Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX
- For best results package the program from the same OS as the target.
- EG if the target is Windows then package the program from a Windows computer with a python interpreter.
- Install Windows python interpreter on Linux.
- Use it to convert python programs to Windows executables.
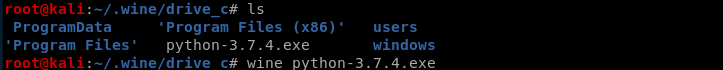
Install wine tool on Kali Linux:
dpkg --add-architecture i386 && apt-get update &&
apt-get install wine32
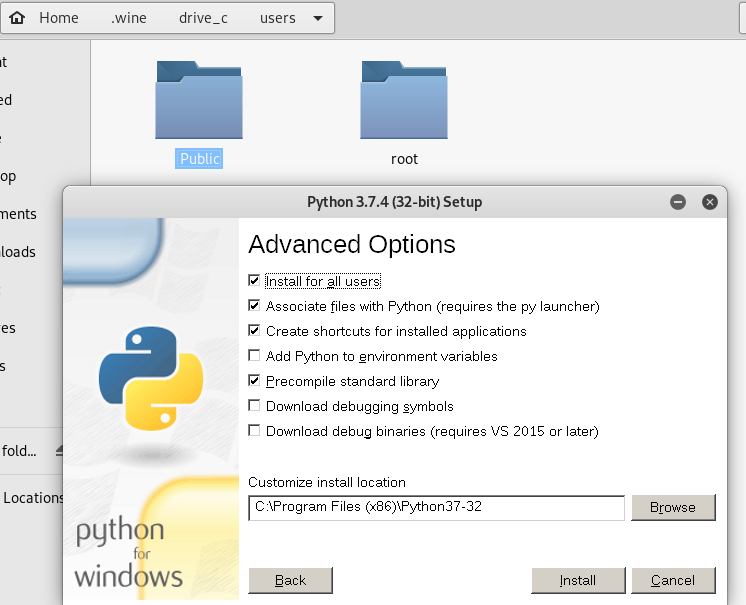
Install Python 3.7.4 using wine.
Install PyInstaller on Kali Linux.
wine python.exe -m pip install /root/Downloads/PyInstaller-3.5.tar.gz

To package the keylogger program, we need to install the pynput module first.
wine python.exe -m pip --default-time= install pynput
Convert the python program to windows executable.
wine ~/.wine/drive_c/'Program Files (x86)'/Python37-/Scripts/pyinstaller.exe zkeylogger.py --onefile --noconsole


Test the zkeylogger.exe file on the Windows 10 PC. It works perfectly.

Python Ethical Hacking - Malware Packaging(2)的更多相关文章
- Python Ethical Hacking - Malware Packaging(1)
PACKAGING Convert python program into an executable that: Packages all program files into a single e ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- cb51a_c++_STL_算法_根据第n个元素排序nth_element
cb51a_c++_STL_算法_根据第n个元素排序nth_elementnth_element(b,n,e),比如最大的5个数排序,或者最小的几个数nth_element(b,n,e,p)对比:pa ...
- 08.DRF-反序列化
三.反序列化使用 3.1 验证 使用序列化器进行反序列化时,需要对数据进行验证后,才能获取验证成功的数据或保存成模型类对象. 在获取反序列化的数据前,必须调用is_valid()方法进行验证,验证成功 ...
- C/C++以及Linux文件操作备忘录
目录 C文件操作 文件开关 文件读写 C++文件操作 Linux文件操作 打开 C文件操作 #include<stdio.h> stdin, stdout, stderr 文件开关 /* ...
- drf之序列化组件(一):Serializer
序列化组件:Serializer.ModelSerializer.ListModelSerializer Serializer 偏底层 ModelSerializer 重点 List ...
- vipkid 面试经历
今天下午去了位于钟鼓楼旁边的 vipkid 研发部进行了面试,面试过程中的回答只能说一般,面试官问的问题大概分为: 实际项目的设计问题 mysql的使用优化问题 多线程与锁的问题 JVM底层原理的问题 ...
- Vmware虚拟机克隆以及关闭防火墙
vmware虚拟机克隆之后,一定要修改克隆机器的mac地址和IP上网地址,不能和之前的机器一样
- DNS信息收集-NSLOOKUP
上一篇文章简单介绍了nslookup的简单用法,这篇文章进一步介绍nslookup. nslookup可以指定DNS服务器,使用server参数: 可以看到,采用不同的DNS服务器的到的结果是不一样的 ...
- 同步/异步/阻塞/非阻塞/BIO/NIO/AIO各种情况介绍
常规的误区 假设有一个展示用户详情的需求,分两步,先调用一个HTTP接口拿到详情数据,然后使用适合的视图展示详情数据. 如果网速很慢,代码发起一个HTTP请求后,就卡住不动了,直到十几秒后才拿到HTT ...
- IntelliJ IDEA 2018.3.6 安装、激活 JRebel
在 IntelliJ IDEA 2018.3.6 中安装## JRebel 1.代开 IDEA 开发工具,然后用快捷键 Ctrl+Alt+S 打开设置并搜索 jrebel 插件 2.安装 jrebel ...
- MongoDB入门二
MongoDB配置 本地启动 c:\MongoDB\bin>mongod.exe --dbpath "C:\\MongoDB\data\db" --logpath " ...
