Ethical Hacking - GAINING ACCESS(8)
Server Side Attacks
NeXpose - configure and launch a scan
Configure and initialize the application.
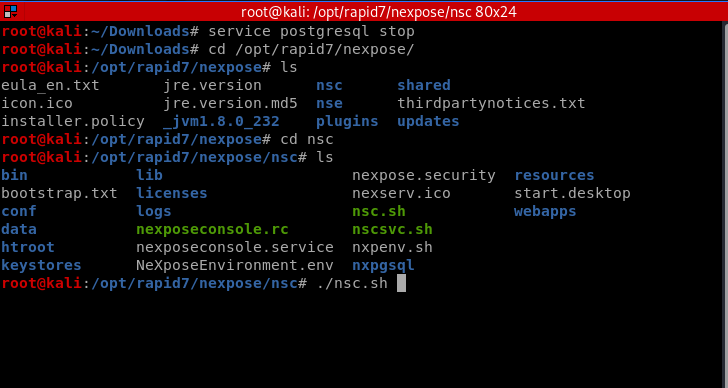
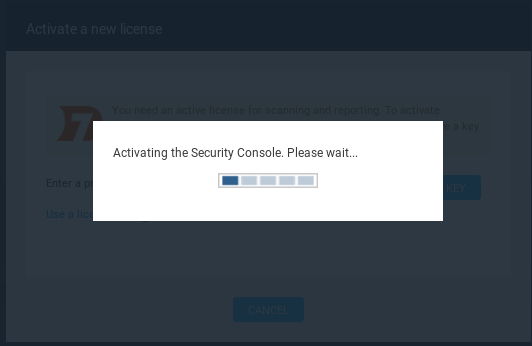
Browse https://localhost:3780 and active the system.

Create site and configure the settings.
Info&security

Assets: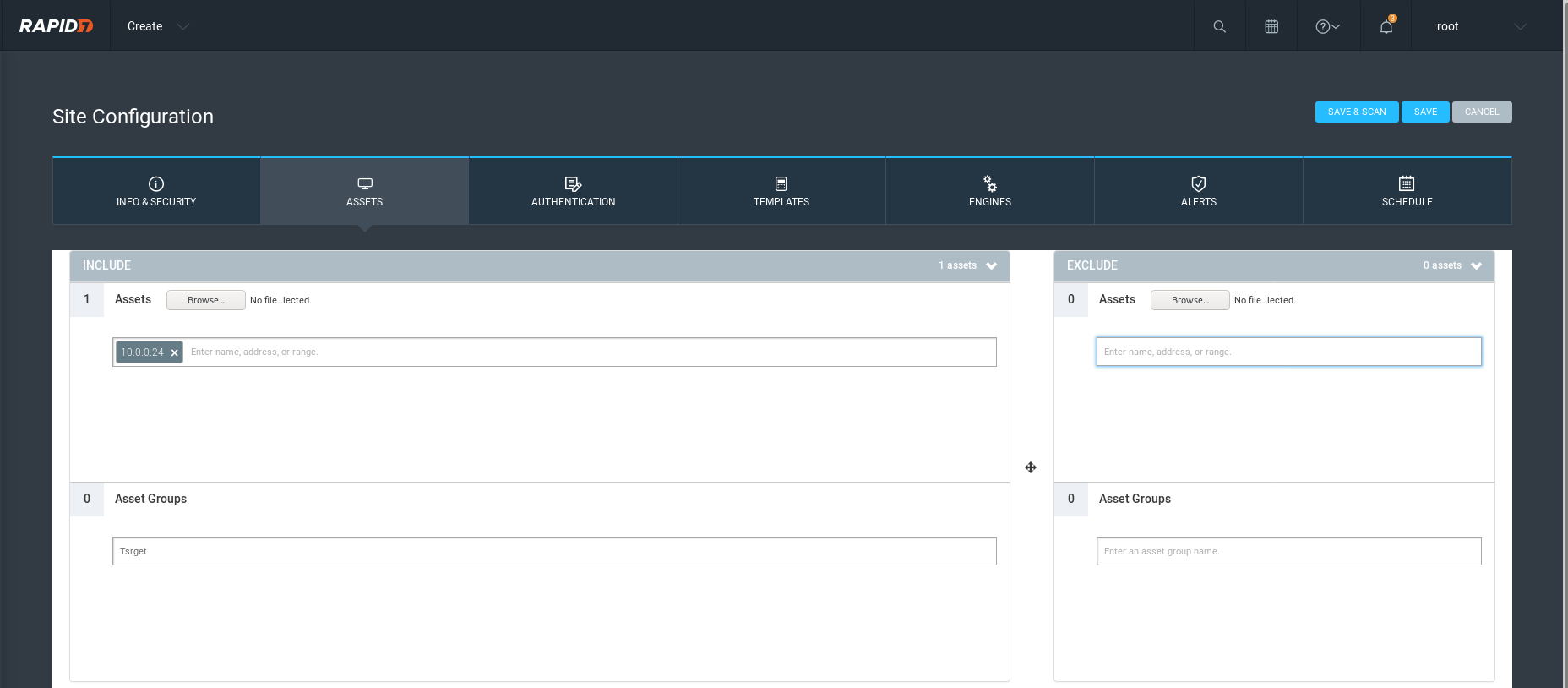
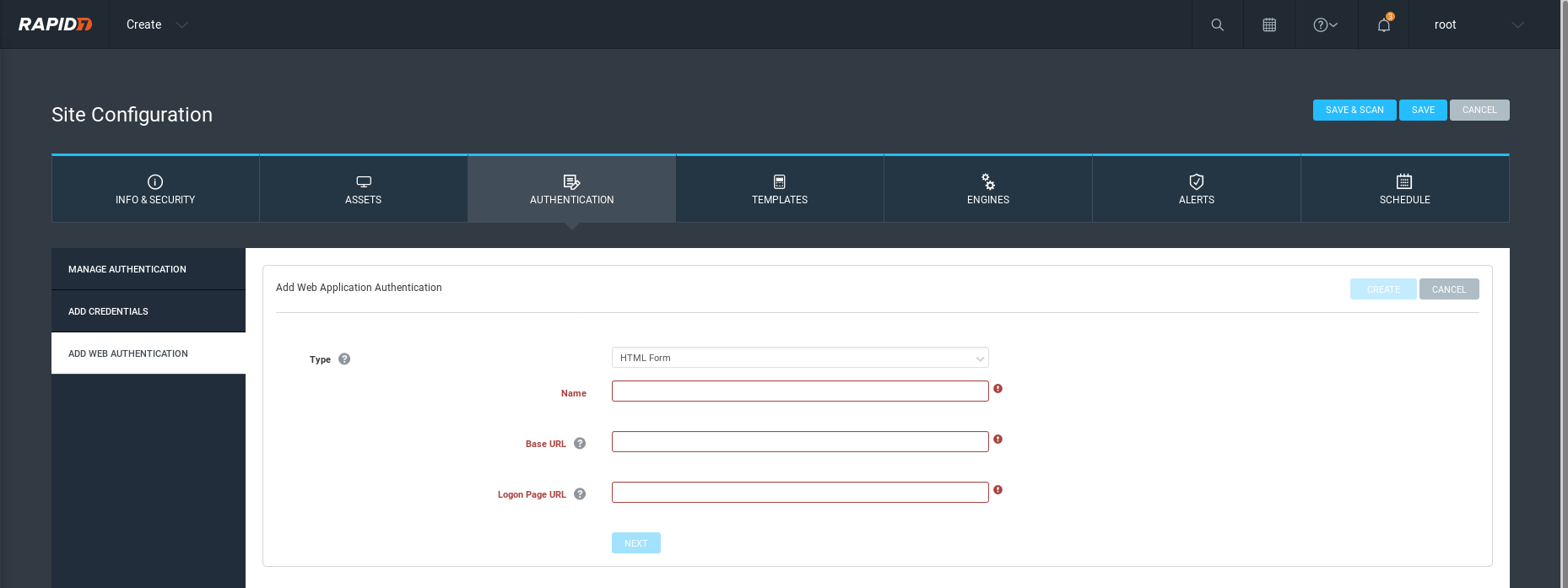
Authentication(Not a must)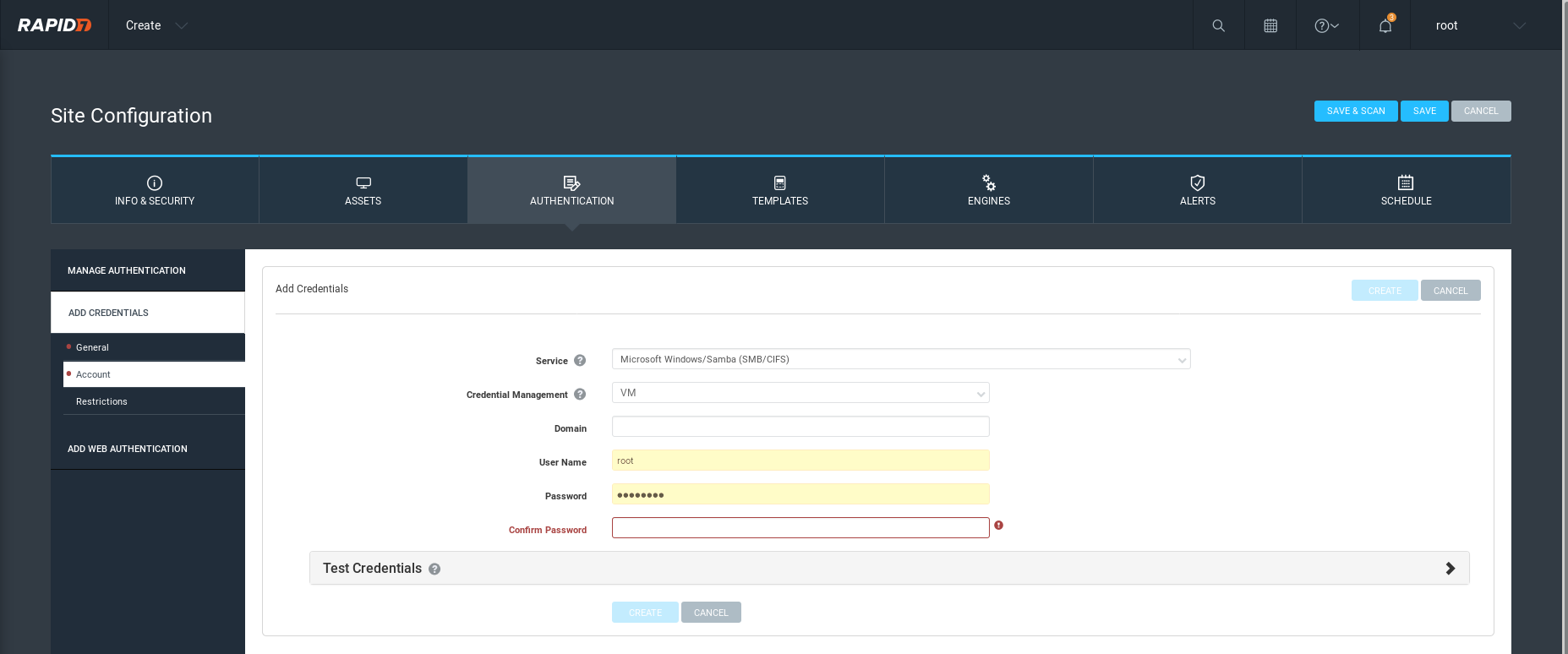
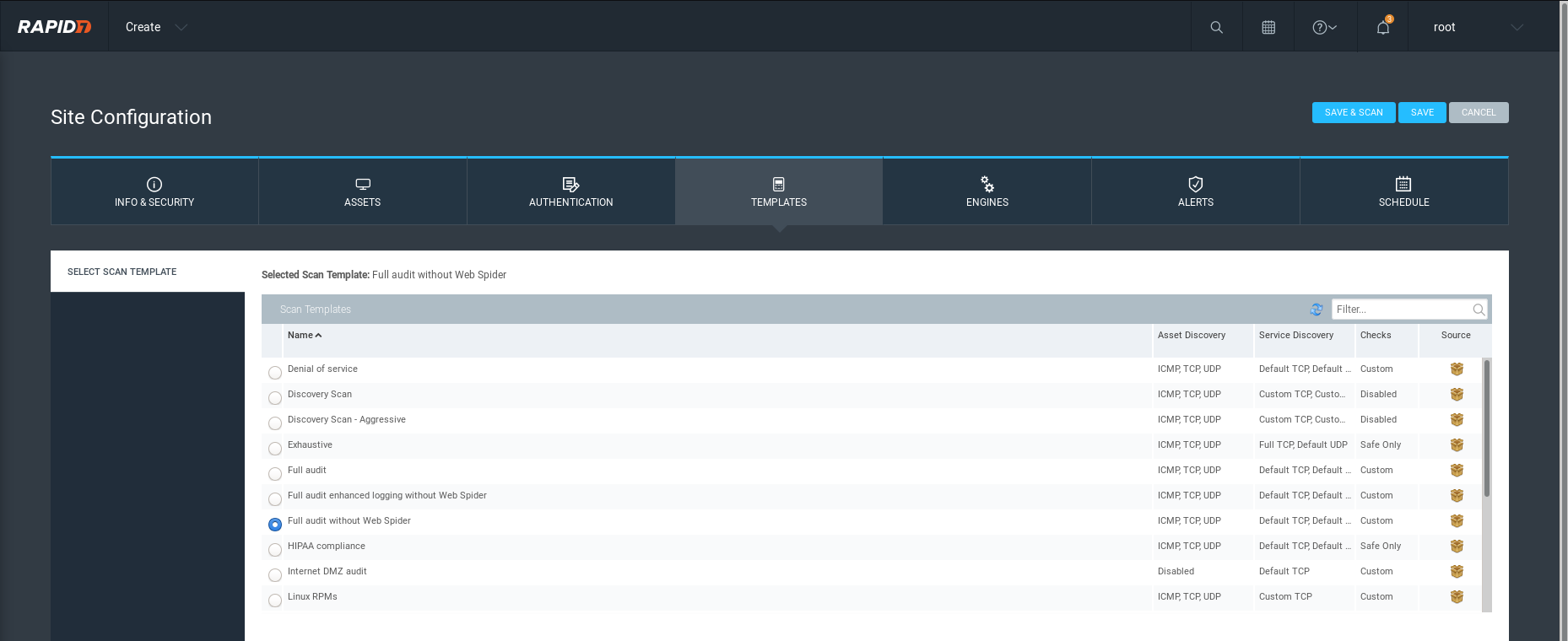
Template:
Choose an Engine.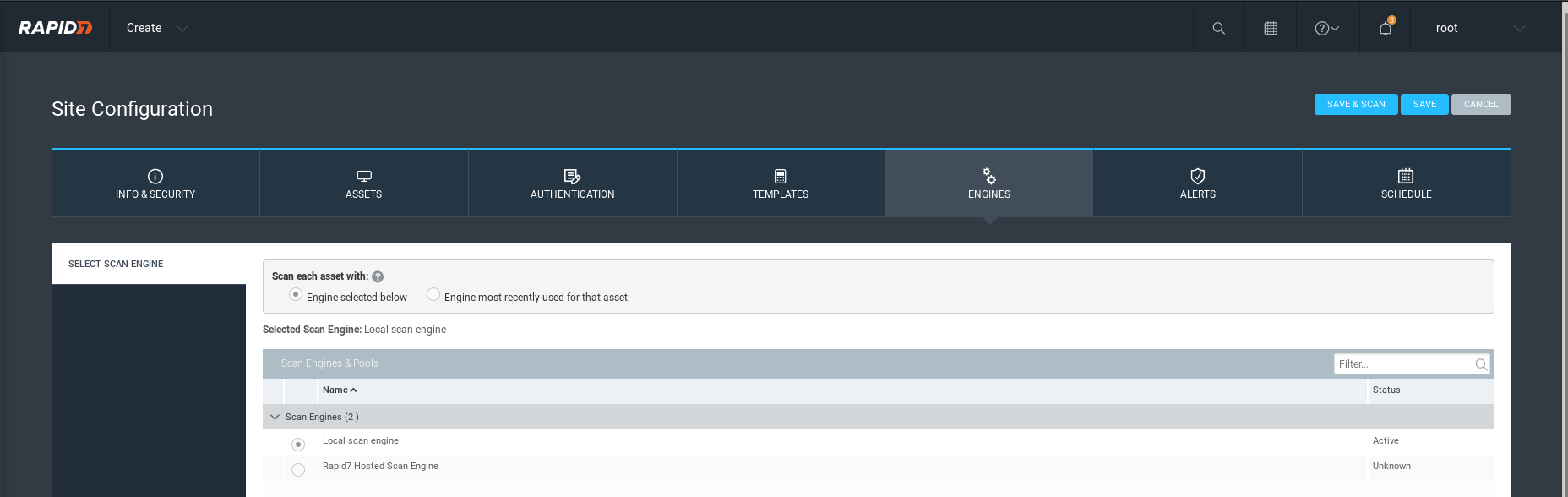
Alerts:

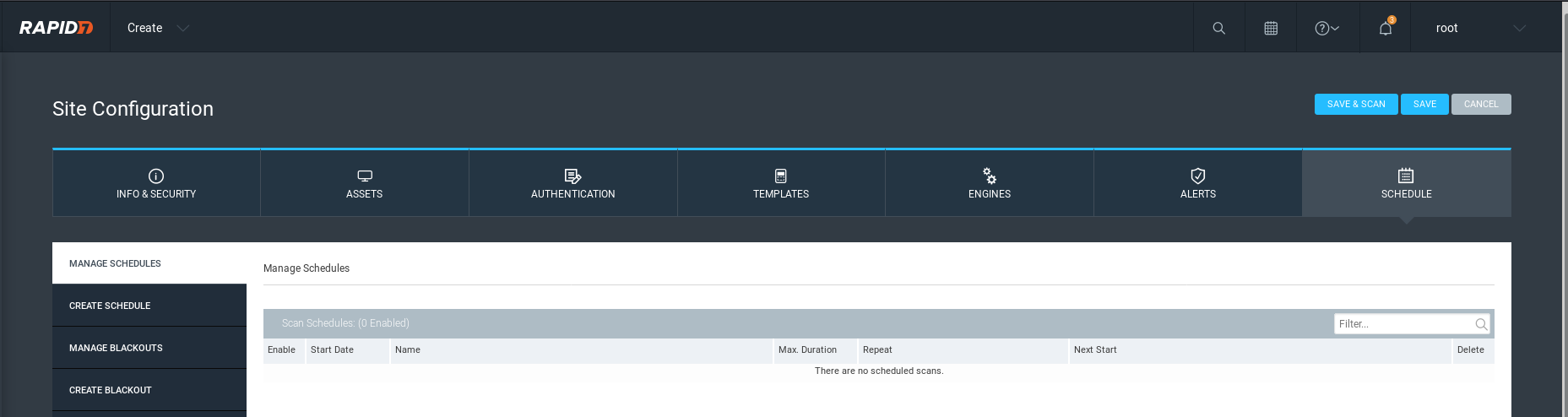
Set the scan schedule based on the critical level.
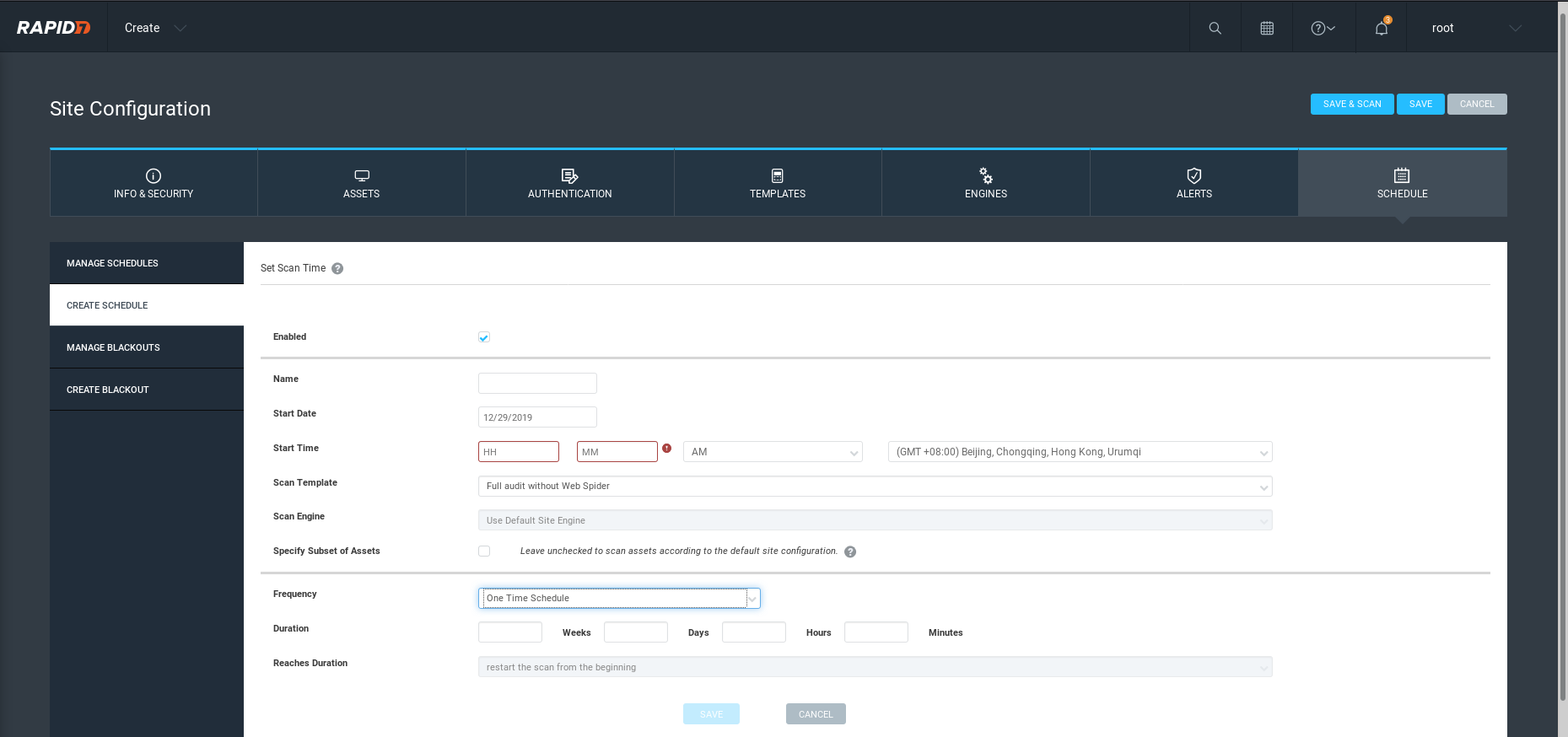
Save and start the scan job.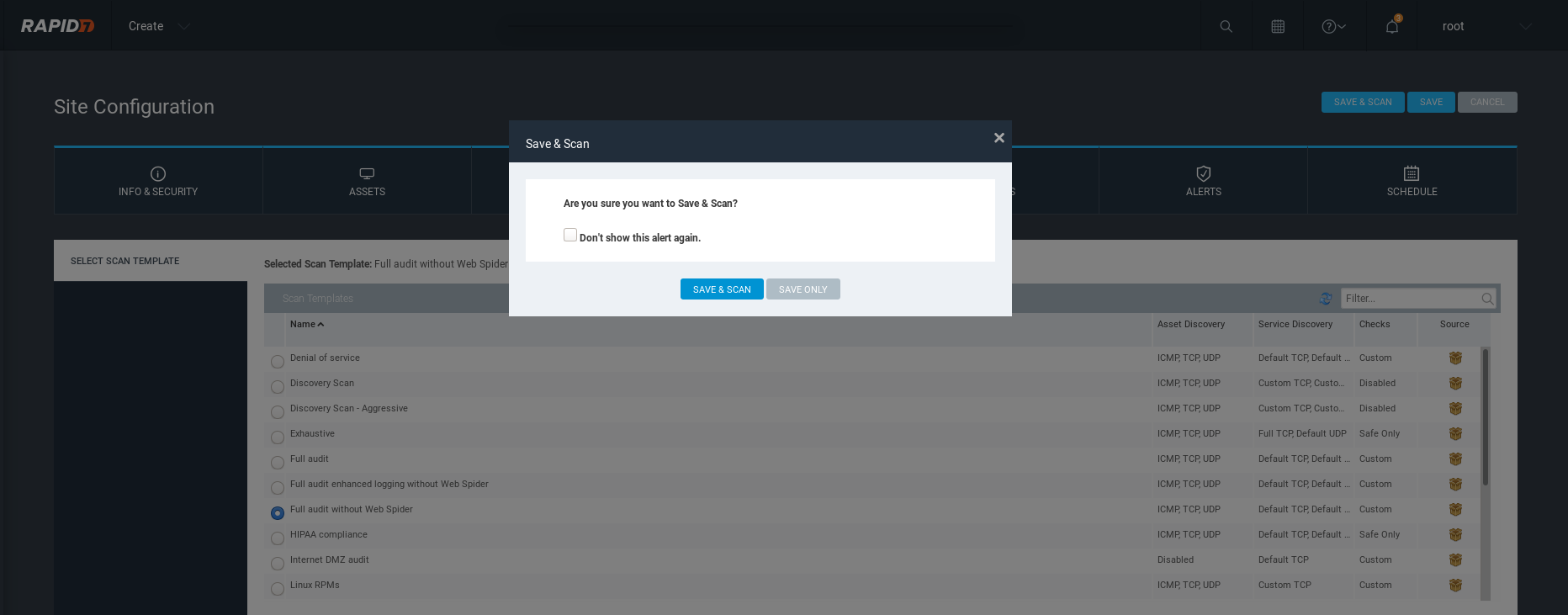
Ethical Hacking - GAINING ACCESS(8)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
- Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS Backdooring ANY file Combine backdoor with any file - Generic solution. Users ar ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
随机推荐
- MFC时间简单比较方法
MFC//时间简单比较方法 void CMFCsaveListTofileDlg::OnBnClickedButton6()//时间简单比较方法 { // TODO: 在此添加控件通知处理程序代码 C ...
- 4a-c++ primer宽字符wchar_t显示设置与输出代码示例
.. #include <iostream> #include <windows.h> #include <locale> //#include<wchar. ...
- WeChair项目Alpha冲刺(10/10)
团队项目进行情况 1.昨日进展 Alpha冲刺第十天 昨日进展: 前端:安排页面美化,设计实名认证 后端:更新dao层代码 数据库:修改数据表属性,与后端部署数据库交互 2.今日安排 前端:继续 ...
- 挖洞入门_显错型SQL注入
简介:在漏洞盒子挖洞已经有一段时间了,虽说还不是大佬,但技术也有所进步,安全行业就是这样,只有自己动手去做,才能将理论的知识变为个人的经验.本篇文章打算分享一下我在挖显错型SQL注入漏洞过程中的一些个 ...
- 也来聊聊 HTTPS.
前言: 网上聊 HTTPS 的文章已经数都数不过来了吧,厚着脸皮,整理下读书笔记,结合平常项目的实践,也来聊聊 HTTPS. 一.为什么需要 HTTPS? 众所周知,HTTP 协议具有无连接.不可靠. ...
- LeetCode 79,这道走迷宫问题为什么不能用宽搜呢?
本文始发于个人公众号:TechFlow,原创不易,求个关注 今天是LeetCode专题第48篇文章,我们一起来看看LeetCode当中的第79题,搜索单词(Word Search). 这一题官方给的难 ...
- oracle包package的使用
创建包 包头: CREATE OR REPLACE PACKAGE test_pkg IS PROCEDURE update_sal(e_name VARCHAR2,newsal NUMBER); ...
- 使用训练好的modle,做些有用的事(各层数据可视化)
---恢复内容开始--- 1. 加载必要的库: 2. 设置当前目录,判断模型是否训练好: 3. 利用提前训练好的模型,设置测试网络: 4. 加载测试图片,并显示: 5. 编写一个函数,将二进制的均值转 ...
- python之浅谈循环
目录 流程控制之while循环 语法 while+break while+continue while+else while循环的嵌套 流程控制之for循环 语法 for+break for+cont ...
- Netty 源码解析(四): Netty 的 ChannelPipeline
今天是猿灯塔“365篇原创计划”第四篇. 接下来的时间灯塔君持续更新Netty系列一共九篇 Netty 源码解析(一): 开始 Netty 源码解析(二): Netty 的 Channel Netty ...
