TCAM and CAM memory usage inside networking devices(转)
TCAM and CAM memory usage inside networking devices Valter Popeskic Equipment and tools, Physical layer, Routing, Switching 8 Comments
As this is networking blog I will focus mostly on the usage of CAM and TCAM memory in routers and switches. I will explain TCAM role in router prefix lookup process and switch mac address table lookup.
However, when we talk about this specific topic, most of you will ask: how is this memory made from architectural aspect?
How is it made in order to have the capability of making lookups faster than any other hardware or software solution? That is the reason for the second part of the article where I will try to explain in short how are the most usual TCAM memory build to have the capabilities they have.
CAM AND TCAM MEMORY
When using TCAM – Ternary Content Addressable Memory inside routers it’s used for faster address lookup that enables fast routing.
In switches CAM – Content Addressable Memory is used for building and lookup of mac address table that enables L2 forwarding decisions. By implementing router prefix lookup in TCAM, we are moving process of Forwarding Information Base lookup from software to hardware.
When we implement TCAM we enable the address search process not to depend on the number of prefix entries because TCAM main characteristic is that it is able to search all its entries in parallel. It means that no matter how many address prefixes are stored in TCAM, router will find the longest prefix match in one iteration. It’s magic, right?
CEF Lookup
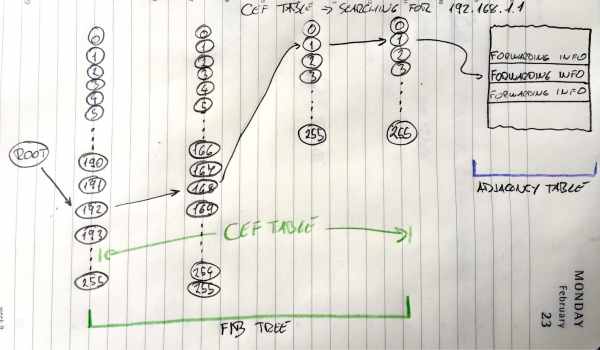
Image 1 shows how FIB lookup functions and points to an entry in the adjacency table. Search process goes through all entries in TCAM table in one iteration.
ROUTER
In routers, like High-End Cisco ones, TCAM is used to enable CEF – Cisco Express Forwarding in hardware. CEF is building FIB table from RIB table (Routing table) and Adjacency table from ARP table for building pre-prepared L2 headers for every next-hop neighbour.
TCAM finds, in one try, every destination prefix inside FIB. Every prefix in FIB points to adjacency table’s pre-prepared L2 header for every outgoing interface. Router glues the header to packet in question and send it out that interface. It seems fast to do it that way? It is fast!
SWITCH
In Layer 2 world of switches, CAM memory is most used as it enables the switch to build and lookup MAC address tables. MAC address is always unique and so CAM architecture and ability to search for only exact matches is perfect for MAC address lookup. That gives the switch ability to go over all MAC addresses of all host connected to all ports in one iteration and resolve where to send received packets.
CAM is so perfect here as the architecture of CAM provides the result of two kinds 0 or 1. So then we make the lookup on CAM table it will only get us with true (1) result if we searched for the exact same bits. L2 forwarding decisions are the one using this fast magical electronics!
MORE THAN PLAIN ROUTING AND SWITCHING
Besides Longest-Prefix Matching, TCAM in today’s Routers and Multilayer Switch devices are used to store ACL, QoS and other things from upper-layer processing. TCAM architecture and the ability of fast lookup enables us to implement Access-Lists without an impact on router/switch performance.
Devices with this ability mostly have more TCAM memory modules in order to implement Access-List in both directions and QoS at the same time at the same port without any performance impact. All those different functions and their lookup process towards a decision is made in parallel.
MORE ON TCAM
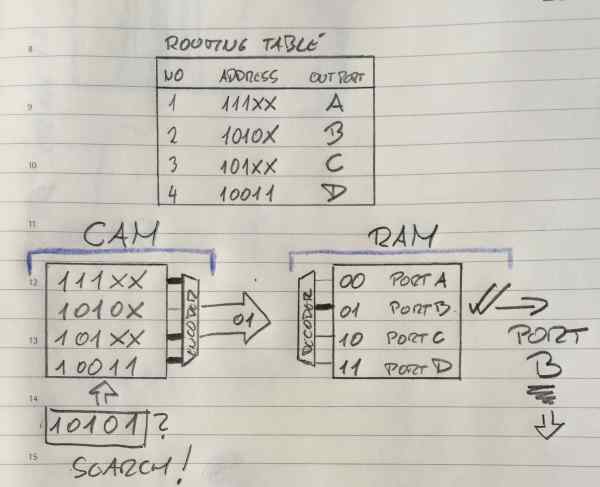
TCAM is basically a special version of CAM constructed for rapid table lookups. Not mentioned before, TCAM can get Us with three different results when doing lookups: 0, 1, and X (I don’t care state).
With this strange third state, TCAM is perfect for building and searching tables for stored longest matches in IP routing tables.
There is just one condition that IP prefixes need to be sorted before they are stored in TCAM so that longest prefixes are on upper position with higher priority (lower address location) in a table. This enables us to always select the longest prefix from given results an thus enables Longest-Prefix Matching.
TCAM ARCHITECTURE
In the Image 2 here below I showed, (please disregard my style), one of the simplest CEF Explanations I could find in scientific articles around. It is basically showing you usage of FIB on the left and Adjacency table on the right. FIB stored in TCAM table and Adjacency table stored in RAM memory. Great, it shows without words what we spoked about before in “ROUTER” section.
TCAM FIB
Image 2 FIB implemented in TCAM, adjacency table implemented in RAM
Ok, Here you must know that IP addresses in the example are smaller that real ones. Here we have addresses of 5 bits not 32 like IPv4, all other is the same as the real stuff.
We are looking on the left side now at the CAM part, it is basically explained for TCAM.
So in TCAM world in order to get the longest match like in the Image 2 above here, before populating the TCAM we need to sort the entries so that longer prefixes are always situated on higher priority places. As the lookup goes from top downwards it means that higher priority is higher in the table, closer to the top. OK, now that we solved this it is easy to see that TCAM here is searching in parallel from left to right all four address entries.
Entries here in TCAM are numbered 00,01,02,03 from top to bottom. Not like in Routing table above where they are numbered 1,2,3,4. Don’t let that confuse you.
Second and third entry (01 and 02 entry) are the same as the one we search in first three bits. When it comes to the fourth bit, he is “X” for entry 02.
X means don’t care or the third possible solution that can come out of TCAM table query. In the situation above, if we look at the second and third line of TCAM table, this search will make a match for both of entries. The fourth bit of “01” is matched and the fifth bit does not care. For “02” it will show true value at the encoder entrance as a fourth and fifth place do not care!
Based on the priority order from above, line “01” is the longest-prefix match and it is selected and send to encoder who will link that entry to Adjacency table entry for making the packet L2 ready. Remember, on this image, “01” is sent to Adjacency table as a pointer. It is pointing to Adjacency table entry 01 which will then be used use for this packet creation.
L2 header will be added to that packet and the packet will be sent out on port B to the neighbour.
TCAM PARALLEL SEARCH PROCESS INSIDE CIRCUITRY
Actually with CAM and TCAM chips the logic is slightly different that you might think.
For all entries that are matching the searched one, encoder entry will get “true” signal, and all not matched entries will show “false” output, no problems there. The catch is in the beginning of the process. Before search begins all entries when entered inside TCAM are closing the circuitry on TCAM word entry and show “true” at encoder side. All entries are temporarily in the match state. When parallel search is done it will brake all entries that have at least one bit that does not match the searched entry.
Here is the explanation of the “don’t care bit”, in the search process when the search gets to X bit (“don’t care bit”) it will not change the state of that matchline. That’s why No 2 and No3 lines made a match, and that’s why TCAM is perfect for longest-prefix lookup.
This also explains why TCAM memory is so power hungry. It needs to power on all circuits to be able to make a search not only the matched ones. Limited memory space and power consumption associated with a large amount of parallel active circuitry are the main issues with TCAM.
If we look at the right side of the Image 2 now, we see that adjacency table is built in RAM memory. Adjacency table uses ARP table and Routing table data for building pre-prepared L2 headers for every next-hop neighbour. As described before in “Router” section it will prepare the packet to be sent to Layer 1 and out the interface in a flash. Entries need to keep L2 data and this data does not change often. RAM memory is consequently perfect fit for adjacency table. Quick, not expensive, not space limited and not so power hungry.
TCAM and CAM memory usage inside networking devices(转)的更多相关文章
- GPU Memory Usage占满而GPU-Util却为0的调试
最近使用github上的一个开源项目训练基于CNN的翻译模型,使用THEANO_FLAGS='floatX=float32,device=gpu2,lib.cnmem=1' python run_nn ...
- Shell script for logging cpu and memory usage of a Linux process
Shell script for logging cpu and memory usage of a Linux process http://www.unix.com/shell-programmi ...
- 5 commands to check memory usage on Linux
Memory Usage On linux, there are commands for almost everything, because the gui might not be always ...
- SHELL:Find Memory Usage In Linux (统计每个程序内存使用情况)
转载一个shell统计linux系统中每个程序的内存使用情况,因为内存结构非常复杂,不一定100%精确,此shell可以在Ghub上下载. [root@db231 ~]# ./memstat.sh P ...
- Why does the memory usage increase when I redeploy a web application?
That is because your web application has a memory leak. A common issue are "PermGen" memor ...
- Reducing and Profiling GPU Memory Usage in Keras with TensorFlow Backend
keras 自适应分配显存 & 清理不用的变量释放 GPU 显存 Intro Are you running out of GPU memory when using keras or ten ...
- 【转】C++ Incorrect Memory Usage and Corrupted Memory(模拟C++程序内存使用崩溃问题)
http://www.bogotobogo.com/cplusplus/CppCrashDebuggingMemoryLeak.php Incorrect Memory Usage and Corru ...
- Memory usage of a Java process java Xms Xmx Xmn
http://www.oracle.com/technetwork/java/javase/memleaks-137499.html 3.1 Meaning of OutOfMemoryError O ...
- Redis: Reducing Memory Usage
High Level Tips for Redis Most of Stream-Framework's users start out with Redis and eventually move ...
- detect data races The cost of race detection varies by program, but for a typical program, memory usage may increase by 5-10x and execution time by 2-20x.
小结: 1. conflicting access 2.性能危害 优化 The cost of race detection varies by program, but for a typical ...
随机推荐
- vulnhub靶场之VENOM: 1
准备: 攻击机:虚拟机kali.本机win10. 靶机:Venom: 1,下载地址:https://download.vulnhub.com/venom/venom.zip,下载后直接vbox打开即可 ...
- ubuntu apt 安装最新版 nodejs
使用最新版本, 当前是 16.x 的版本. 这里我使用了 LTS 版本. curl -fsSL https://deb.nodesource.com/setup_current.x | sudo -E ...
- springcloud11 spring cloud config
1.spring cloud config是什么 官网:https://cloud.spring.io/spring-cloud-static/spring-cloud-config/2.2.1.RE ...
- WAF Bypass 介绍与实战
前言 WAF是英文"Web Application Firewall"的缩写,中文意思是"Web应用防火墙",也称为"网站应用级入侵防御系统" ...
- Could not execute query ---> MySql.Data.MySqlClient.MySqlException: You have an error in your SQL sy
1.出现问题 执行sql查询时出现如题错误,原因是安装mysql-connector-net的版本过高,当前项目在用的mysql版本不符合:关于当前安装的mysql-connector-net版本的查 ...
- StatisticalOutlierRemoval:离群点移除
1.简介 StatisticalOutlierRemoval滤波器主要用于剔除离群点,或则测量误差导致的粗差点. 滤波思想为:对每一个点的邻域进行一个统计分析,计算它到所有临*点的*均距离.假设得到的 ...
- 列表(list)内置方法补充、字典(dict)内置方法、元组(tuple)内置方法、集合(set)内置方法
目录 一.列表(list)内置方法补充 二.字典(dict)内置方法 三.元组(tuple)内置方法 四.集合(set)内置方法 一.列表(list)内置方法补充 # reverse()颠倒列表内元素 ...
- 修改安卓ID为硬件唯一ID
前言: 最近接到个需求,我们新产品上的外包侧APP需要使用硬件唯一ID(不管怎么升级怎么操作,ID始终不变和硬件绑定),用来做权限校验. 由于了解到安卓ID或序列号都会在擦除升级后重新随机生成,所以这 ...
- LG P4148 简单题
\(\text{Code}\) #include <cstdio> #include <iostream> #include <algorithm> #define ...
- JZOJ 3213. 【SDOI2013】直径
题目 思路 树的直径很好求,两遍 \(dfs\),记下两个端点 然后很显然所有直径经过的边必然在我们求出的这条直线上 那么我们只要判断一下一条直径上的边是不是答案 假设当前边为 \(i\) 那么把 \ ...
