Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS
XSS - CROSS SITE SCRIPTING VULNS
- Allow an attacker to inject javascript code into the page.
- The code is executed when the page loads.
- The code is executed on the client machine, not the server.
Three main types:
1. Persistent/Stored XSS.
2. Reflected XSS.
3.DOM-based XSS
DISCOVERING XSS
- Try to inject javascript code into the pages.
- Test text boxes and URL parameters on the form
- http://target.com/page.php?something=something
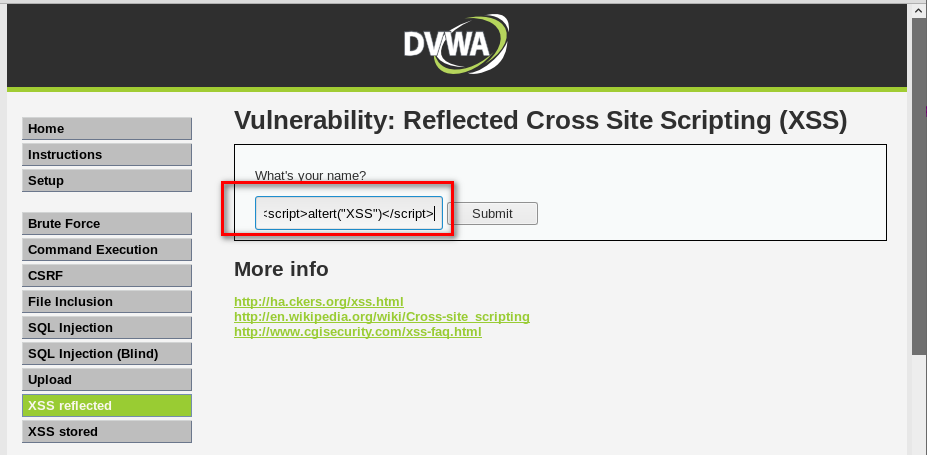
REFLECTED XSS
- None persistent, not stored.
- Only work if the target visits a specially crafted URL
- http://target.com/page.php?something=<script>altert("XSS")</script>
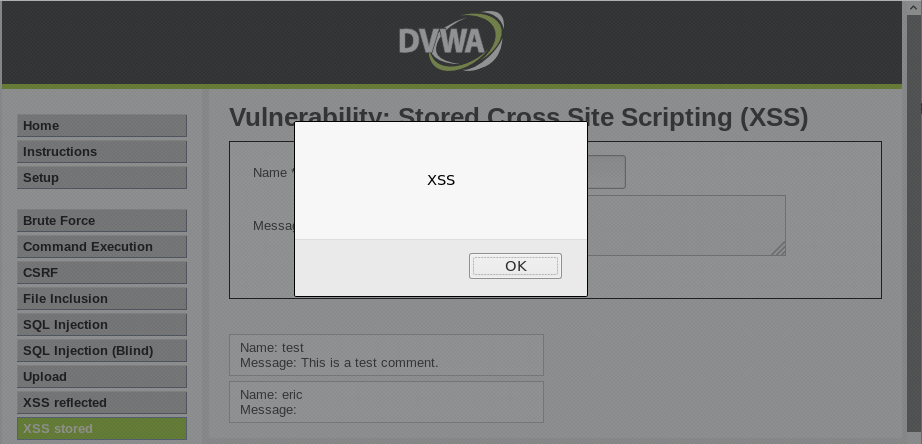
STORED XSS
- Persistent, stored on the page or DB.
- The injected code is executed every time the page is loaded.
Python Ethical Hacking - VULNERABILITY SCANNER(5)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS BASIC INFORMATION FLOW The user clicks on a link. HTML website generates a request(cli ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- 001.OpenShift介绍
一 OpenShift特性 1.1 OpenShift概述 Red Hat OpenShijft Container Platform (OpenShift)是一个容器应用程序平台,它为开发人员和IT ...
- 本地yum源及更新
创建本地yumrepo源 概述 在生产环境中,由于网络环境隔离,很多内网机器,无法直接通过网络下载安装相关软件包,所以这个时候就需要在内网搭建一个yum源,然后通过下载将需要的软件包rpm下载下来,然 ...
- oracle 索引失效原因_汇总
1) 没有查询条件,或者查询条件没有建立索引 2) 在查询条件上没有使用引导列 3) 查询的数量是大表的大部分,应该是30%以上. 4) 索引本身失效 5) 查询条件使用函数在索引列上,或者对索引列进 ...
- 多图解释Redis的整数集合intset升级过程
redis源码分析系列文章 [Redis源码系列]在Liunx安装和常见API 为什么要从Redis源码分析 String底层实现——动态字符串SDS 双向链表都不懂,还说懂Redis? 面试官:说说 ...
- openstack-taskflow 组件记录
[Summary] TaskFlow 是一个为了 openstack 实现的 python 库,使得执行 task 变得简单,一致,易扩展,可靠: 它能以一种声明的方式,将轻量级 task 对象的创建 ...
- hibernate快速入门示例
hibernate概述 hibernate是一个java的全自动ORM框架,它可以自动生成SQL语句.自动建表.自动执行,使用者可以不使用SQL完成数据的CRUD操作,同时它也是基于JPA规则的一种实 ...
- Java1.7的HashMap源码分析-面试必备技能
HashMap是现在用的最多的map,HashMap的源码可以说是面试必备技能,今天我们试着分析一下jdk1.7下的源码. 先说结论:数组加链表 一.先看整体的数据结构 首先我们注意到数据是存放在一个 ...
- 解决只能通过localhost访问Elasticsearch的问题
解决只能通过localhost访问Elasticsearch的问题 在默认情况下Elasticsearch是无法通过外网访问的 需要绑定地址,原因如下: 具体方法为: vim /opt/es/ ...
- Electricity POJ - 2117 + SPF POJ - 1523 去除割点后求强连通分量个数问题
Electricity POJ - 2117 题目描述 Blackouts and Dark Nights (also known as ACM++) is a company that provid ...
- 洛谷 P4408 [NOI2003]逃学的小孩
题目传送门 题目描述 Chris家的电话铃响起了,里面传出了Chris的老师焦急的声音:“喂,是Chris的家长吗?你们的孩子又没来上课,不想参加考试了吗?”一听说要考试,Chris的父母就心急如焚, ...
