Ethical Hacking - GAINING ACCESS(18)
CLIENT SIDE ATTACKS
Backdooring ANY file
- Combine backdoor with any file - Generic solution.
- Users are more likely to run a pdf, image or audio file than an executable.
- Works well with social engineering.
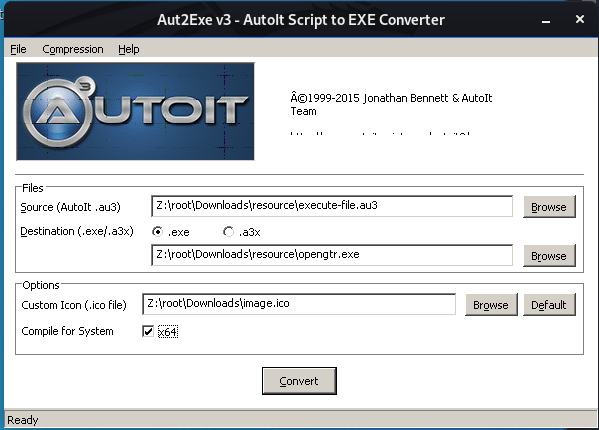
To convert the original(pdf, jpg, mp3) file to an exe, then combine it with a backdoor using veil.
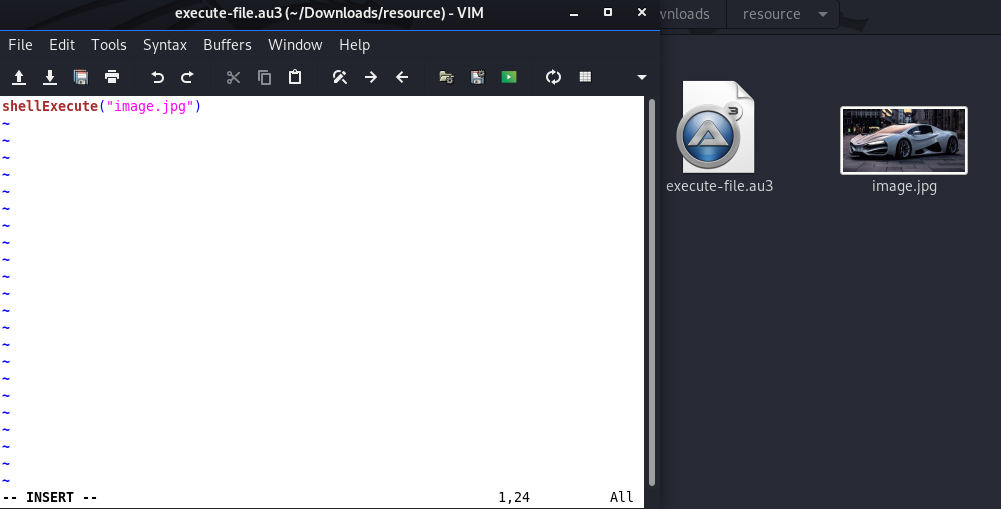
Step 1:
Step 2:
Ethical Hacking - GAINING ACCESS(18)的更多相关文章
- Ethical Hacking - GAINING ACCESS(1)
Gaining Access Introduction Everything is a computer Two main approaches (1)Server Side Do not requi ...
- Ethical Hacking - GAINING ACCESS(23)
CLIENT SIDE ATTACK - BeEF Framework Hooking targets using MITMF Tools: MITMF and BeEF Start BeEF and ...
- Ethical Hacking - GAINING ACCESS(17)
CLIENT SIDE ATTACKS - Backdooring exe' s Download an executable file first. VEIL - FRAMEWORK A backd ...
- Ethical Hacking - GAINING ACCESS(10)
CLIENT SIDE ATTACKS Use if server-side attacks fail. If IP is probably useless. Require user interac ...
- Ethical Hacking - GAINING ACCESS(6)
Server Side Attack Analysing scan results and exploiting target system. Go to the Analysis page and ...
- Ethical Hacking - GAINING ACCESS(24)
CLIENT SIDE ATTACKS - Detecting Trojan manually or using a sandbox Analyzing trojans Check the prope ...
- Ethical Hacking - GAINING ACCESS(22)
CLIENT SIDE ATTACKS - BeEf Framework Browser Exploitation Framework allowing us to launch a number o ...
- Ethical Hacking - GAINING ACCESS(21)
CLIENT SIDE ATTACKS - Trojan delivery method - using email spoofing Use gathered info to contract ta ...
- Ethical Hacking - GAINING ACCESS(20)
CLIENT SIDE ATTACKS - Spoofing backdoor extension Change the extension of the trojan from exe to a s ...
随机推荐
- Flutter学习笔记(37)--动画曲线Curves 效果
如需转载,请注明出处:Flutter学习笔记(37)--动画曲线Curves 效果
- [ C++ ] set_new_handler解析
当 operator new 中malloc返回值为0(NULL)时,表示分配内存失败(可能是因为内存不足), 此时会通过_callnewh()调用用户通过set_new_handler()设定的ne ...
- 新老单点的改造——-理解Cookie、Session、Token
近期参与了新老单点的改造,一直想总结一下,发现这篇文章比较贴切. 整理了如下: 随着交互式Web应用的兴起,像在线购物网站,需要登录的网站等等,马上就面临一个问题,那就是要管理会话,必须记住哪些人登录 ...
- 前端基础:深入浅出 TCP/IP 协议栈
一个主机的数据要经过哪些过程才能发送到对方的主机上 参考:https://www.cnblogs.com/onepixel/p/7092302.html 首先我们梳理一下每层模型的职责: 链路层:对0 ...
- Linux命令查勘进程:ps -ef |grep java
一.ps -ef |grep java 查看包含“java”的所有进程 二.涉及命令详解 ps命令将某个进程显示出来(是LINUX下最常用的也是非常强大的进程查看命令) grep命令是查找(是一种强大 ...
- 【spring boot】spring boot 拦截器
今日份代码: 1.定义拦截器 import com.alibaba.fastjson.JSON; import org.apache.commons.collections.CollectionUti ...
- 对于python 作用域新的理解
今天看Python习题,看到如下题目 def num(): return [lambda x: i*x for i in range(4)] print([m(2) for m in num()]) ...
- JavaScript学习笔记(1)
概念: 运行在浏览器端的脚本语言. 构成: ECMAScript(语法) + DOM(文档对象模型) + BOM(浏览器对象模型) 语法: 1.区分大小写 2.变量是弱类型 数据类型: string ...
- unicode键盘编码表
键盘uniCode编码 功能键: 8 ==> Backspace 9 ==> Tab 12==> Clear ...
- 每日一题 - 剑指 Offer 42. 连续子数组的最大和
题目信息 时间: 2019-06-30 题目链接:Leetcode tag: 动态规划 难易程度:简单 题目描述: 输入一个整型数组,数组里有正数也有负数.数组中的一个或连续多个整数组成一个子数组.求 ...
