Python Ethical Hacking - TROJANS Analysis(3)
BYPASSING ANTI-VIRUS PROGRAMS
AV programs detect viruses based on:
1. Code - compare files to huge databases of signatures.
->Use own code, obfuscation, useless operations, encode, pack ...etc
2. Behaviour - run a file in a sandbox and analyze it.
-> Run trusted operations before evil code.
->Delay execution of evil code.
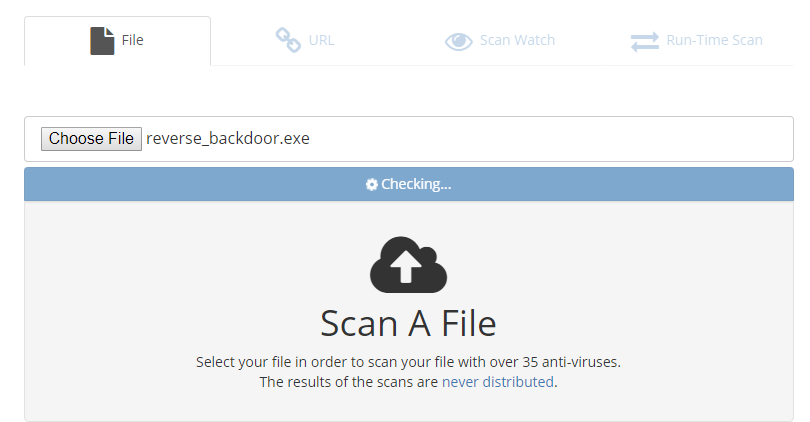
Scan the file on the following website:
NoDistribute - Online Virus Scanner Without Result Distribution
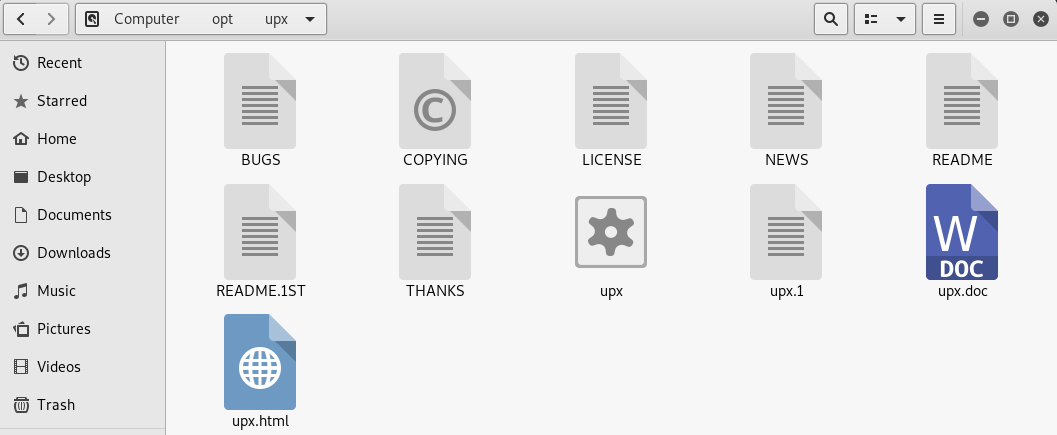
Using UPX to Package the executable program.
Download the file from https://github.com/upx/upx/releases/download/v3.95/upx-3.95-amd64_linux.tar.xz.
And extract to the /opt folder.
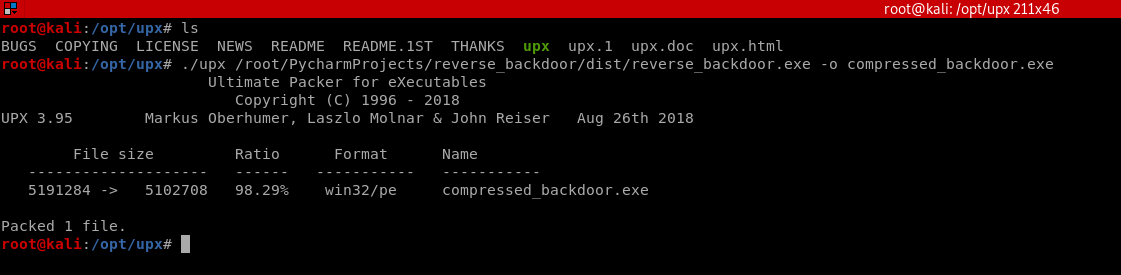
Compress the evil file through UPX.
./upx /root/PycharmProjects/reverse_backdoor/dist/reverse_backdoor.exe -o compressed_backdoor.exe
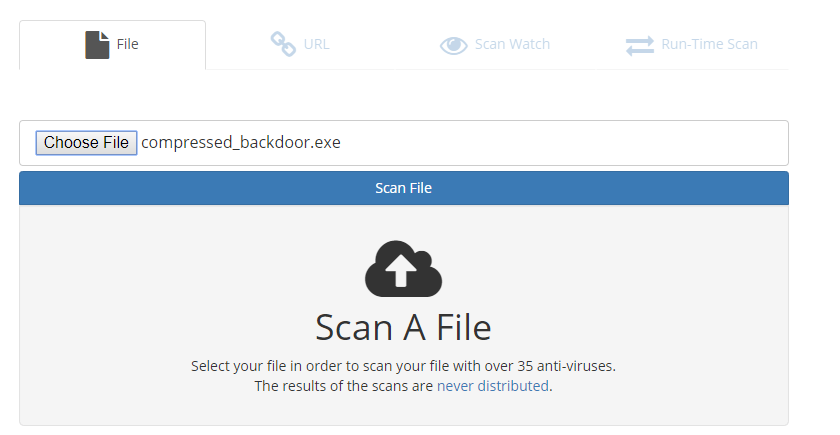
Scan the compressed_backdoor.exe file, the result is a little better.
Take your file Unique and delay to execute the evil code to let the AV program think your program is harmless.
Python Ethical Hacking - TROJANS Analysis(3)的更多相关文章
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(5)
Spoofing File Extention - A trick. Use the Kali Linux Program - Characters 1. Open the program. 2. F ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- arduino连接12864LCD方法
arduino连接12864LCD方法,参考相关代码. https://blog.csdn.net/txwtech/article/details/95038386
- Python在Linux下编译安装
[准备环境] Linux centos [前言] 1 linux下默认带Python,带的是2.7版本的 ,如果需要升级版本,需要把系统的自带的Python改名或者卸载,再次安装你所需要的Python ...
- C/C++以及Linux文件操作备忘录
目录 C文件操作 文件开关 文件读写 C++文件操作 Linux文件操作 打开 C文件操作 #include<stdio.h> stdin, stdout, stderr 文件开关 /* ...
- ArrayList、Vector、LinkedList 区别及底层实现
一.ArrayList.Vector.LinkedList 三者区别 1.ArrayList 底层:是数组结构,查询快,增删慢,线程不安全,效率高.2.LinkedList底层:是链表数据结构,查询 ...
- springboot集成jpa操作mybatis数据库
数据库如下 CREATE TABLE `jpa`.`Untitled` ( `cust_id` bigint() NOT NULL AUTO_INCREMENT, `cust_address` var ...
- JS中style.display和style.visibility的区别
在JS中可以通过设置style.display或者style.visibility属性来控制元素是否显示,在style.display=block和style.visibility=visible的时 ...
- Kubernetes 两步验证 - 使用 Serverless 实现动态准入控制
作者:CODING - 王炜 1. 背景 如果对 Kubernetes 集群安全特别关注,那么我们可能想要实现这些需求: 如何实现 Kubernetes 集群的两步验证,除了集群凭据,还需要提供一次性 ...
- SpringBoot2.x入门:快速创建一个SpringBoot应用
前提 这篇文章是<SpringBoot2.x入门>专辑的第2篇文章,使用的SpringBoot版本为2.3.1.RELEASE,JDK版本为1.8. 常规的套路会建议使用Spring官方提 ...
- java实现在一个字符串中查找某个子字符串出现的次数
public static void main(String[] args) { String a = "我爱我的祖国!!!"; String b = "爱"; ...
- CSS三种布局模型是什么?
在网页中,元素有三种布局模型:流动模型(Flow) 默认的.浮动模型 (Float).层模型(Layer).下面我们来看一下这三种布局模型. 三种布局模型介绍: 1.流动模型(Flow) 流动(Flo ...
