Ethical Hacking - GAINING ACCESS(9)
Server Side Attack
Nexpose - Analysing Scan Results and Generating Reports
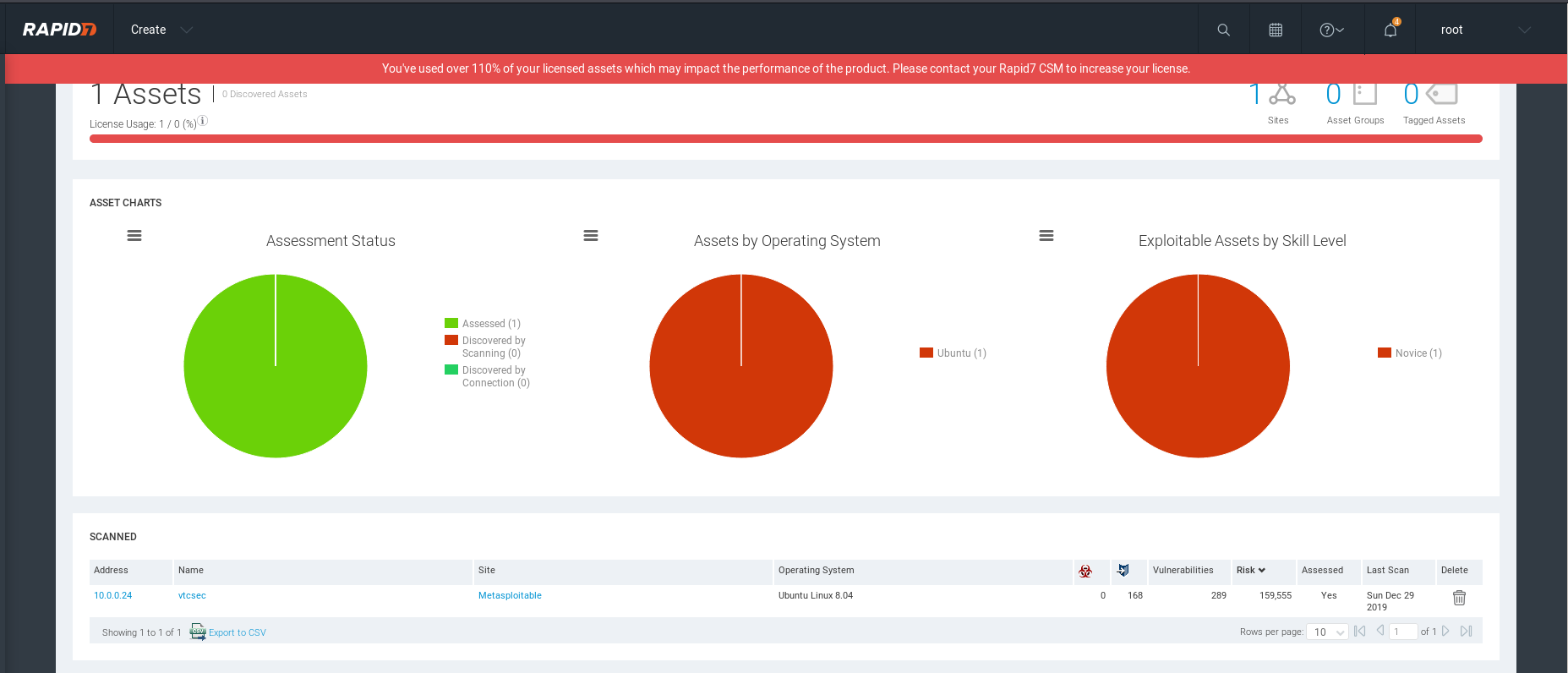
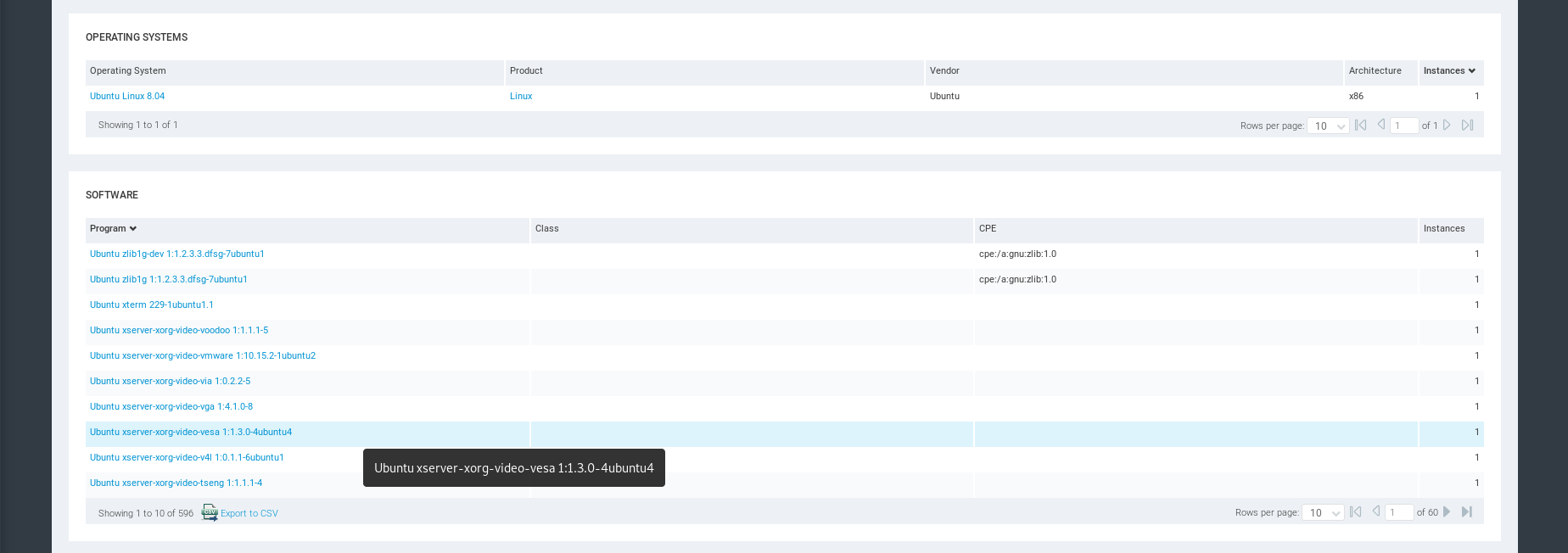
OS and Software Inforation.
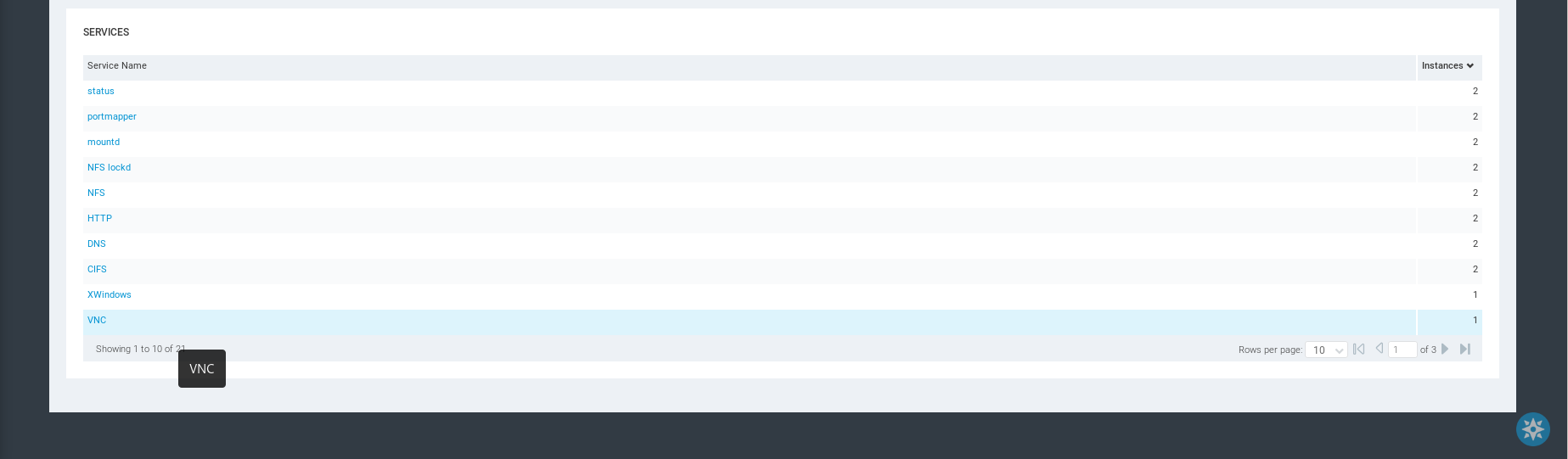
Services Information
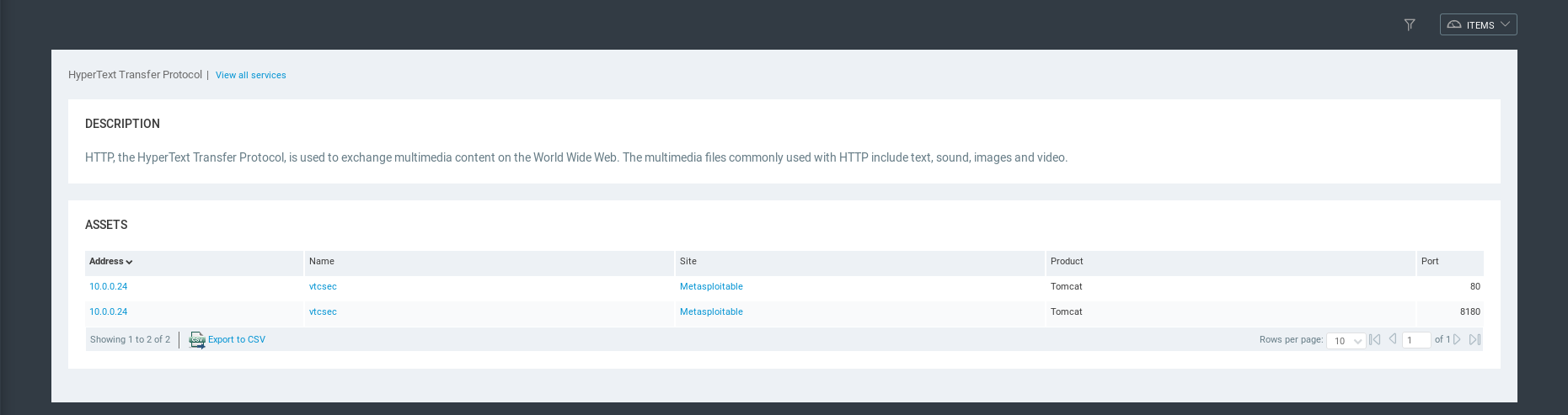
HTTP Service Detailed Information.
Vulnerability Information
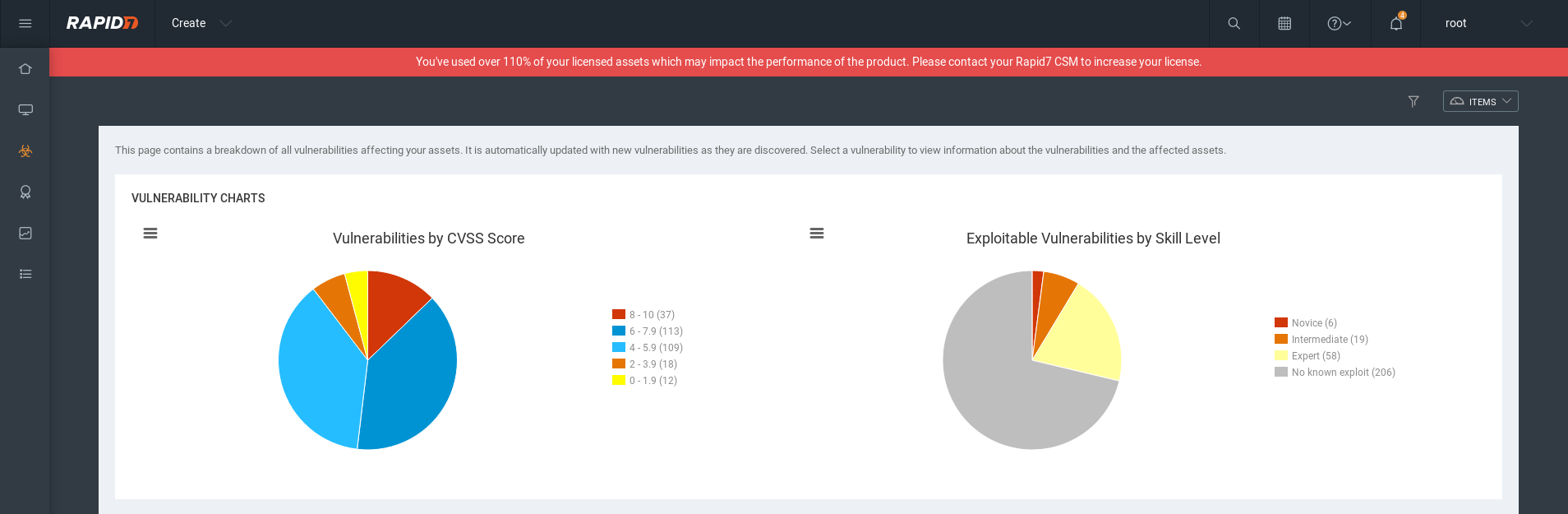
Vulnerabilities list:
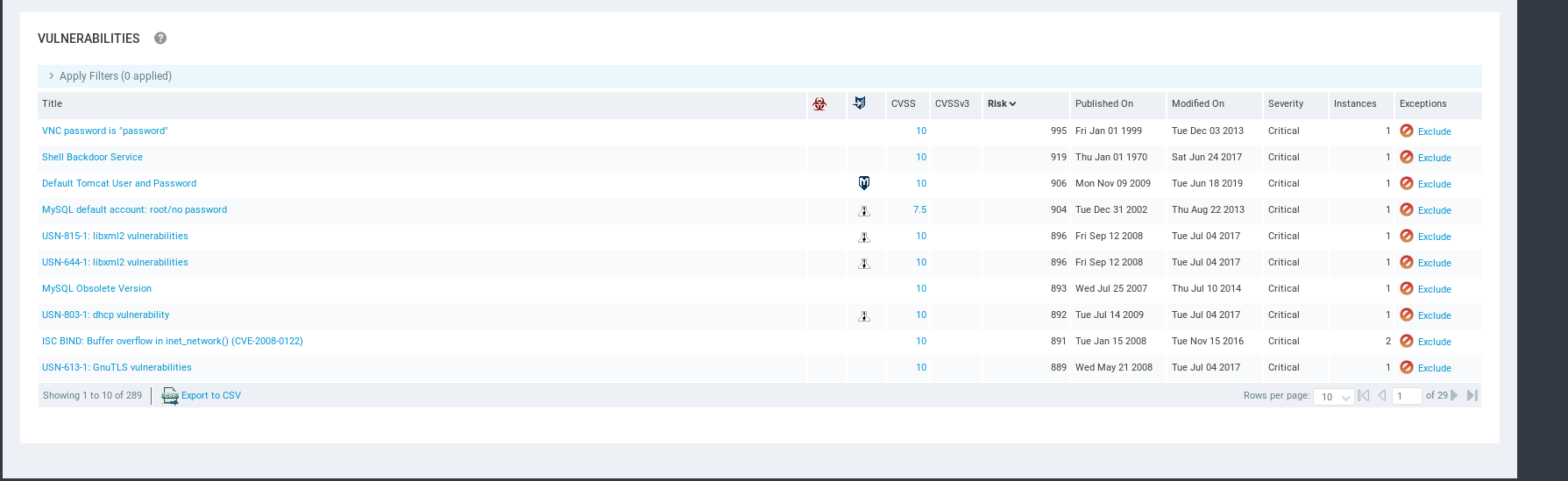
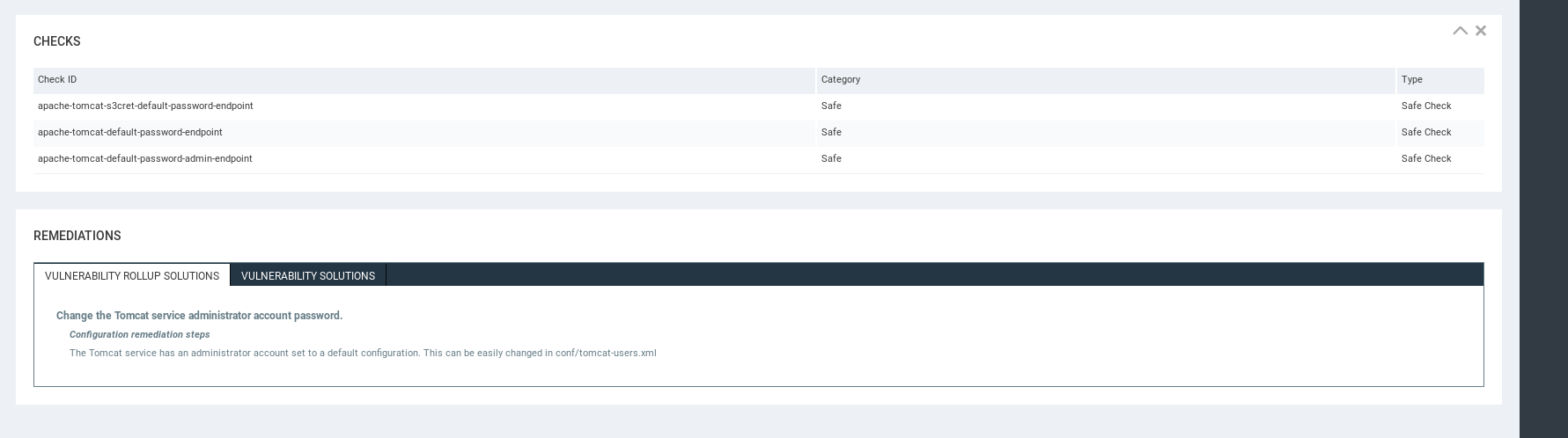
Detailed Vulnerability Information - Affects
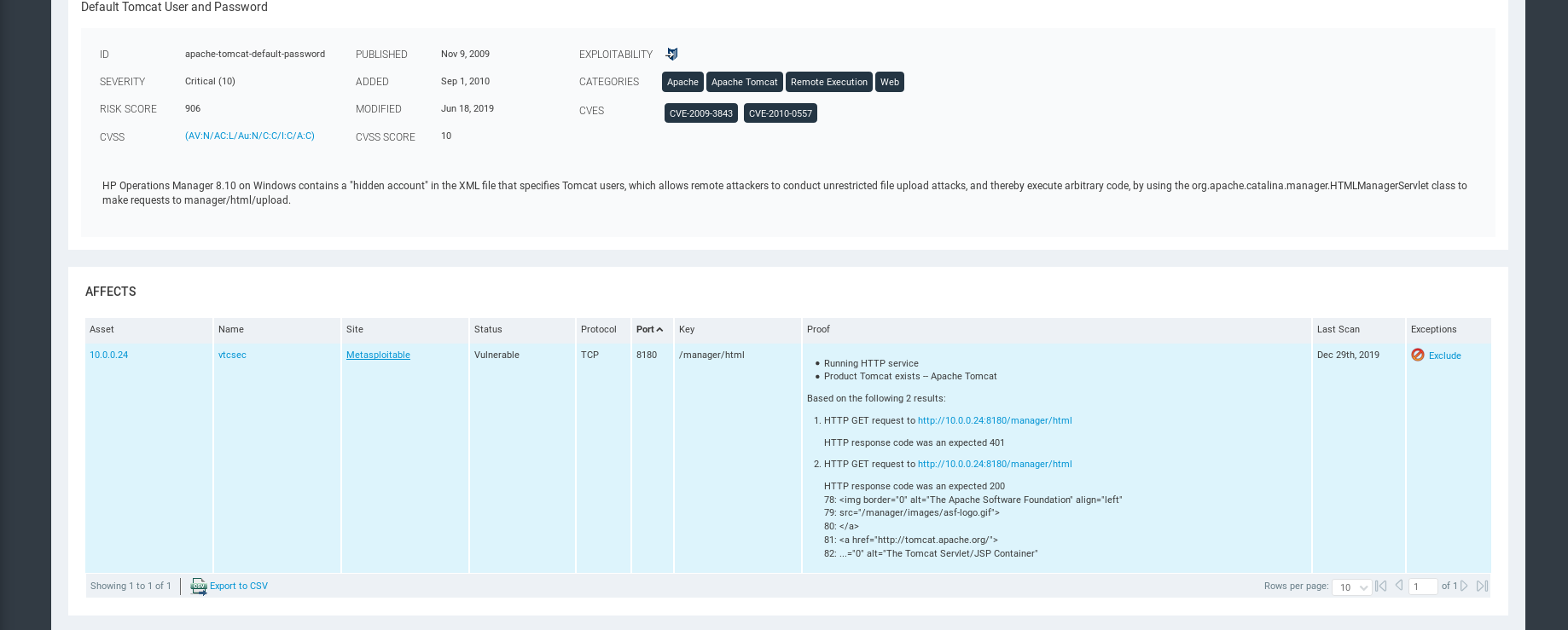
Exploits can be used in Metasploit.
Remediations.
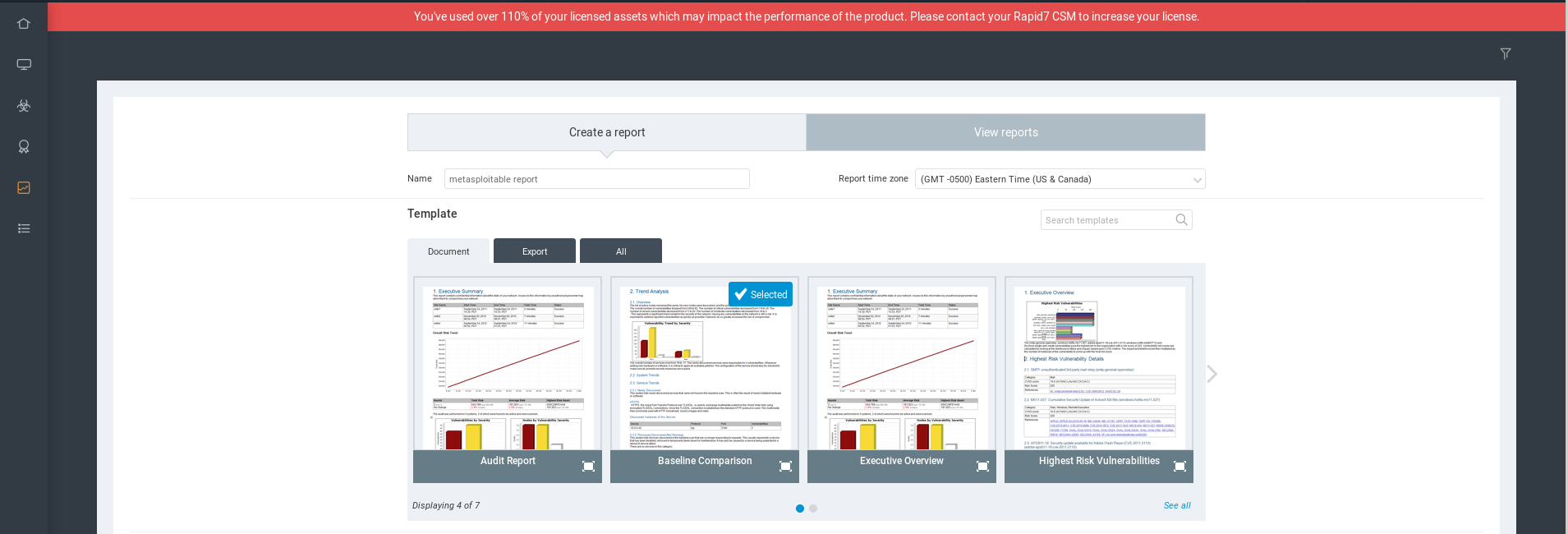
Report
Select the template first.
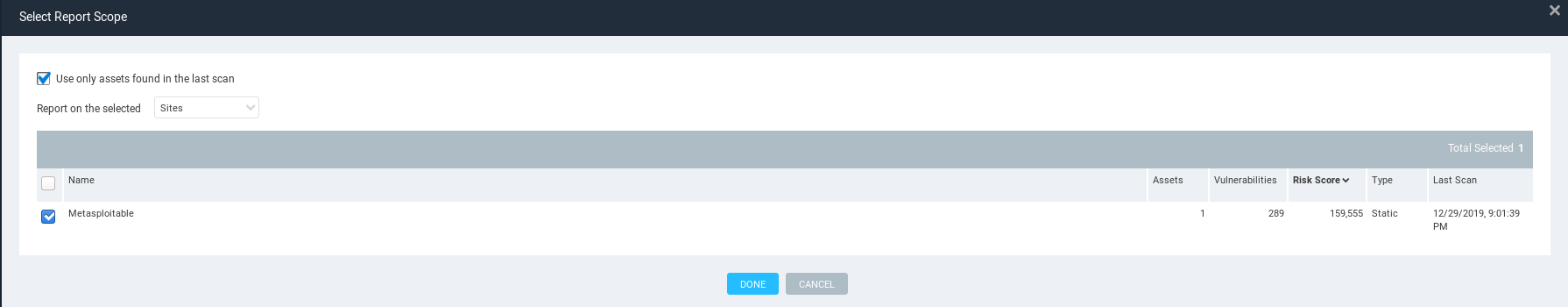
Select Report Scope
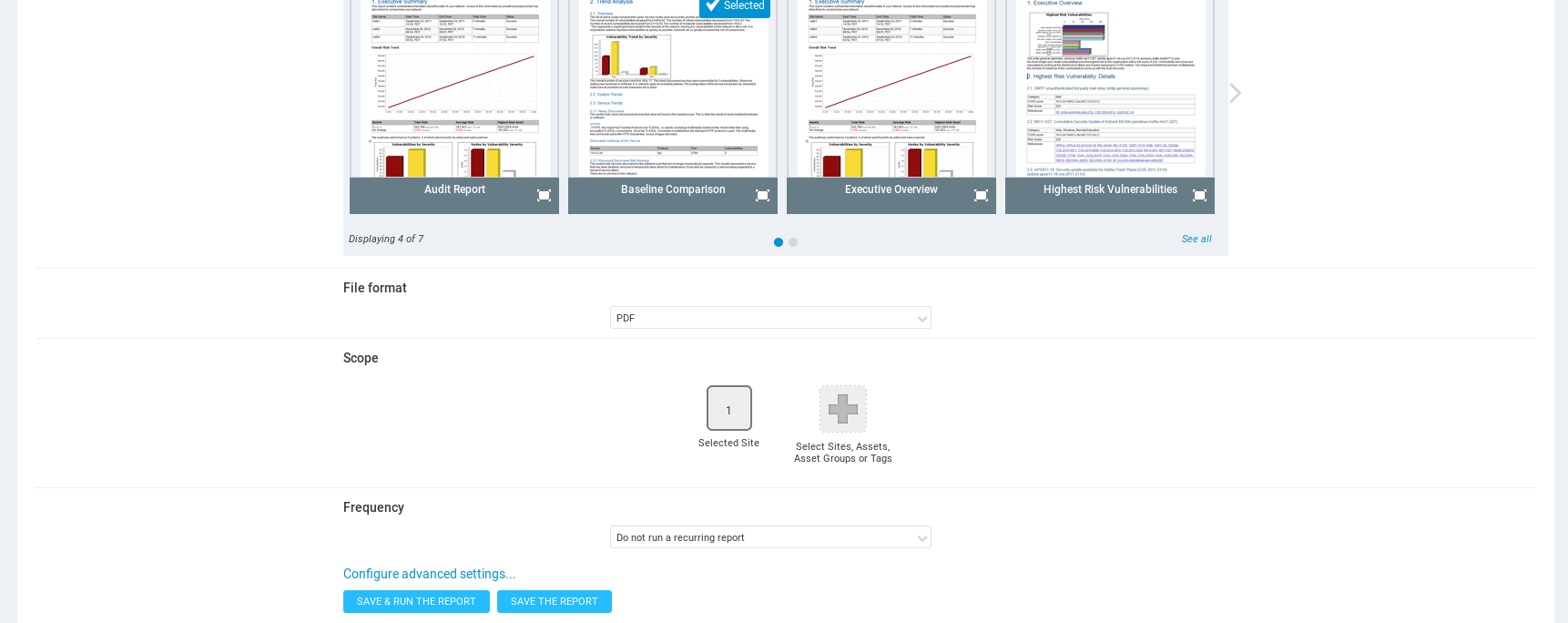
Save and run the report.
View the report result.
Ethical Hacking - GAINING ACCESS(9)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
- Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering Tool: The FAT RAT Just like Veil, it generates Undetectable ...
- Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS Backdooring ANY file Combine backdoor with any file - Generic solution. Users ar ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
随机推荐
- Laravel:No application encryption key has been specified.
其实吧,这个就是你没有生成密钥 你首先去看看,如果是刚刚下载的lavavel应该会有一个.env.example文件在根目录下,然后修改这个文件名,改成.env 然后用命令行去执行php artisa ...
- position两种绝对定位的区别
position绝对定有两种,分别为absolute和fixed 一.共同点: 1.改变行内元素的呈现方式,display被置为inline:block 2.让元素脱离普通流,不占据空间 3.默认会覆 ...
- ca78a_c++_字符串流在内存中的输入输出(速度快)
/*ca78a_c++_字符串流在内存中的输入输出**字符串流:在内存中的输入输出.(在内存中进行,速度快)**文件流 :是对文件进行输入和输出.(在磁盘里面进行)istringstream(输入), ...
- 这篇文章,我们来谈一谈Spring中的属性注入
本系列文章: 读源码,我们可以从第一行读起 你知道Spring是怎么解析配置类的吗? 配置类为什么要添加@Configuration注解? 谈谈Spring中的对象跟Bean,你知道Spring怎么创 ...
- ArrayList、Vector、LinkedList 区别及底层实现
一.ArrayList.Vector.LinkedList 三者区别 1.ArrayList 底层:是数组结构,查询快,增删慢,线程不安全,效率高.2.LinkedList底层:是链表数据结构,查询 ...
- Struts2 自定义拦截器时Action无法接收到参数
问题:自定义拦截器,没有添加defaultStack导致Action无法接受到参数 解决办法: 方法一,添加defaultStack,然后在Action中引用 自定义的stack,其实defaultS ...
- mybatis视频教程2-动态参数
/MyBatis_04_DynamicSQL/src/com/atguigu/mybatis/dao/EmployeeMapperDynamicSQL.java package com.atguigu ...
- day01---学习Mysql高级性能优化1
Mysql逻辑架构图
- 自定义Springboot全局异常类
一.简要说明 如何实现网上文章基本是随便一搜就可以很快找到, 这里不再赘述. 二.Spring-web和Spring-webmvc 通过idea查看到两个注解位于 spring-web-5.2.2.R ...
- C# 特性篇 Attributes
特性[Required] (必修的) /// <summary> /// 操作人EmpID /// </summary> [Required] public string Op ...
