Ethical Hacking - GAINING ACCESS(9)
Server Side Attack
Nexpose - Analysing Scan Results and Generating Reports
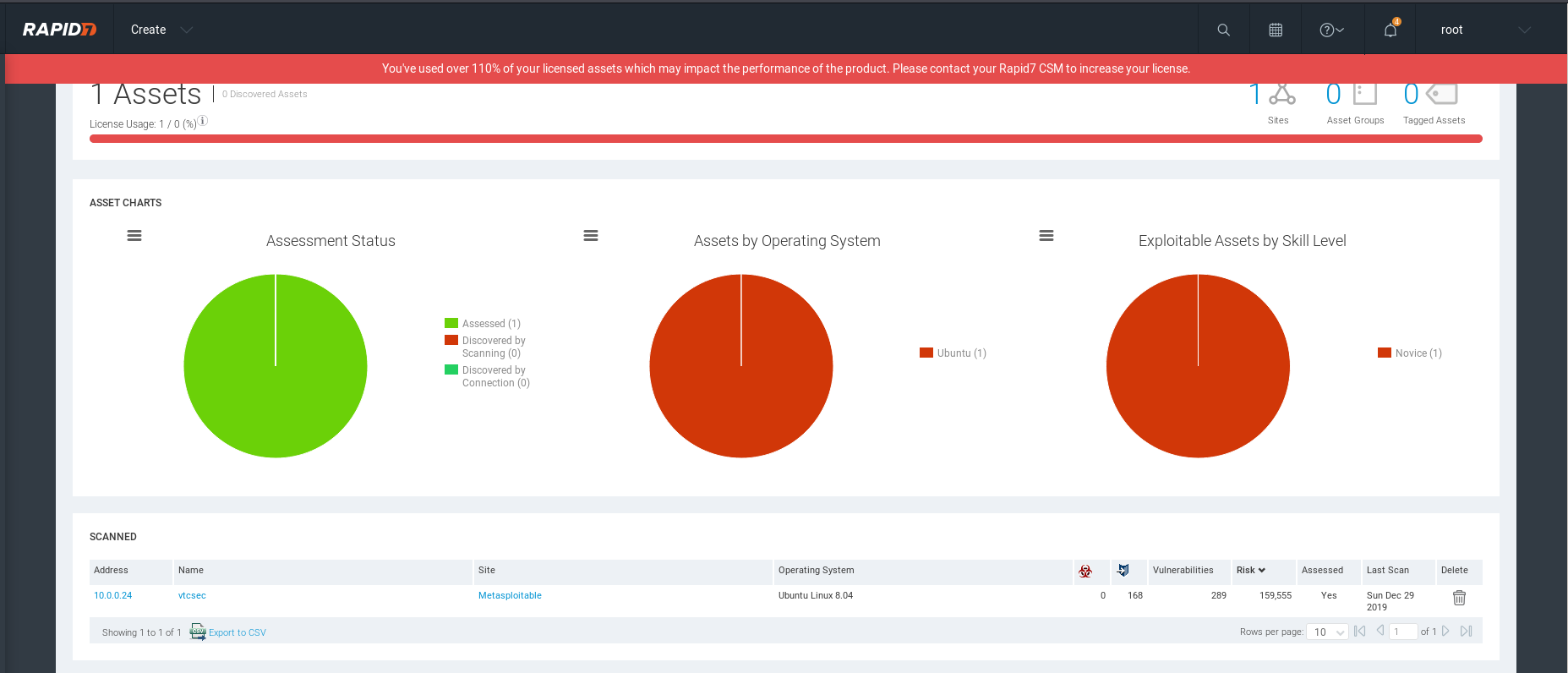
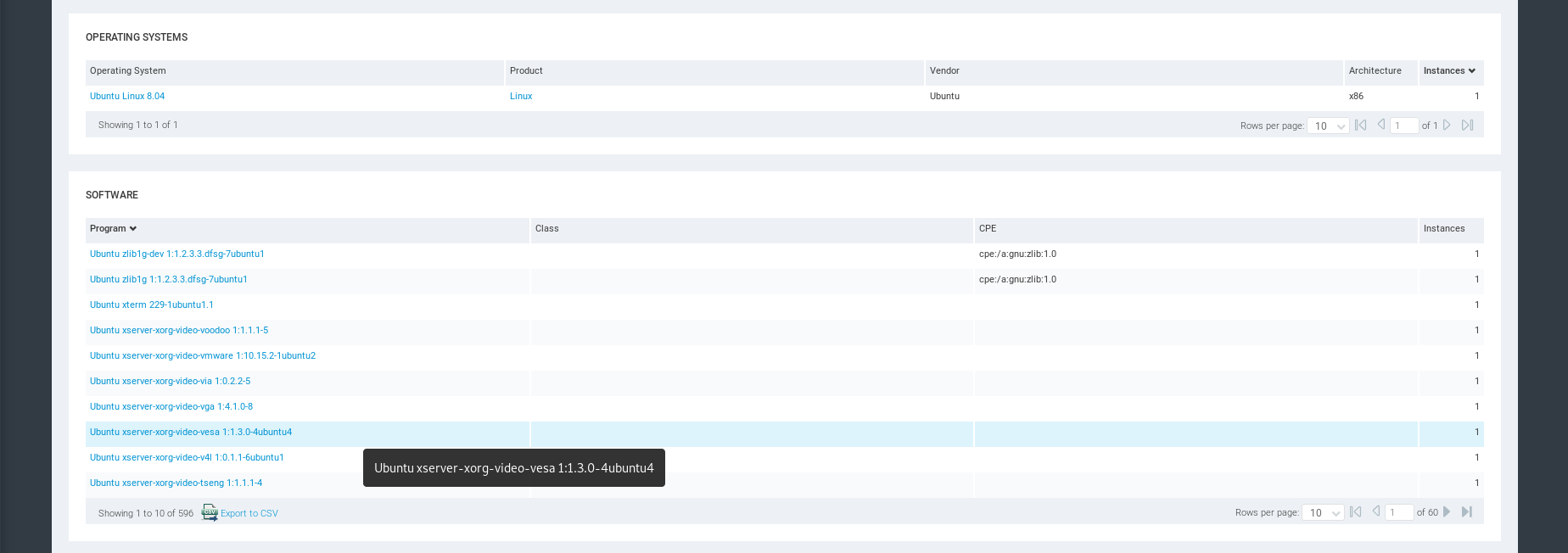
OS and Software Inforation.
Services Information
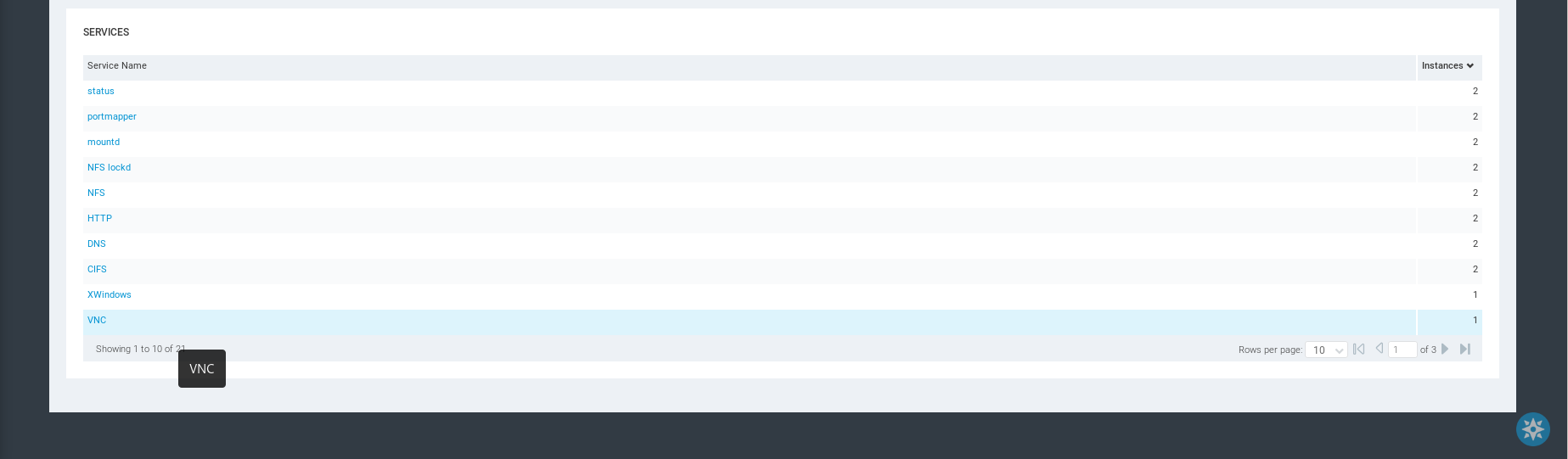
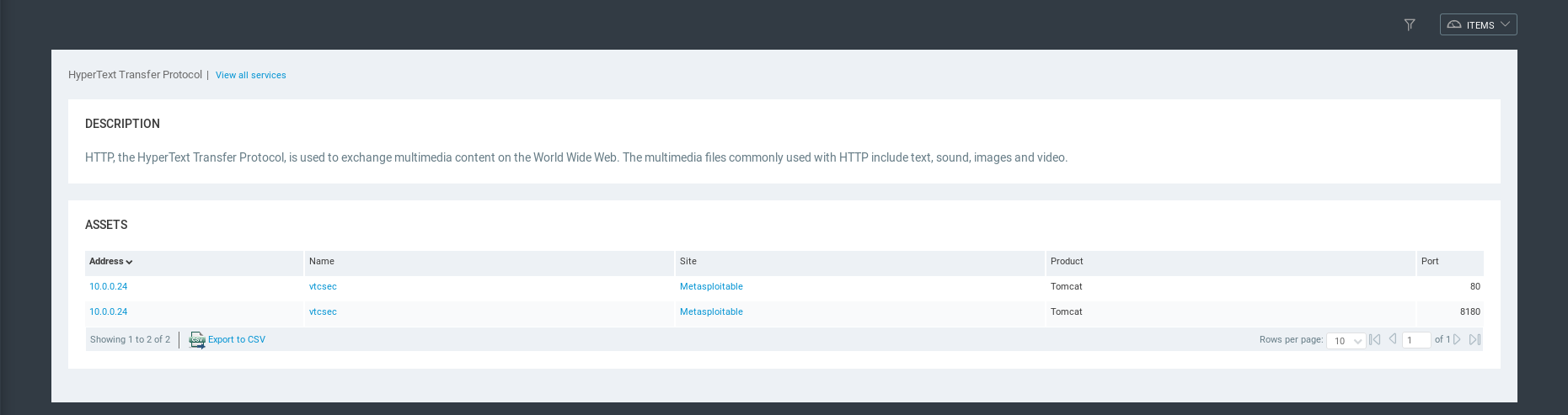
HTTP Service Detailed Information.
Vulnerability Information
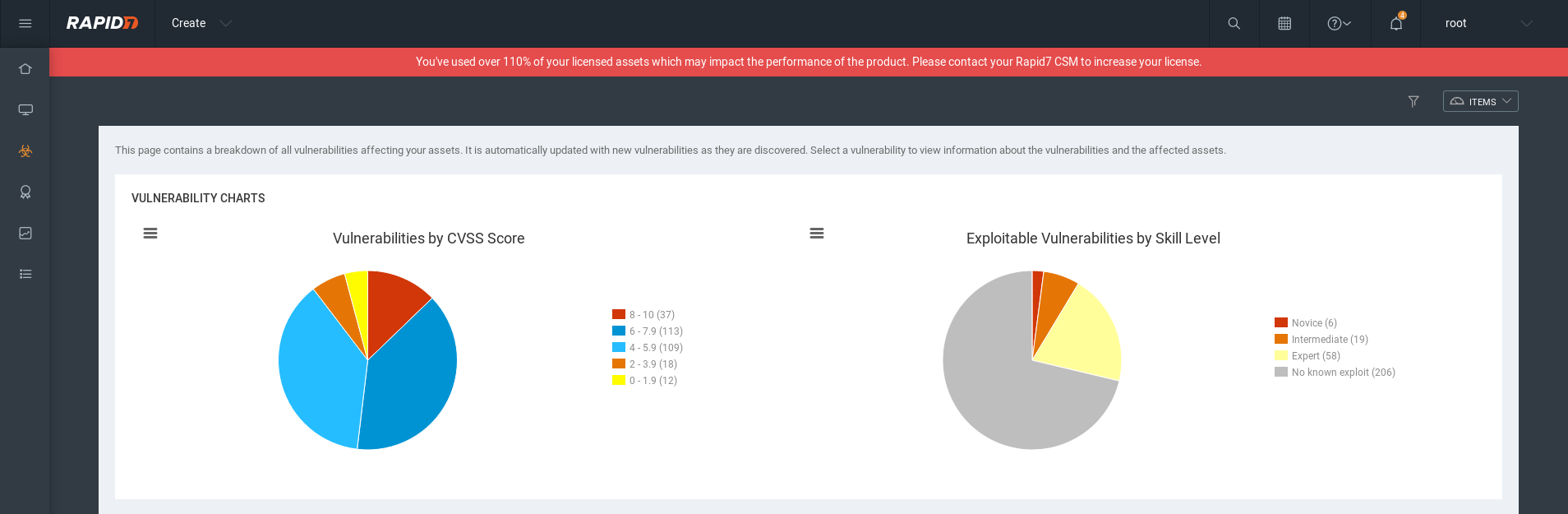
Vulnerabilities list:
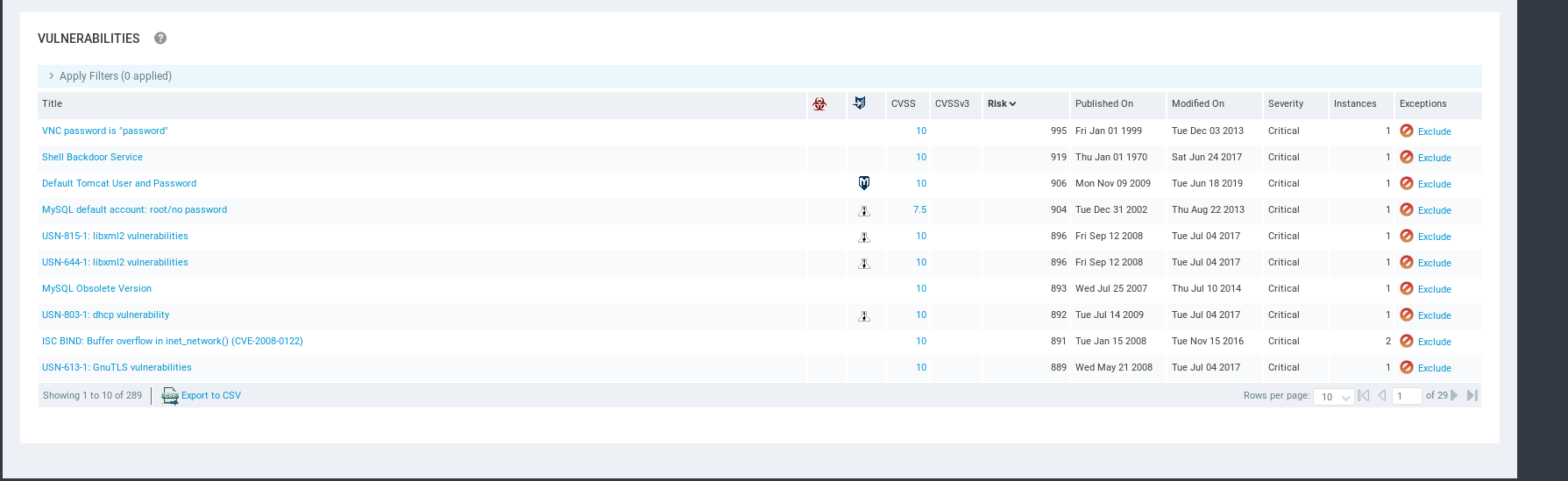
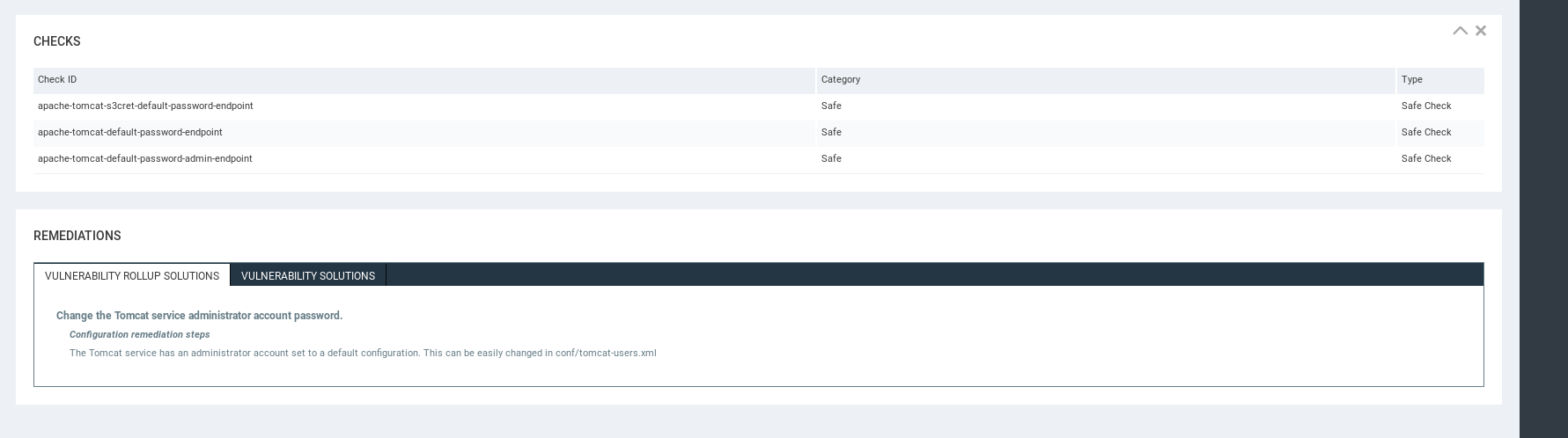
Detailed Vulnerability Information - Affects
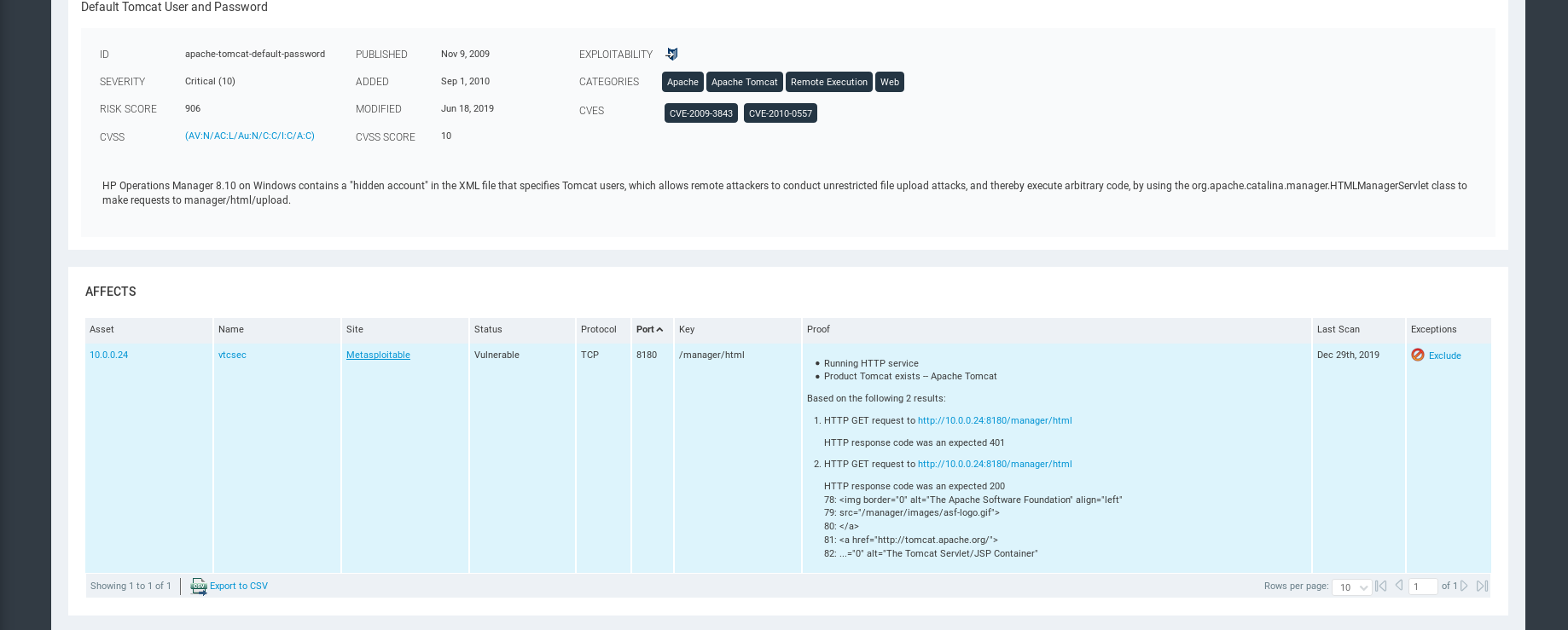
Exploits can be used in Metasploit.
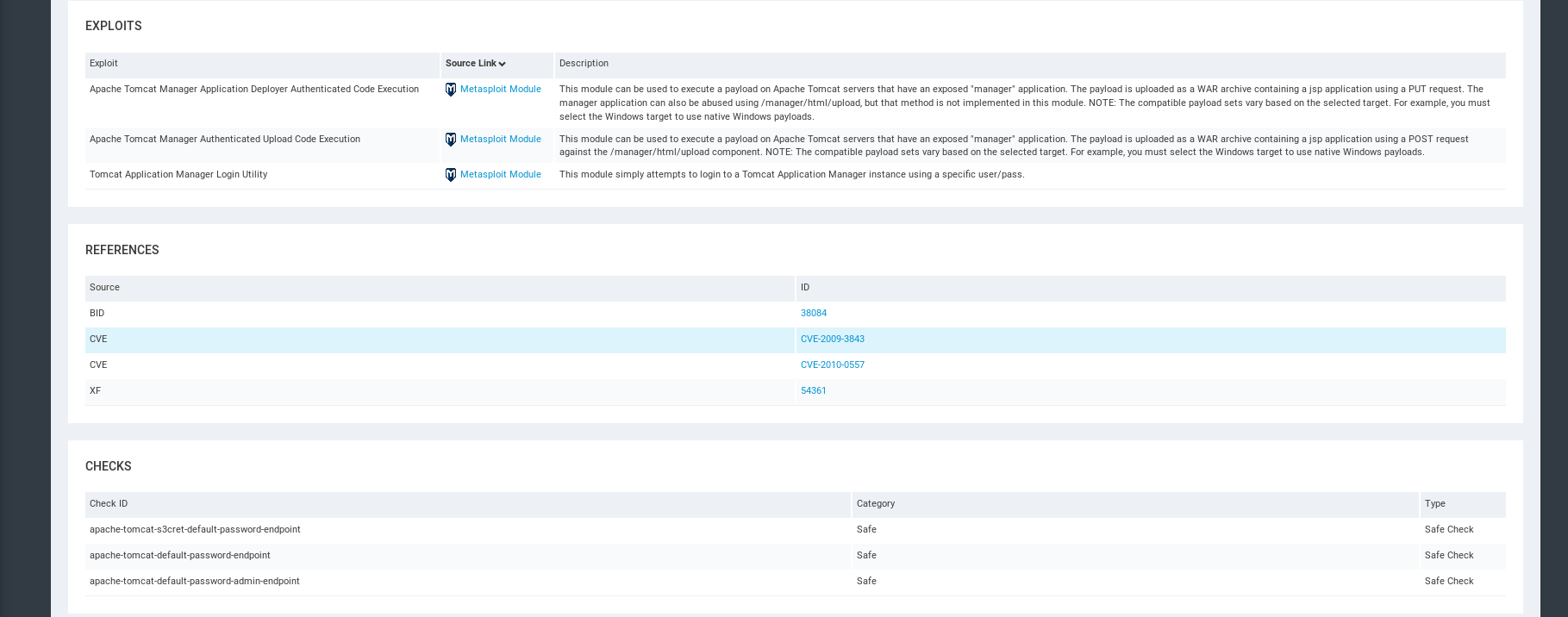
Remediations.
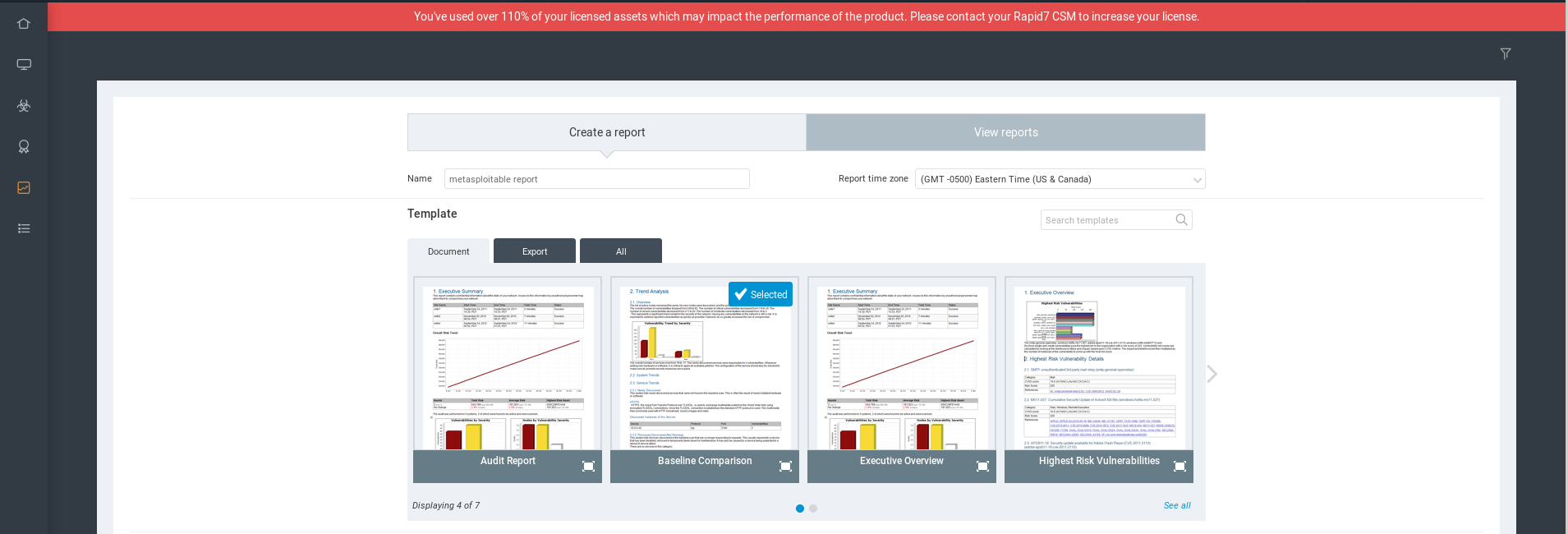
Report
Select the template first.
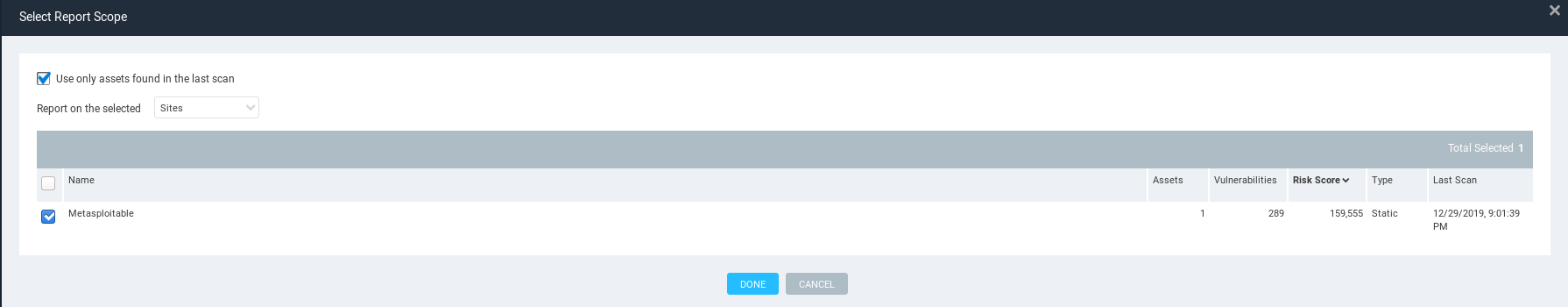
Select Report Scope
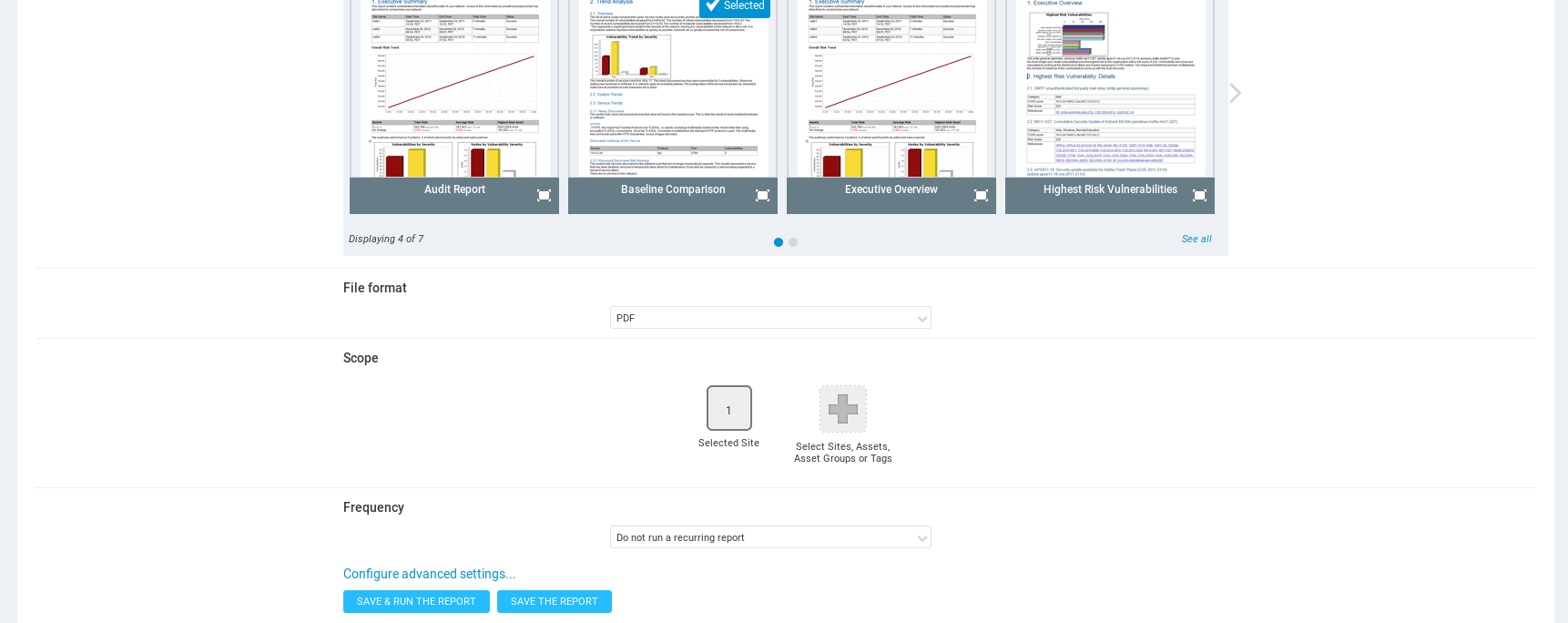
Save and run the report.
View the report result.
Ethical Hacking - GAINING ACCESS(9)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
- Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS Backdooring ANY file Combine backdoor with any file - Generic solution. Users ar ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
随机推荐
- post请求头的常见类型
1.application/json(JSON数据格式) xhr.setRequestHeader("Content-type","application/json; c ...
- winxp系统连接服务器丢包解决方法
winxp系统连接服务器丢包解决方法 MFC编写一个打开网页的程序,发生异常没有获取到数据. 分析步骤: 1. 用getLastError()获取到的信息,(2)- 系统找不到指定的文件. 2. 用浏 ...
- program files (x86)\microsoft visual studio 14.0\vc\include\xtree,如果没有找到,下标溢出了,就报错咯
---------------------------Microsoft Visual C++ Runtime Library---------------------------Debug Asse ...
- Redis删除策略和逐出策略
本文知识点 过期数据概念 数据删除策略 逐出算法 过期数据 先来看三个key值,分别为sex.name.age. 这三个值设置的指令为 set name kaka setex age 100 24 s ...
- Beta冲刺<2/10>
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 这个作业要求在哪里 Beta冲刺 这个作业的目标 Beta冲刺--第二天(05.20) 作业正文 如下 其他参考文献 ... B ...
- Java并发编程的本质是解决这三大问题
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 前言 并发编程的 ...
- C# MVC LayUI实现下拉框二级联动
一.layui.use 1.LayUI的官方使用文档:https://www.layui.com/doc/ 2.layui的内置模块不是默认就加载好的,必须要执行启动模块的这种方法后模块才会加载: 3 ...
- 04[掌握] Java连接redis操作
1,Jedis所需要的jar包依赖 <dependency> <groupId>redis.clients</groupId> <artifactId> ...
- Jquery的一些方法
$.trim(str);说明:去掉字符串首尾空格.
- Java 从入门到进阶之路(二十六)
在之前的文章我们介绍了一下 Java 中的 集合框架中的Collection 的子接口 List,本章我们来看一下 Java 集合框架中的Collection 的子接口 Queue. 在之前我们讲 ...
