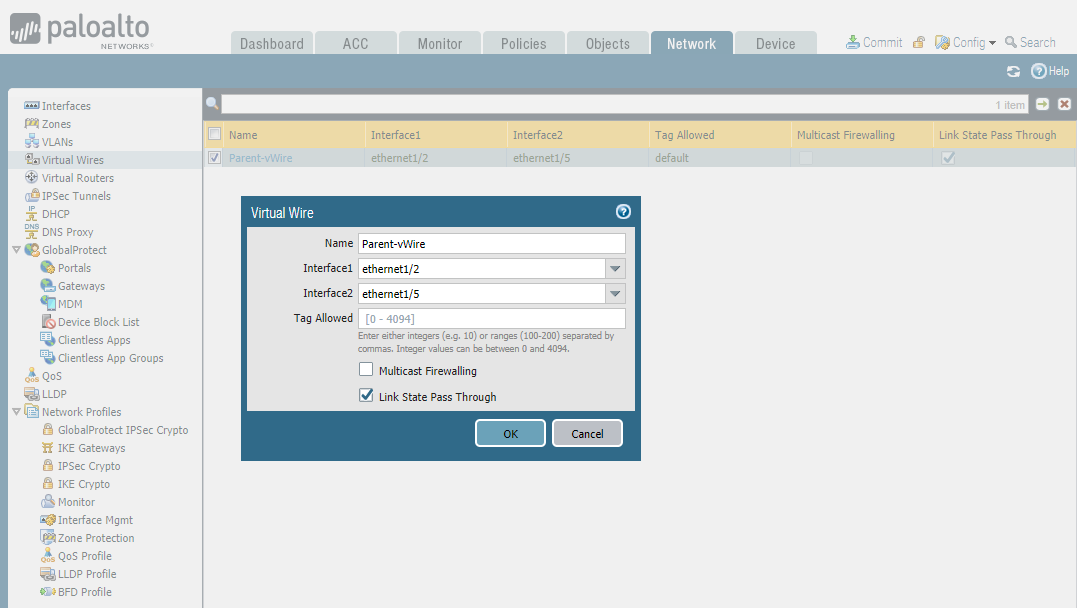
STEP1: Configure parent Virtual Wire interfaces - ethernet 1/2 and ethernet 1/5
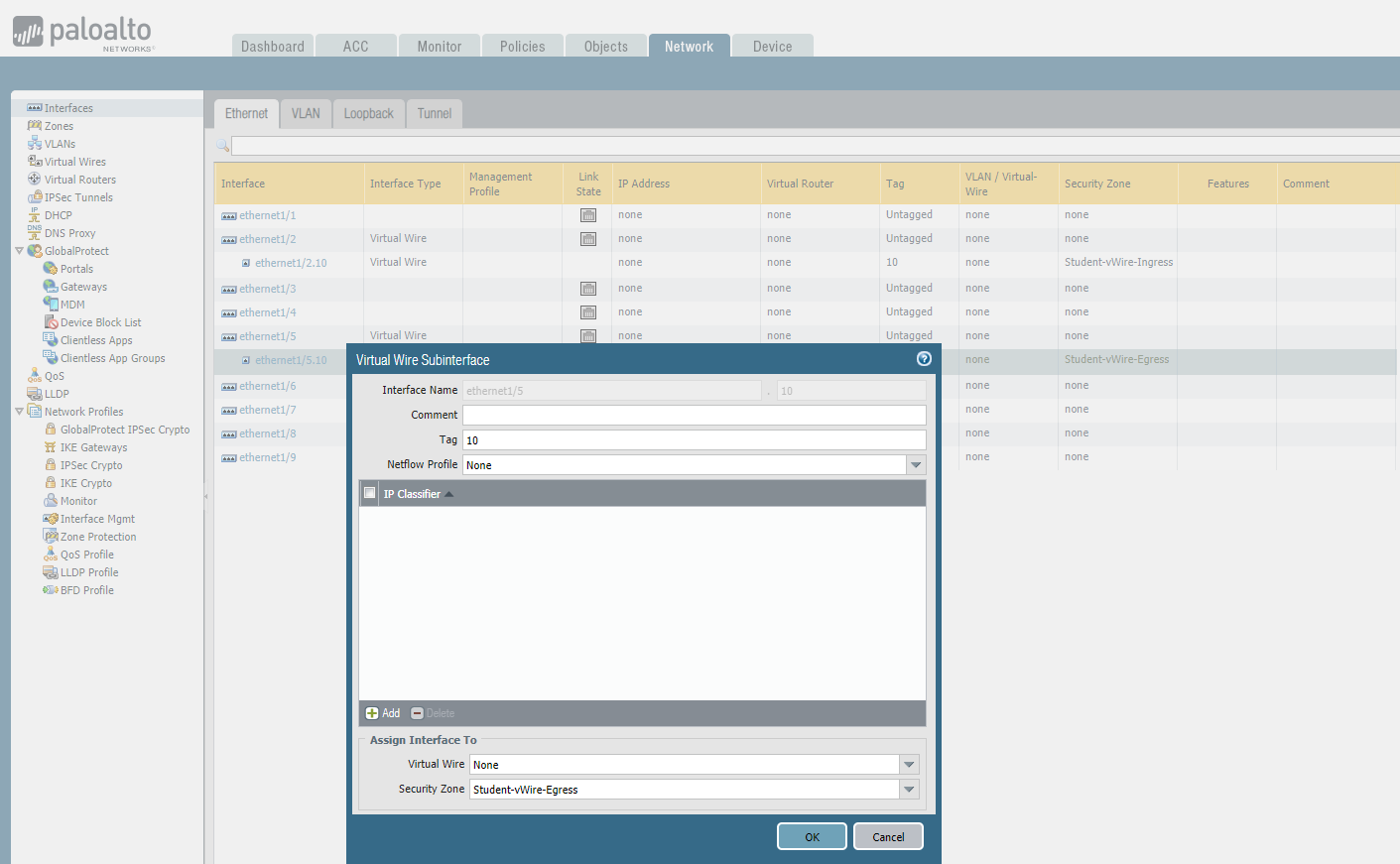
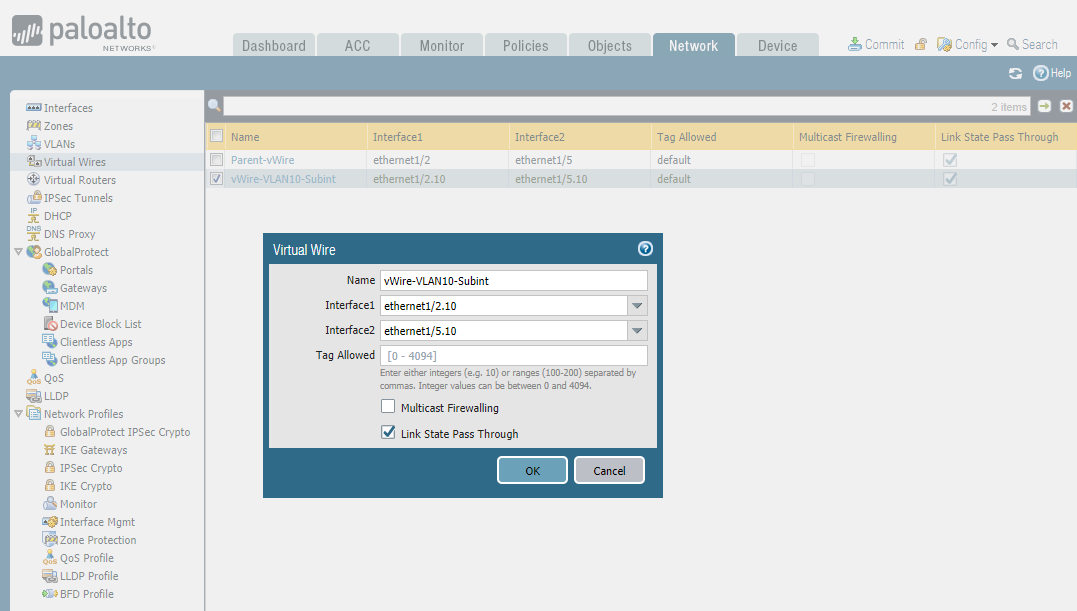
STEP2: Configure subinterface - ethernet1/2.10 and ethernet 1/5/10
STEP3: Connect virtual wires - Parent-vWire
STEP4: Connect virtual wires - Sub-vWire
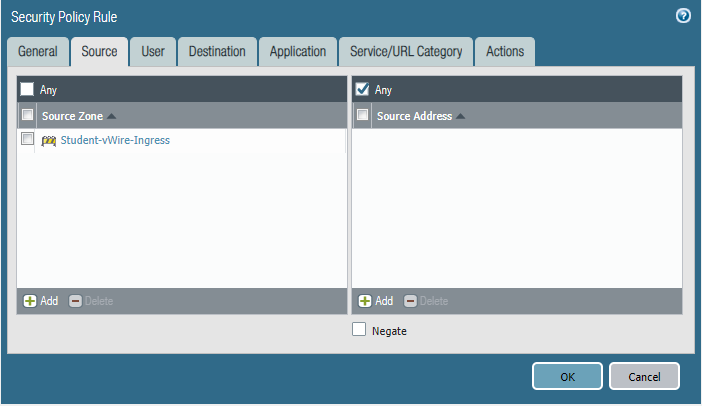
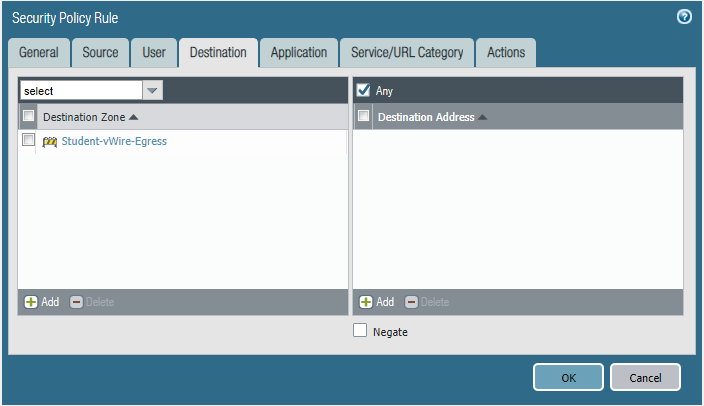
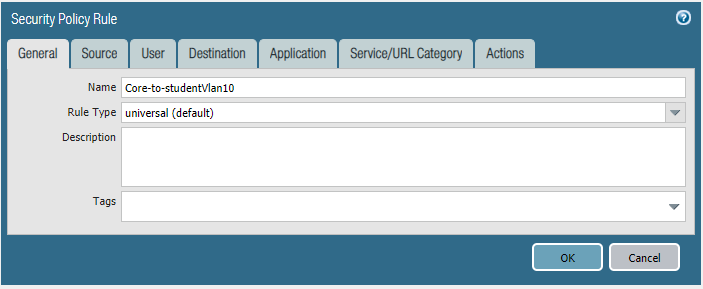
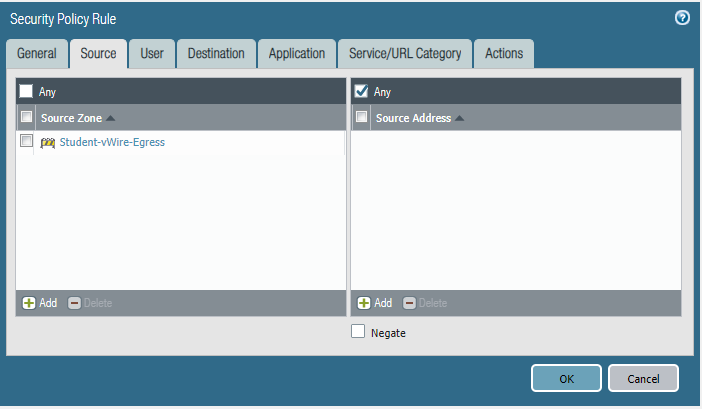
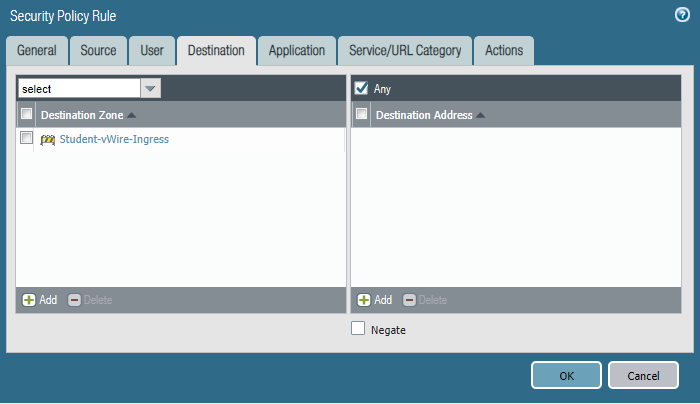
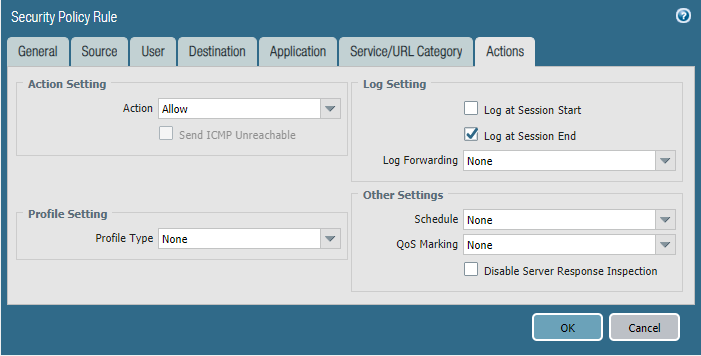
STEP5: Configure security policies.
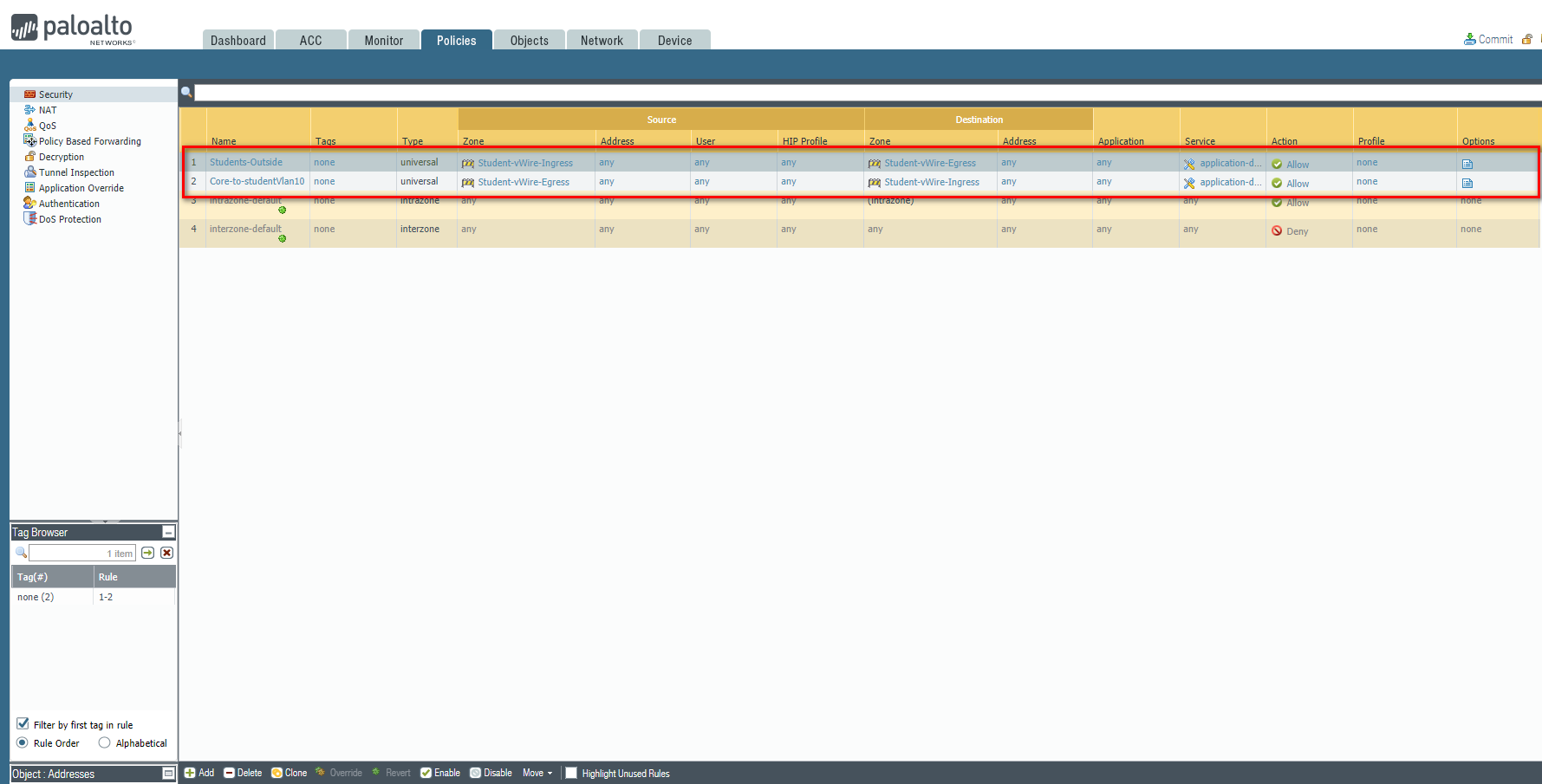
Students-Outside
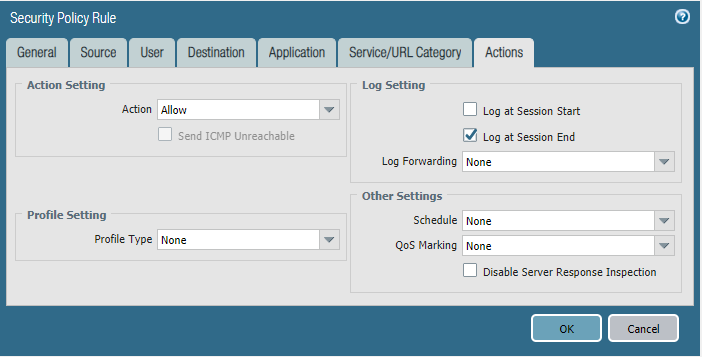
Core-to-studentVlan10
Commit the configuration and test.
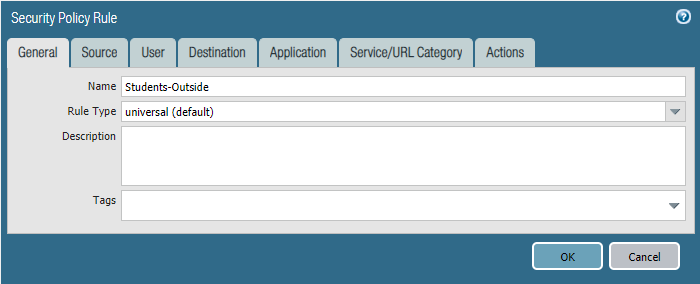
Students-Outside
Cyber Security - Palo Alto Firewall V-Wires的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- cb34a_c++_STL_算法_查找算法_(7)_lower_bound
cb34a_c++_STL_算法_查找算法_(7)_lower_bound//针对已序区间的查找算法,如set,multiset关联容器-自动排序lower_bound()--第一个可能的位置uppe ...
- CFS三层网络环境靶场实战
一.环境搭建: ①根据作者公开的靶机信息整理 共有三个targets,目标是拿下三台主机权限,且是三层的网络环境,内网网段有192.168.22.0/24和192.168.33.0/24,添加两张仅主 ...
- Linux监控CPU,内存,磁盘I/O
简单讲讲Linux下监控 [CPU] 监控CPU,top命令能够实时监控系统的运行状态,并且可以按照CPU.内存和执行时间进行排序,同时top命令还可以通过交互式命令进行设定显示,通过top命令可以查 ...
- 使用DragonFly进行智能镜像分发
Dragonfly 是一款基于 P2P 的智能镜像和文件分发工具.它旨在提高文件传输的效率和速率,最大限度地利用网络带宽,尤其是在分发大量数据时,例如应用分发.缓存分发.日志分发和镜像分发. 在阿里巴 ...
- 2.WebPack初始化
一.Package.json 在项目中输入: npm init 之后会提示你一步一步输入信息,我输入的信息如下: 生成的Package.json文件如下 我们也可以在初始时省略这些步骤,让脚本使用默认 ...
- SpringMVC拦截器使用
源码地址 拦截器interceptor 拦截器是URL请求的第一道门,所有请求会先经过拦截器interceptor,然后再进入controller: 下面,记录一种通过注解方法拦截所有需要登录才能发起 ...
- maven中pom.xml中配置整理: groupId、artifactId、parent、dependency、dependencyManagement区别
<groupId>com.mycompany.commonmaven</groupId> <artifactId>commonmaven</artifactI ...
- java代理,静态代理、jdk代理、cglib代理、Aspectj
我实在接触spring的时候才接触到代理这个东西的,一直想整理一下笔记. 什么是代理模式:代理模式是通过代理对象访问目标对象,这样可以在目标对象基础上增强额外的功能.简单来说就是要创建一个新的对象,我 ...
- git配置用户和邮箱
1. 查看git用户配置 git config user.name 2. 查看git邮箱配置 git config user.email 3. 配置git用户 git config --global ...
- 哈希传递攻击利用(Pass The Hash)
最近又复习了一下内网的相关知识,把以前的整理了一下发出来做个记录. 0x01 哈希传递攻击概念 有一点内网渗透经验的都应该听说过哈希传递攻击,通过找到相应账户相关的密码散列值(LM Hash,NTLM ...
