Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM
Goal -> Check if MAC address was changed.
Steps:
1. Execute and read ifconfig.
2. Read the mac address from the output.
3. Check if MAC in ifconfig is what the user requested.
4. Print appropriate message.
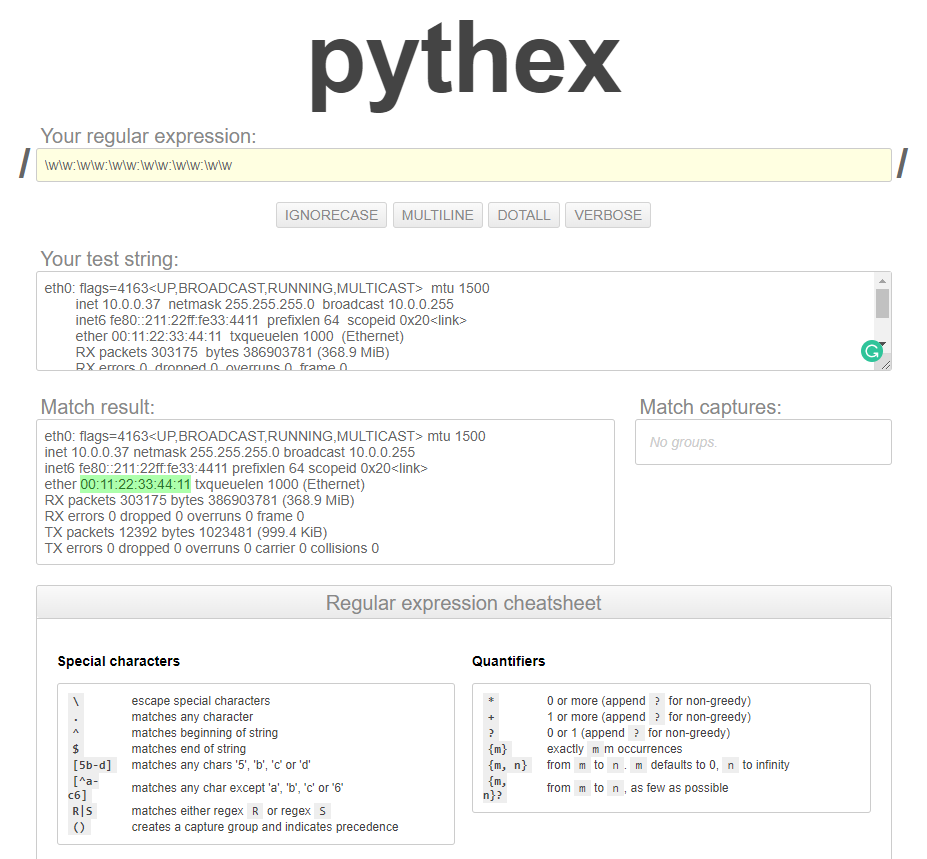
To find the MAC address, we can use the Pythex tool.
https://docs.python.org/2.7/library/re.html
https://pythex.org/?regex=%5Cw%5Cw%3A%5Cw%5Cw%3A%5Cw%5Cw%3A%5Cw%5Cw%3A%5Cw%5Cw%3A%5Cw%5Cw&test_string=eth0%3A%20flags%3D4163%3CUP%2CBROADCAST%2CRUNNING%2CMULTICAST%3E%20%20mtu%201500%0A%20%20%20%20%20%20%20%20inet%2010.0.0.37%20%20netmask%20255.255.255.0%20%20broadcast%2010.0.0.255%0A%20%20%20%20%20%20%20%20inet6%20fe80%3A%3A211%3A22ff%3Afe33%3A4411%20%20prefixlen%2064%20%20scopeid%200x20%3Clink%3E%0A%20%20%20%20%20%20%20%20ether%2000%3A11%3A22%3A33%3A44%3A11%20%20txqueuelen%201000%20%20(Ethernet)%0A%20%20%20%20%20%20%20%20RX%20packets%20303175%20%20bytes%20386903781%20(368.9%20MiB)%0A%20%20%20%20%20%20%20%20RX%20errors%200%20%20dropped%200%20%20overruns%200%20%20frame%200%0A%20%20%20%20%20%20%20%20TX%20packets%2012392%20%20bytes%201023481%20(999.4%20KiB)%0A%20%20%20%20%20%20%20%20TX%20errors%200%20%20dropped%200%20overruns%200%20%20carrier%200%20%20collisions%200%0A&ignorecase=0&multiline=0&dotall=0&verbose=0
EX: Python Code
#!/usr/bin/env python import subprocess
import optparse
import re def get_arguments():
parser = optparse.OptionParser()
parser.add_option("-i", "--interface", dest="interface", help="Interface to change its MAC address")
parser.add_option("-m", "--mac", dest="new_mac", help="New MAC address")
(options, arguments) = parser.parse_args()
if not options.interface:
parser.error("[-] Please specify an interface, use --help for more info.")
elif not options.new_mac:
parser.error("[-] Please specify a new mac, use --help for more info.")
return options def change_mac(interface, new_mac):
print("[+] Changing MAC address for " + interface + " to " + new_mac)
subprocess.call(["ifconfig", interface, "down"])
subprocess.call(["ifconfig", interface, "hw", "ether", new_mac])
subprocess.call(["ifconfig", interface, "up"]) def get_current_mac(interface):
ifconfig_result = subprocess.check_output(["ifconfig", interface])
mac_address_search_result = re.search(r"\w\w:\w\w:\w\w:\w\w:\w\w:\w\w", ifconfig_result) if mac_address_search_result:
return mac_address_search_result.group(0)
else:
print("[-] Could not read MAC address.") options = get_arguments() current_mac = get_current_mac(options.interface)
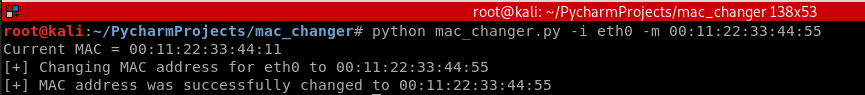
print("Current MAC = " + str(current_mac)) change_mac(options.interface, options.new_mac) current_mac = get_current_mac(options.interface)
if current_mac == options.new_mac:
print("[+] MAC address was successfully changed to " + current_mac)
else:
print("[-] MAC address did not get changed.")
Execute the following command to test the Python code:
python mac_changer.py -i eth0 -m :::::
Python Ethical Hacking - MAC Address & How to Change(3)的更多相关文章
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - BeEF Framework(1)
Browser Exploitation Framework. Allows us to launch a number of attacks on a hooked target. Targets ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(7)
Handling Errors: If the client or server crashes, the connection will be lost. Backdoor crashes if: ...
随机推荐
- IntelliJ IDEA中项目import与open的区别
场景: 从原来公司离职来到新的公司,接手公司项目,先将项目从git或svn项目版本管理上clone下来,如果项目原先是用Eclipse开发的,而你更习惯于使用IntelliJ IDEA,下面是针对使用 ...
- Mac 安装fiddler
1, 安装mono 2,下载fiddler for mac https://www.telerik.com/download/fiddler 3. 解压fiddler-mac.zip 4, cd fi ...
- Spring中的JDBC API
1 JdbcTemplate的诞生 JDBC作为Java平台访问关系数据库的标准API,其成功是有目共睹的.为了避免在JDBC API在使用中的种种尴尬局面(几乎程式一样的代码,繁琐的异常处理),Sp ...
- 工业4.0:换热站最酷设计—— Web SCADA 工业组态软件界面
前言 随着工业4.0的不断普及与发展,以及国民经济的飞速前进,我国的城市集中供热规模也不断扩大,科学的管理热力管网具有非常重大的经济和社会效益.目前热力系统,如换热站大都采用人工监控,人工监控不仅浪费 ...
- java程序员软件测试技巧
测试是开发的一个非常重要的方面,可以在很大程度上决定一个应用程序的命运.良好的测试可以在早期捕获导致应用程序崩溃的问题,但较差的测试往往总是导致故障和停机. 测试是开发的一个非常重要的方面,可以在很大 ...
- cn.arxiv.org || https://arxiv.org/xxxx 访问失败
https://arxiv.org/xxxx 访问失败解决方法问题:原论文网址::https://arxiv.org/xxxx 无法访问 解决办法:原论文网址::https://arxiv.org/+ ...
- 入门大数据---SparkSQL常用聚合函数
一.简单聚合 1.1 数据准备 // 需要导入 spark sql 内置的函数包 import org.apache.spark.sql.functions._ val spark = SparkSe ...
- Python实用笔记 (10)高级特性——生成器
通过列表生成式,我们可以直接创建一个列表.但是,受到内存限制,列表容量肯定是有限的.而且,创建一个包含100万个元素的列表,不仅占用很大的存储空间,如果我们仅仅需要访问前面几个元素,那后面绝大多数元素 ...
- Visual C++线程同步技术剖析:临界区,时间,信号量,互斥量
使线程同步 在程序中使用多线程时,一般很少有多个线程能在其生命期内进行完全独立的操作.更多的情况是一些线程进行某些处理操作,而其他的线程必须对其处理结果进行了解.正常情况下对这种处理结果的了解应当在其 ...
- 几个常见CSS错误和解决办法
1.IE6下,当float存在时,margin双倍的问题 解决方法:加display:inline; 例: #content { float: left; width: 500px; ...
