Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER
- Discover all devices on the network.
- Display their IP address.
- Display their MAC address.
Write the Python code using the scapy.all module.
Refer to: https://scapy.readthedocs.io/en/latest/installation.html
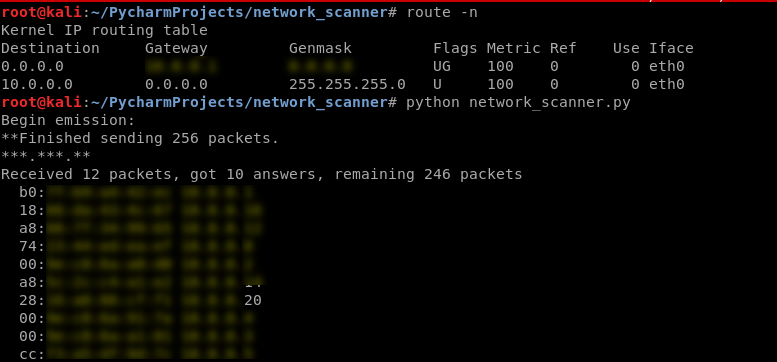
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
scapy.arping(ip) scan("10.0.0.1/24")
ALGORITHM
Goal -> Discover clients on the network.
Steps:
1. Create arp request directed to broadcast MAC asking for IP.
Two main parts:
-> Use ARP to ask who has target IP.
-> Set destination MAC to broadcast MAC.
2. Send packet and receive a response.
3. Parse the response.
4. Print result.
Use the scapy module in this program.
https://scapy.readthedocs.io/en/latest/usage.html
EX: Python Script to discover the clients on the network.
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
arp_request = scapy.ARP(pdst=ip)
broadcast = scapy.Ether(dst="ff:ff:ff:ff:ff:ff")
arp_request_broadcast = broadcast/arp_request
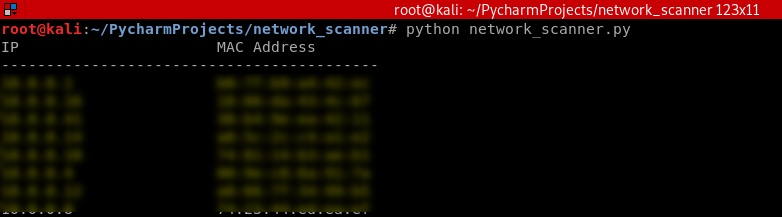
answered_list = scapy.srp(arp_request_broadcast, timeout=1, verbose=False)[0] print("IP\t\t\tMAC Address\n------------------------------------------")
for element in answered_list:
print(element[1].psrc + "\t\t" + element[1].hwsrc) scan("10.0.0.1/24")
Execute the script and show the result.
Python Ethical Hacking - NETWORK_SCANNER(1)的更多相关文章
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - The Lab and Needed Software
The Lab and Needed Software Attacker Machine - Kali Linux https://www.kali.org/ 1. Install the softw ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
随机推荐
- JavaWeb网上图书商城完整项目--day02-24.分类模块的相关类创建
所谓的分类模块:就是显示所有的分类的功能,显示所有的分类在left.jsp页面中 这就是显示所有的分类: 要实现上面的,我们首先创建一个分类模块,该模块需要实现下面的功能 我们先创建上面的java包 ...
- Springboot 集成 ElasticSearch 踩坑
这里只涉及到基础使用 导包 <dependency> <groupId>org.springframework.boot</groupId> <artifac ...
- C#数据结构与算法系列(二十):插入排序算法(InsertSort)
1.介绍 插入排序算法属于内部排序算法,是对于欲排序的元素以插入的方式找寻该元素的适当位置,以达到排序的目的 2.思想 插入排序(Insertion Sorting)的基本思想是:把n个待排序的元素看 ...
- SELinux已经允许,为什么日志显示的仍然是denied?
从日志可以看到,SELinux的Mode已经修改位了permissive = 1,也就是允许模式,但它前面的日志仍然显示的是“denied".本来我还以为是自己哪里没弄好导致的这个问题,但访 ...
- Solaris 11.4安装,映像包管理系统(IPS)搭建
文章目录 1.下载地址 2. IPS安装准备 2.1 repo包 2.1 install-repo.ksh 2.2 校验文本 3. Solaris系统安装 3.1 虚拟机软件 3.2 安装os 3.3 ...
- 第三方登陆---GITEE
第三方登陆QQ通行入口 https://www.cnblogs.com/Yangbuyi/p/13194007.html 呼~~~~ 应身边的同学要集成第三方登陆 gitee.github.qq登陆. ...
- 不花钱搞定PDF编辑难题
PDF格式是专为显示而设计的格式,并不容易被编辑,市面上并没有一款可以真正免费使用的PDF编辑器. 不花钱搞定PDF编辑难题的办法: 1.免费使用PDF编辑器+去水印:免费版的PDF编辑器不是会加水印 ...
- 美国6w刀的远程工作高级工程师职位,说下在线评估, 倒在第一阶段, 认知能力测试?智商不够怎么办?!
前几天刚被裁员了, 然后在Linkedin上面看到一个crossover的senior software engineer的职位,写的可以remote, 6w刀, 我第一次参加这个公司的这种在线测试, ...
- 每日一题 - 剑指 Offer 36. 二叉搜索树与双向链表
题目信息 时间: 2019-06-29 题目链接:Leetcode tag: 二叉搜索树 中序遍历 递归 深度优先搜索 难易程度:中等 题目描述: 输入一棵二叉搜索树,将该二叉搜索树转换成一个排序的循 ...
- JIT的Profile神器JITWatch
简介 老是使用命令行工具在现代化社会好像已经跟不上节奏了,尤其是在做JIT分析时,使用LogCompilation输出的日志实在是太大了,让人望而生畏.有没有什么更加简便的方法来分析JIT日志呢?快来 ...
