Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner
1. Modify the run_scanner method in the scanner class.
#!/usr/bin/env python import requests
import re
from bs4 import BeautifulSoup
from urllib.parse import urljoin class Scanner:
def __init__(self, url, ignore_links):
self.session = requests.Session()
self.target_url = url
self.target_links = []
self.links_to_ignore = ignore_links def extract_links_from(self, url):
response = self.session.get(url)
return re.findall('(?:href=")(.*?)"', response.content.decode(errors='ignore')) def crawl(self, url=None):
if url == None:
url = self.target_url
href_links = self.extract_links_from(url)
for link in href_links:
link = urljoin(url, link) if "#" in link:
link = link.split("#")[0] if self.target_url in link and link not in self.target_links and link not in self.links_to_ignore:
self.target_links.append(link)
print(link)
self.crawl(link) def extract_forms(self, url):
response = self.session.get(url)
parsed_html = BeautifulSoup(response.content, features="lxml")
return parsed_html.findAll("form") def submit_form(self, form, value, url):
action = form.get("action")
post_url = urljoin(url, action)
method = form.get("method") inputs_list = form.findAll("input")
post_data = {}
for input in inputs_list:
input_name = input.get("name")
input_type = input.get("type")
input_value = input.get("value")
if input_type == "text":
input_value = value post_data[input_name] = input_value
if method == "post":
return requests.post(post_url, data=post_data)
return self.session.get(post_url, params=post_data) def run_scanner(self):
for link in self.target_links:
forms = self.extract_forms(link)
for form in forms:
print("[+] Testing form in " + link)
is_vulnerable_to_xss = self.test_xss_in_form(form, link)
if is_vulnerable_to_xss:
print("\n\n[***] XSS discovered in " + link + " in the following from")
print(form) if "=" in link:
print("\n\n[+] Testing " + link)
is_vulnerable_to_xss = self.test_xss_in_link(link)
if is_vulnerable_to_xss:
print("[***] Discovered XSS in " + link) def test_xss_in_link(self, url):
xss_test_script = "<sCript>alert('test')</scriPt>"
url = url.replace("=", "=" + xss_test_script)
response = self.session.get(url)
return xss_test_script in response.content.decode() def test_xss_in_form(self, form, url):
xss_test_script = "<sCript>alert('test')</scriPt>"
response = self.submit_form(form, xss_test_script, url)
return xss_test_script in response.content.decode()
2. Test this new automatically vulnerability scanner.
#!/usr/bin/env python import scanner target_url = "http://10.0.0.45/dvwa/"
links_to_ignore = "http://10.0.0.45/dvwa/logout.php" data_dict = {"username": "admin", "password": "password", "Login": "submit"} vuln_scanner = scanner.Scanner(target_url, links_to_ignore)
vuln_scanner.session.post("http://10.0.0.45/dvwa/login.php", data=data_dict) vuln_scanner.crawl()
vuln_scanner.run_scanner()
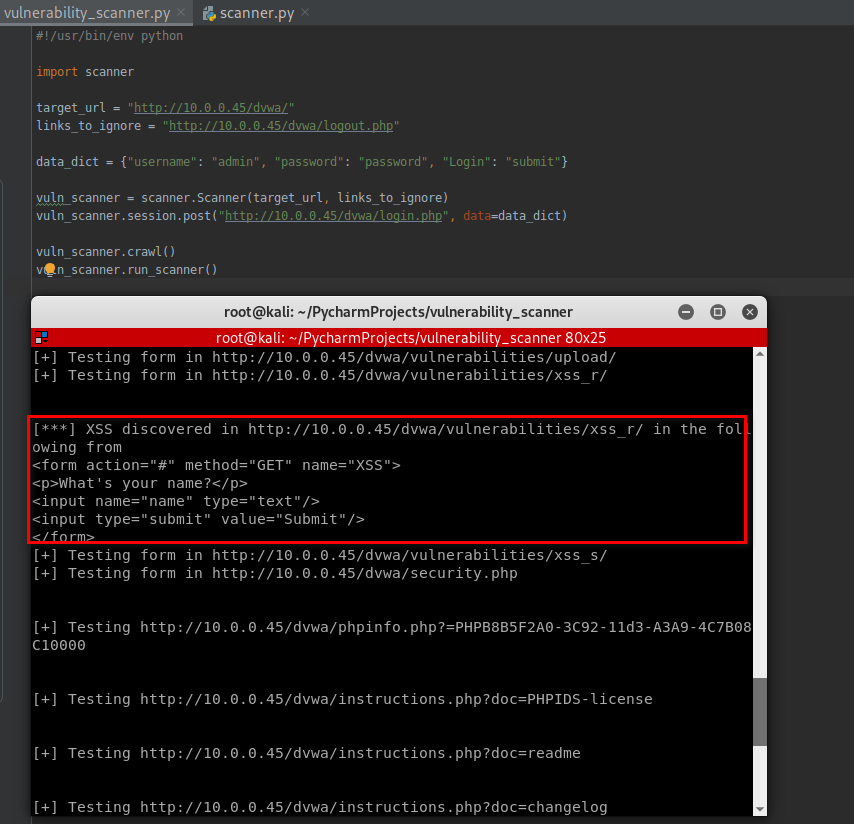
Following is the full test result.
root@kali:~/PycharmProjects/vulnerability_scanner# python3 vulnerability_scanner.py
http://10.0.0.45/dvwa/dvwa/css/main.css
http://10.0.0.45/dvwa/favicon.ico
http://10.0.0.45/dvwa/instructions.php
http://10.0.0.45/dvwa/setup.php
http://10.0.0.45/dvwa/vulnerabilities/brute/
http://10.0.0.45/dvwa/vulnerabilities/exec/
http://10.0.0.45/dvwa/vulnerabilities/csrf/
http://10.0.0.45/dvwa/vulnerabilities/fi/?page=include.php
http://10.0.0.45/dvwa/vulnerabilities/sqli/
http://10.0.0.45/dvwa/vulnerabilities/sqli_blind/
http://10.0.0.45/dvwa/vulnerabilities/upload/
http://10.0.0.45/dvwa/vulnerabilities/xss_r/
http://10.0.0.45/dvwa/vulnerabilities/xss_s/
http://10.0.0.45/dvwa/security.php
http://10.0.0.45/dvwa/phpinfo.php
http://10.0.0.45/dvwa/phpinfo.php?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000
http://10.0.0.45/dvwa/about.php
http://10.0.0.45/dvwa/instructions.php?doc=PHPIDS-license
http://10.0.0.45/dvwa/instructions.php?doc=readme
http://10.0.0.45/dvwa/instructions.php?doc=changelog
http://10.0.0.45/dvwa/instructions.php?doc=copying
http://10.0.0.45/dvwa/security.php?phpids=on
http://10.0.0.45/dvwa/security.php?phpids=off
http://10.0.0.45/dvwa/security.php?test=%22><script>eval(window.name)</script>
http://10.0.0.45/dvwa/ids_log.php
[+] Testing form in http://10.0.0.45/dvwa/setup.php
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/brute/
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/exec/
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/csrf/ [+] Testing http://10.0.0.45/dvwa/vulnerabilities/fi/?page=include.php
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/sqli/
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/sqli_blind/
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/upload/
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/xss_r/ [***] XSS discovered in http://10.0.0.45/dvwa/vulnerabilities/xss_r/ in the following from
<form action="#" method="GET" name="XSS">
<p>What's your name?</p>
<input name="name" type="text"/>
<input type="submit" value="Submit"/>
</form>
[+] Testing form in http://10.0.0.45/dvwa/vulnerabilities/xss_s/
[+] Testing form in http://10.0.0.45/dvwa/security.php [+] Testing http://10.0.0.45/dvwa/phpinfo.php?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000 [+] Testing http://10.0.0.45/dvwa/instructions.php?doc=PHPIDS-license [+] Testing http://10.0.0.45/dvwa/instructions.php?doc=readme [+] Testing http://10.0.0.45/dvwa/instructions.php?doc=changelog [+] Testing http://10.0.0.45/dvwa/instructions.php?doc=copying
[+] Testing form in http://10.0.0.45/dvwa/security.php?phpids=on [+] Testing http://10.0.0.45/dvwa/security.php?phpids=on
[+] Testing form in http://10.0.0.45/dvwa/security.php?phpids=off [+] Testing http://10.0.0.45/dvwa/security.php?phpids=off
[+] Testing form in http://10.0.0.45/dvwa/security.php?test=%22><script>eval(window.name)</script> [+] Testing http://10.0.0.45/dvwa/security.php?test=%22><script>eval(window.name)</script>
[+] Testing form in http://10.0.0.45/dvwa/ids_log.php
You can add new methods in the scanner class to find more vulnerabilities.
Python Ethical Hacking - VULNERABILITY SCANNER(9)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS BASIC INFORMATION FLOW The user clicks on a link. HTML website generates a request(cli ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- c#openCV图片传递-尝试读取或写入受保护的内存。这通常指示其他内存已损坏。解决方法
未处理AccessViolationException 这通常指示其他内存已损坏,这里内存损坏并非物理的内存条损坏.猜想是执行到此步骤后,内存空间被清理了,没有找到内存地址的感觉. public st ...
- 09.DRF-ModelSerializer
四.模型类序列化器ModelSerializer 如果我们想要使用序列化器对应的是Django的模型类,DRF为我们提供了ModelSerializer模型类序列化器来帮助我们快速创建一个Serial ...
- Linux Pam后门总结拓展
首发先知社区: https://xz.aliyun.com/t/7902 前言 渐渐发现pam后门在实战中存在种植繁琐.隐蔽性不强等缺点,这里记录下学习pam后门相关知识和pam后门的拓展改进. 0x ...
- 图解 Git 基本命令 merge 和 rebase
Git 基本命令 merge 和 rebase,你真的了解吗? 前言 Git 中的分支合并是一个常见的使用场景. 仓库的 bugfix 分支修复完 bug 之后,要回合到主干分支,这时候两个分支需要合 ...
- junit配合catubuter统计单元测试的代码覆盖率
1.视频参考孔浩老师ant视频笔记 对应的build-junit.xml脚步如下所示: <?xml version="1.0" encoding="UTF-8&qu ...
- Python分支结构与流程控制
Python分支结构与流程控制 分支结构 if 语句 分支结构在任何编程语言中都是至关重要的一环,它最主要的目的是让计算机拥有像人一样的思想,能在不同的情况下做出不同的应对方案,所以if语句不管是在什 ...
- 基于MarkDown和Github图床以及SourceTree的一站式文章编辑和发布
标题: 基于MarkDown和Github图床以及SourceTree的一站式文章编辑和发布 作者: 梦幻之心星 sky-seeker@qq.com 标签: [MarkDown,Github,图床,S ...
- vue全家桶(2.3)
3.4.嵌套路由 实际生活中的应用界面,通常由多层嵌套的组件组合而成.同样地,URL 中各段动态路径也按某种结构对应嵌套的各层组件,例如: 再来看看下面这种更直观的嵌套图: 接下来我们需要实现下面这种 ...
- java使字符串的数字加一
/** * 字符串+1方法,该方法将其结尾的整数+1,适用于任何以整数结尾的字符串,不限格式,不限分隔符. * @author zxcvbnmzb * @param testStr 要+1的字符串 * ...
- " 橘松 " 的自我介绍
昵称:(OrangeCsong)橘松(在其他平台也是这个名字) 年龄:95后(摩羯座) 性别:boy 性格:性格还阔以,不轻易发脾气,沉稳.喜欢独立思考. 爱好:运动(工作了,运动时间太少),基金理财 ...
