Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters
1. Watch the URL of the XSS reflected page carefully.
2. Add the test_xss_in_link method in the Scanner class.
#!/usr/bin/env python import requests
import re
from bs4 import BeautifulSoup
from urllib.parse import urljoin class Scanner:
def __init__(self, url, ignore_links):
self.session = requests.Session()
self.target_url = url
self.target_links = []
self.links_to_ignore = ignore_links def extract_links_from(self, url):
response = self.session.get(url)
return re.findall('(?:href=")(.*?)"', response.content.decode(errors='ignore')) def crawl(self, url=None):
if url == None:
url = self.target_url
href_links = self.extract_links_from(url)
for link in href_links:
link = urljoin(url, link) if "#" in link:
link = link.split("#")[0] if self.target_url in link and link not in self.target_links and link not in self.links_to_ignore:
self.target_links.append(link)
print(link)
self.crawl(link) def extract_forms(self, url):
response = self.session.get(url)
parsed_html = BeautifulSoup(response.content.decode(), features="lxml")
return parsed_html.findAll("form") def submit_form(self, form, value, url):
action = form.get("action")
post_url = urljoin(url, action)
method = form.get("method") inputs_list = form.findAll("input")
post_data = {}
for input in inputs_list:
input_name = input.get("name")
input_type = input.get("type")
input_value = input.get("value")
if input_type == "text":
input_value = value post_data[input_name] = input_value
if method == "post":
return requests.post(post_url, data=post_data)
return self.session.get(post_url, params=post_data) def run_scanner(self):
for link in self.target_links:
forms = self.extract_forms(link)
for form in forms:
print("[+] Testing form in " + link) if "=" in link:
print("[+] Testing " + link) def test_xss_in_link(self, url):
xss_test_script = "<sCript>alert('test')</scriPt>"
url = url.replace("=", "=" + xss_test_script)
response = self.session.get(url)
return xss_test_script in response.content.decode() def test_xss_in_form(self, form, url):
xss_test_script = "<sCript>alert('test')</scriPt>"
response = self.submit_form(form, xss_test_script, url)
return xss_test_script in response.content.decode()
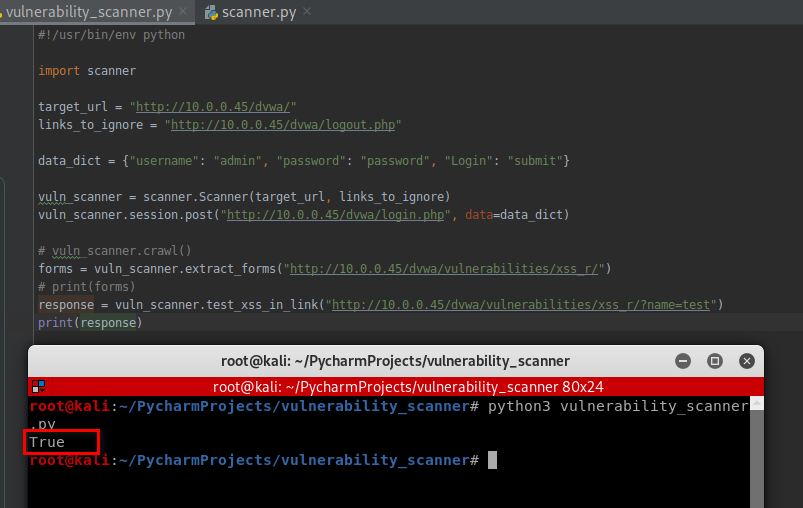
3. Test this scanner.
#!/usr/bin/env python import scanner target_url = "http://10.0.0.45/dvwa/"
links_to_ignore = "http://10.0.0.45/dvwa/logout.php" data_dict = {"username": "admin", "password": "password", "Login": "submit"} vuln_scanner = scanner.Scanner(target_url, links_to_ignore)
vuln_scanner.session.post("http://10.0.0.45/dvwa/login.php", data=data_dict) # vuln_scanner.crawl()
forms = vuln_scanner.extract_forms("http://10.0.0.45/dvwa/vulnerabilities/xss_r/")
print(forms)
response = vuln_scanner.test_xss_in_link("http://10.0.0.45/dvwa/vulnerabilities/xss_r/?name=test")
print(response)
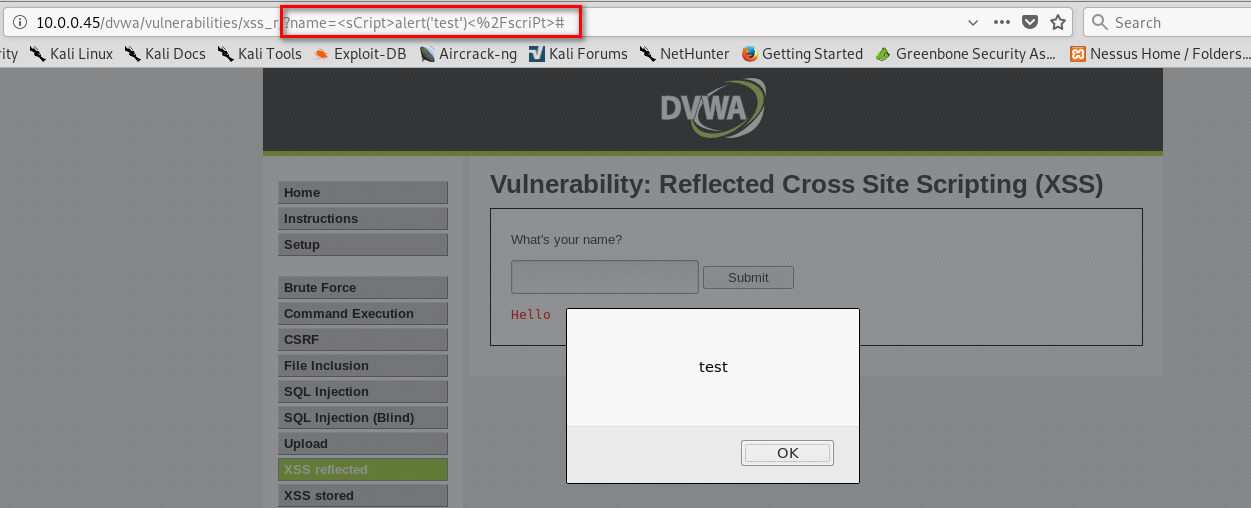
Test the web page - http://10.0.0.45/dvwa/vulnerabilities/xss_r/?name=test:
vuln_scanner.test_xss_in_link("http://10.0.0.45/dvwa/vulnerabilities/xss_r/?name=test")
It is vulnerable on XSS.
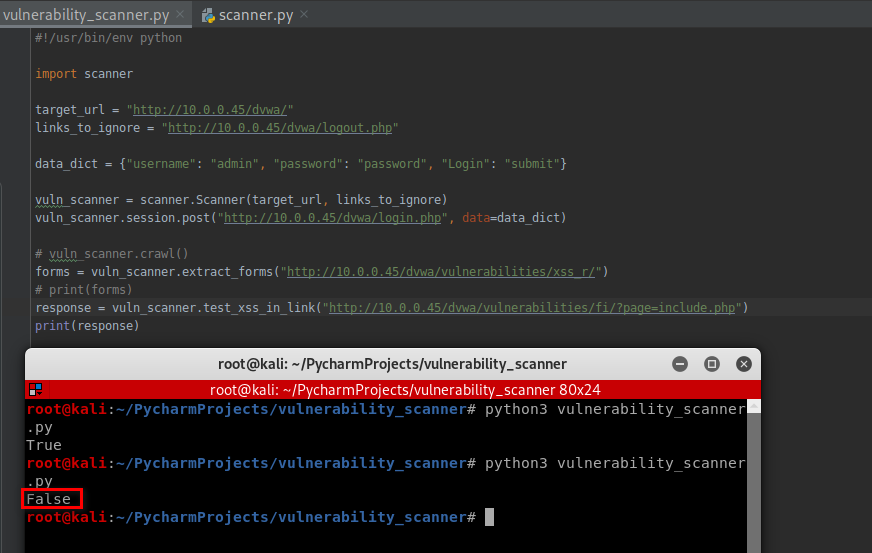
Test the web page - http://10.0.0.45/dvwa/vulnerabilities/fi/?page=include.php:
vuln_scanner.test_xss_in_link("http://10.0.0.45/dvwa/vulnerabilities/fi/?page=include.php")
It is not vulnerable on XSS.
Python Ethical Hacking - VULNERABILITY SCANNER(8)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS BASIC INFORMATION FLOW The user clicks on a link. HTML website generates a request(cli ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- cron计划任务
格式 crontab -e [-u 用户名] ##编辑:注意,每项工作都是一行. crontab -l [-u 用户名] ##查看 crontab -r [-u 用户名] #清除 分 时 日 月 周 ...
- python3.6 + django2.0.6 + xadmin0.6
django2.0集成xadmin0.6报错集锦 http://www.lybbn.cn/data/bbsdatas.php?lybbs=50 1.django2.0把from django.core ...
- 再看rabbitmq的交换器和队列的关系
最近又要用到rabbitmq,业务上要求服务器只发一次消息,需要多个客户端都去单独消费.但我们知道rabbitmq的机制里,每个队列里的消息只能消费一次,所以客户端要单独消费信息,就必须得每个客户端单 ...
- Project Loom:Reactive模型和协程进行时(翻译)
Java 15将发布Project Loom的第一个版本.我相信这将改变JVM.在这篇文章中,我想深入探讨一下导致我相信这一点的原因. 首先,我们需要了解核心问题.然后,我将尝试描述以前的技术如何解决 ...
- js清除所有的空格
/** * 清除所有的空格 * @returns {*} */ String.prototype.removeSpace = function () { var str = this.replaceA ...
- SpringCloud 入门(一)
本人也是刚接触springcloud,现在先将创建项目的过程记录下来,springcloud的理解日后再慢慢补齐,最好还是自己参考官方文档的介绍 使用工具:IDEA IDEA创建springcloud ...
- 利用EasyMock生成数据库连接简单测试示例
package demo.mock; import java.sql.Connection; import java.sql.PreparedStatement; import java.sql.Re ...
- 【弹性碰撞问题】POJ 1852 Ants
Description An army of ants walk on a horizontal pole of length l cm, each with a constant speed of ...
- C++ MFC 操作文件夹及属性(新建,删除[包含子文件[夹]],剪切,复制,重命名)
源文件:http://pan.baidu.com/s/169HCL 运行mfc缺失的动态连接库:http://pan.baidu.com/s/17pGlT 截图: 不足之处仅供参考,哈哈.
- python使用selenium和requests.session登录抓取
# Author:song from selenium import webdriver from selenium.webdriver.common.keys import Keys from re ...
