SPRING IN ACTION 第4版笔记-第九章Securing web applications-009-拦截请求()
一、
对特定的请求拦截
For example, consider the requests served by the Spittr application. Certainly, the
home page is public and doesn’t need to be secured. Likewise, since all Spittle
objects are essentially public, the pages that display Spittle s don’t require security.
Requests that create a Spittle , however, should only be performed by an authenti-
cated user. Similarly, although user profile pages are public and don’t require authen-
tication, if you were to handle a request for /spitters/me to display the current user’s
profile, then authentication is required to know whose profile to show.
The key to fine-tuning security for each request is to override the configure
(HttpSecurity) method. The following code snippet shows how you might override
configure(HttpSecurity) to selectively apply security to different URL paths.
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.authorizeRequests()
.antMatchers("/spitters/me").authenticated()
.antMatchers(HttpMethod.POST, "/spittles").authenticated()
.anyRequest().permitAll();
}
The HttpSecurity object given to configure() can be used to configure several
aspects of HTTP security. Here you’re calling authorizeRequests() and then calling
methods on the object it returns to indicate that you want to configure request-level
security details. The first call to antMatchers() specifies that requests whose path is
/spitters/me should be authenticated. The second call to antMatchers() is even
more specific, saying that any HTTP POST request to /spittles must be authenticated.
Finally, a call to anyRequests() says that all other requests should be permitted, not
requiring authentication or any authorities.
(1)用通配符
.antMatchers("/spitters/**").authenticated();
(2)写多个路径
.antMatchers("/spitters/**", "/spittles/mine").authenticated();
(3)Whereas the antMatchers() method works with paths that may contain Ant-style wild-
cards, there’s also a regexMatchers() method that accepts regular expressions to
define request paths. For example, the following snippet uses a regular expression
that’s equivalent to /spitters/** (Ant-style):
.regexMatchers("/spitters/.*").authenticated();
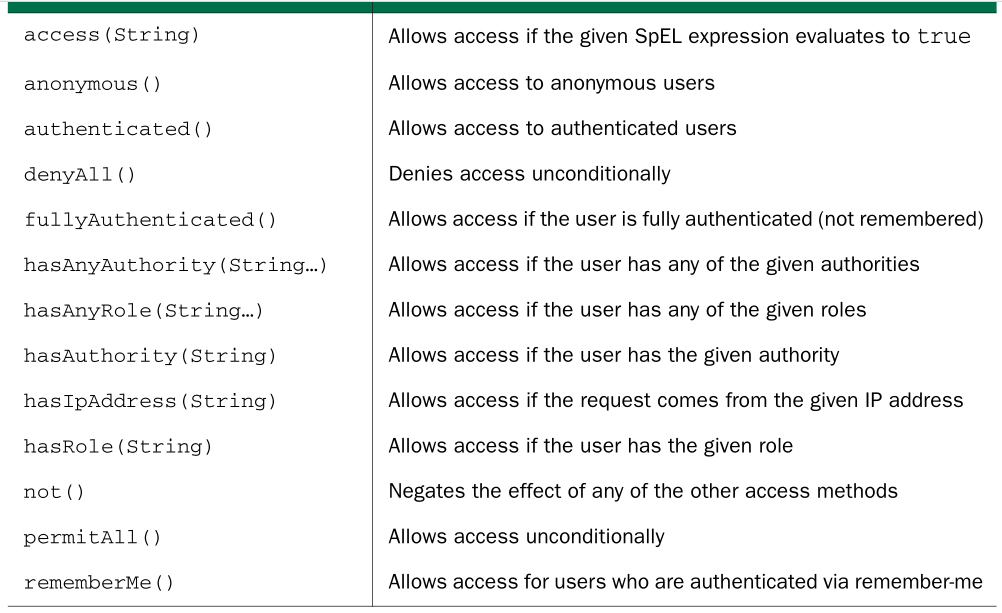
(4)全部可配置的方法
(1)you could change the previous configure() method to require that the user not only be authenticated, but also have ROLE_SPITTER authority:
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.authorizeRequests()
.antMatchers("/spitters/me").hasAuthority("ROLE_SPITTER")
.antMatchers(HttpMethod.POST, "/spittles")
.hasAuthority("ROLE_SPITTER")
.anyRequest().permitAll();
}
或
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.authorizeRequests()
.antMatchers("/spitter/me").hasRole("SPITTER")
.antMatchers(HttpMethod.POST, "/spittles").hasRole("SPITTER")
.anyRequest().permitAll();
}
You can chain as many calls to antMatchers() , regexMatchers() , and anyRequest()
as you need to fully establish the security rules around your web application. You
should know, however, that they’ll be applied in the order given. For that reason, it’s
important to configure the most specific request path patterns first and the least spe-
cific ones (such as anyRequest() ) last. If not, then the least specific paths will trump
the more specific ones.
SPRING IN ACTION 第4版笔记-第九章Securing web applications-009-拦截请求()的更多相关文章
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-011-把敏感信息请求转为https(requiresChannel())
1.把包含敏感信息的请求转为https请求,则较为安全,但如何只把有需要安全的请求转为https,而不是不加分辩就把所有请求都转为https呢?可以用requiresChannel() @Overri ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-001-SpringSecurity简介(DelegatingFilterProxy、AbstractSecurityWebApplicationInitializer、WebSecurityConfigurerAdapter、@EnableWebSecurity、@EnableWebMvcS)
一.SpringSecurity的模块 At the least, you’ll want to include the Core and Configuration modules in your ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-010-拦截请求
一. What if you wanted to restrict access to certain roles only on Tuesday? Using the access() method ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-008-使用非关系型数据库时如何验证用户(自定义UserService)
一. 1.定义接口 Suppose that you need to authenticate against users in a non-relational database suchas Mo ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-007-设置LDAP server比较密码(contextSource、root()、ldif()、)
一.LDAP server在哪 By default, Spring Security’s LDAP authentication assumes that the LDAP server is li ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-004-对密码加密passwordEncoder
一. 1.Focusing on the authentication query, you can see that user passwords are expected to be stored ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-003-把用户数据存在数据库
一. 1.It’s quite common for user data to be stored in a relational database, accessed via JDBC . To c ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-002-把用户数据存在memory里(AuthenticationManagerBuilder、 UserDetailsManagerConfigurer.UserDetailsBuilder)
Spring Security is extremely flexible and is capable of authenticating users against virtually any d ...
- SPRING IN ACTION 第4版笔记-第九章Securing web applications-006-用LDAP比较密码(passwordCompare()、passwordAttribute("passcode")、passwordEncoder(new Md5PasswordEncoder()))
一. The default strategy for authenticating against LDAP is to perform a bind operation,authenticatin ...
随机推荐
- 应注意的Flex&Bison潜规则
1.Flex的二义性模式 语法分析器匹配输入时匹配尽可能多的字符串 如果两个模式都可以匹配的话,匹配在程序中更早出的模式. 针对这一点的理解,在语法分析文件当中,token的识别,应从特殊到一般的过程 ...
- C语言中格式化输出的转换说明的fldwidth和precision解析
首先说什么是C语言的格式化输出,就是printf和它的几个变种(grep -E "v?(sn|s|f)printf").像这些函数都有一个参数format,format中可以加点转 ...
- 删除vim-minimal导致sudo不可用
Ok, if anyone ends up in a similar situation, you can use pkexec yum install sudo. pkexec will let y ...
- Linux C 程序 字符串函数(12)
字符串函数C语言的字符串处理函数1.puts函数 //把一个以'\0'结尾的字符串输出到屏幕 char a[] = "Welcome to"; char *p = "Li ...
- 进度条轮播【BackgroundColor】
直接贴代码先看 HTML: <div class="bannar"> <div class="img"> <ul> < ...
- 页面有什么隐藏bug:字体,图片
字体: 一行(太长)-display:inline-block,text-overflow: ellipsis;max-width:xxpx 多行(太高,太矮)-设置max-height,min-he ...
- javascript的setTimeout以及setInterval休眠问题。
前端码农们在做项目中时候,必定不可少的需要做到轮播效果.但是有些特殊的需求,比如: 需要做到第一个容器内容轮播滚动之后,第二个容器内部再轮播滚动,再第三个容器内容轮播滚动. 这时候我的一开始的思路是: ...
- background之你不知道的background-position
这是一个有趣的话题 其实我并不确切的平时大家是怎么去应用或者玩转一个属性,一个值.我能肯定的是这些东西都有不少的可玩性. 我今天要聊的 background-position 应该已经被大家玩得色彩斑 ...
- 1048. Find Coins (25)
时间限制 50 ms 内存限制 65536 kB 代码长度限制 16000 B 判题程序 Standard 作者 CHEN, Yue Eva loves to collect coins from a ...
- Qt 内存管理机制(转)
许转载http://devbean.blog.51cto.com/448512/526734 强类型语言在创建对象时总会显式或隐式地包含对象的类型信息.也就是说,强类型语言在分配对象内存空间时,总 ...
