Cyber Security - Palo Alto Security Policies(2)
Task 3
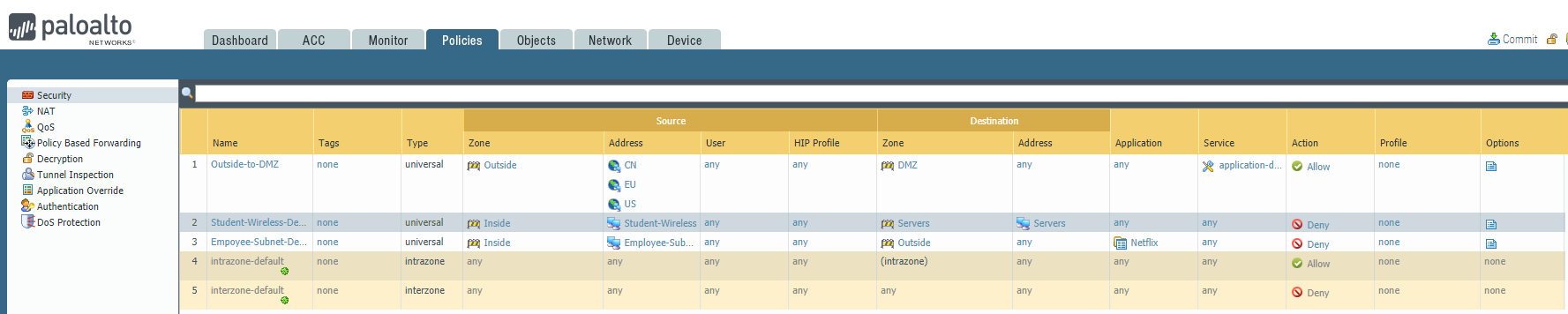
The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to one of our eCommerce Server HTTPS portals in a matter of minutes. The source address identified by our SOC came from Africa and we only serve customers in the United States, China, and Europe.
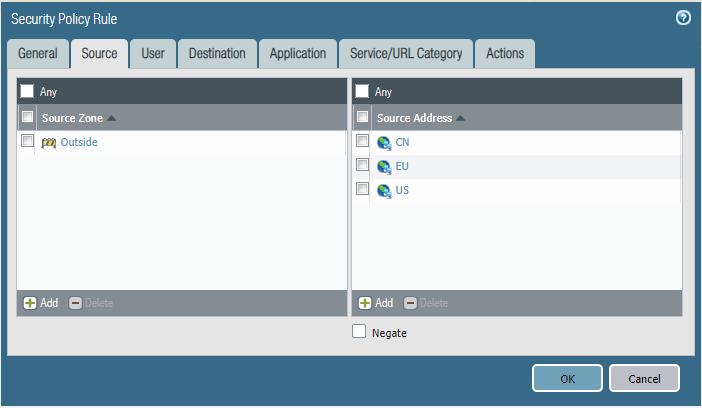
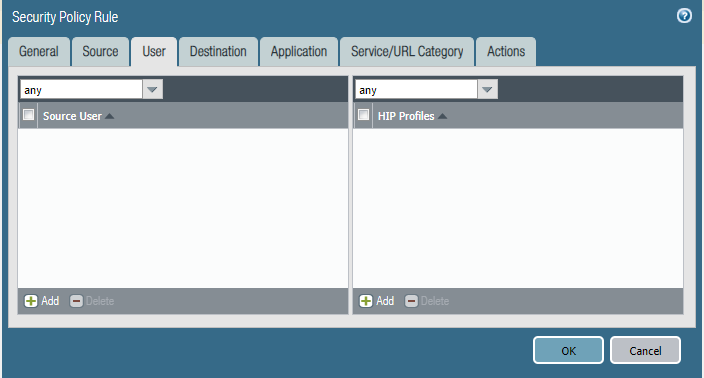
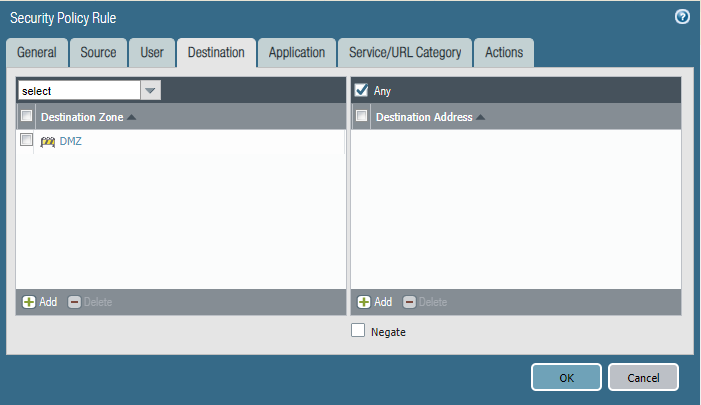
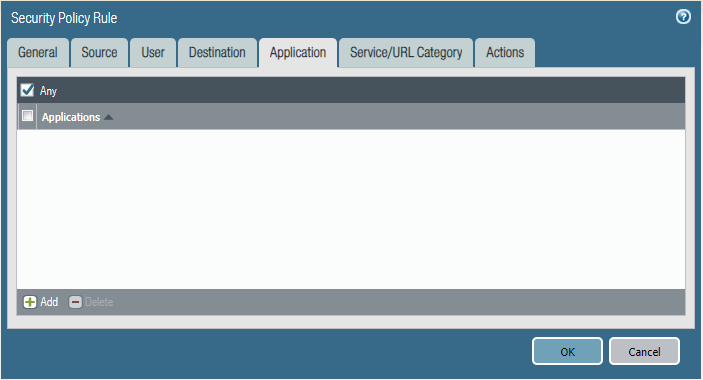
Please block access to our DMZ from all the internet but allow the USA, China, and Europe.
Configure the firewall policy. Please mind that the order of this policy may affect the effect.


Task 4
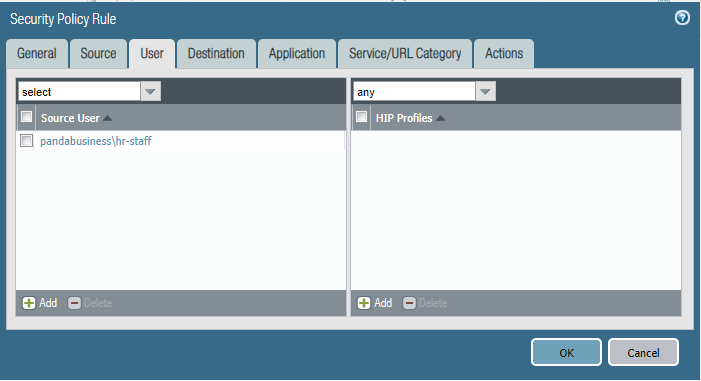
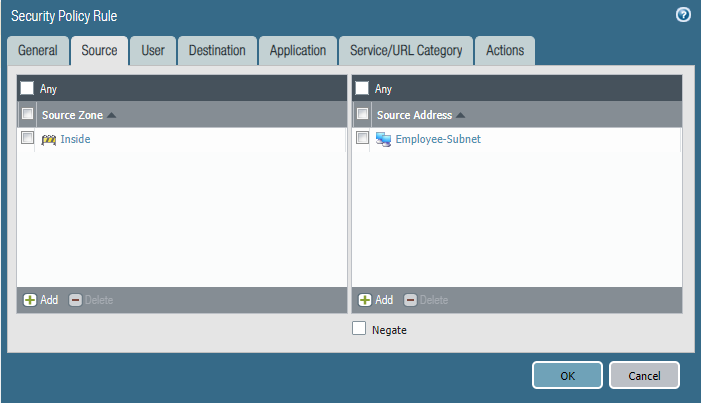
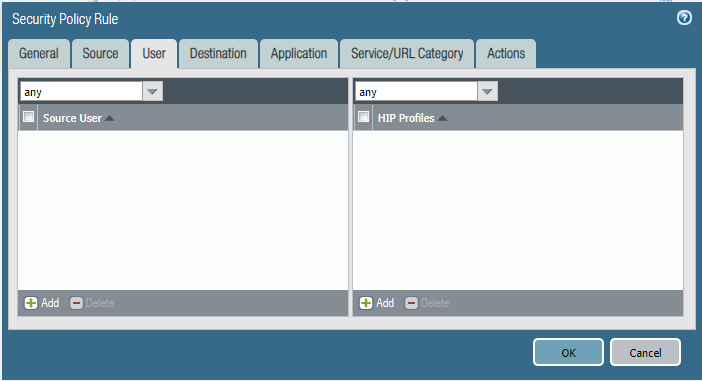
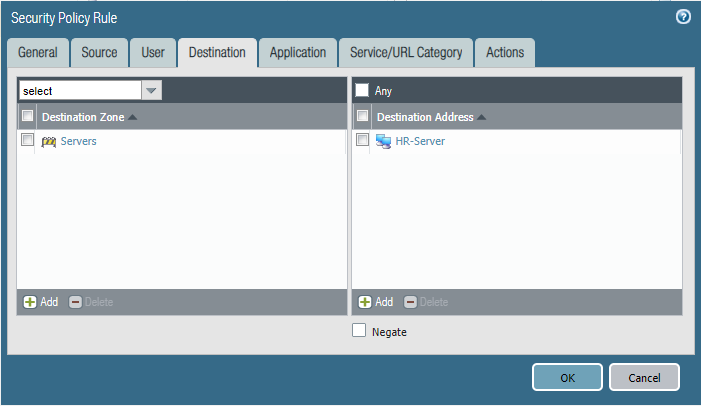
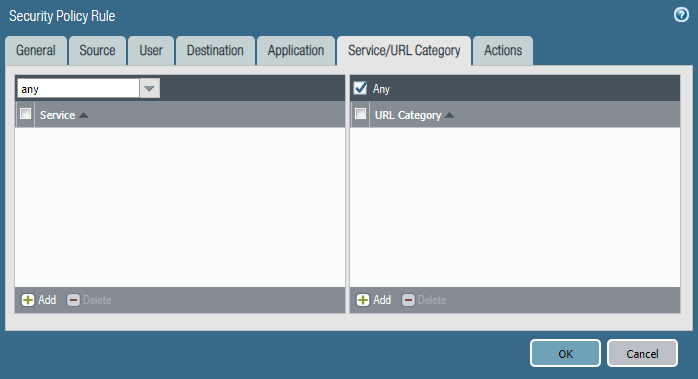
Last week after a policy change by another engineer, users from the marketing department were able to access the HR Fileserver shares.
Can you identify the root cause and remediate this issue asap?
Configure firewall policies.
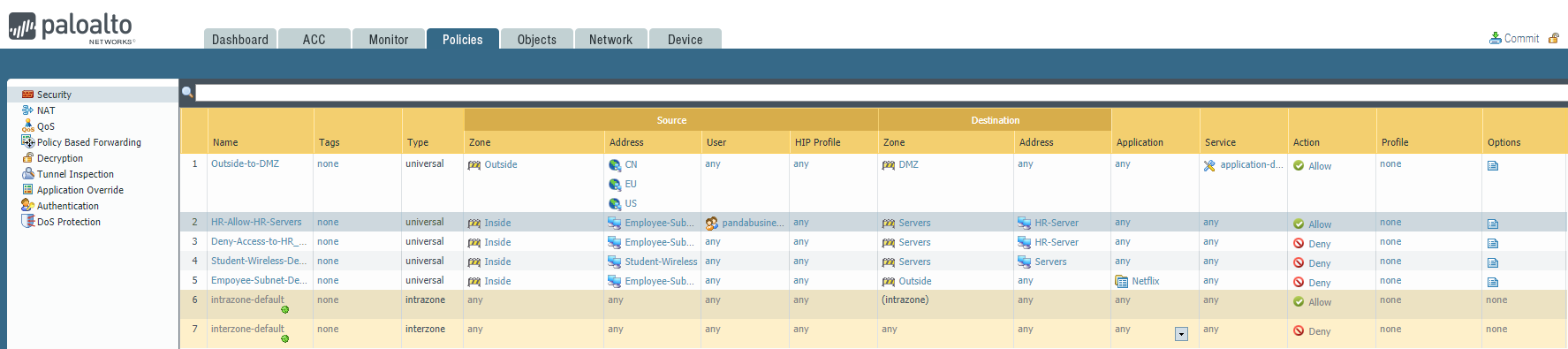
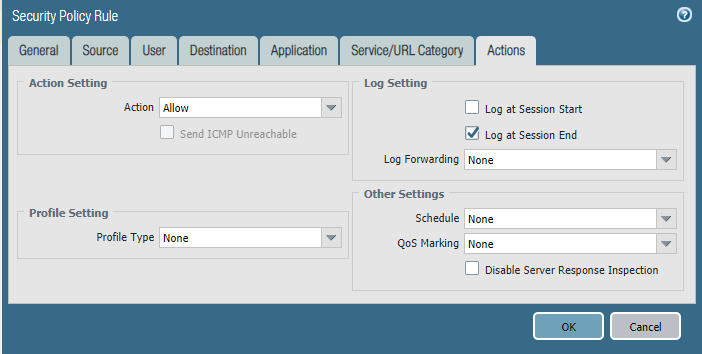
Policy one: HR-Allow-HR-Servers


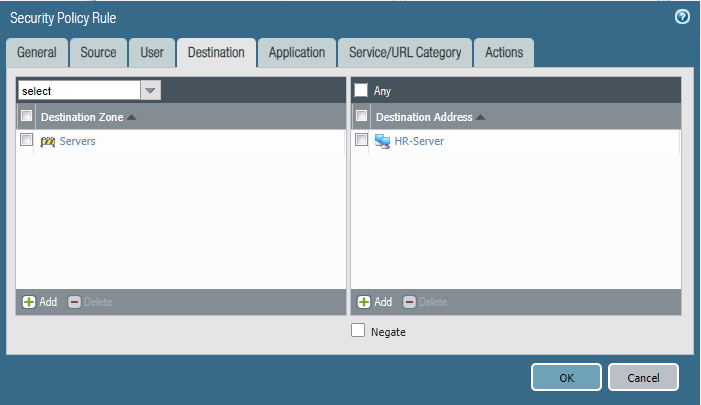
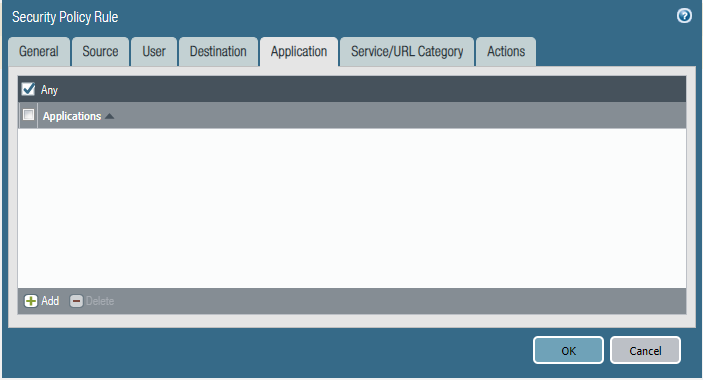
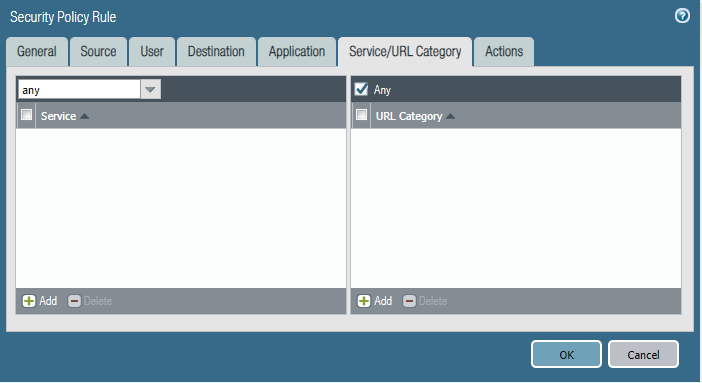

Policy Two: Deny-Access-to-HR_Servers



Cyber Security - Palo Alto Security Policies(2)的更多相关文章
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- Appium查看应用包名
方式一没有apk 如果应用已经安装在手机上了(例如应用商城下载).可以直接打开手机上该应用, 进入到要操作的界面然后执行: adb shell dumpsys activity recents | f ...
- Linux系统结构详解(转)
Linux系统一般有4个主要部分: 内核.shell.文件系统和应用程序.内核.shell和文件系统一起形成了基本的操作系统结构,它们使得用户可以运行程序.管理文件并使用系统.部分层次结构如图1-1所 ...
- Java WebService _CXF、Xfire、AXIS2、AXIS1_四种发布方式(使用整理)
目录 1. CXF方式2. Xfire方式3. AXIS2方式4. AXIS1方式5. AXIS1客户端调用6. AXIS2客户端调用7. CXF客户端调用8. Web Service Client客 ...
- 计算机网络之DDOS
1.什么是DDOS DDOS(Distributed Denial of Service),中文意思为“分布式拒绝服务”,就是利用大量合法的分布式服务器对目标发送请求,从而导致正常合法用户无法获得服务 ...
- Flask01-HelloWorld
# flask学习 参考:http://www.pythondoc.com/flask-mega-tutorial/ ## python3. 默认支持虚拟环境使用(用最简单的方法,解决问题) wget ...
- 入门大数据---Spark累加器与广播变量
一.简介 在 Spark 中,提供了两种类型的共享变量:累加器 (accumulator) 与广播变量 (broadcast variable): 累加器:用来对信息进行聚合,主要用于累计计数等场景: ...
- egret Exml自定义组件
有个需求,在A组件里面包裹 B组件: 碰到了一些奇怪的问题,这些问题是由于编辑器bug引起的.创建了皮肤后并没有在default.thm.json直接添加进去,造成拖动组件莫名其妙的bug,这里忘记保 ...
- Oracle 导出、导入某用户所有数据(包括表、视图、存储过程...)
Oracle 导出.导入某用户所有数据(包括表.视图.存储过程...)前提:在CMD 命令下 导出命令:exp 用户名/密码@数据库 owner=用户名 file=文件存储路径(如:F:\abcd.d ...
- java语言基础(六)_String类_static_Arrays类_Math类
String类 1. 使用 java.lang.String类代表字符串.lang包含的包不用特意引用,即默认已经引用了. API当中说:Java 程序中的所有字符串字面值(如 "abc&q ...
- [Python] datetime.timedelta模块用法
python使用datetime模块timedelta实现日期时间相加: python计算明天的日期: from datetime import datetime from datetime impo ...
