Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your:
- Network
- Layer 2 interfaces and VLAN interfaces
- Layer 3 interfaces
- Tap interfaces
- Loopback and tunnel interfaces
- HA interfaces
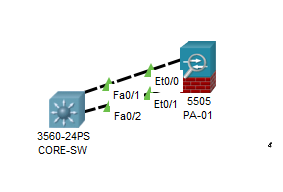
Type 1 - Layer 2 interfaces:
- Allows a Trunk interface to transmit
- Tagged VLAN's which can be assigned to VLAN interfaces
- Can be allocated in port channels (link aggregation with LACP)

Configure a Layer2 interface with Wired-VLAN20.
Add a layer2 subinterface.
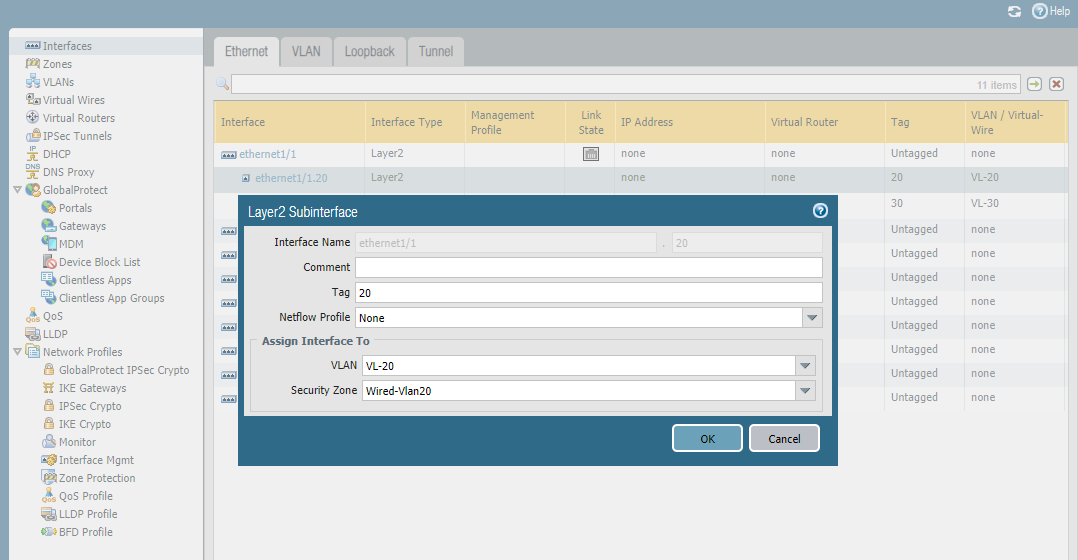
Add a Wireless-VLAN30 subinterface.

Type2 - Layer 3 interfaces:
- Carries end-to-end Layer 3 traffic with an assigned IP address.
- Can be allocated in port channels(link aggregation with LACP)
- Can be sub-divided in L3 Subinterfaces.
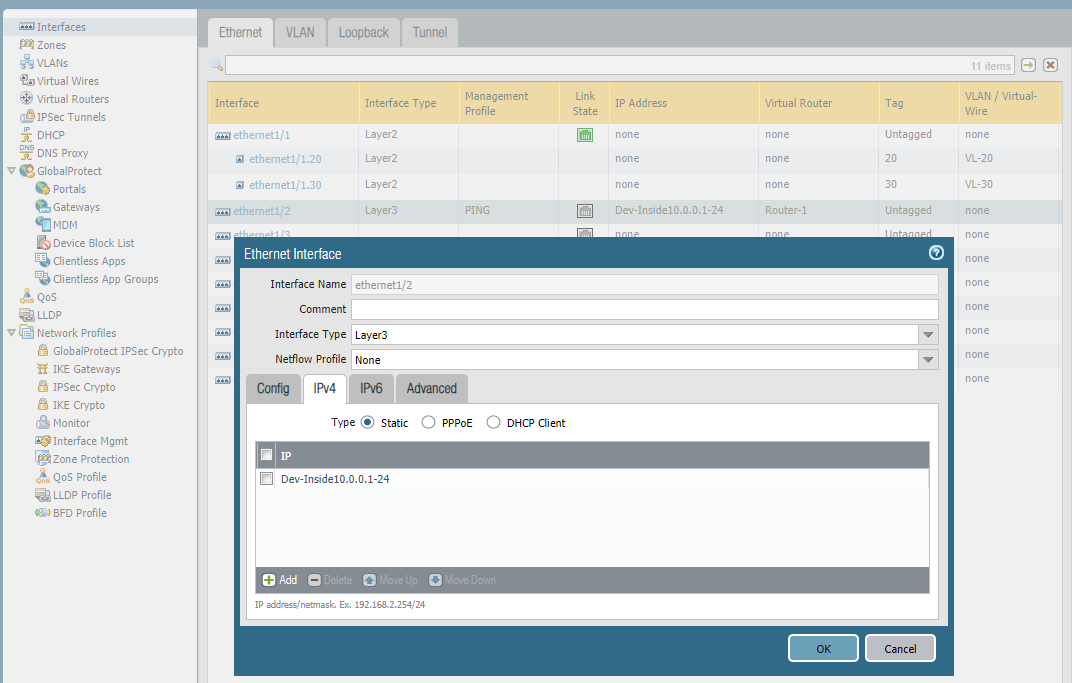
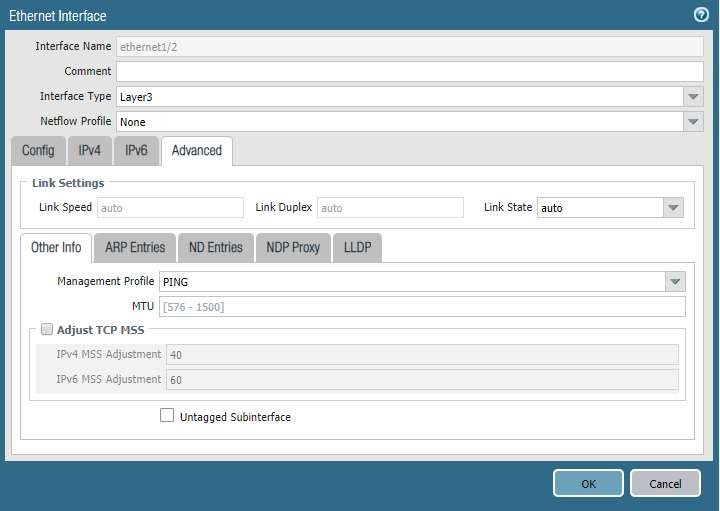
Add a layer3 interface.

Type3 - Tunnel and loopback interfaces:
- Used to logically assign attributes to tunnel entry/exit points
- Loopbacks: Create always-on logical interfaces for required applications.
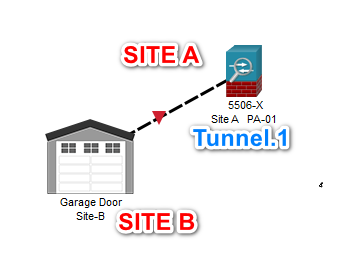
Configure a tunnel.
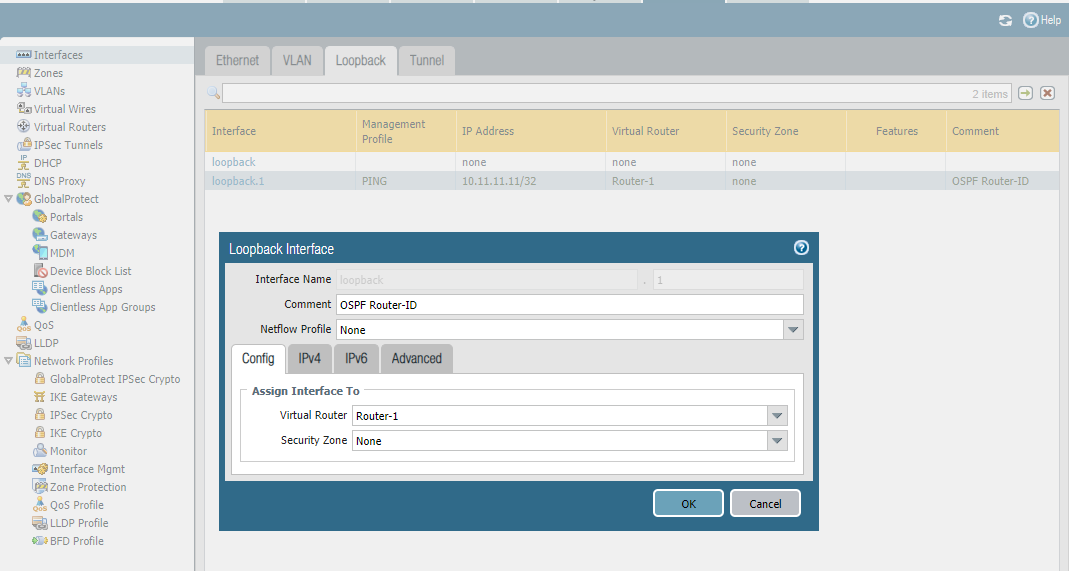
Confiture Loopback


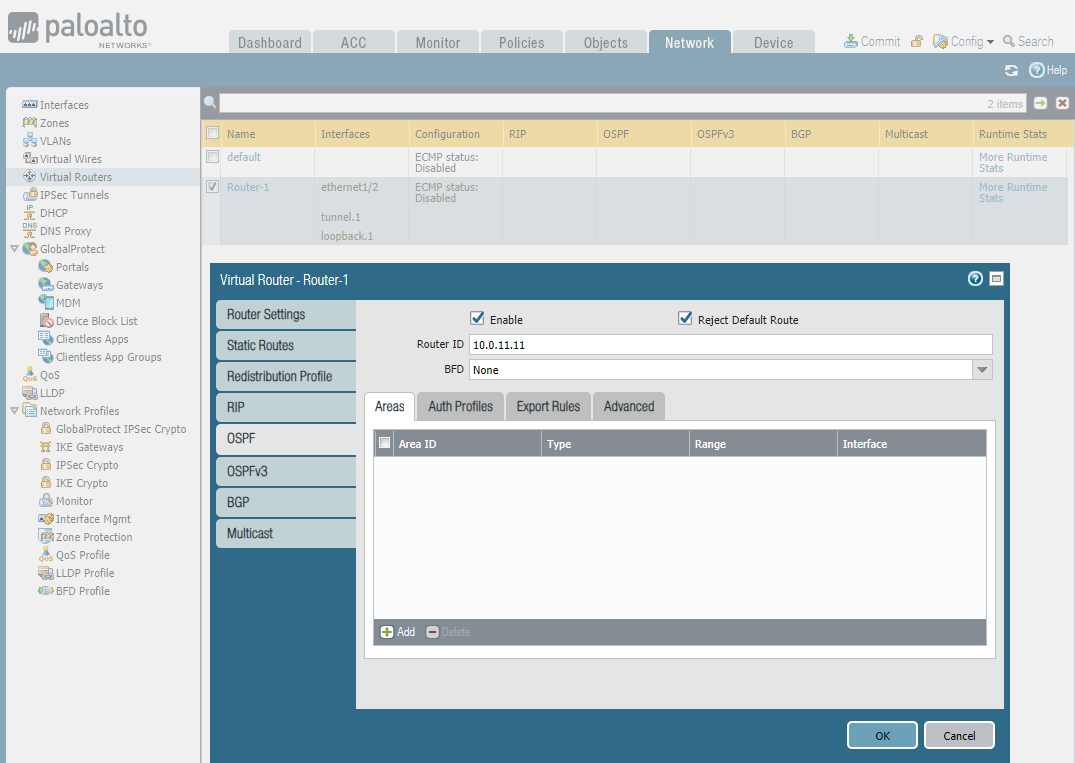
Configure Virtual Router
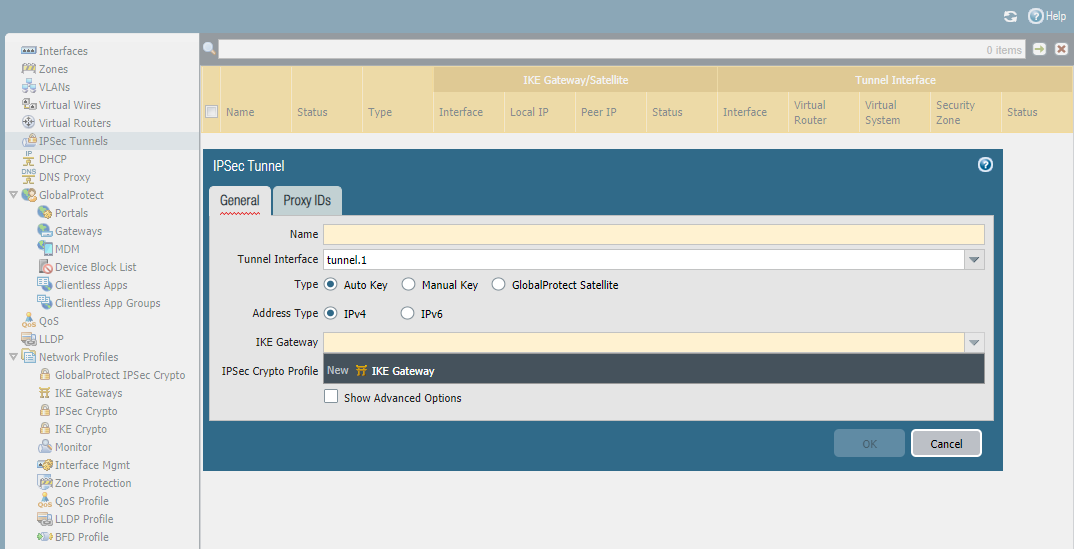
Configure IPsec Tunnels here.
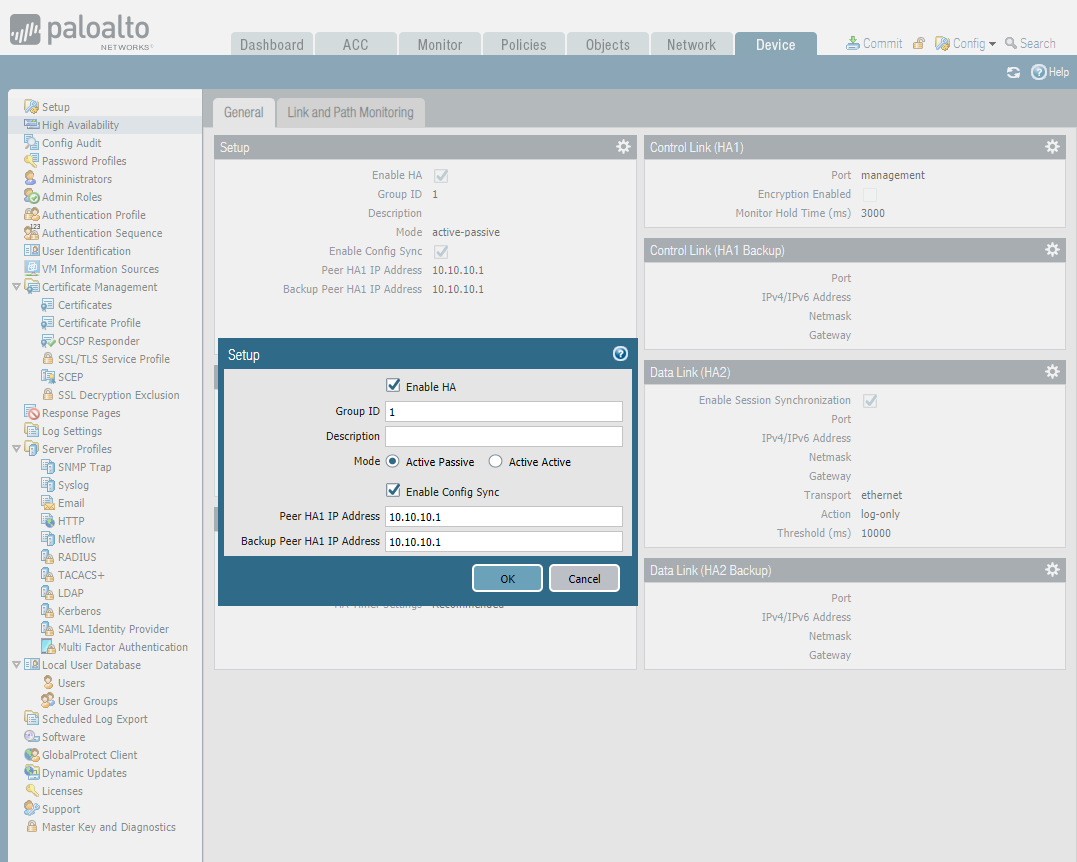
Typer 4 - HA(High availability interfaces):
- Allows connectively between two Palo Alto Firewalls to establish a highly available Firewall setup
- HA links will carry required information to build the cluster, and sync routing/configuration across the members.

Configure HA interface.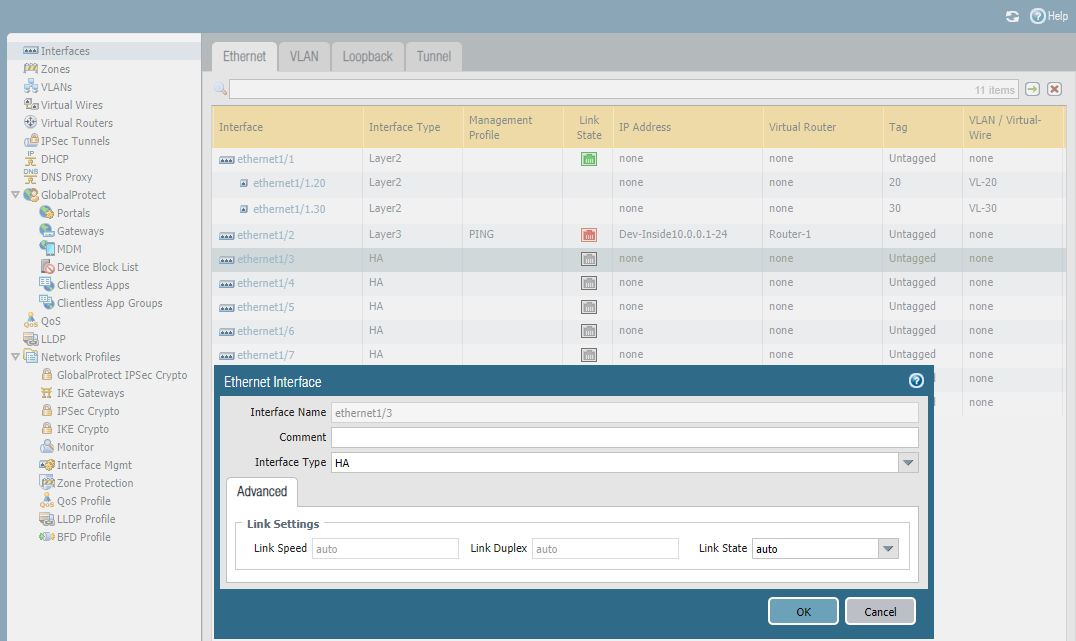
Enable HA setup.
Configure the Control Link.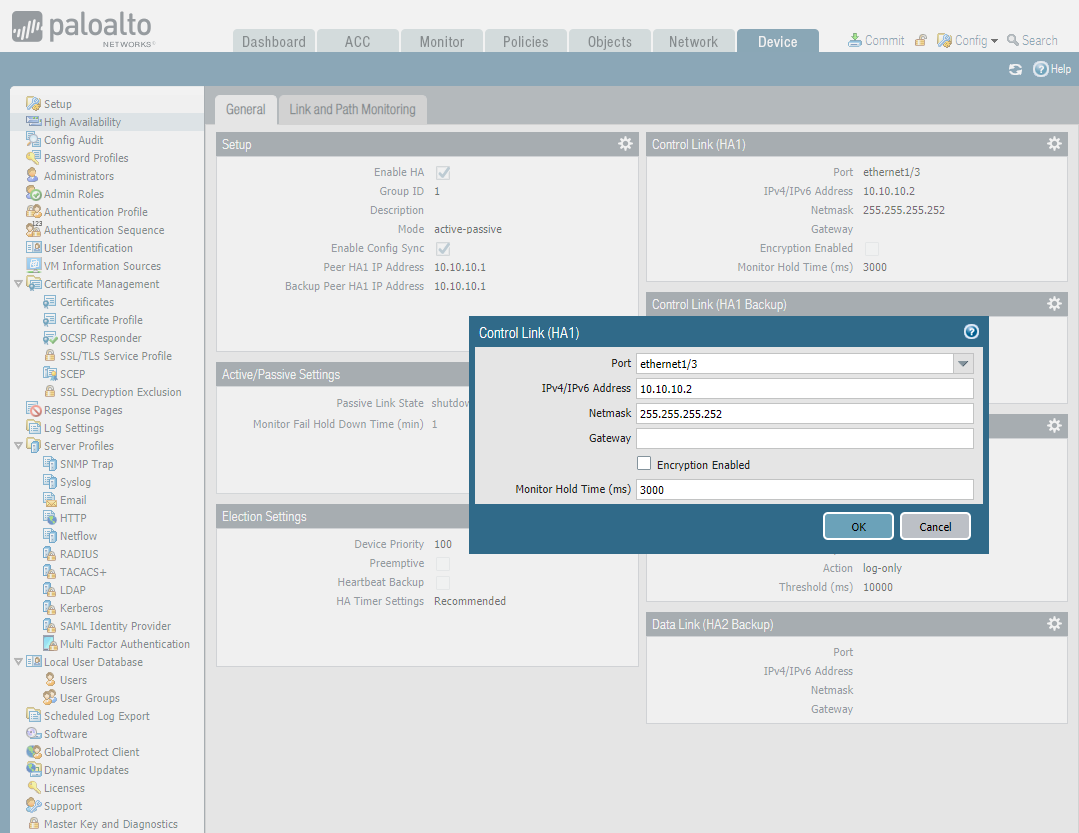
Cyber Security - Palo Alto Firewall Interface Types的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- Android笔记布局资源文件
在项目的res--layout目录下的文件叫布局资源文件,用于控制页面的布局显示 在Java代码中引用布局资源我们已经很熟悉了. setContentView(R.layout.activity_ma ...
- python基础内容整理(一)
基本数据类型 字符串 String 字符串是不可变类型 字符串的分割: s.split(sep)以给定的sep为分隔符对s进行分割. In [4]: s = "hello world&quo ...
- 使用ssh连接数据库时出现Permission denied, please try again.解决方案
安装ssh(如果已经安装则会覆盖)sudo apt-get install openssh-server找到/etc/ssh/sshd_config这个文件 将permitrootlogin的值设置为 ...
- Windows 程序设计(4) MFC 03 -系列学习
本文整体目录和绝大部门内容来自 [鸡啄米网站]的MFC系列文章,欢迎支持原创 (一)VS2010/MFC编程入门之前言 VC++全称是Visual C++,是由微软提供的C++开发工具,它与C++的根 ...
- 八张图彻底了解JDK8 GC调优秘籍-附PDF下载
目录 简介 分代垃圾回收器的内存结构 JDK8中可用的GC 打印GC信息 内存调整参数 Thread配置 通用GC参数 CMS GC G1参数 总结 简介 JVM的参数有很多很多,根据我的统计JDK8 ...
- java scoket Blocking 阻塞IO socket通信二
在上面一节中,服务端收到客户端的连接之后,都是new一个新的线程来处理客户端发送的请求,每次new 一个线程比较耗费系统资源,如果100万个客户端,我们就要创建100万个线程,相当的 耗费系统的资源, ...
- Pikachu靶场SQL注入刷题记录
数字型注入 0x01 burp抓包,发送至repeater 后面加and 1=1,and 1=2 可判断存在注入 0x02 通过order by判断字段数,order by 2 和order by 3 ...
- SDL软件安全读书笔记(一)
# 如何应对当前的全球网络安全威胁? 开发安全漏洞尽可能少的软件,应该着眼于源头安全. 边界安全盒深度防御是重要的安全手段,但软件自身的安全是安全防护的第一关. 即使软件源头存在较少的漏洞,这些漏洞也 ...
- MySQL一招入门
连接mysql数据库命令:mysql -u root -p 创建mysql数据库:create databaase xx库; 创建mysql表: create table db_xx表( id int ...
- Python-数据结构-最全六种排序代码实现
1.冒泡排序 def bubble_sort(alist): """冒泡排序""" n = len(alist) for j in rang ...
