Ethical Hacking - GAINING ACCESS(19)
Client-Side Attacks - Social Engineering
Tool: The FAT RAT
Just like Veil, it generates Undetectable Metasploit backdoors.
Uses a different method to evade AV programs.
Generates executable binary backdoors for:
- Windows
- Mac OS
- Linux
- Android
Install and initiate TheFatRat successfully.
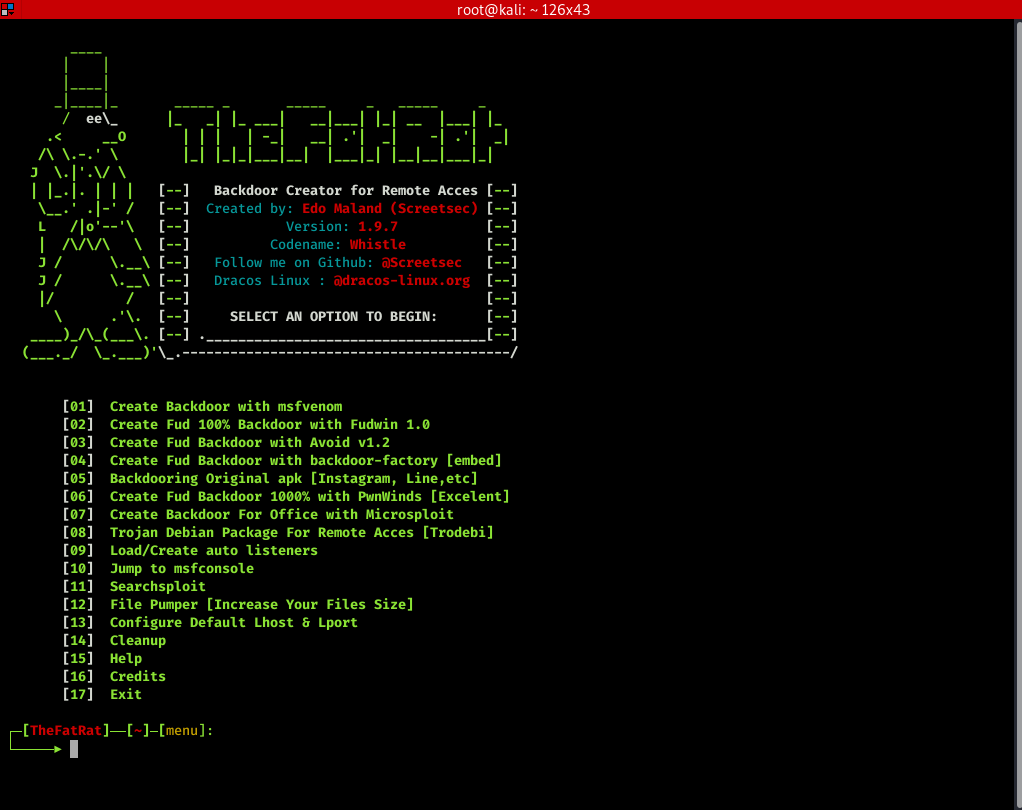
Generate a backdoor.
Ethical Hacking - GAINING ACCESS(19)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
- Ethical Hacking - GAINING ACCESS(10)
CLIENT SIDE ATTACKS Use if server-side attacks fail. If IP is probably useless. Require user interac ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
随机推荐
- pomelo 依赖分析
最新版本: 2.2.7 npm i pomelo 之后: ➜ haloServer npm i pomelonpm WARN deprecated node-uuid@1.4.0: Use uuid ...
- 一个简单的 react 实例: < TodoList >
< react TodoList: > 组件: //引入React : import React from 'react'; //组件 class TodoList exten ...
- Windows7/10实现ICMP(ping命令)
如果觉得本文如果帮到你或者你想转载都可以,只需要标注出处即可.谢谢 利用ICMP数据包.C语言实现Ping命令程序,能实现基本的Ping操作,发送ICMP回显请求报文,用于测试—个主机到只一个主机之间 ...
- Java中设置多个Access-Control-Allow-Origin跨域访问
1.如果服务端是Java开发的,添加如下设置允许跨域即可,但是这样做是允许所有域名都可以访问,不够安全. response.setHeader("Access-Control-Allow-O ...
- elasticsearch中query和filter的区别
参考博客来自: https://mp.weixin.qq.com/s/tiiveCW3W-oDIgxvlwsmXA?utm_medium=hao.caibaojian.com&utm_sour ...
- android 事件分发机制2-案例测试
我们来看程序的代码: 要求: 1.通过手指移动来拖动图片 2.控制图片不能超出屏幕显示区域 技术点: 1.MotionEvent处理 2.对View进行动态定位(layout) package im. ...
- Hibenate面试
5. 对比总结 返回值: get()返回的是查询出来的实体对象,而load()查询出来的是一个目标实体的代理对象. 查询时机: get()在调用的时候就立即发出SQL语句查询,而load()在访问非I ...
- 一条SQL删除重复记录,重复的只保留一条
情景: 我们的数据库中可能会存在很多因各种原因而重复的记录,我们需要对这些重复的记录进行删除,每组组重复的记录只保留一条就行 例如我们有这么个表:两个框框都是有重复记录的,红框和绿框都只需要留下一条, ...
- 暑假集训Day0
啊这 跟学长学的要写日记 希望到时候能写省选集训的总结 咳咳 今天上午做了一上午苦力好像让老苏夸了难以接受(年纪两百考到年级两千他居然没有干我) 上午搞卫生搞到了十点半………… 替女生拉包提东西了!! ...
- Github仓库如何选择开源许可证
Github仓库如何选择开源许可证 目录 Github仓库如何选择开源许可证 为什么需要开源许可证? 不使用开源许可证对于开发者有何影响? 不使用开源许可证对于项目的使用者有何影响? Github的开 ...
