Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap
Nmap is a network discovery tool that can be used to gather detailed information about any client or network.
We shall have a look at some of its uses to discover connected clients and gather information about them.
We are going to use Zenmap - the GUI for Namp.
1. Ping scan: Very quick - only shows connected clients.

2. Quick scan plus: Quick - shows MAC and open clients.
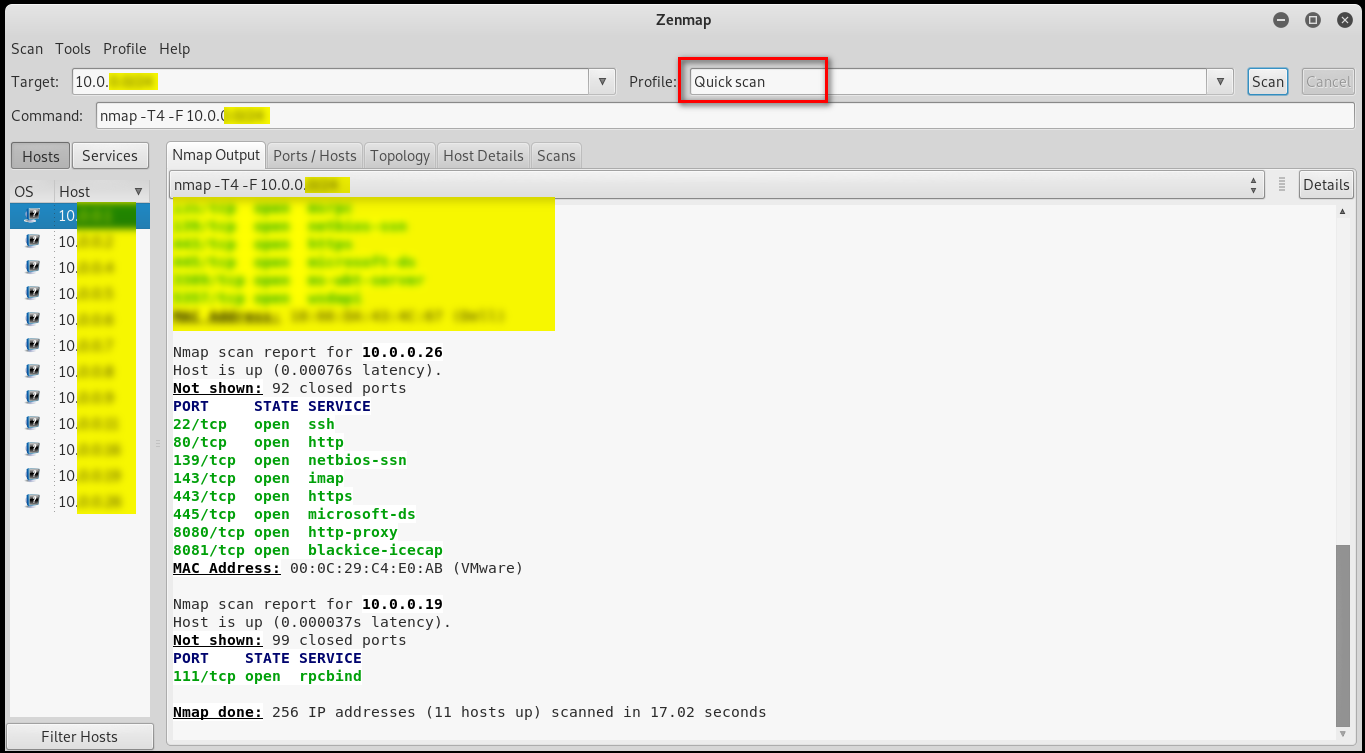
3. Quick scan plus: Slower than the 2 above, more detailed info.

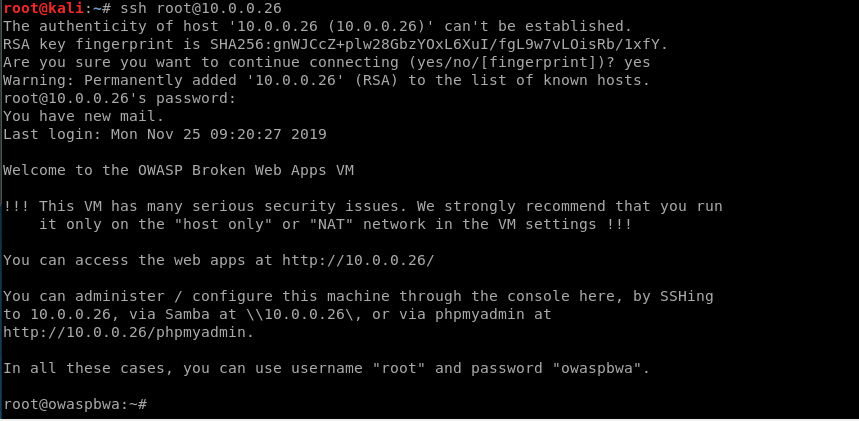
Many people are too lazy to change the password, so I log in to the target victim pc through default username/password.
Ethical Hacking - NETWORK PENETRATION TESTING(13)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- VMWare12安装CentOS7操作系统并搭建GitLab环境【1】
查看了网上这方面的资料,发现都比较复杂,自己到官方网站上查询,并实际动手安装了一下,发现还是比较简单的. 1.VMWare Workstation 12 Professinal安装 2.安装64位Ce ...
- Linux MySQL集群搭建之主从复制
前期准备 准备两台Linux,一主,一从,具体Linux安装MySQL操作步骤:点我直达 集群搭建 注意事项 一主可以多从 一从只能一主 关闭主从机器的防火墙策略 chkconfig iptables ...
- Linux文件目录和访问权限
前言 本文知识点是曾经学习过程中收录整理的,方便学习使用,并非在下撰写. 一>Lniux目录结构 /:根目录,一般根目录下只存放目录,在Linux下有且只有一个根目录.所有的东西都是从这里开始. ...
- Mysql使用xtrabackup备份失败处理
在生产环境中使用的是xtrabackup,对mysql进行备份,每天0点开始备份,周日是全量备份,其他时间是基于周日做的增量备份,通过脚本实现,每天备份完成后会发送短信,突然有一天,备份全部失败,手动 ...
- Redis:rdb和aof
由于redis的数据都直接存储在内存里,在服务器发生宕机时内存的数据会瞬间清空,那么必须要有重启时恢复数据的方法. redis通过持久化机制将数据存储到磁盘中从而在服务器重启时恢复数据,这篇文章主要简 ...
- 搜索引擎-SHODAN
shodan这个搜索引擎不会爬取网页内容,而是爬取所有的联网设备. 这个搜索引擎还是很强大的,下图就是我用shodan查自己的案例服务器的结果: 如图,可以查到这台服务器安装了wdcp管理面板,黑客完 ...
- python黑帽子之tcp服务端
试着用python创建一个标准的多线程tcp服务器 import socket import threading bind_ip = "0.0.0.0" bind_port = 8 ...
- ABP(ASP.NET Boilerplate Project)快速入门
前言 这两天看了一下ABP,做个简单的学习记录.记录主要有以下内容: 从官网创建并下载项目(.net core 3.x + vue) 项目在本地成功运行 新增实体并映射到数据库 完成对新增实体的基本增 ...
- HTTP 协议详解(二)
前面一篇已经说过了 HTTP 的基本特性,HTTP 的发展史,前情回顾.这一篇就更详细的 HTTP 协议使用过程一些参数配置,缓存,Cookie设置相关的细节做一些梳理. 数据类型与编码 在 TCP/ ...
- SELinux已经允许,为什么日志显示的仍然是denied?
从日志可以看到,SELinux的Mode已经修改位了permissive = 1,也就是允许模式,但它前面的日志仍然显示的是“denied".本来我还以为是自己哪里没弄好导致的这个问题,但访 ...
