Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks
Sophisticated attacks that can be used after connecting to the target AP.
Gathering Information
Now that we are connected to a specific AP, we can gather more detailed info about the clients connected to this AP. There is a number of programs that can be used to do this, we shall talk about 3 programs starting with the simplest and quickest one.
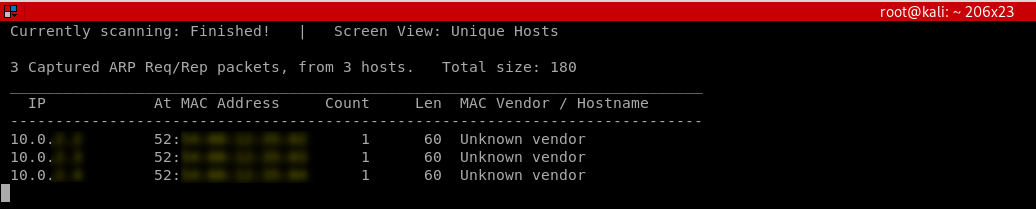
· Netdiscover
Netdiscover is a program that can be used to discover the connected clients to our current network, it's very quick but it does not show detailed information about the clients: IP, MAC address and some times the hardware manufacturer for the client's wireless card.
netdiscover -i [INTERFACE] -r [RANGE]
Netdiscover 0.5.1 [Active/passive ARP reconnaissance tool]
Written by: Jaime Penalba <jpenalbae@gmail.com>
Usage: netdiscover [-i device] [-r range | -l file | -p] [-m file] [-F filter] [-s time] [-c count] [-n node] [-dfPLNS]
-i device: your network device
-r range: scan a given range instead of auto scan. 192.168.6.0/24,/16,/8
-l file: scan the list of ranges contained into the given file
-p passive mode: do not send anything, only sniff
-m file: scan a list of known MACs and host names
-F filter: customize pcap filter expression (default: "arp")
-s time: time to sleep between each ARP request (milliseconds)
-c count: number of times to send each ARP request (for nets with packet loss)
-n node: last source IP octet used for scanning (from 2 to 253)
-d ignore home config files for autoscan and fast mode
-f enable fastmode scan, saves a lot of time, recommended for auto
-P print results in a format suitable for parsing by another program and stop after active scan
-L similar to -P but continue listening after the active scan is completed
-N Do not print header. Only valid when -P or -L is enabled.
-S enable sleep time suppression between each request (hardcore mode)
If -r, -l or -p are not enabled, netdiscover will scan for common LAN addresses.
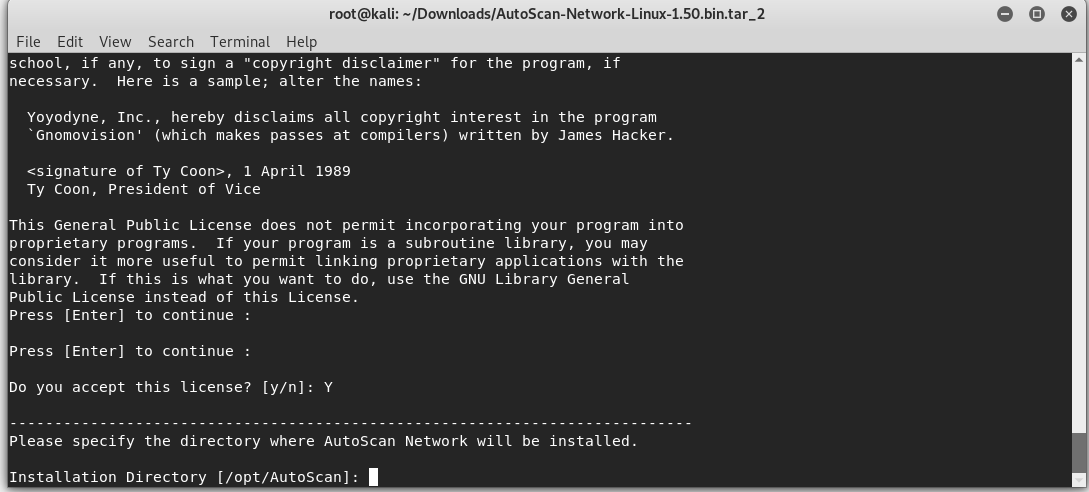
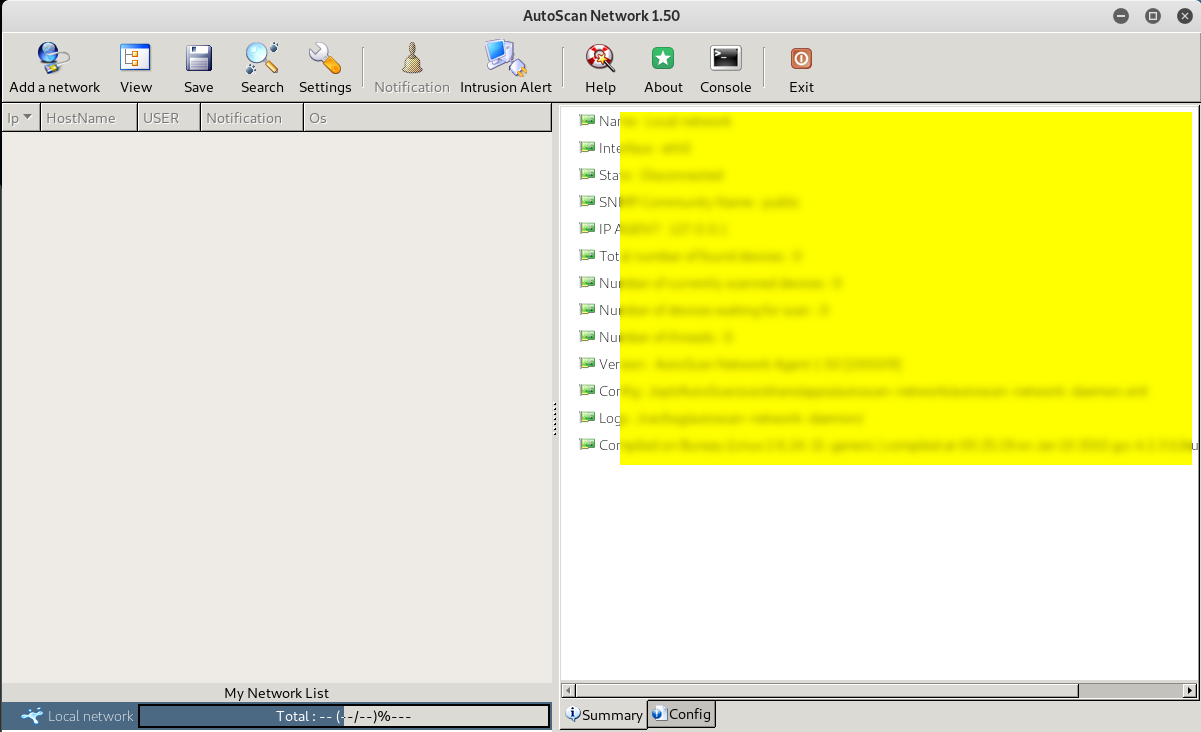
· Autoscan
Autoscan is another program that can be used to discover the connected clients to our current network, it's not as quick as netdiscover, but it shows more detailed information about the connected devices and it has a graphical user interface.
Download autoscan from: https://sourceforge.net/projects/autoscan/files/AutoScan/autoscan-network%201.50/AutoScan-Network-1.50.pkg.zip/download
-> Install autoscan

->Chose the installation directory
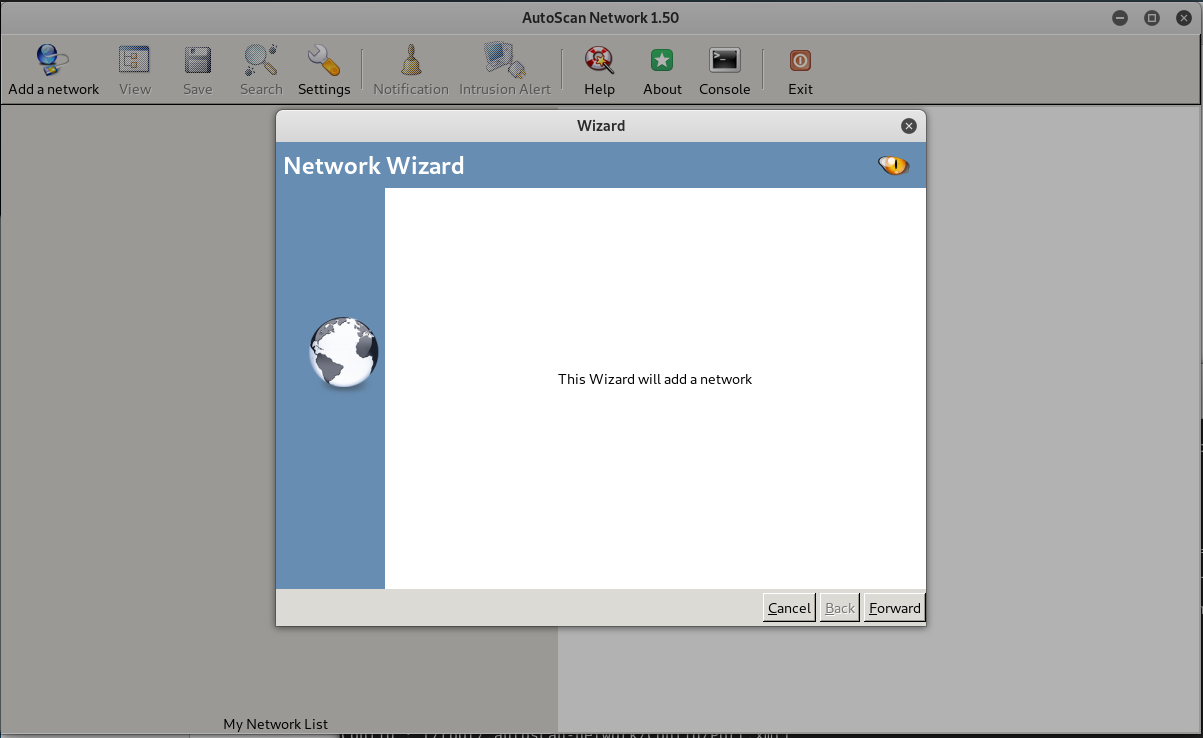
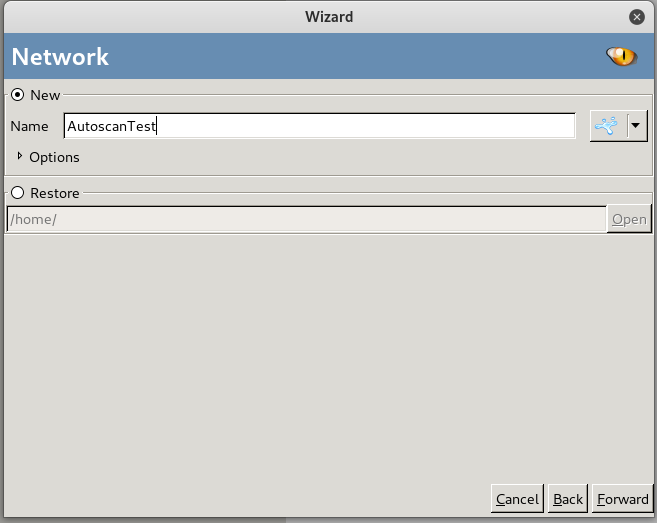
->Complete the installation and set the Network Wizard.

Ethical Hacking - NETWORK PENETRATION TESTING(12)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- 面试问Redis集群,被虐的不行了......
哨兵主要针对单节点故障无法自动恢复的解决方案,集群主要针对单节点容量.并发问题.线性可扩展性的解决方案.本文使用官方提供的redis cluster.文末有你们想要的设置ssh背景哦! 本文主要围绕如 ...
- 使用git畅游代码的海洋
如果把互联网上的纷繁代码比作一片海洋,那么git就是在这片海洋上航行的船只,正所谓“水可载舟,亦可覆舟”,git使用恰当可以远征星辰,不然可能会坠入无穷无尽的代码海洋无法自拔.书回正传,我们的征途是星 ...
- SpringCloud教程第2篇:Ribbon(F版本)
一.ribbon简介 Spring cloud有两种服务调用方式,一种是ribbon+restTemplate,另一种是feign.在这一篇文章首先讲解下基于ribbon+rest. ribbon是一 ...
- springcloud2.0 添加配置中心遇到的坑
新手入门,在springcloud 配置config的时候遇到了几个比较烦的坑 先说1.5x版本的一些配置吧 首先是端点暴露的方式 management: security: enabled: fal ...
- Python 分布式缓存之Reids数据类型操作
目录 1.Redis API 2.String 操作 3.Hash 操作 4.List 操作 1.Redis API 1.操作模式 redis-py提供两个类Redis和StrictRedis用于实现 ...
- IDEA 使用jebel热部署插件启动失败
在使用Jebel热部署插件开发springmvc时,启动会出现内存溢出错误.可在配置Tomcat时增加JVM参数解决. -Xms768m -Xmx768m -XX:PermSize=64M -XX:M ...
- python文件处理-将图像根据坐标切割成若干小图
代码涉及到:遍历目标路径,选取csv后缀的文件,遍历csv每一行,读取坐标,用cv操作图片 # !/usr/bin/python # -*- coding: UTF- -*- import panda ...
- 三.接收并处理请求参数与QueryDict对象
一.get与post请求:重点看传参与接收参数 GET请求与传参 ---->url后面跟上?k1=v1&&k2=v2 POST请求与数据提交 (1)get请求:如直接在浏览 ...
- 写给.NET开发者的Python教程(一):C# vs Python: 语言特性、Conda和Jupyter Notebook环境
承接上篇,本文会从语言特性.开发环境和必备工具来带领大家进入Python的世界. 语言特性 首先一起看下C#和Python在语言特性层面的对比,他们作为截然不同的两类面向对象高级语言,在语言层面上有何 ...
- Lost connection to MYSQL server at 'reading for initial communication packet'
这个异常,是我在对外开放了本地数据库端口后,测试能否连接上数据库时候出现的问题: 解决步骤: 1.services.msc打开服务窗口,重启mysql,进行重试,还不行: 2.对数据库进行操作 USE ...
