Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER
- Discover all devices on the network.
- Display their IP address.
- Display their MAC address.
Write the Python code using the scapy.all module.
Refer to: https://scapy.readthedocs.io/en/latest/installation.html
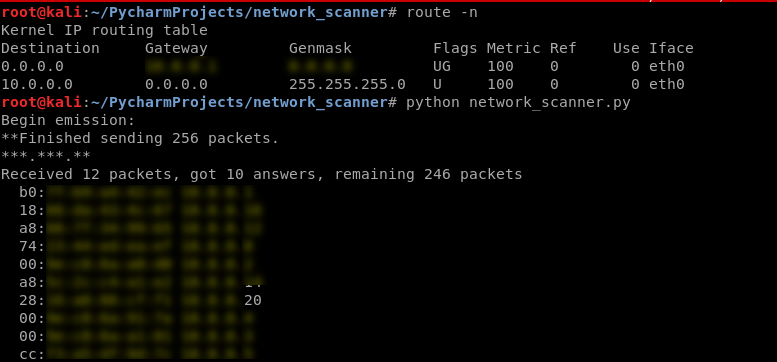
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
scapy.arping(ip) scan("10.0.0.1/24")
ALGORITHM
Goal -> Discover clients on the network.
Steps:
1. Create arp request directed to broadcast MAC asking for IP.
Two main parts:
-> Use ARP to ask who has target IP.
-> Set destination MAC to broadcast MAC.
2. Send packet and receive a response.
3. Parse the response.
4. Print result.
Use the scapy module in this program.
https://scapy.readthedocs.io/en/latest/usage.html
EX: Python Script to discover the clients on the network.
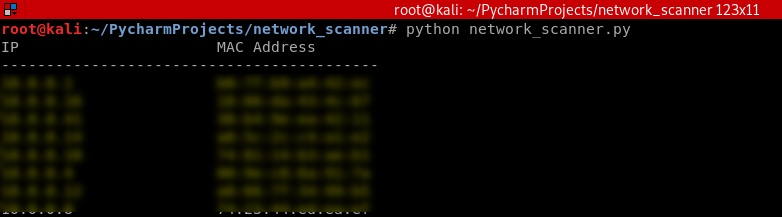
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
arp_request = scapy.ARP(pdst=ip)
broadcast = scapy.Ether(dst="ff:ff:ff:ff:ff:ff")
arp_request_broadcast = broadcast/arp_request
answered_list = scapy.srp(arp_request_broadcast, timeout=1, verbose=False)[0] print("IP\t\t\tMAC Address\n------------------------------------------")
for element in answered_list:
print(element[1].psrc + "\t\t" + element[1].hwsrc) scan("10.0.0.1/24")
Execute the script and show the result.
Python Ethical Hacking - NETWORK_SCANNER(1)的更多相关文章
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - The Lab and Needed Software
The Lab and Needed Software Attacker Machine - Kali Linux https://www.kali.org/ 1. Install the softw ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
随机推荐
- java中HashMap原理?
参考:https://www.cnblogs.com/yuanblog/p/4441017.html(推荐) https://blog.csdn.net/a745233700/article/deta ...
- 使用Docker构建企业Jenkins CI平台
在如今的互联网时代,随着软件开发复杂度的不断提高,软件开发和发布管理也越来越重要.目前已经形成一套标准的流程,最重要的组成部分就是持续集成(Continuous Integration,CI)及持续部 ...
- django 网站域名解析 IP绑定 新建站 新域名
备案成功后,我们要用域名来访问服务器,这个不仅要修改nginx的配置文件,还要设置域名的解析,下面是我的一个调试经验过程:直接上图了. 1.问题查找
- CPU明明8个核,网卡为啥拼命折腾一号核?
中断机制 我是CPU一号车间的阿Q,我又来了! 我们日常的工作就是不断执行代码指令,不过这看似简单的工作背后其实也并不轻松. 咱不能闷着头啥也不管一个劲的只管执行代码,还得和连接在主板上的其他单位打交 ...
- CentOS 6.4 安装 rar软件(tar.gz 包)并注册成功
1.下载地址: www.rarlab.com/download.htm 2.解压tar.gz文件(cd进入文件目录) # cd /home/wjshan0808/Documents # ls rarl ...
- Java 内存回收机制
当执行构造方法生成一个对象时,需要占用各种系统资源.当生成的对象不再使用时,就需要返回给操作系统,以免资源的泄露.在各种系统资源中,最常使用的就是内存.Java运行时系统通过垃圾收集周期性地释放无用对 ...
- postcss.config.js not found
https://github.com/ElemeFE/element/issues/10249
- css引入的方式有哪些_四种css的引入方式与特点
在网页中css主要负责html文档的样式显示,目前css主要有4种引入方式:行内式.内嵌式.导入式.链接式. 1.行内式 行内式也叫内联样式,是指标记的style属性中设定CSS样式,这种方式没有体现 ...
- 「疫期集训day10」玫瑰
不管我们在怎么抵抗,德国都已经败了----失守苏瓦松后绝望中的德国兵 (貌似今天的题记和内容毫无关系) 觉得以后还是不要抱怨考试失误了,感觉没啥大用 T1暴搜/状压(然俄一看题很像刚写过的二分答案,上 ...
- flex-direction和flex-wrap
当外层容器使用flex布局,并且把flex-direction设置成colum的时候,内层容器的宽度会跟外层容器的宽度保持一致. 在浏览器上的效果如下: 当把外层容器的纵向布局不适用flex-dire ...
