A simple introduction to Three kinds of Delegation of Kerberos
1.What is Delegation?
Just like the name. Delegation is that a server pretend to behalf of a user and to authenticate with kerberos protocol.There are three kinds of delegations.
| Kinds of Delegations | Limitions | Protocol | Note |
|---|---|---|---|
| Unconstrained Delegation | None | Just forward the TGT ticket which is able to be forwarded | None |
| Constrained Delegation | Front-End Server decide which Back-End service can receive delegation | 1.S4U2Proxy -> Forward the TGT ticket 2.S4U2Self -> Receive information of NTLM Authentication(Username&NTLM-Hash) And use that to get TGT and send TGT and receive TGS from KDC |
AD administrator account |
| Resource-Based Constrained Delegation | Back-End Services decide which Front-End service's delegation can be received | The same as Constrained Delegation | 1.S4U2Proxy -> Can Forward TGT ticket which is not to be able to forwarded. 2.You can use this cross the domain. 3.Service administrator account |
2.Unconstrained Delegation
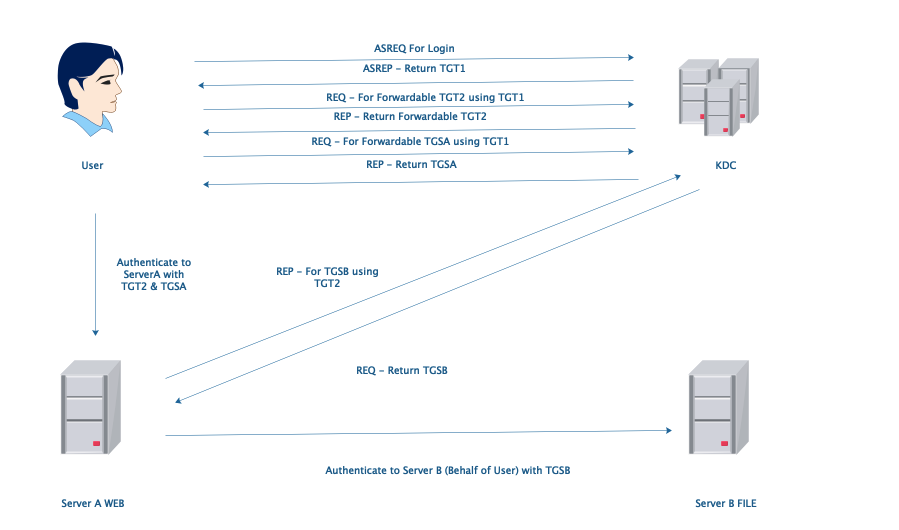
Unconstrained Delegation: ServerA can authenticate to any server in this domain behalf of user with TGT2. It is too dangerous.
3.Constrained Delegation
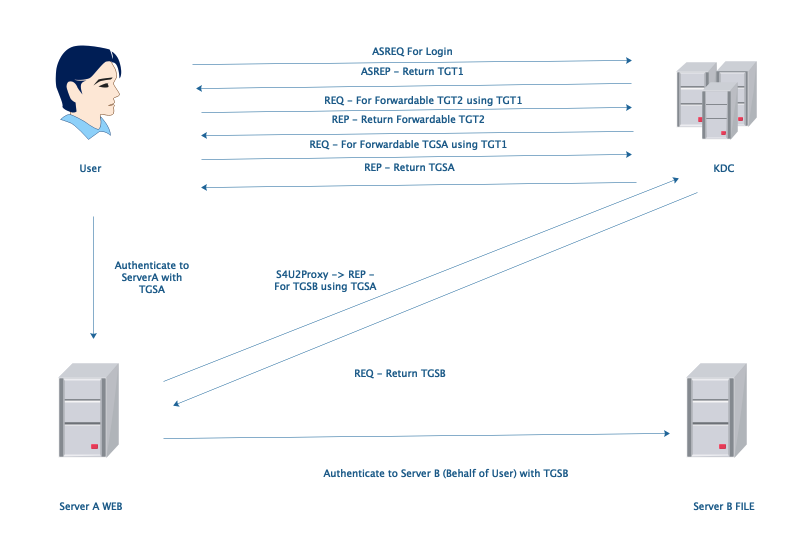
Only S4U2Proxy is what we need, if user use kerberos ticket to authenticate. Otherwise we need both S4U2Self and S4U2Proxy if user use NTLM hash to authenticate. In this condition, AD administrators can configure which service(SPNs) can receive ServerA’s delegation in ServerA's msDC-AllowedToDelegateTo property.
4.Resource-Based Constrained Delegation
There is one important difference between Constrained Delegation and Resource-Based Constrained Delegation. In Constrained Delegation, administrators of AD can configure which service can receive ServerA's delegation in their msDS-AllowedToActOnBehalfOfOtherIdentity properties. However, In Resource-Based Constrained Delegation, administrators of services can decide if those service will receive the ServerA's delegation or not. And it should be configured on the computers which is running those services. Do you think Resource-Based Constrained Delegation is much more safe than Constrained Delegation? No, Resource-Based Constrained Delegation has a big problem. In this condition, S4U2Proxy can forward unforwardable TGT and KDC will return TGS back. So if we could get the TGT which is not able to forward, We also could use it to do something bad.
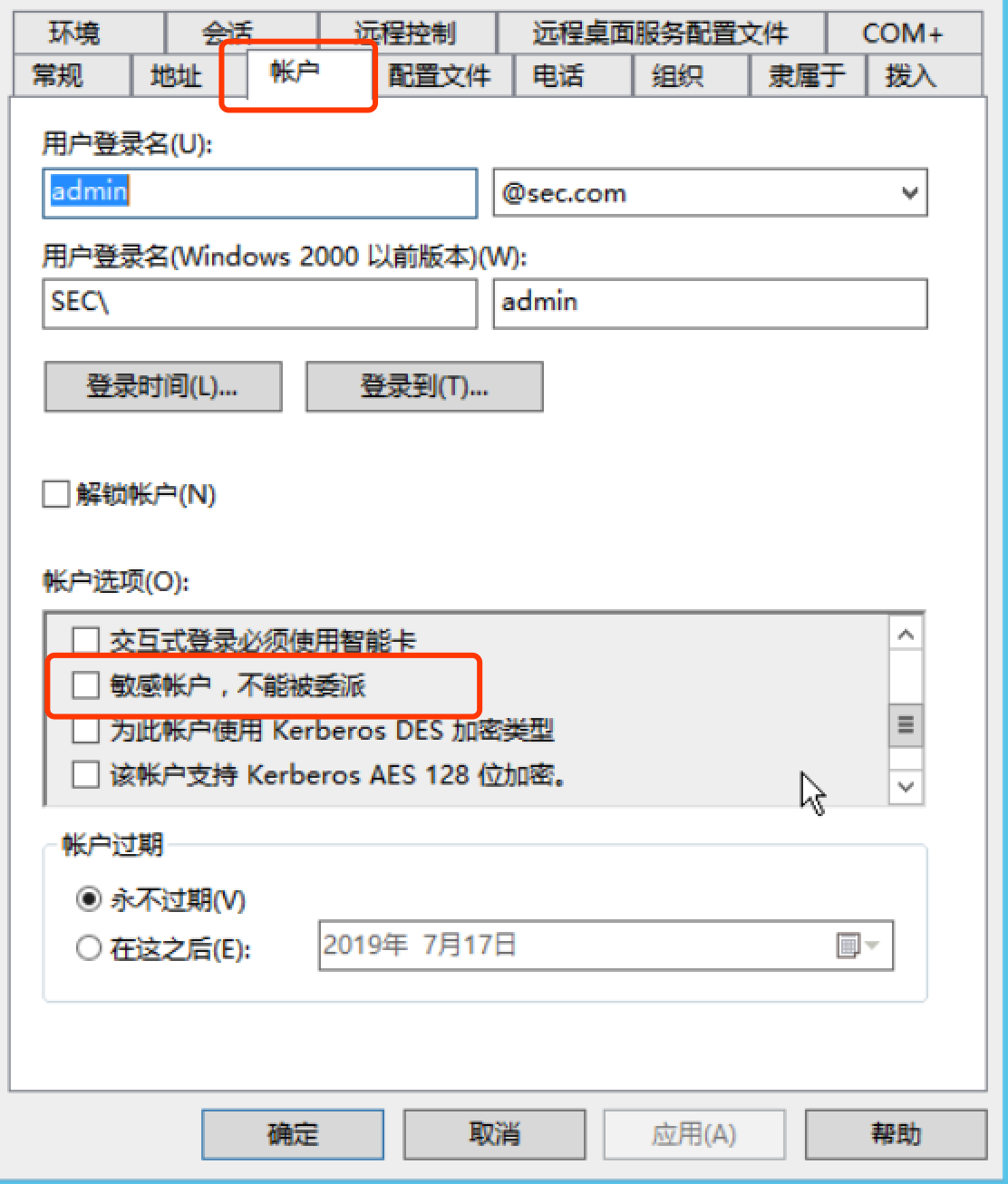
5. What we can do to make it a little more safe?
** We can do a lot of things to make it more safe. Plus, the first one is to configure like this.**
A simple introduction to Three kinds of Delegation of Kerberos的更多相关文章
- A Simple Introduction To Computer Networking
Most networking discussions are a jumble of acronyms. Forget the configuration details - what are th ...
- The Most Simple Introduction to Hypothesis Testing
https://www.youtube.com/watch?v=UApFKiK4Hi8
- 转:Simple Introduction to Dirichlet Process
来源:http://hi.baidu.com/vyfrcemnsnbgxyd/item/2f10ecc3fc35597dced4f88b Dirichlet Process(DP)是一个很重要的统计模 ...
- An Introduction to Variational Methods (5.1)
在这篇文章中,我引用Bishop书中的一个例子,来简单介绍一下Variational Methods的应用.想要更详细地理解这个例子,可以参考Bishop的书Pattern Recongnition ...
- 深度强化学习(Deep Reinforcement Learning)入门:RL base & DQN-DDPG-A3C introduction
转自https://zhuanlan.zhihu.com/p/25239682 过去的一段时间在深度强化学习领域投入了不少精力,工作中也在应用DRL解决业务问题.子曰:温故而知新,在进一步深入研究和应 ...
- ML Lecture 0-1: Introduction of Machine Learning
本博客是针对李宏毅教授在Youtube上上传的课程视频<ML Lecture 0-1: Introduction of Machine Learning>的学习笔记.在Github上也po ...
- CI Weekly #6 | 再谈 Docker / CI / CD 实践经验
CI Weekly 围绕『 软件工程效率提升』 进行一系列技术内容分享,包括国内外持续集成.持续交付,持续部署.自动化测试. DevOps 等实践教程.工具与资源,以及一些工程师文化相关的程序员 Ti ...
- 理解callback function in javascript
以下内容主要摘自[1,2] (1)In javascript, functions are first-class objects, which means functions can be used ...
- Discovering the Computer Science Behind Postgres Indexes
This is the last in a series of Postgres posts that Pat Shaughnessy wrote based on his presentation ...
随机推荐
- Slack完整教学与上手心得:找到正确的团队沟通之道
Slack完整教学与上手心得:找到正确的团队沟通之道 时间 2015-06-13 09:21:42 逐鹿网 原文 http://www.zhulu.com/article/5519.html 主题 ...
- LeetCode 120. Triangle三角形最小路径和 (C++)
题目: Given a triangle, find the minimum path sum from top to bottom. Each step you may move to adjace ...
- 论文阅读笔记六十:Squeeze-and-Excitation Networks(SENet CVPR2017)
论文原址:https://arxiv.org/abs/1709.01507 github:https://github.com/hujie-frank/SENet 摘要 卷积网络的关键构件是卷积操作, ...
- Mysql对表中 数据 的操作 DML
上一知识点回顾: mysql的备份: 直接使用navicat进行备份 转储SQL文件:有结构和数据/ 仅结构 两种 需要还原时 单击 数据库名字 运行SQL文件 创建表ctreate 修改表alt ...
- 如何确保redis中都是热数据
相关知识:redis 内存数据集大小上升到一定大小的时候,就会施行数据淘汰策略. redis 提供 6种数据淘汰策略: voltile-lru:从已设置过期时间的数据集(server.db[i].ex ...
- Boost Graph Library使用学习
Boost Graph Library,BGL 使用学习 探索 Boost Graph Library https://www.ibm.com/developerworks/cn/aix/librar ...
- RAMOS与PE 到底哪里不一样?
RAMOS与PE 到底哪里不一样? 答:PE只是RAMOS的雏形.无论是system身份还是Administrator身份登录的PE都不能算是真正意义上的RAMOS. 号外号外,下面开始跑题..... ...
- [LeetCode] 662. Maximum Width of Binary Tree 二叉树的最大宽度
Given a binary tree, write a function to get the maximum width of the given tree. The width of a tre ...
- [LeetCode] 222. Count Complete Tree Nodes 求完全二叉树的节点个数
Given a complete binary tree, count the number of nodes. Note: Definition of a complete binary tree ...
- JavaScript 系列--JavaScript一些奇淫技巧的实现方法(三)数字取整,数组求和
一.前言 简短的sleep函数,获取时间戳:https://www.mwcxs.top/page/746.html 数字格式化 1234567890 --> 1,234,567,890:argr ...
