Jack Straws(POJ 1127)
- 原题如下:
Jack Straws
Time Limit: 1000MS Memory Limit: 10000K Total Submissions: 5555 Accepted: 2536 Description
In the game of Jack Straws, a number of plastic or wooden "straws" are dumped on the table and players try to remove them one-by-one without disturbing the other straws. Here, we are only concerned with if various pairs of straws are connected by a path of touching straws. You will be given a list of the endpoints for some straws (as if they were dumped on a large piece of graph paper) and then will be asked if various pairs of straws are connected. Note that touching is connecting, but also two straws can be connected indirectly via other connected straws.Input
Input consist multiple case,each case consists of multiple lines. The first line will be an integer n (1 < n < 13) giving the number of straws on the table. Each of the next n lines contain 4 positive integers,x1,y1,x2 and y2, giving the coordinates, (x1,y1),(x2,y2) of the endpoints of a single straw. All coordinates will be less than 100. (Note that the straws will be of varying lengths.) The first straw entered will be known as straw #1, the second as straw #2, and so on. The remaining lines of the current case(except for the final line) will each contain two positive integers, a and b, both between 1 and n, inclusive. You are to determine if straw a can be connected to straw b. When a = 0 = b, the current case is terminated.When n=0,the input is terminated.
There will be no illegal input and there are no zero-length straws.
Output
You should generate a line of output for each line containing a pair a and b, except the final line where a = 0 = b. The line should say simply "CONNECTED", if straw a is connected to straw b, or "NOT CONNECTED", if straw a is not connected to straw b. For our purposes, a straw is considered connected to itself.Sample Input
7
1 6 3 3
4 6 4 9
4 5 6 7
1 4 3 5
3 5 5 5
5 2 6 3
5 4 7 2
1 4
1 6
3 3
6 7
2 3
1 3
0 0 2
0 2 0 0
0 0 0 1
1 1
2 2
1 2
0 0 0Sample Output
CONNECTED
NOT CONNECTED
CONNECTED
CONNECTED
NOT CONNECTED
CONNECTED
CONNECTED
CONNECTED
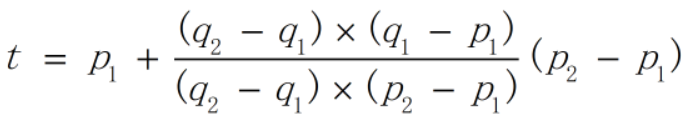
CONNECTED - 题解:问题的关键是判断线段是否相交,然后就可以建图进行连接性判断。首先会想到计算两直线的交点然后判断交点是否在线段上的方法,这样问题就变成如何判断点是否在线段上以及如何求两直线的交点。在几何问题中,运用向量的内积和外积进行计算是非常方便的。对于二维向量p1=(x1,y1)和p2=(x2,y2),定义内积p1·p2=x1x2+y1y2,外积p1×p2=x1y2-y1x2。要判断点q是否在线段p1-p2上,只要先根据外积(p1-q)×(p2-q)是否等于0来判断点q是否在直线p1-p2上,再利用内积(p1-q)·(p2-q)是否小于等于0来判断点q是否落在p1-p2之间。而要求两直线的交点,通过变量t将直线p1-p2上的点表示为p1+t(p2-p1),交点又在直线q1-q2上,所以有:(q2-q1)×(p1+t(p2-p1)-q1)=0,于是可以利用下式求得t的值:
但是,使用这个方法还要注意边界情况,如果两条线段是平行的,也有可能有公共点,可以通过检查端点是否在另一条线段上来判断。 - 代码:
#include <cstdio>
#include <cmath>
#include <algorithm> using namespace std; const double EPS=1e-; double add(double a, double b)
{
if (fabs(a+b)<EPS*(fabs(a)+fabs(b))) return ;
return a+b;
} struct P
{
double x,y;
P(){};
P(double x, double y):x(x),y(y){}
P operator + (P p)
{
return P(add(x, p.x), add(y, p.y));
}
P operator - (P p)
{
return P(add(x, -p.x), add(y, -p.y));
}
P operator * (double d)
{
return P(x*d, y*d);
}
double dot(P p)
{
return add(x*p.x, y*p.y);
}
double det(P p)
{
return add(x*p.y, -y*p.x);
}
}; bool on_seg(P p1, P p2, P q)
{
return (p1-q).det(p2-q)== && (p1-q).dot(p2-q)<=;
} P intersection(P p1, P p2, P q1, P q2)
{
return p1+(p2-p1)*((q2-q1).det(q1-p1)/(q2-q1).det(p2-p1));
} const int MAX_N=;
const int MAX_M=;
int n;
P p[MAX_N], q[MAX_N];
int m;
int a[MAX_M], b[MAX_M];
bool g[MAX_N][MAX_N]; int main()
{
while (~scanf("%d", &n) && n)
{
fill(g[], g[]+sizeof(bool)**, false);
for (int i=; i<n; i++)
{
scanf("%lf %lf %lf %lf", &p[i].x, &p[i].y, &q[i].x, &q[i].y);
}
for (int i=;;i++)
{
scanf("%d %d",&a[i], &b[i]);
if (a[i]== && b[i]==)
{
m=i;
break;
}
}
for (int i=; i<n; i++)
{
g[i][i]=true;
for (int j=; j<i; j++)
{
if ((p[i]-q[i]).det(p[j]-q[j])==)
{
g[i][j]=g[j][i]=on_seg(p[i], q[i], p[j])
|| on_seg(p[i], q[i], q[j])
|| on_seg(p[j], q[j], p[i])
|| on_seg(p[j], q[j], q[i]);
}
else
{
P r=intersection(p[i], q[i], p[j], q[j]);
g[i][j]=g[j][i]=on_seg(p[i], q[i], r) && on_seg(p[j], q[j], r);
}
}
}
for (int k=; k<n; k++)
for (int i=; i<n; i++)
for (int j=; j<n; j++)
{
g[i][j] |= g[i][k]&&g[k][j];
}
for (int i=; i<m; i++)
{
puts(g[a[i]-][b[i]-] ? "CONNECTED" : "NOT CONNECTED");
}
}
}
Jack Straws(POJ 1127)的更多相关文章
- Jack Straws POJ - 1127 (简单几何计算 + 并查集)
In the game of Jack Straws, a number of plastic or wooden "straws" are dumped on the table ...
- Jack Straws POJ - 1127 (几何计算)
Jack Straws Time Limit: 1000MS Memory Limit: 10000K Total Submissions: 5428 Accepted: 2461 Descr ...
- Jack Straws(poj 1127) 两直线是否相交模板
http://poj.org/problem?id=1127 Description In the game of Jack Straws, a number of plastic or wood ...
- poj 1127:Jack Straws(判断两线段相交 + 并查集)
Jack Straws Time Limit: 1000MS Memory Limit: 10000K Total Submissions: 2911 Accepted: 1322 Descr ...
- poj 1127 -- Jack Straws(计算几何判断两线段相交 + 并查集)
Jack Straws In the game of Jack Straws, a number of plastic or wooden "straws" are dumped ...
- poj1127 Jack Straws(线段相交+并查集)
转载请注明出处: http://www.cnblogs.com/fraud/ ——by fraud Jack Straws Time Limit: 1000MS Memory L ...
- 1840: Jack Straws
1840: Jack Straws 时间限制(普通/Java):1000MS/10000MS 内存限制:65536KByte 总提交: 168 测试通过:129 描述 I ...
- TZOJ 1840 Jack Straws(线段相交+并查集)
描述 In the game of Jack Straws, a number of plastic or wooden "straws" are dumped on the ta ...
- poj 1127(直线相交+并查集)
Jack Straws Description In the game of Jack Straws, a number of plastic or wooden "straws" ...
随机推荐
- Kafka2.6.0发布——性能大幅提升
近日Kafka2.6版本发布,距离2.5.0发布只过去了不到四个月的时间. Kafka 2.6.0包含许多重要的新功能.以下是一些重要更改的摘要: 默认情况下,已为Java 11或更高版本启用TLSv ...
- asp.netcore mvc 防CSRF攻击,原理介绍+代码演示+详细讲解
一.CSRF介绍 1.CSRF是什么? CSRF(Cross-site request forgery),中文名称:跨站请求伪造,也被称为:one click attack/session ridin ...
- css中关于:nth-child()和:nth-of-type()的深入理解
css中关于:nth-child()和:nth-of-type()的深入理解 在css中有这样一类属性,是以:nth-开头的,其中最常见的就是:nth-child() 和 :nth-of-type() ...
- 一个在交流群里讨论过两轮的问题,答案竟然跟一个 PEP 有关
Python 中有没有办法通过类方法找到其所属的类? 这个问题看起来不容易理解,我可以给出一个例子: class Test: @xxx def foo(self): pass 现在有一个类和一个类方法 ...
- gpio模拟i2c驱动
前段时间做项目,需要gpio模拟i2c通信,最后参考了一些资料,然后编写了一个程序.现在发出来,以免以后忘记,也为一些需要的朋友提供参考.不喜勿喷哈. /* 说明:该程序是基于atmel公司的sama ...
- 构造 IPv6 报文
#!/usr/bin/python from scapy.all import * a=IPv6(nh=58, src='fe80::214:f2ff:fe07:af0', dst='ff02::1' ...
- Spring Security认证流程分析--练气后期
写在前面 在前一篇文章中,我们介绍了如何配置spring security的自定义认证页面,以及前后端分离场景下如何获取spring security的CSRF Token.在这一篇文章中我们将来分析 ...
- Reinforcement learning in artificial and biological systems
郑重声明:原文参见标题,如有侵权,请联系作者,将会撤销发布! Abstract 在生物和人工系统的学习研究之间,已经有富有成果的概念和想法流.Bush and Mosteller,Rescorla a ...
- 《Head First 设计模式》:外观模式
正文 一.定义 外观模式提供了一个统一的接口,用来访问子系统中的一群接口.外观定义了一个高层接口,让子系统更容易使用. 要点: 外观模式将一个或数个类的复杂的一切都隐藏在背后,只显露出一个干净美好的外 ...
- JS事件——添加、移除事件
element.addEventListener(event, function, useCapture) 方法用于向指定元素添加事件句柄. event: 必须.字符串,指定事件名.注意: 例 使 ...
