Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires
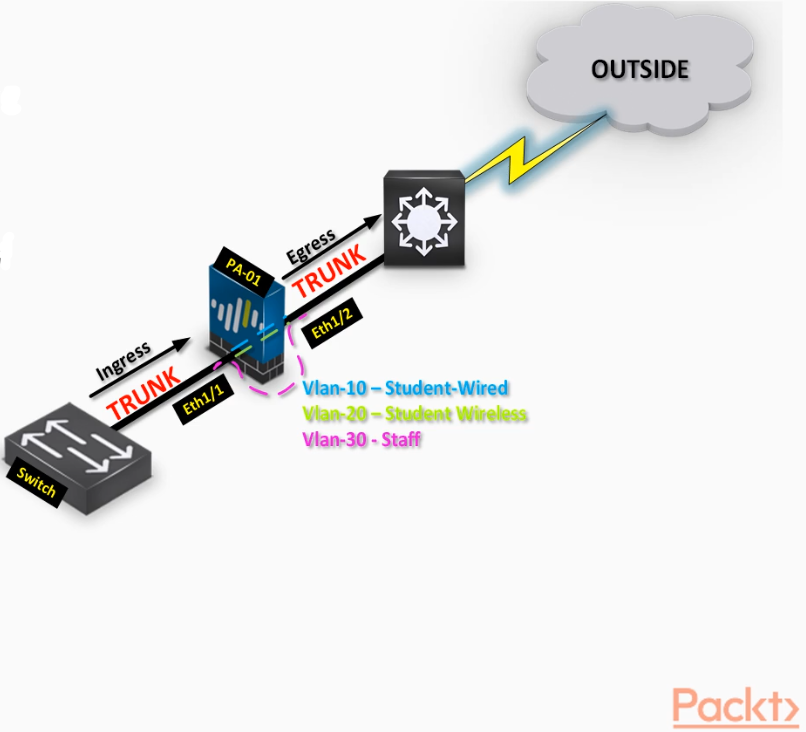
- Bridge two physical connections and apply security
- Policies without influencing any routing decision(transparent Firewall inspection)
- Inspect per VLAN traffic by creating V-Wire sub interfaces.
Interface configuration>>
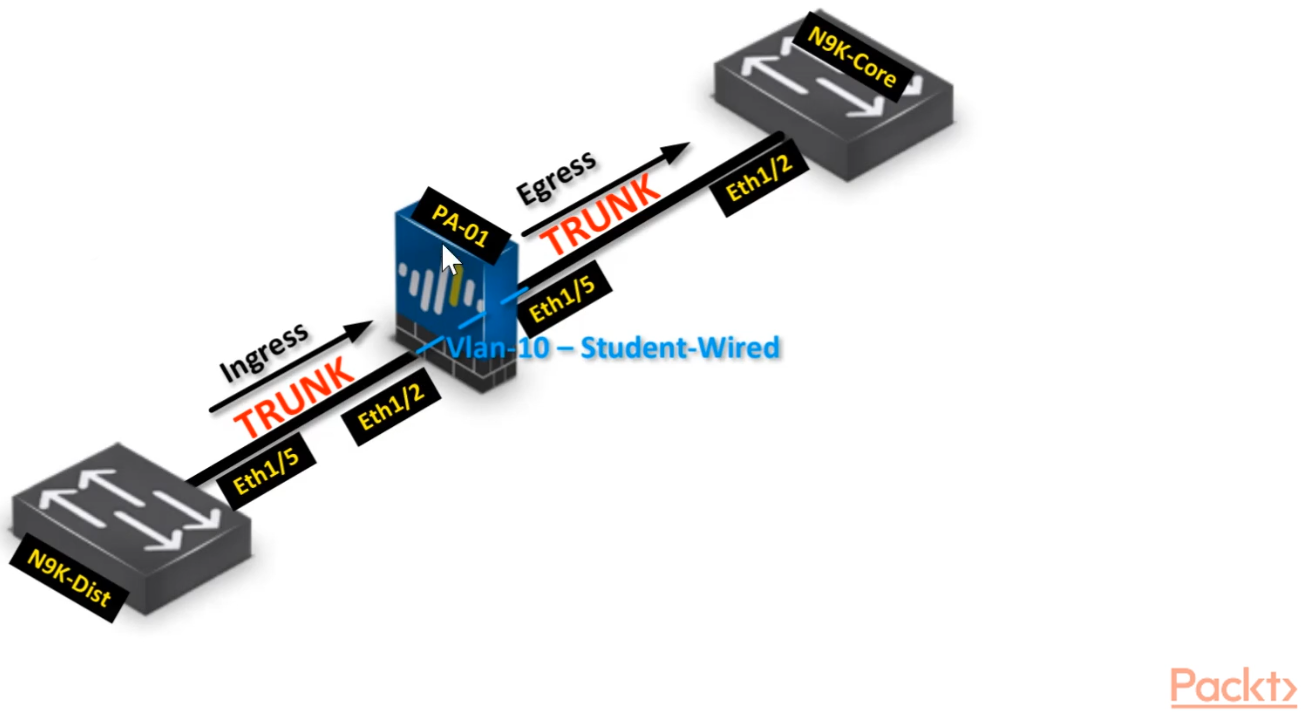
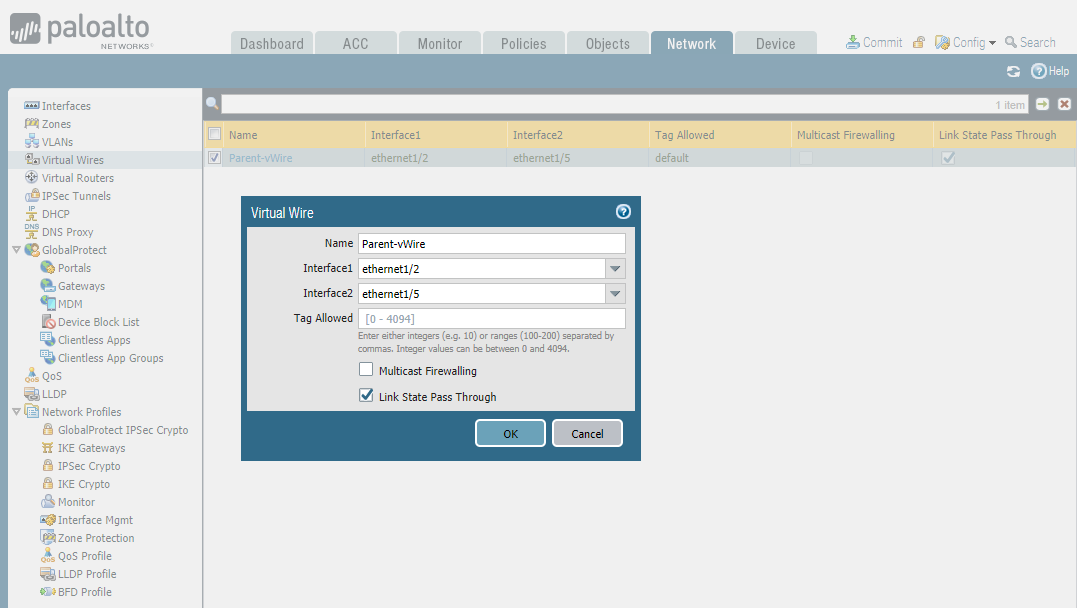
STEP1: Configure parent Virtual Wire interfaces - ethernet 1/2 and ethernet 1/5
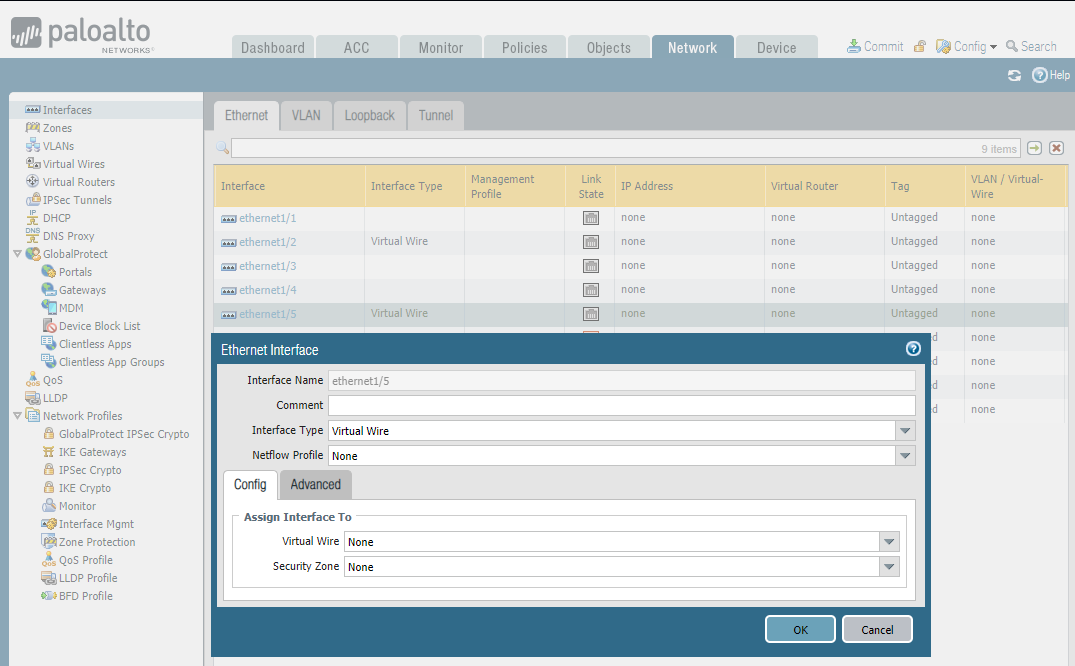
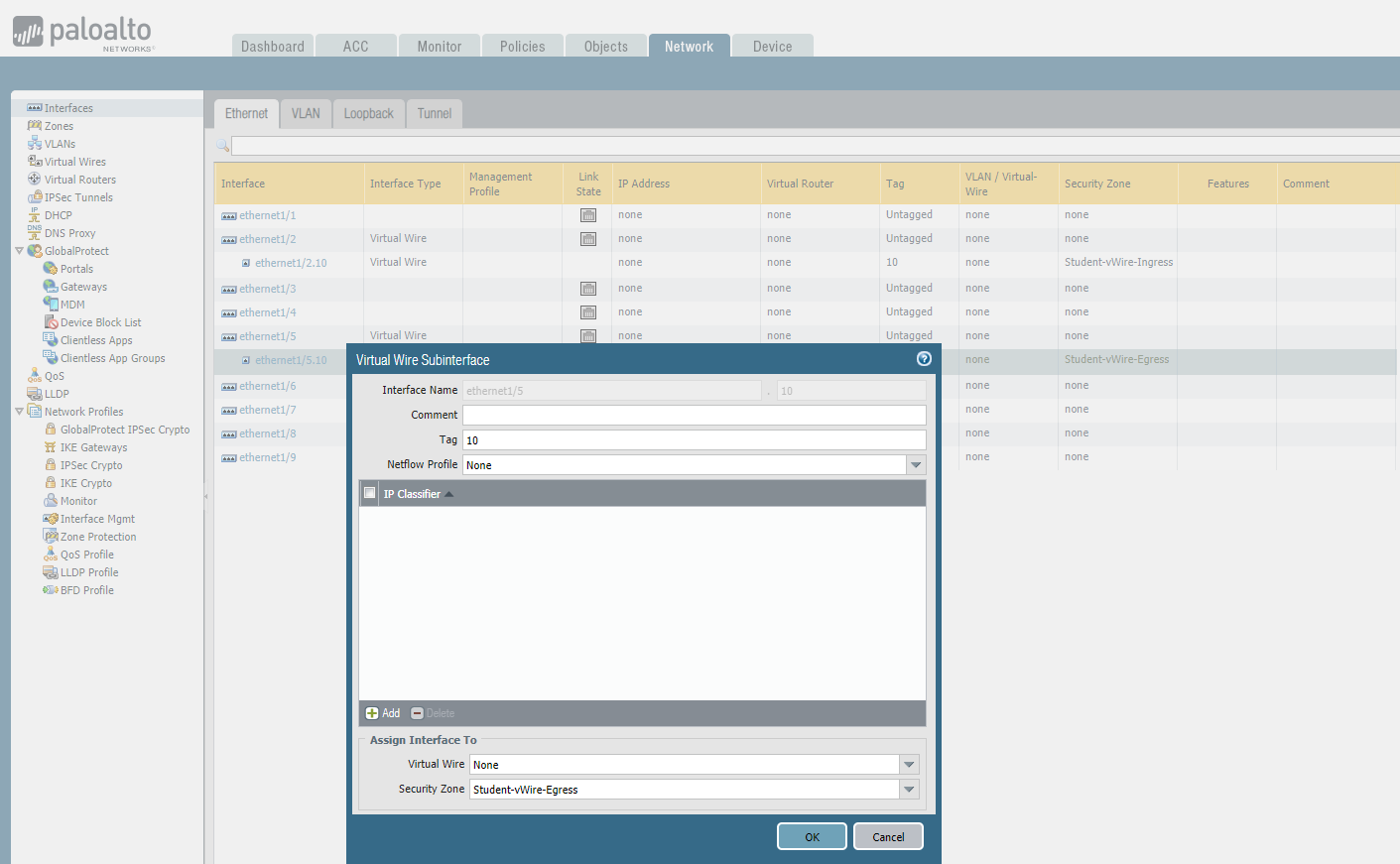
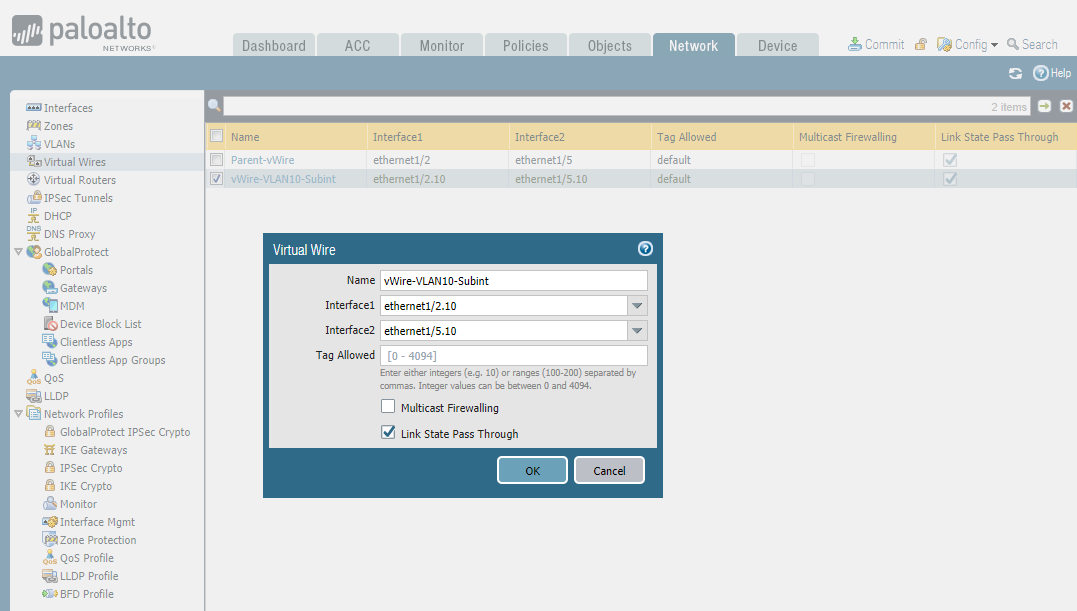
STEP2: Configure subinterface - ethernet1/2.10 and ethernet 1/5/10
STEP3: Connect virtual wires - Parent-vWire
STEP4: Connect virtual wires - Sub-vWire
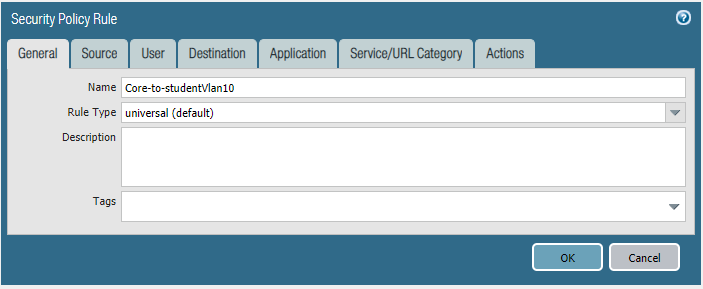
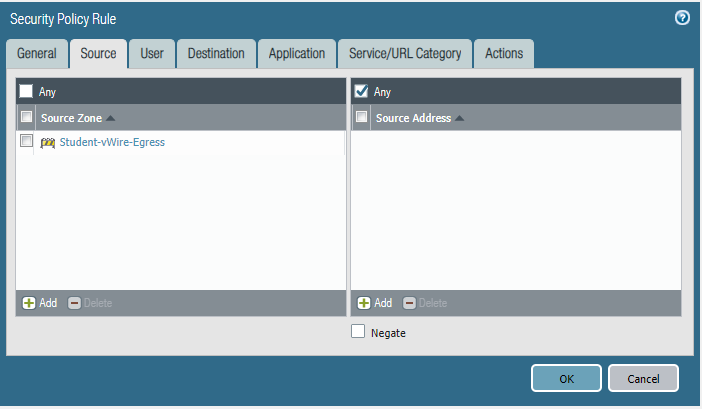
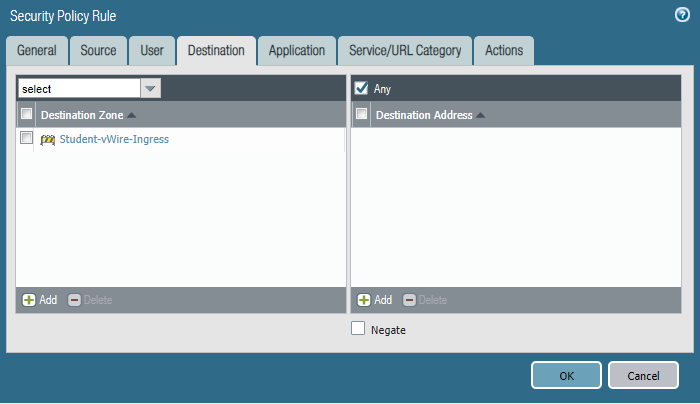
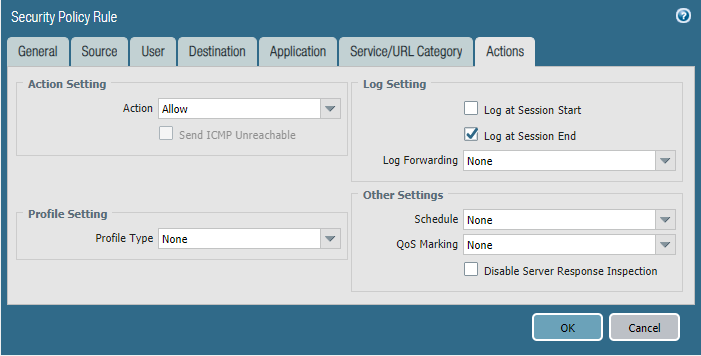
STEP5: Configure security policies.
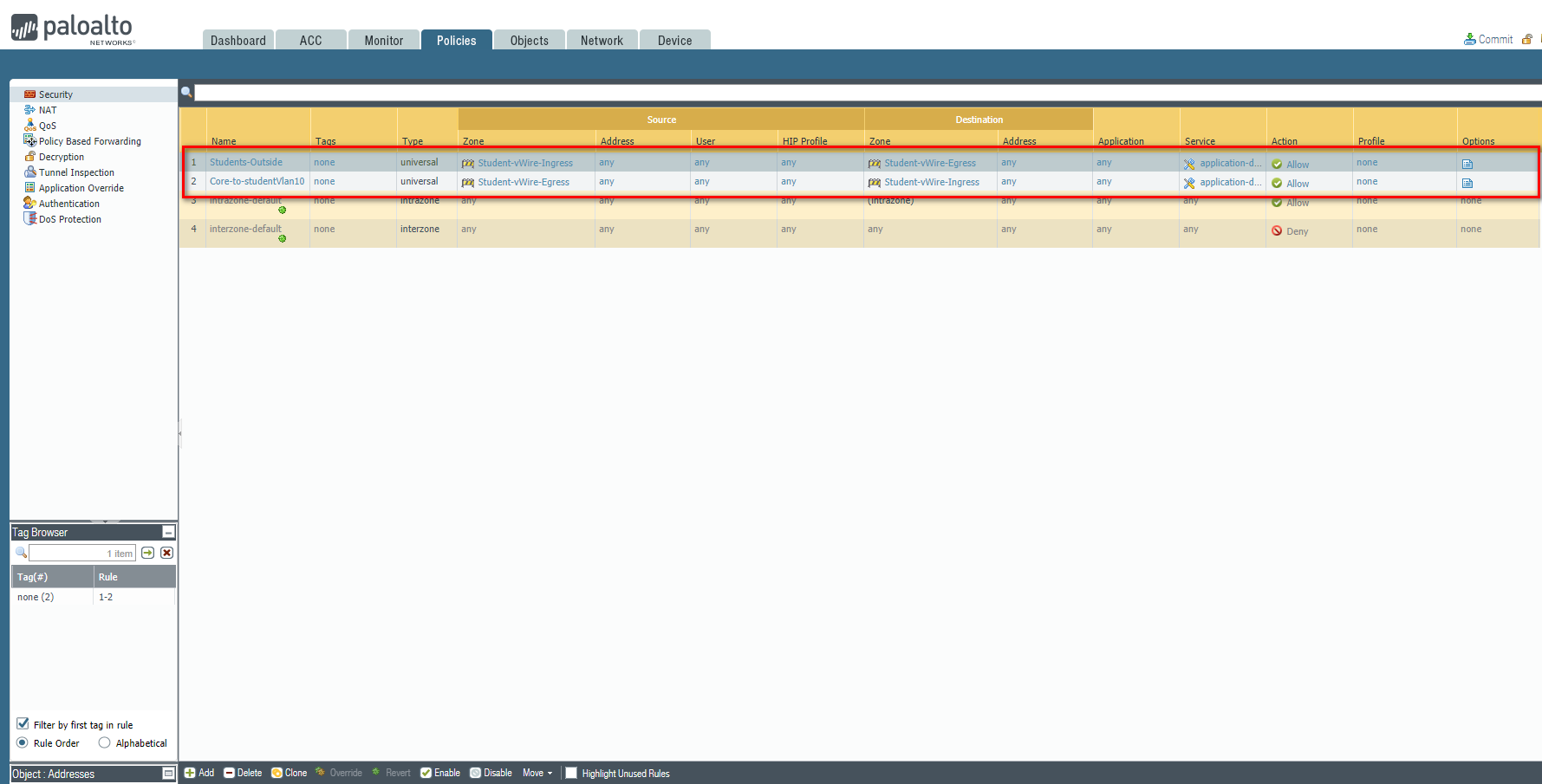
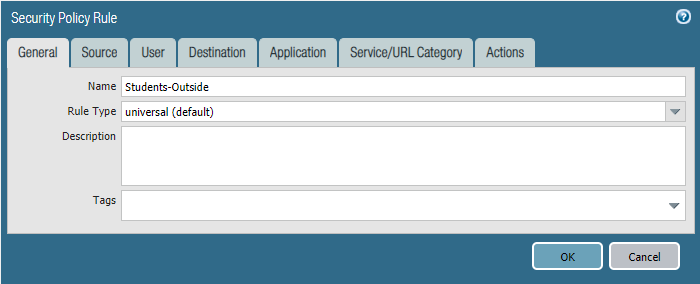
Students-Outside
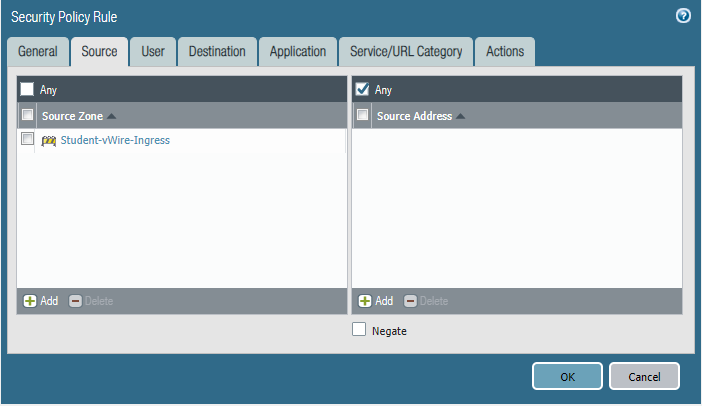
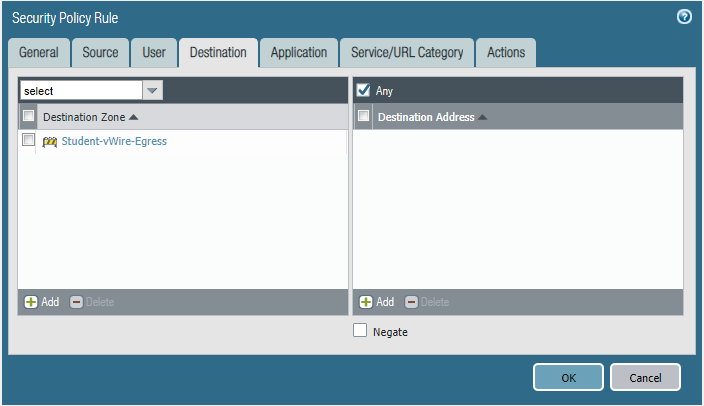
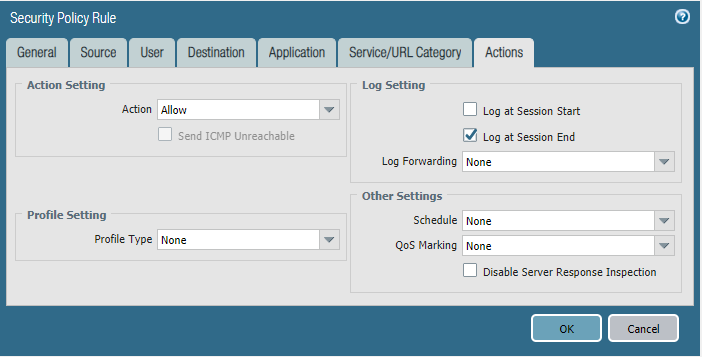
Core-to-studentVlan10
Commit the configuration and test.
Students-Outside
Cyber Security - Palo Alto Firewall V-Wires的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- Win10 1903小白搭建Redis
一.Redis介绍 Please Baidu. 二.安装 1)下载: 下载网址 https://github.com/microsoftarchive/redis/releases 选这个 2)安装 ...
- .NET进行客户端Web开发又一利器 - Ant Design Blazor
你好,我是Dotnet9,继上篇介绍Bootstrap风格的BlazorUI组件库后,今天我来介绍另一款Blazor UI组件库:一套基于 Ant Design 和 Blazor 的企业级组件库. 本 ...
- java并发编程-线程生命周期
线程生命周期 现代操作系统在运行一个程序时,会为其创建一个进程.例如,启动一个Java程序,操作系统就会创建一个Java进程.现代操作系统调度的最小单元是线程,也叫轻量级进程(Light Weight ...
- SpringBoot中注入ApplicationContext对象的三种方式
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 在项目中,我们可 ...
- 在 Spring Boot 中使用 HikariCP 连接池
上次帮小王解决了如何在 Spring Boot 中使用 JDBC 连接 MySQL 后,我就一直在等,等他问我第三个问题,比如说如何在 Spring Boot 中使用 HikariCP 连接池.但我等 ...
- vue全家桶(3.1)
4.数据请求 4.1.axios是什么? axios 是一个基于Promise 用于浏览器和 nodejs 的 HTTP 客户端,它有以下特征: 从浏览器中创建 XMLHttpRequest 从 no ...
- Python之浅谈基础
执行python的两种方式 交互式(jupyter) 通过cmd或jupyter运行python代码 优点:运行一句执行一句 缺点:关闭cmd或jupyter后数据消失 命令行式(pycharm) 优 ...
- Mybatis 动态insert语句
mybatis的一个比较先进的思想是把Sql语句写在了配置xml文件(也支持注解),通过配置文件的方式,免去了一般软件开发的硬编码,当业务需求改变的时候,只需要更改sql语句即可! 下面是个人在学习m ...
- elasticsearch7.6 安装 并且开启外网访问,真的好累。
下载 下载页面 https://www.elastic.co/cn/downloads/elasticsearch wget https://artifacts.elastic.co/download ...
- 编辑器之神_vim
01vim简介 1.什么是vim: 文本编辑器 2.vim特点: 没有图形界面;只能是编辑文本内容;没有菜单 ;只有命令 3.在很多linux发行版中,直接把vi作为vim的软连接 02打开和新建文件 ...
