Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups
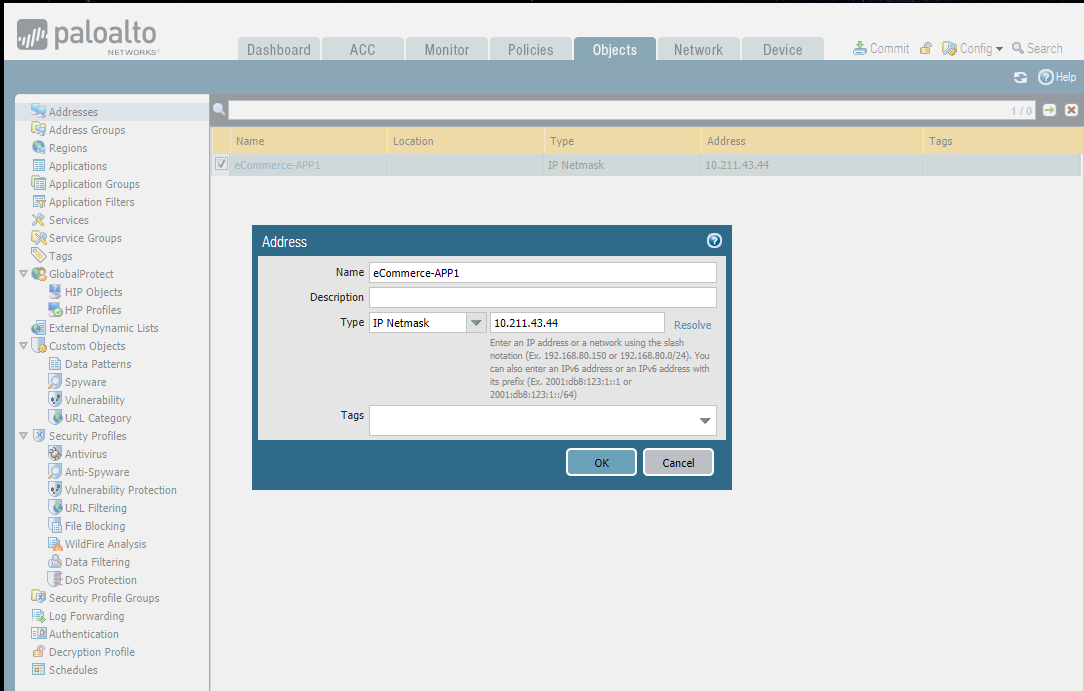
- Creating address objects.
- Organizing address objects with address groups
- Limiting the human error and complexity thanks to address groups.

Add a new address:
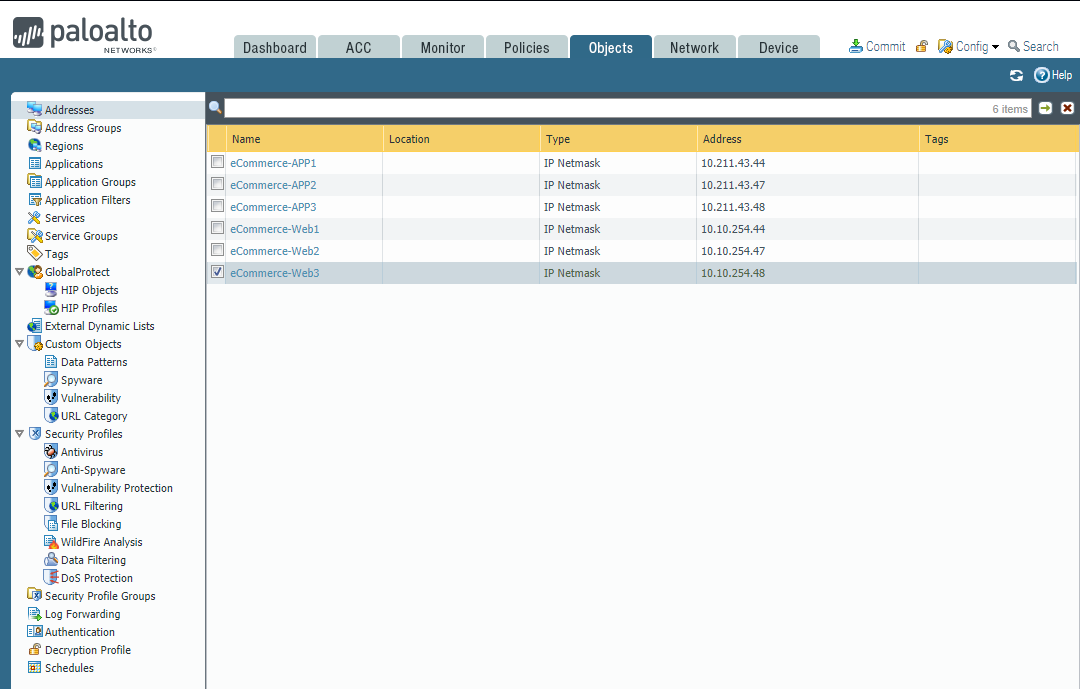
Add new Address Groups:


Service Objects and Groups
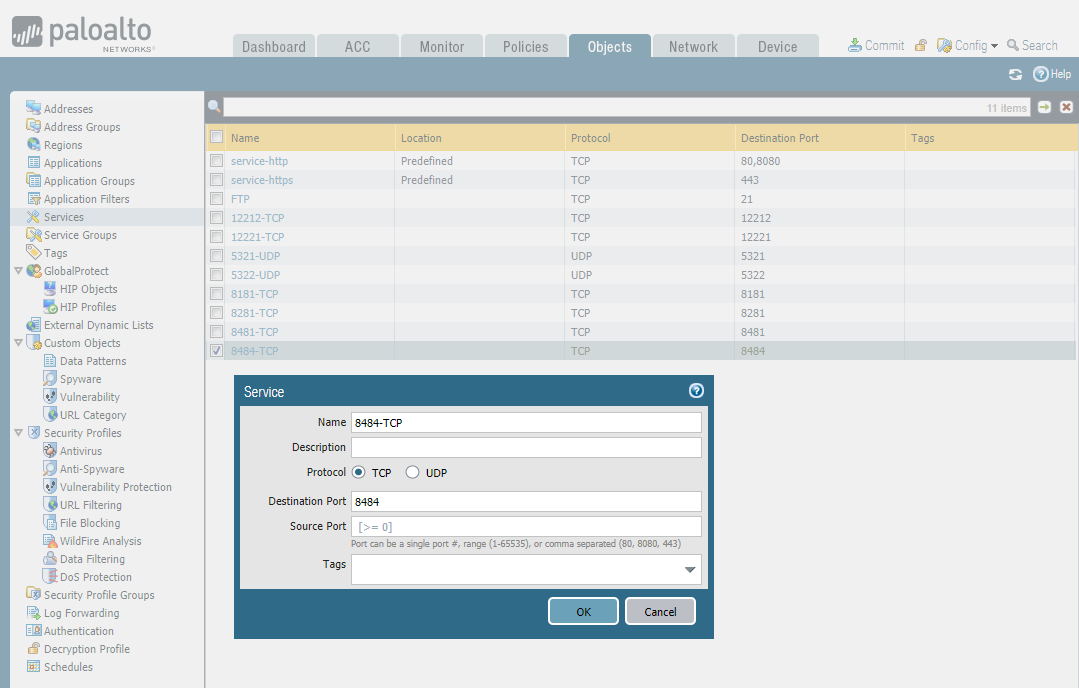
- Creating service objects.
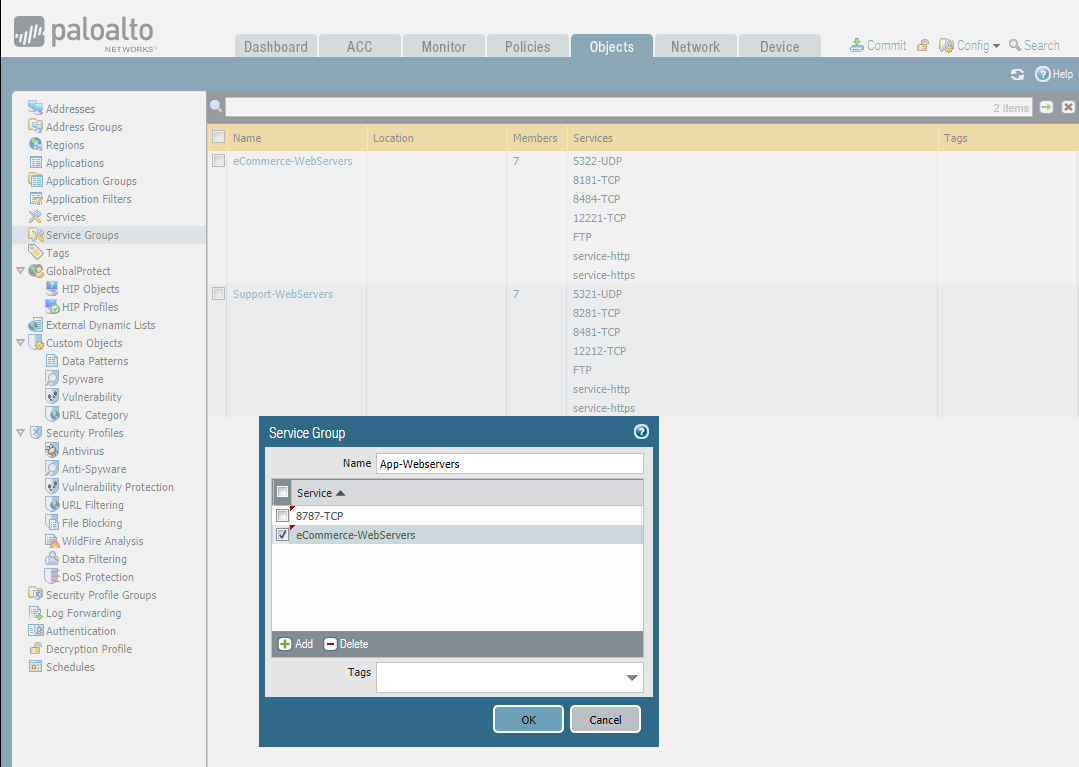
- Organizing service objects with service groups
- Using service groups to avoid long and complex security policy tables.
Add services:
Add Service Groups:
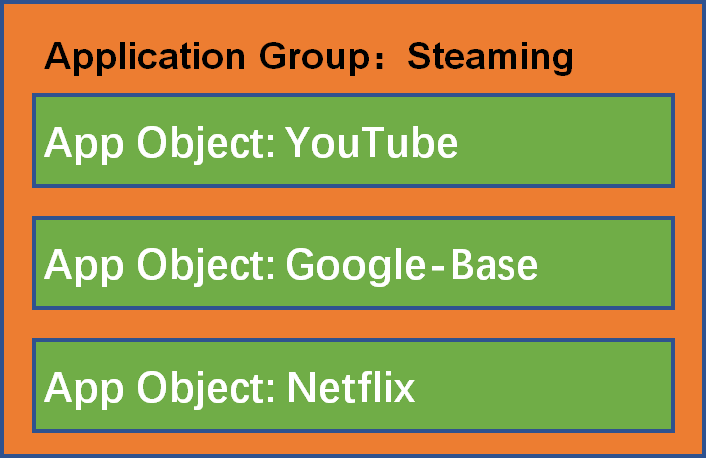
Application Objects and Groups
- Creating application objects.
- Classify application objects in groups.
Add applications:
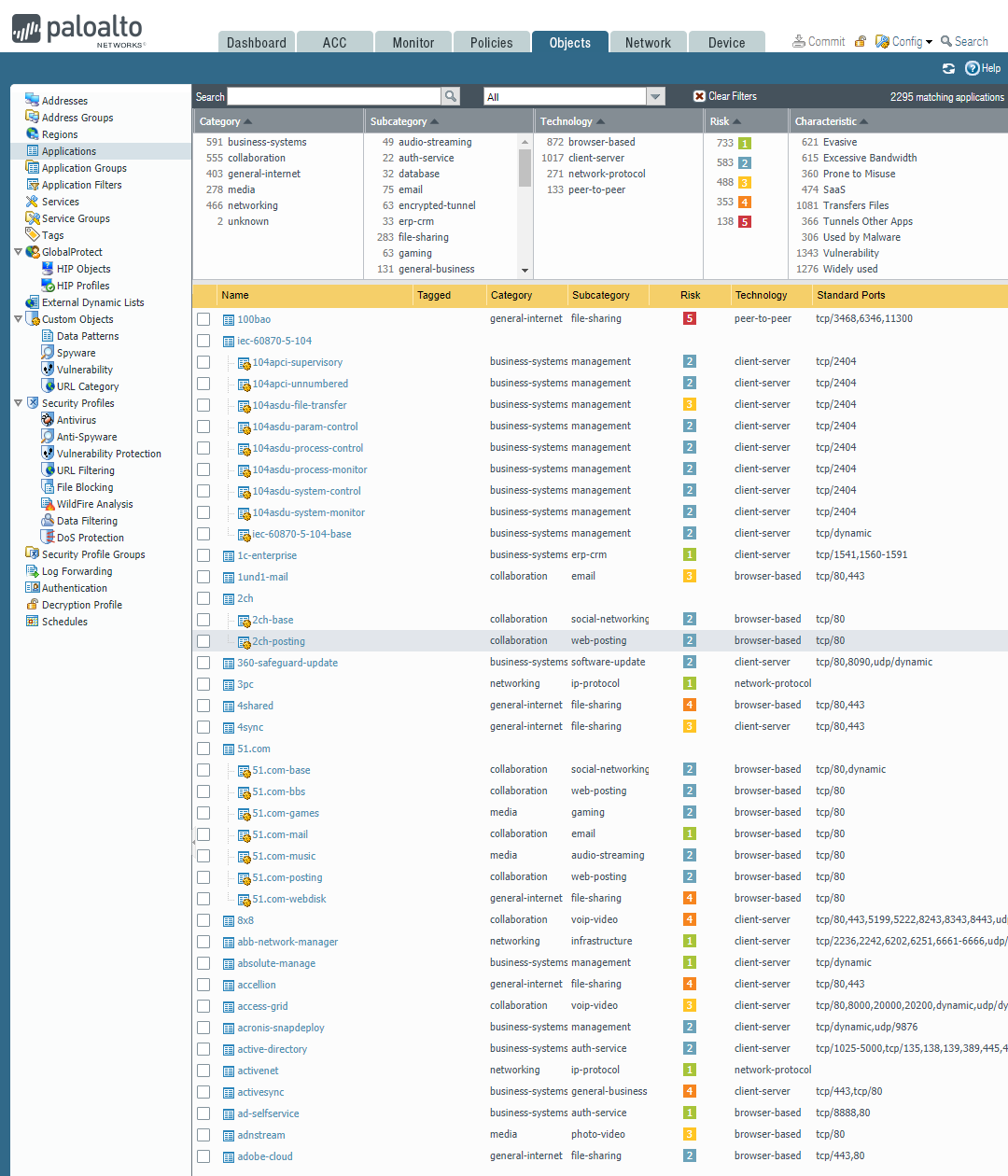
Add a new Clinical system:



Add a new application group:
Search the PAN Application Research Center before adding an application group. Identifying any required dependencies when applying application-specific rules and taking advantage of Palo Alto's application portal. https://applipedia.paloaltonetworks.com/

Then add the Youtube-Group.

Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- 【01JMeter基础】测试计划
测试计划 整个脚本的集合根目录,所有线程组集合的承载,可以添加线程组.测试片段.非测试元件.配置元件.监听器.定时器.前置/后置处理起器.断言等 一.用户自定义变量 可以使用在所有的线程组中,通过${ ...
- 后渗透工具Empire使用教程
一.前言 Empire是一个PowerShell后期漏洞利用代理工具同时也是一款很强大的后渗透测神器,它建立在密码学.安全通信和灵活的架构之上.Empire实现了无需powershell.exe就可运 ...
- idea的maven项目无法引入junit类
本机:java版本:1.8 pom中是junit版本:4.12 出现问题:在使用@Test 无法引入 : org.junit.Test; 解决方法:junit在pom.xml改为 4.12-beta- ...
- layer.open弹框中的表单数据无法获取
layer.open弹框中的表单数据无法获取 表单数据模板 layer.open() 页面效果: 当点击确定后,radio和textarea获取的值总是为空,解决办法: var setPriCustB ...
- 计算机网络之DNS协议
DNS( Domain Name System)是“域名系统”的英文缩写,是一种组织成域层次结构的计算机和网络服务命名系统,它用于TCP/IP网络,它所提供的服务是用来将主机名和域名转换为IP地址的工 ...
- c语言二维数组的转置
#include <stdio.h> #include <string.h> #include <stdlib.h> #define maxsize 3 #defi ...
- 自定义Springboot全局异常类
一.简要说明 如何实现网上文章基本是随便一搜就可以很快找到, 这里不再赘述. 二.Spring-web和Spring-webmvc 通过idea查看到两个注解位于 spring-web-5.2.2.R ...
- git和github入门指南(1)
1.git和github简介 1.1.git是什么?github是什么?git和github的关系? Git是一个开源的分布式版本控制系统,可以有效.高速地处理从很小到非常大的项目版本管理. Git ...
- POJ 3463 Sightseeing 【最短路与次短路】
题目 Tour operator Your Personal Holiday organises guided bus trips across the Benelux. Every day the ...
- JasperReport报表中输出Excel时,部分列不显示的问题
JasperReport开源报表功能强大,是我们WEB系统中做报表开发的一个强有力的工具,上手也比较简单.我碰到的问题是进行报表输出时,在html网页中显示正常,但如果导出为Excel时,部分列不显示 ...
